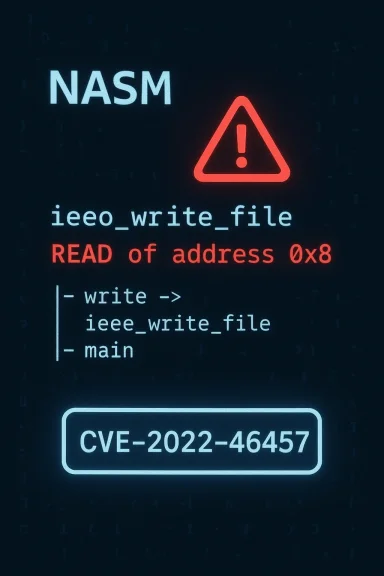
NASM users should immediately take notice: a segmentation fault bug in the IEEE output writer for NASM 2.16—tracked as CVE-2022-46457—can be triggered by a crafted assembly file and causes the assembler to crash, producing a denial-of-service condition for any workflow that processes untrusted NASM inputs. This is an availability-focused vulnerability in the ieee_write_file implementation (output/outieee.c) that was reported to NASM’s bug tracker and recorded in public vulnerability databases; upstream tracking shows the issue was investigated and closed in NASM’s bug tracker, and multiple Linux distributions have evaluated and remedied the problem in packaged builds. (bugzilla.nasm.us)
NASM (the Netwide Assembler) is one of the most widely used assemblers for x86/x86-64 development. Its flexibility and broad output-format support (ELF, COFF, Mach-O, IEEE-style object output, etc.) make it a staple in toolchains, bootloaders, embedded toolchains, and developer environments. A defect in one of NASM’s output backends therefore has outsized operational impact whenever NASM is used in automated build systems, continuous integration, or as a library step in production toolchains.
CVE-2022-46457 was published in early January 2023 and identifies a segmentation violation (SIGSEGV) occurring in the function responsible for writing IEEE-format object files: ieee_write_file in output/outieee.c. The National Vulnerability Database records the core description and associated CVSS v3.1 vector (local attack vector; user interaction required; high availability impact). The vulnerability’s CVSS score is listed as 5.5 (Medium) under CVSS v3.1 in vendor databases that performed scoring. (nvd.nist.gov)
Short-term mitigations (high priority)
In summary: CVE-2022-46457 is a real, publicly tracked segmentation violation in NASM’s IEEE writer that can crash the assembler and cause denial-of-service for systems that process untrusted assembly files. The fix path is straightforward—apply the NASM update provided by your OS vendor or update upstream—but the operational recommendation is broader: reduce exposure to untrusted inputs, sandbox assembler invocations, and integrate NASM updates into regular patch cycles for development and CI infrastructure. Verify your distro’s package advisory for the correct patched version and confirm remediation with the proof-of-concept in a controlled sandbox before declaring systems secure. (bugzilla.nasm.us)
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
NASM (the Netwide Assembler) is one of the most widely used assemblers for x86/x86-64 development. Its flexibility and broad output-format support (ELF, COFF, Mach-O, IEEE-style object output, etc.) make it a staple in toolchains, bootloaders, embedded toolchains, and developer environments. A defect in one of NASM’s output backends therefore has outsized operational impact whenever NASM is used in automated build systems, continuous integration, or as a library step in production toolchains.CVE-2022-46457 was published in early January 2023 and identifies a segmentation violation (SIGSEGV) occurring in the function responsible for writing IEEE-format object files: ieee_write_file in output/outieee.c. The National Vulnerability Database records the core description and associated CVSS v3.1 vector (local attack vector; user interaction required; high availability impact). The vulnerability’s CVSS score is listed as 5.5 (Medium) under CVSS v3.1 in vendor databases that performed scoring. (nvd.nist.gov)
What happened: a concise technical summary
- The crash was reported by a researcher who supplied a tiny proof-of-concept input; when NASM was invoked with the IEEE output format on that input, it emitted a warning and then crashed with an AddressSanitizer (ASAN) trace showing a read at address 0x8 inside ieee_write_file. The NASM bug entry includes the ASAN backtrace demonstrating the invalid read and confirms the crash occurs during ieee_write_file execution. (bugzilla.nasm.us)
