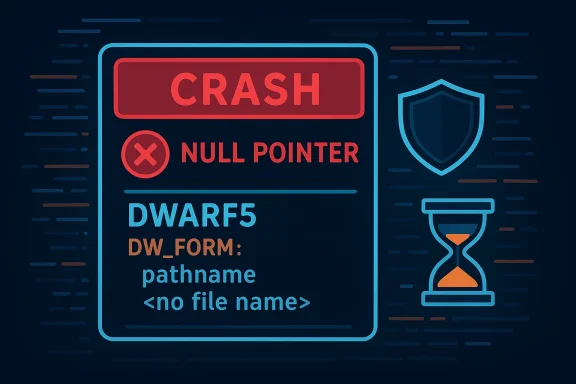
A subtle corruption in a DWARF5 line-table header can still bring a debugging toolchain to its knees: CVE-2020-28163 is a null-pointer dereference in libdwarf’s dwarf_print_lines.c that allows a crafted DWARF5 line-table header with an invalid FORM for a pathname to crash applications that consume the library, producing a denial‑of‑service condition until the buggy library is patched. (github.com)
libdwarf is the focused, single‑purpose library used by tools such as dwarfdump and other utilities that read DWARF debugging information in object files and executables. It is not a runtime tracer or dynamic debugger; rather, it parses DWARF sections from files on disk and exposes that information to callers. The project’s stated goal is to robustly handle DWARF versions up through DWARF5 and beyond, and to handle corrupted DWARF safely where possible.
DWARF is the standard debug information format used on many Unix‑like systems (and on many toolchains for native development). Line tables are a core DWARF structure: they map program counters to source file names and line numbers so debuggers, stack‑traces, and tools like dwarfdump can show meaningful source‑level information. Libraries that read those line tables must parse a mixture of variable‑length encodings and forms; a malformed or unexpected FORM field in that header can lead to incorrect pointer handling if the library doesn’t validate the form before using it. The bug tracked as CVE‑2020‑28163 is exactly such a boundary case.
This is not an isolated hiccup in the libdwarf codebase. The project has fixed multiple parsing flaws over the years and continues to harden its output routines to avoid crashes when presented with corrupted or fuzzed DWARF data. The upstream maintainer’s change log and commit history show a pattern of corrective patches addressing malformed DWARF inputs. (github.com)
Distribution vendors and vulnerability trackers incorporated the CVE entry and assigned it moderate severity with the suggested remediation being to update libdwarf to the version that contains the commit (libdwarf versions dated on or after 2020‑12‑01 per vendor advisories). Several distros and security trackers (Ubuntu, SUSE, OpenCVE, OSV) have records for CVE‑2020‑28163 and indicate the fix was incorporated in later package versions.
Because libdwarf is packaged across Linux distributions and may be statically linked into vendor tools, remediation requires both patching the library and auditing dependent binaries. Downstream vendors who ship static binaries that include libdwarf must be contacted or reviewed, and continuous integration providers should verify that hosted runners do not accept malformed artifacts without sandboxing. Vendor advisories and distro trackers that catalog the CVE help operators prioritize which images and machines to update.
For maintainers of libraries that parse complex, variable binary formats the lessons are straightforward:
Long term, the community should continue to push for:
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
libdwarf is the focused, single‑purpose library used by tools such as dwarfdump and other utilities that read DWARF debugging information in object files and executables. It is not a runtime tracer or dynamic debugger; rather, it parses DWARF sections from files on disk and exposes that information to callers. The project’s stated goal is to robustly handle DWARF versions up through DWARF5 and beyond, and to handle corrupted DWARF safely where possible.DWARF is the standard debug information format used on many Unix‑like systems (and on many toolchains for native development). Line tables are a core DWARF structure: they map program counters to source file names and line numbers so debuggers, stack‑traces, and tools like dwarfdump can show meaningful source‑level information. Libraries that read those line tables must parse a mixture of variable‑length encodings and forms; a malformed or unexpected FORM field in that header can lead to incorrect pointer handling if the library doesn’t validate the form before using it. The bug tracked as CVE‑2020‑28163 is exactly such a boundary case.
