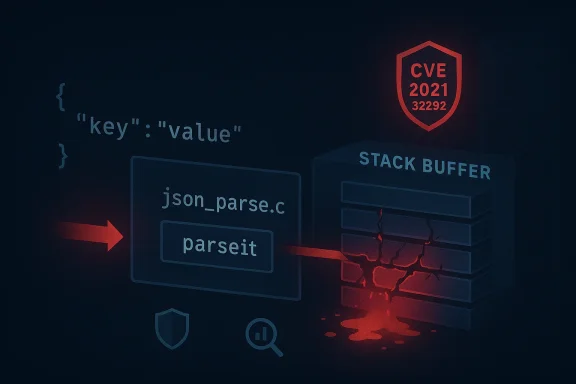
The json-c library’s long‑running reputation for light‑weight JSON parsing took a sharp turn in 2023 when a stack‑buffer‑overflow in the auxiliary sample program json_parse was assigned CVE‑2021‑32292 — a defect that can be triggered by crafted input to the parseit() function and which, in affected builds, enables denial‑of‑service and potentially remote code execution.
json-c is a widely used C library that implements a reference‑counted object model for parsing and constructing JSON in C projects. It’s embedded in countless Linux distributions, appliances and third‑party products; because it’s C‑based, mistakes in manual memory handling can have severe security consequences. The vulnerability tracked as CVE‑2021‑32292 affects json‑c sample code rather than necessarily the core parsing library API — specifically, the auxiliary sample program
That combination — a simple, common library plus exploitable C memory‑safety issues — is what elevates the severity for many consumers. Multiple vulnerability databases and distro trackers classify the issue as high or critical, and multiple vendors issued advisories or package updates after public disclosure.
For developers and security engineers, the immediate lesson is familiar: avoid unsafe C string APIs, apply explicit length checks, and treat sample programs as code that must be scrutinized equally to library API surfaces.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
json-c is a widely used C library that implements a reference‑counted object model for parsing and constructing JSON in C projects. It’s embedded in countless Linux distributions, appliances and third‑party products; because it’s C‑based, mistakes in manual memory handling can have severe security consequences. The vulnerability tracked as CVE‑2021‑32292 affects json‑c sample code rather than necessarily the core parsing library API — specifically, the auxiliary sample program json_parse contains a stack buffer overflow in the function parseit(). Public vulnerability records and vendor trackers confirm the affected range as code from 20200420 (post 0.14 unreleased code) through 0.15‑20200726.That combination — a simple, common library plus exploitable C memory‑safety issues — is what elevates the severity for many consumers. Multiple vulnerability databases and distro trackers classify the issue as high or critical, and multiple vendors issued advisories or package updates after public disclosure.
What the vulnerability is, in plain technical terms
- The flaw is a stack‑based buffer overflow in
parseit()insidejson_parse.c. A function allocates a fixed‑size stack buffer and then copies or composes data into it without sufficient bounds checking. When fed an input larger than the buffer, writes spill past the buffer boundary into adjacent stack memory. - Because the overflow is on the stack, attackers can — in principle — overwrite saved frame data (return addresses, saved base pointers) and alter control flow, which opens the classic path to remote code execution (RCE) or to reliably crash the process (denial‑of‑service).
- The vulnerable code is part of an auxiliary sample program, not the primary API used by applications; however, sample code frequently serves as the source for copy‑paste usage, proof‑of‑concept demos, or quick local tools that are then embedded or shipped in appliances. That makes this more than an academic problem. Multiple distro advisories stress examining derived code and packages that vendor products ship.
Timeline and disclosure (concise)
- The defect dates from code revisions around 2020; affected builds are labeled 20200420 through 0.15‑20200726 in multiple trackers.
- Public CVE record and community trackers aggregated the issue and cataloged it under CVE‑2021‑32292.
- Distributions and vendors (Debian, Gentoo, vendor product advisories) later published security advisories and updated packages; many recommended or required upgrading to json‑c >= 0.16 where the problem is addressed.
- Community discussion, issue tracking, and follow‑on advisories tied the CVE to a GitHub issue / project backlog and to vendor packages that embed json‑c.
Why this matters: exposure and practical risk
- Wide reuse of C libraries. json‑c is a dependency in OS packages and appliances. Even when the vulnerable code is an auxiliary program, downstream consumers sometimes include or run sample utilities, or vendors fork and modify code — multiplying potential exposure.