- Multiple vulnerability trackers (NVD, OSV, OpenCVE and distro advisories) consolidated this report under CVE-2022-46457 and documented the core facts: segmentation violation in ieee_write_file and the likely impact being application crash / availability loss. The CPEs and affected commits were enumerated in open-source vulnerability feeds. (nvd.nist.gov)
- The bug is characterized as an invalid memory read (out-of-bounds read) that results in a segmentation fault, not as a straightforward code-execution primitive. The primary risk, therefore, is denial-of-service (DoS): NASM can be crashed by processing a malicious or malformed assembler file. Several vendors and maintainers categorized impact as availability only (no confidentiality/integrity loss reported). (bugzilla.nasm.us)
Why this matters — practical risk analysis
- Toolchain availability: Many build systems call NASM as a build step. If a CI runner or a packaging pipeline assembles untrusted inputs (for example, unvetted contributions, third-party code, or attacker-controlled content), an attacker who can provide a specially crafted file can repeatedly crash the assembler process. That can stall or deny downstream builds until human intervention. Even if each crash is “just” an application exit, the cumulative effect on automated pipelines can be severe. (bugzilla.nasm.us)
- Supply-chain exposure: Open-source projects often accept community-submitted assembly snippets or pull requests. A malicious or malformed assembly file could be used as a simple vector to disrupt automated tooling, particularly in federated or multi-tenant CI environments. This is an operational risk that’s easy to underestimate because the vulnerability requires local invocation (AV:L) or the user to run NASM on the crafted file—but modern CI environments often run arbitrary contributor code during builds. (nvd.nist.gov)
- Not a direct remote code-execution (RCE) verdict: Public reporting shows no evidence that CVE-2022-46457 enables arbitrary code execution; the available ASAN trace and vendor write-ups point at out-of-bounds reads that crash the process. However, history shows that crash-inducing bugs in low-level tooling can sometimes be escalated or chained into more serious problems, depending on context and further bugs. Treat this as availability-first risk, but do not dismiss the potential for future exploitation pathways if other memory errors are present. (bugzilla.nasm.us)
What sources say (cross-checked)
- The NVD entry for CVE-2022-46457 records the concise description and a CVSS vector placing the attack vector as Local and availability as High. This is the authoritative CVE aggregation point for the public description. (nvd.nist.gov)
- NASM’s own bugzilla contains the original report, a small proof-of-concept, and an ASAN trace showing the crash in ieee_write_file; the tracking entry was marked CLOSED FIXED in the upstream bug tracker. That entry is the primary technical artifact for the vulnerability. (bugzilla.nasm.us)
- Linux distribution advisories and security trackers (Gentoo GLSA, Ubuntu security pages, SUSE, AWS ALAS) referenced the CVE and incorporated it into their packaging security workstreams. Gentoo’s GLSA references multiple NASM CVEs and specifically recommends using versions >= 2.16.01 to remediate earlier issues; other feeds and distro trackers indicate packaged updates or status per release. Because distributions manage binary packaging separately, administrators must consult their distro advisory for the exact patched package version.
Technical breakdown (deeper)
What the ASAN trace shows
The proof-of-concept provided to the NASM bugtracker triggers a read from a near-null pointer (address 0x8), indicating that a pointer used inside ieee_write_file was not initialized or was cleared before dereference. The AddressSanitizer output in the bug entry shows:- Crash in ieee_write_file (output/outieee.c) with a read at 0x8.
