The Linux kernel patch tracked as CVE-2022-48716 fixes a subtle but real bug in the ASoC codec driver for Qualcomm’s WCD938x family: mixer controls were using a channel id where a port id was required, allowing out-of-bounds access of an internal port_map array and risking corruption of the driver’s private state. This is a memory-safety / availability issue in kernel audio code that was corrected upstream and backported into stable kernel releases; operators should treat it as a timely patch-and-reboot priority for any hosts that load the WCD938x codec driver.
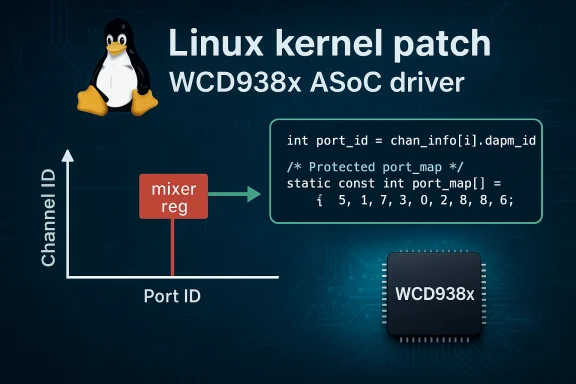
The Advanced Linux Sound Architecture’s System-on-Chip (ASoC) layer exposes codec drivers that directly manage audio hardware on many mobile and embedded platforms. The WCD938x driver (sound/soc/codecs/wcd938x.c) handles mixer controls and port mappings for Qualcomm WCD938x audio codecs used in some SoC platforms. A programming mistake in how a mixer’s register value (which contains a channel id) was interpreted as a port id allowed the code to index the codec’s port_map array with the wrong value. The result: a possible out‑of‑bounds access that can corrupt the driver’s struct wcd938x_sdw_priv and produce crashes or undefined kernel behavior.
Why this matters: kernel memory corruption—even when limited to a driver private struct—can cause immediate availability loss (kernel oops, panic, device driver crash) and in theory can be escalated into more serious integrity or confidentiality issues if an attacker can reliably control heap layout. For practical defenders the clear and immediate outcome is instability and denial‑of‑service against the audio subsystem or the host, and for embedded appliances the bug may be the difference between graceful failure and a hard device reboot.
Third‑party vulnerability trackers and vendor advisories list the patched thresholds as including the 5.15.22, 5.16.8 and 5.17 stable updates (and downstream vendor backports where applicable). If you manage kernels in those series, check your distribution’s security advisory for the specific package version that includes the stable patch.
For maintainers, the lesson is practical: rigorously document data layouts and ensure public-facing mixer or control registers are normalized into driver-internal indices before indexing arrays. Use defensive checks on array bounds and prefer safe helpers for lifecycle-managed objects. These simple engineering disciplines prevent small bugs from creating high-impact outages. (mirrors.edge.kernel.org)
Two important operational cautions:
Conclusion: the vulnerability underlines an enduring truth in systems software—small, semantic mistakes in low-level code can produce outsized operational risk. The upstream fix is short, correct, and backportable; the operational work is in finding every device that needs it and closing that long tail of unpatched, embedded exposures.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
The Advanced Linux Sound Architecture’s System-on-Chip (ASoC) layer exposes codec drivers that directly manage audio hardware on many mobile and embedded platforms. The WCD938x driver (sound/soc/codecs/wcd938x.c) handles mixer controls and port mappings for Qualcomm WCD938x audio codecs used in some SoC platforms. A programming mistake in how a mixer’s register value (which contains a channel id) was interpreted as a port id allowed the code to index the codec’s port_map array with the wrong value. The result: a possible out‑of‑bounds access that can corrupt the driver’s struct wcd938x_sdw_priv and produce crashes or undefined kernel behavior.Why this matters: kernel memory corruption—even when limited to a driver private struct—can cause immediate availability loss (kernel oops, panic, device driver crash) and in theory can be escalated into more serious integrity or confidentiality issues if an attacker can reliably control heap layout. For practical defenders the clear and immediate outcome is instability and denial‑of‑service against the audio subsystem or the host, and for embedded appliances the bug may be the difference between graceful failure and a hard device reboot.
The technical fault: channel id vs port id
What went wrong
- Mixer controls in the ASoC framework store an identifier in mixer->reg. In the WCD938x driver implementation that value contained a channel id, not a port id.
- The vulnerable code used mixer->reg (the channel id) to index into port_map, which expects an index derived from the channel‑info’s port id instead.
- When a channel id differed from the intended port id, this led to out-of-bounds indexing of port_map and corruption of struct wcd938x_sdw_priv. That corruption manifests as crashes, kernel oopses, or unpredictable audio driver behavior. (mirrors.edge.kernel.org)
Why it’s not just a harmless UI bug
At first glance a mixer-control mismatch sounds like an audio parameter issue, but kernel drivers operate in privileged context and incorrect array indexing in kernel space carries outsized risk. The immediate consequences include:- Kernel oopses or driver crashes that bring down audio services.