- Low exploitation complexity. Buffer overflow exploitation in C, while mitigations exist (stack canaries, ASLR, NX), is still feasible, especially on systems where protections are absent or incomplete. Several vulnerability databases rate the vector as network‑accessible with low complexity.
- Impact ranges from DoS to RCE. At a minimum, a successful overflow can crash the process and deny service; at worst, an attacker may execute arbitrary code in the context of the process, escalate access, or move laterally within a networked environment. Multiple advisories conservatively treat the issue as allowing high confidentiality, integrity and availability impacts.
- Product integration risk. Appliance vendors and proprietary products that statically link json‑c, or embed the sample program in management tooling, may carry the vulnerability even when OS packages are patched. NetApp and other vendors flagged dependent products in vendor advisories.
Technical deep dive: what makes parseit() exploitable
The vulnerability follows a standard pattern:- A stack buffer is declared with a fixed size.
- Untrusted input — JSON text, filename strings, or tokenized fragments — is copied or built into that buffer using unsafe or insufficiently‑bounded operations.
- There is no robust length check relative to the buffer’s capacity; error handling and parsing paths can permit longer attacker‑controlled strings to be placed on the stack.
- Because the overflow happens on the stack, an attacker who supplies a carefully crafted input can overwrite saved registers or return addresses and influence the return path. Depending on compiler options and runtime hardening, this may lead to code execution or an immediate crash.
parseit(); other sources label it under CWE‑121 (stack‑based buffer overflow) depending on the analysis lens.For developers and security engineers, the immediate lesson is familiar: avoid unsafe C string APIs, apply explicit length checks, and treat sample programs as code that must be scrutinized equally to library API surfaces.
Evidence, verification and cross‑references
To ensure accuracy, key claims were cross‑checked across independent sources:- The national CVE/NVD record reproduces the canonical description and the affected version range.
- Distro security trackers and vendor advisories (Debian, Gentoo, NetApp and others cataloged in vulnerability databases) confirm the affected versions and advise upgrading to patched packages or version 0.16+.
- The json‑c project repository documents releases and issue tracking for the project and is the authoritative code source for the sample program; community issue threads and changelogs show discussion and fixes.
Real‑world exploitation: what we know and what we don’t
- There are no widely publicized, reliable reports of large‑scale, in‑the‑wild exploitation campaigns solely targeting CVE‑2021‑32292 at the time of writing in public advisories. Several intelligence and vulnerability databases record low EPSS/exploitability estimates or note the absence of public exploit code. That said, the potential for targeted exploitation exists because of the simplicity of the root defect.
- Exploit availability: some community writeups and PoC examples exist in controlled repositories or researcher blogs, but confirmed weaponization against production targets has not been widely documented in the public disclosures we reviewed. As with many memory‑safety bugs, the timeline from disclosure to exploitation varies and can be short for well‑understood classes like stack overflows. Exercise caution: absence of evidence is not evidence of absence.
Affected products and packaging pitfalls
- Direct consumers: Applications that link to json‑c and include the auxiliary
json_parsesample program — or copy‑pasted code derived from it — are directly affected. Many Linux distributions shipped packages with json‑c; distributions published advisories listing affected releases and updated package versions. - Appliances and vendor products: Vendors that embed json‑c in management tooling or in appliance firmware may be affected even if their OS packages are up to date. Vendor advisories and product security bulletins often list json‑c among third‑party library CVEs. Administrators should consult vendor firmware release notes and security pages.
- Static linking and vendor forks: If a product statically links an old json‑c library or has in‑tree copies of the sample code, applying distribution package updates will not remediate the vendor binary. For such cases, a rebuild or vendor patch release is required.
Detection, indicators and recommended investigative steps
Detecting exploitation requires both binary analysis and runtime observation:- Look for crashes or core dumps of processes that link json‑c or run
json_parseutilities. A sudden segmentation fault or illegal instruction in a utility that parses JSON is a potential red flag. - Inspect process command lines, service wrappers, cron jobs, and startup scripts for any instance of
json_parseor tooling that invokes bundled utilities. - Review vendor advisories and distribution changelogs for package names and filenames (for example, json‑c binary packages and their tested fixes). Package manager metadata can show installed versions.
- If you are a security operations team: correlate application crashes with incoming network traffic containing unusual JSON payloads, especially very long string fields or nested structures that exceed expected bounds.
- Query package manager for installed json‑c versions and compare with patched versions supplied by your distribution vendor.
- Audit product firmware and vendor images for static json‑c copies.