- Stack frames include ieee_cleanup and main, which indicates the crash happens during the final output/cleanup phase for the IEEE backend. (bugzilla.nasm.us)
Where in the flow this happens
The IEEE backend is a relatively niche output format compared to ELF or COFF, and the crash occurs during formation of the IEEE-format object file. That means the vulnerability can be triggered only if NASM is asked to produce IEEE-format output (for example, via-f ieee), or during cleanup code paths that reference IEEE-specific structures. This limits the attack surface to cases where the IEEE writer is invoked, but it still matters for environments that rely on less-common object formats or for fuzzing scenarios where a bad format flag is provided. (bugzilla.nasm.us)Who is affected
- Developers and CI/CD pipelines that call
nasmon untrusted or external inputs. - Packaging and distribution maintainers shipping NASM in binary distributions.
- Embedded toolchains and custom build systems that may use NASM’s IEEE output format.
- Security-conscious users relying on NASM in multi-tenant build infrastructure.
Detection and indicators
There are straightforward indicators you can search for in logs and CI output:- Build or assembler failures that contain the string “Segmentation fault” or an AddressSanitizer report referencing output/outieee.c or ieee_write_file.
- CI job failures that consistently occur when assembling certain files, especially with the
-f ieeeflag set. - Crash backtraces captured by systemd/journald or container logs showing the NASM executable aborted with SIGSEGV.
- Package vulnerability scanners (OSV, distribution advisories) flagging nasm packages with CVE-2022-46457 in their advisory feeds. (bugzilla.nasm.us)
- Run
nasm -f ieeeon suspect files in an isolated environment understrace(or ASAN-enabled build) to see whether the crash reproduces. - Add simple static policy rules in CI to refuse test inputs that require legacy formats (like IEEE) unless explicitly allowed.
- Use your vulnerability-management tooling to flag the nasm package version against CVE-2022-46457 advisories.
Mitigation and remediation
The immediate, highest-confidence remediation is to update NASM to a version that contains the fix or to install your distribution’s patched nasm package. Upstream bug tracking shows the issue as CLOSED FIXED, and multiple distros have packaged updates or provided guidance. However, because packaging timelines differ across distributions, administrators should verify the exact package version in their distro’s security advisory before assuming their systems are safe. (bugzilla.nasm.us)Short-term mitigations (high priority)
- Do not run
nasmon untrusted assembly files, especially with-f ieee. If possible, restrict assembly stages to trusted sources only. - Block
nasmexecution from untrusted user contexts or contributors in CI (use job sandboxing or explicit allow-lists). - If you must process third-party assembly files, run them in an isolated container or ephemeral VM where a crash cannot affect critical systems.
- Check your distribution’s advisory and package repository for a nasm update that addresses CVE-2022-46457; apply the OS-specific security update (APT, YUM/DNF, zypper, emerge, etc.).
- If building from source, update to the NASM release or commit that contains the fix. Upstream bug tracking indicates the issue was addressed in the tracker; consult upstream ChangeLog and release notes for the precise release you should use. (bugzilla.nasm.us)
- Rebuild any downstream packages and CI images that include NASM to ensure they contain the patched binary.
- Verify remediation by running the previously failing proof-of-concept (in a sandbox) to confirm the assembler no longer crashes.
- Add sandboxing to build steps that invoke native binaries (use seccomp, containers, or dedicated build VMs).
- Use input validation or format whitelists to avoid invoking niche output formats unless they’re required.
- Include NASM in routine vulnerability scanning, and subscribe to upstream and distro security mailing lists to receive advisories.
Remediation checklist (quick reference)
- Inventory: Identify all hosts, images, and CI runners where
nasmis installed or invoked. - Verify: Determine installed nasm package version(s) and check against distro advisories for patches addressing CVE-2022-46457.
- Isolate: Suspend automated processing of untrusted assembly inputs, or enforce privileged separation for build jobs that call
nasm. - Patch: Apply OS vendor/package updates or rebuild NASM from a patched upstream release.
- Test: Reproduce the original POC in a safe sandbox; confirm the crash no longer occurs.
- Harden: Add sandboxing to assembler invocations; restrict use of legacy formats when not necessary.
- Monitor: Watch for new NASM vulnerabilities and track CVE feeds and distro advisories for follow-ups.
What about exploitability and real-world attacks?