This is not an isolated hiccup in the libdwarf codebase. The project has fixed multiple parsing flaws over the years and continues to harden its output routines to avoid crashes when presented with corrupted or fuzzed DWARF data. The upstream maintainer’s change log and commit history show a pattern of corrective patches addressing malformed DWARF inputs. (github.com)
What CVE‑2020‑28163 is — technical breakdown
The fault: an invalid FORM for a pathname in a DWARF5 line‑table header
At its core, the vulnerability arises when libdwarf parses the line‑table header for a DWARF5 table and encounters a FORM value for a pathname entry it does not expect or validate correctly. DWARF uses typed “forms” to denote how a following attribute is encoded (for example, DW_FORM_strp, DW_FORM_strx, or other encodings). If the code assumes a pathname field is present and non‑NULL without validating the form and the form yields a NULL fi_file_name value, subsequent code paths attempt to append that name into a dwarfstring using dwarfstring_append (or similar helpers) while passing a NULL pointer. That causes a classic null pointer dereference and a crash in the consuming process. (github.com)Where it happens: dwarf_print_lines.c
The problematic function is in dwarf_print_lines.c, the part of the library that formats and prints line table entries for utilities such as dwarfdump. The upstream fix (committed by the libdwarf maintainer) adds a defensive check: when the file‑entry name pointer (fi_file_name) is NULL because of corrupted input, the code substitutes a literal string such as "<no file name>" rather than passing NULL to the string‑append helper. This is a small but correct change that avoids the unchecked dereference. (github.com)Why this class of error matters
NULL pointer dereferences are not exotic — they’re the bread and butter of crash primitives used in denial‑of‑service tests, fuzzers, and, in rare cases, as part of more complex exploit chains. For a debug‑parsing library, the primary risk is availability: a malicious or malformed object file can cause a debugger or inspection tool to die. Although the bug does not directly give code execution or data corruption, the availability impact is real because many toolchains and CI systems invoke DWARF parsers automatically during build, test, packaging, or symbolization tasks. Repeated or automated delivery of malformed files can take those systems offline or interrupt operations.Severity, exploitability, and real‑world impact
- CVSS context: CVSS scores assigned by multiple vendors put this bug in the medium category (CVSS v3.1 base score ~6.5), with availability impact rated High while confidentiality and integrity are unaffected. Attack vectors are typically network‑adjacent to remote when the vulnerable library is invoked in a context that accepts or processes remote input; attacker complexity is low but user interaction is often required because the attacker must get a crafted file to the victim.
- Realistic exploit scenarios:
- A developer downloads or builds a malicious or corrupted binary and runs a local tool (dwarfdump or another tool that ships with libdwarf) that invokes the vulnerable code; the tool crashes, disrupting the developer’s workflow.
- Continuous integration (CI) or artifact processing pipelines that analyze binaries for symbolization or metadata can be forced to fail when they encounter a crafted artifact, potentially stopping automated deployments.
- Malware authors or attackers who control artifact repositories (or inject artifacts into build pipelines) can use malformed object files to trigger repeated crashes, achieving a Denial‑of‑Service (DoS) effect on build infrastructure.
- Scope of affected software: the upstream libdwarf codebase before the 2020‑12‑01 fix is vulnerable; downstream distributions and packages that include older libdwarf builds — and binaries statically linked against them — may remain exposed until maintainers ship updated packages. Multiple vendor advisories and distro trackers list the CVE and mark it as resolved when consumers update to a patched libdwarf.
The upstream fix and disclosure timeline
On 2020‑10‑28 the libdwarf maintainer committed a small but effective change to dwarf_print_lines.c: where fi_file_name could be NULL for a file entry (due to a corrupted DWARF5 line header), the code now prints a literal placeholder string "<no file name>" instead of passing NULL into dwarfstring_append. The commit message explicitly references the Dwarfbug DW202010‑003 and documents the change as a defensive measure to avoid passing a null pointer into a string append routine. That commit is the canonical upstream fix. (github.com)Distribution vendors and vulnerability trackers incorporated the CVE entry and assigned it moderate severity with the suggested remediation being to update libdwarf to the version that contains the commit (libdwarf versions dated on or after 2020‑12‑01 per vendor advisories). Several distros and security trackers (Ubuntu, SUSE, OpenCVE, OSV) have records for CVE‑2020‑28163 and indicate the fix was incorporated in later package versions.
Detection and indicators
Detecting exploitation of CVE‑2020‑28163 is largely a matter of spotting crashes and abnormal failures in programs that parse debugging metadata. Practical detection steps include:- Monitor log files and CI job results for repeated or new crashes in dwarfdump, symbolization steps, or any tooling that runs libdwarf code. Sudden increases in failures against object files or packages that previously succeeded should be investigated.
- Add instrumentation to artifact ingestion services to validate inputs and reject suspicious or malformed ELF/COFF/Mach‑O files before handing them to DWARF parsers. Use strict file‑type checks and, where feasible, run parsing in a sandbox or container that isolates crashes.
- Use vulnerability scanners and package tracking: Qualys, distribution security trackers, and other scanners have detections or advisories for this CVE; ensure your CI or asset inventory flags vulnerable libdwarf package versions.
Mitigation and remediation: what operators should do now
- Identify affected assets:
- Inventory systems and CI runners that have libdwarf installed or that include tooling compiled against an older libdwarf. Pay special attention to packaging and build servers that automatically analyze binaries.
- Update libdwarf packages:
- Upgrade libdwarf in your distribution to the version that contains the October 28, 2020 upstream commit — distributions list fixed package versions in their security advisories. If a distribution lacks a backport, consider rebuilding libdwarf from a patched upstream source and deploying it via your internal package manager.