- If you operate IDS/IPS or WAF signatures, enrich them with detection for anomalously long JSON tokens that could attempt to overflow a fixed buffer. Note that signature rules are inherently brittle; use them only as a layering control.
Patching and mitigation guidance (practical steps)
- Primary action: update json‑c to a non‑vulnerable version. Distributions and the project recommend upgrading to versions that include the fix (versions >= 0.16 in most vendor advisories). Use your OS package tooling or vendor update mechanism — do not simply copy single files.
- For appliances or vendor products: apply vendor firmware or software updates. If no update is available, contact the vendor to obtain an official patch or a workaround.
- If immediate patching is impossible:
- Remove or disable auxiliary sample programs like
json_parsefrom production systems. - Limit exposure by applying network segmentation and filtering to reduce the chance of untrusted JSON reaching vulnerable utilities.
- Use application‑level input validation to reject input with suspiciously long tokens or structures before passing it into native code. This is a stopgap — not a substitution for a proper patch.
- Build‑time mitigations for developers:
- Recompile with modern hardening flags: stack canaries, position‑independent executables, ASLR, and non‑executable stack when available.
- Replace unsafe string operations with bounded APIs and adopt safe parsing practices (e.g., use tokenizer APIs that accept length parameters).
- Run fuzz‑testing and static analysis tools against parsing code to proactively discover similar issues.
Developer takeaways: avoidance and secure coding practices
- Treat sample programs as first‑class code: they may be copied into production or used in debugging tools. Do not assume auxiliary tools are less critical.
- Prefer robust parsing routines that accept explicit lengths and avoid unbounded copies.
- Add automated fuzzing and regression tests into CI for any parsing components.
- When reusing third‑party code, check upstream advisories and upstream commits; keep third‑party components on a regular update cadence.
Strengths and shortcomings of the public response (critical analysis)
Strengths:- The vulnerability was cataloged and cross‑referenced quickly across vulnerability trackers and the NVD record, allowing distributors and vendors to coordinate fixes and package updates.
- Distributions and security teams produced practical mitigations (package upgrades, advisory notices) and made explicit the risk from derived code — an important point that operators sometimes miss.
- Because the vulnerable code is in an auxiliary program, some organizations initially deprioritized remediation — but sample utilities are commonly repurposed, increasing supply‑chain risk. This semantic distinction (auxiliary vs. core) can lull responders into a false sense of safety.
- Public CVSS and severity assignments sometimes vary across trackers and vendors; this inconsistency can complicate prioritization. Analysts should rely on concrete exposure (is vulnerable code shipped/unpatched in my environment?) rather than on a single aggregated score.
- Vendor imaging and appliance ecosystems often lag behind distro packages; static linking, in‑tree library copies and custom builds mean that package updates are not a universal fix. That disconnect is the practical gap that attackers can exploit.
Recommendations for WindowsForum readers (system owners, developers, sysadmins)
- Inventory: run a dependency inventory for json‑c across your servers, appliances and developer toolchains. Identify any instance where the
json_parsesample program or older json‑c versions are present. Use package manager queries on Linux systems and vendor advisories for appliances. - Patch: apply distro packages or vendor firmware updates that include the json‑c fix. If you manage bespoke builds, reb 0.16 and ensure the auxiliary sample programs are removed from production images.
- Harden: ensure builds are compiled with modern mitigations (canaries, PIE, ASLR) and that deployment hardening is in place for services that process untrusted JSON.
- Monitor: add crash and anomalous JSON payload detection to your monitoring runbook; centralize crash reports and examine core dumps where available.
- Educate: remind development teams that sample code is code — and that copy‑paste reuse is a frequent supply‑chain vector for vulnerabilities.
Closing analysis: supply‑chain risk is the real lesson
CVE‑2021‑32292 is technically a classic buffer overflow, but the larger story is supply‑chain hygiene. A fixed, trivial‑looking sample program in a small open‑source library escalates into a real operational problem when downstream packages, appliances, and vendor distributions copy or ship that code without active patching. The vulnerability underscores three perennial truths:- Memory safety in C remains a critical, unresolved source of high‑impact vulnerabilities.
- Dependence on third‑party code — even samples — requires active inventory, timely patching and vendor coordination.
- Technical fixes (upgrades, hardening) combined with operational controls (segmentation, monitoring) form the only realistic defense in production environments.
Source: MSRC Security Update Guide - Microsoft Security Response Center