- The public indicators and vulnerability records show no evidence of a public RCE exploit for CVE-2022-46457. Attackers can cause NASM to crash by supplying a crafted assembly file, but the available information supports a DoS/availability impact rather than code execution. That said, CVE triage and mitigation should treat the issue seriously because toolchain crashes can be used as part of supply-chain disruption or to force fallback to less secure paths in automated workflows. (nvd.nist.gov)
- Distribution advisories and security trackers give the vulnerability a medium-severity CVSS score (5.5) largely due to High impact on availability but limited confidentiality/integrity impact. The attack vector is local (AV:L) and requires user interaction in many contexts (UI:R), which reduces remote-exploitability risk but does not eliminate real-world risk to automated build systems and multi-tenant CI. (nvd.nist.gov)
Special considerations for packagers and distributions
- Different distros take different approaches: some backport patches into older packaged branches, others require an upstream version jump. Gentoo’s advisory recommended upgrading to >= 2.16.01 for a group of NASM vulnerabilities, while other packagers show fixes rolled into 2.16.02 / 2.16.03 or later packaging updates; packaging metadata and changelogs are the final authority for a given distribution. This divergence means administrators should consult their distro’s security tracker rather than assume one specific fixed version covers every vendor.
- If you maintain your own distribution snapshots or container images, rebuild them to include patched nasm packages and test the images in a CI environment before rolling into production. For embedded toolchains where upstream updates are hard to integrate, evaluate targeted backports or vendor-stated mitigations.
Recommendations for CI/CD and development teams
- Treat assembly source files as you treat other third-party code: do not run unvetted assembler invocations in privileged or shared runners without sandboxing.
- Add a preflight step to CI that rejects unusual or legacy object-format flags unless explicitly approved (for example, disallow
-f ieeeunless required). - Run toolchain binaries (assemblers, linkers, native compilers) in ephemeral containers or dedicated build VMs that can be forcefully reset if a crash occurs.
- Incorporate nasm version checks into your image build/test pipelines and automate package updates where possible to reduce window-of-exposure. (bugzilla.nasm.us)
Closing analysis — strengths, limitations, and lingering uncertainties
Strengths in the handling of this report:- Clear upstream bug tracking with a reproducible proof-of-concept and ASAN output allowed maintainers and packagers to triage and address the issue. The bug entry is explicit and includes diagnostic output, which helped downstream vendors prepare updates. (bugzilla.nasm.us)
- Multiple independent vulnerability feeds and distro advisories converged on the same fault description and impact model (segfault in ieee_write_file → availability impact), providing reliable cross-verification. (nvd.nist.gov)
- The vulnerability’s fixed-version metadata varies between distributions and advisory feeds. For administrators, the single-most important action is to confirm that the NASM package installed in your environment is the specific patched build from your vendor. Do not assume fix presence based solely on an upstream release number without verifying vendor changelogs. This point is especially important because some NASM releases in the 2.16.x line (for example, 2.16.03) were described as build/documentation-only updates; packagers may have applied fixes at different points. When in doubt, check the distribution package changelog and rebuild or redeploy patched images.
- While current reporting indicates availability-only impact, any memory-safety bug in a low-level tool deserves careful monitoring. The presence of other NASM CVEs in recent years (some enabling more severe impact) means toolchain components remain attractive targets; a crash could be a stepping stone in combined attacks if additional vulnerabilities are present. Treat toolchain hardening and input sanitization as ongoing measures, not one-time fixes.
In summary: CVE-2022-46457 is a real, publicly tracked segmentation violation in NASM’s IEEE writer that can crash the assembler and cause denial-of-service for systems that process untrusted assembly files. The fix path is straightforward—apply the NASM update provided by your OS vendor or update upstream—but the operational recommendation is broader: reduce exposure to untrusted inputs, sandbox assembler invocations, and integrate NASM updates into regular patch cycles for development and CI infrastructure. Verify your distro’s package advisory for the correct patched version and confirm remediation with the proof-of-concept in a controlled sandbox before declaring systems secure. (bugzilla.nasm.us)
Source: MSRC Security Update Guide - Microsoft Security Response Center