- Persistent instability in the device driver that may require module unload or full reboot.
- In embedded or tightly integrated devices, a crash in the sound driver can cascade to device-level failures or block suspend/resume flows.
Where the fix landed and which kernels are patched
The upstream patch was merged into the stable kernel trees and appears in multiple 5.x stable releases. Maintainers included the corrected code in stable updates; examples in the official changelogs show the commit landed as part of the 5.15.22 branch and appears in subsequent stable branches as well. The stable changelog entries that mention the change describe the exact correction: “Mixer controls have the channel id in mixer->reg, which is not same as port id. port id should be derived from chan_info array. So fix this.” (mirrors.edge.kernel.org)Third‑party vulnerability trackers and vendor advisories list the patched thresholds as including the 5.15.22, 5.16.8 and 5.17 stable updates (and downstream vendor backports where applicable). If you manage kernels in those series, check your distribution’s security advisory for the specific package version that includes the stable patch.
Severity, CVSS and inconsistent public reporting
Different sources have labeled the issue with different severities and vectors, which is worth flagging.- The NVD records the vulnerability and succinct description but does not always publish an immediate CVSS score for every entry. For the authoritative defect description you should consult the NVD entry.
- Several third‑party aggregators flagged the issue with very high CVSS scores (some citing CVSS v3.1 base scores around 9.8) and even suggested a network vector in some machine-generated summaries. Those high‑severity / network‑vector assessments appear to be automated or heuristic outputs and should be treated with caution. At least one vendor advisory classifies it as local and rated the CVSS differently.
- The kernel code and patch context indicate the attack surface is constrained: exploitation requires the vulnerable driver to be present and, practically, a way to trigger the problematic mixer control behavior—i.e., local privilege or a local process that can interact with ALSA mixer controls. That strongly supports a local attack vector (AV:L) rather than a public, unauthenticated remote vector. Several distribution advisories and trackers reflect that local requirement.
Practical impact and exploitation considerations
Likely attack scenarios
- Local adversary or malicious process on a host that has the wcd938x codec driver loaded can attempt to exercise mixer control paths and provoke out‑of‑range accesses.
- Faulty or malicious userland audio clients (for example, apps that send crafted control messages to ALSA) could trigger the code paths that index port_map incorrectly.
- On some embedded platforms where the audio codec is tightly integrated with other subsystems, driver corruption could escalate availability impact beyond the audio service—e.g., impacting system suspend/resume or platform-specific control sequences. (mirrors.edge.kernel.org)
What an attacker can achieve
- The most immediate and realistic outcome is denial‑of‑service: driver crashes, kernel oops, or unstable audio behavior that may require module unload or reboot.
- Memory corruption could, in theory, be developed into more powerful exploits (information disclosure or code execution) by sophisticated attackers who can control kernel heap layout and precisely craft trigger sequences; however, practical exploitation to arbitrary code execution is non‑trivial and requires more conditions than a straightforward crash. Treat those possibilities as plausible but speculative.
Exploit availability
- As of the documented advisories and community trackers, there were no widely published public exploits weaponizing this specific index mistake. That said, the bug is trivial to reason about for a local attacker with access to the device, and attackers targeting embedded fleets or multi‑tenant systems could weaponize it if they have foothold. Monitor threat feeds for any signs of active exploitation.
Detection, triage and forensics
Detection of exploitation or attempted triggers for this issue will typically show up as kernel-level errors and device driver traces:- Check dmesg and system journal for kernel oops traces referencing the sound ASoC stack or the WCD938x driver. Look for stack traces in sound/soc/codecs/wcd938x.c or crash lines near port_map or struct wcd938x_sdw_priv references. (mirrors.edge.kernel.org)
- Unexpected driver crashes, repeated restarts of audio services, or failures during suspend/resume on affected devices may indicate the bug was triggered.
- If you suspect exploitation, preserve kernel logs and, if possible, capture kdump/kernel core dumps for offline analysis before rebooting. Balance forensic needs with service availability; if hosts must be rebooted, collect logs first.
- Run: uname -r to find the running kernel version.
- Inspect: lsmod | grep wcd938x or look for module names and dmesg lines indicating the WCD938x codec is probed.
- Audit: review which devices and product SKUs in your fleet include Qualcomm WCD938x codecs (mobile, some embedded platforms).
- Monitor: set SIEM rules for kernel oops traces that include “wcd938x”, “snd_soc”, or suspicious NULL/dereference traces in the sound subsystem. (mirrors.edge.kernel.org)
Mitigation and remediation
Immediate steps (0–48 hours)
- Inventory affected systems:
- Identify hosts that have the WCD938x codec driver loaded or include the driver in their kernel builds.
- Prioritize devices with local user access, multi-tenant usage, or critical audio dependencies.