- Protect the toolchain:
- Where updating is not immediately possible, run DWARF‑parsing steps inside short‑lived containers or restricted sandboxes. This limits the blast radius if a crash occurs and prevents a malformed artifact from affecting other services.
- Harden artifact handling:
- Validate artifacts at repository boundaries. Reject object files that fail lightweight syntactic checks before invoking heavyweight parsers. Reject or quarantine artifacts with suspicious section headers or unusual DWARF version tags.
- Retest and rebuild:
- If you use statically linked binaries that incorporated an older libdwarf at build time, plan for a rebuild. Static linking bakes vulnerabilities into executable artifacts; only rebuilding against a patched libdwarf guarantees the fix.
Supply‑chain considerations and long‑tail exposure
This vulnerability underlines a classic supply‑chain exposure: libraries used for offline analysis (not just network services) are important attack surfaces. Build systems, CI, packaging tools, debuggers, and symbolizers often operate automatically and on incoming artifacts — including those provided by external contributors or mirrored from remote repositories. A maliciously crafted artifact placed into an artifact feed can cause downstream crashes in many consuming environments.Because libdwarf is packaged across Linux distributions and may be statically linked into vendor tools, remediation requires both patching the library and auditing dependent binaries. Downstream vendors who ship static binaries that include libdwarf must be contacted or reviewed, and continuous integration providers should verify that hosted runners do not accept malformed artifacts without sandboxing. Vendor advisories and distro trackers that catalog the CVE help operators prioritize which images and machines to update.
Why small fixes like this matter: reliability vs. security
The upstream fix is small — a substitution of a placeholder string when a name pointer is NULL — and yet the impact is disproportionate for environments that rely on robust processing of external artifacts. Defensive programming in parsing libraries is a security best practice: instead of letting unexpected encodings flow into an unchecked API, the library should validate input and return an error code describing malformed data. In this case the upstream action prevents a crash and preserves availability without changing public APIs.For maintainers of libraries that parse complex, variable binary formats the lessons are straightforward:
- Never assume well‑formed input.
- Use defensive checks immediately after parsing fields that can be absent or encoded in multiple forms.
- Prefer returning an error rather than silently continuing with potentially invalid pointers.
- Add fuzzing and synthetic tests that exercise malformed headers (including corrupt FORM values) and assert that the library returns a controlled failure rather than crashing. The libdwarf project has made such fixes repeatedly as fuzzing and real‑world malformed files surfaced problems. (github.com)
Actionable checklist for developers and administrators
- Developers:
- Rebuild any statically linked binaries that include libdwarf against a patched libdwarf release.
- Add defensive input validation to any code that calls into libdwarf: never dereference pointer returns from the library without checking for errors.
- Add unit tests that simulate incomplete or corrupted DWARF line‑table headers and assert that your code handles these failures gracefully.
- Administrators / SREs:
- Patch libdwarf packages to the vendor‑supplied fixed versions or deploy the patched upstream tarball where vendor packages are unavailable.
- Sandboxed parsing: run DWARF parsing tasks in containers, apply resource limits (CPU, memory), and capture crashes to a central monitoring system.
- Update vulnerability scanners and inventory to flag older libdwarf versions and track remediation progress.
- Security teams:
- Consider adding DWARF parsing into fuzzing campaigns for internal triage: corrupted DWARF files are an easy and relatively low‑cost surface to fuzz for parse errors.
- Review artifact ingestion policies to ensure external artifacts are validated before internal processing.
Broader implications for supply‑chain and tooling security
CVE‑2020‑28163 is a textbook example of why even “non‑network” libraries matter to defenders. Attackers need not find a remote socket to induce a denial of service; they only need a path into the artifact stream. Modern build and CI environments are inherently connected: they pull dependencies, test third‑party inputs, and process artifacts. As a result, a low‑complexity crash bug in a parsing library can be weaponized into a sustained availability problem by repeatedly feeding malformed objects into ingestion points.Long term, the community should continue to push for:
- Better fuzzing coverage for DWARF and binary parsers.
- Safer library APIs that make NULL‑safe use harder to misuse.
- Faster vendor patch distribution and transparent advisories so downstream package maintainers can coordinate updates without delay.
Conclusion
CVE‑2020‑28163 is not an exotic escalation or a memory corruption that yields remote code execution, but it is exactly the kind of practical availability risk that disrupts developer workflows and CI/CD pipelines. The upstream patch is simple, effective, and illustrates how small defensive checks in parsing code pay dividends for reliability and security. Operators should inventory libdwarf usage in their environments, apply patched packages or upstream fixes, sandbox DWARF parsing where possible, and treat artifact ingestion as an attack surface. The fix is available; the important work now is to deploy it and to harden ingestion and build systems so that one malformed line‑table header can no longer halt the delivery pipeline. (github.com)Source: MSRC Security Update Guide - Microsoft Security Response Center