- Patch promptly:
- Install vendor/distribution kernel updates that include the upstream fix (stable kernel updates like 5.15.22 and corresponding backports have the commit). After patching, reboot to ensure the updated kernel is running. (mirrors.edge.kernel.org)
- If you cannot immediately patch:
- If audio functionality on the host is not required, consider disabling the codec module (blacklist) or disabling ALSA/ASoC interfaces temporarily to remove the attack surface. Note this is a blunt instrument and will break audio features.
Medium term (weeks)
- Apply vendor-supplied kernel updates across staging and production; ensure kernel packaging includes the stable commit (don’t rely solely on kernel version number if your vendor backports fixes differently).
- For embedded devices and appliances that rely on vendor kernels, request vendor firmware or kernel updates and validate fixes in test environments before mass rollout. Many embedded platforms are slow to receive backports—treat them as high-priority inventory items.
Long tail and hardening
- For long-lived appliances without easy update channels, consider compensating controls: restrict local access to maintenance interfaces, physically secure devices, or isolate equipment in network segments that reduce service exposure.
- Strengthen runtime protections (e.g., kernel hardening, address‑space protections) where available; these do not replace the fix but can raise the bar for exploitation complexity.
Vendor and distribution posture
- Kernel stable changelogs show the commit included in the 5.15.22 stable release and analogous entries for subsequent series; distributions that ship those kernels or that backport security fixes will publish advisories listing the patched package names and versions. Check your distribution’s security tracker for the exact package to install. (mirrors.edge.kernel.org)
- SUSE’s advisory marks the issue as resolved in their packaging and provides a distinct severity assessment that may differ from some third-party aggregators. Always treat your distribution’s bulletin as the authoritative remediation guidance for its kernels.
- Several vulnerability databases and security intelligence vendors summarized the issue and recommended updating to the fixes in the 5.15.22 / 5.16.8 / 5.17 series; these summaries are useful for triage but must be cross-checked against vendor package IDs and changelogs.
A developer’s view: why small fixes matter
From a systems-programming perspective this bug is a textbook example of lifetime/ID semantics mistakes: two integers live in the same binary space but carry distinct meanings; using one as if it were the other breaks invariants. The kernel device model and driver helper arrays require disciplined mapping between logical channel identifiers and actual hardware ports; tiny errors in that mapping ripple into memory-safety failures. The upstream patch is deliberately small—change the index derivation—and that surgical approach is why these fixes can be safely backported into stable branches. (mirrors.edge.kernel.org)For maintainers, the lesson is practical: rigorously document data layouts and ensure public-facing mixer or control registers are normalized into driver-internal indices before indexing arrays. Use defensive checks on array bounds and prefer safe helpers for lifecycle-managed objects. These simple engineering disciplines prevent small bugs from creating high-impact outages. (mirrors.edge.kernel.org)
Checklist for administrators (practical, prioritized)
- Inventory
- Run uname -r to determine kernel version.
- Search for module or boot messages: dmesg | grep -i wcd938x or lsmod | grep wcd938x.
- Patch
- Install your distro’s kernel update that includes the stable fix (for many, that’s the updates derived from 5.15.22 / 5.16.8 / 5.17 stable branches).
- Reboot hosts to activate the patched kernel.
- Mitigate (if you cannot immediately patch)
- Disable or blacklist the wcd938x module (note: breaks audio).
- Restrict local user access to prevent untrusted processes from interacting with ALSA controls.
- Monitor
- Add SIEM alerts for kernel oops messages referencing wcd938x or snd_soc.
- Watch for repeated audio driver crashes or failed suspend/resume cycles.
- Embedded device owners
- Contact OEM or device vendor for firmware/kernel updates.
- If the vendor cannot supply updates, consider shielding the device from untrusted local users and reduce its exposure in critical workflows. (mirrors.edge.kernel.org)
Final analysis and recommendations
CVE-2022-48716 is a concise, high‑value kernel correctness fix: a mistaken use of a channel id where a port id is required that can cause out-of-bounds indexing and driver state corruption in the WCD938x codec driver. The fix is small, was merged upstream, and has been backported into stable kernels—so the practical remediation is straightforward for most modern Linux distributions: update the kernel package and reboot. (mirrors.edge.kernel.org)Two important operational cautions:
- Do not assume every public CVE summary is correct about the attack vector or severity. Some automated feeds have misclassified the vector as network-remote and assigned very high CVSS numbers; the kernel context and distribution advisories point toward a local attack surface that requires the vulnerable driver to be present and invoked. Cross-check vendor advisories and the NVD entry when prioritizing patches.
- Embedded platforms and OEM kernels create the largest residual risk: devices that are rarely updated or that run vendor-pinned kernels can remain vulnerable long after upstream fixes exist. Those devices should be inventoried and treated as high-priority for vendor engagement or isolation plans.
Conclusion: the vulnerability underlines an enduring truth in systems software—small, semantic mistakes in low-level code can produce outsized operational risk. The upstream fix is short, correct, and backportable; the operational work is in finding every device that needs it and closing that long tail of unpatched, embedded exposures.
Source: MSRC Security Update Guide - Microsoft Security Response Center