A privilege‑escalation vulnerability in the QEMU Guest Agent for Windows — tracked as CVE‑2023‑0664 — allows a local, unprivileged user inside a Windows virtual machine to manipulate the QEMU Guest Agent installer’s repair custom actions and obtain SYSTEM privileges inside the guest; the issue was fixed upstream in QEMU 8.0.0‑rc0 via two targeted installer patches, but the bug’s mechanics and the remediation responsibilities span both guest administrators and virtualization stack maintainers. (bugzilla.redhat.com)
Virtualized environments rely on a small set of guest‑side services to provide cooperative features between host and guest. The QEMU Guest Agent (qemu‑ga) is one such component for Windows guests: it enables coordinated operations such as file copy, clean shutdowns, and integration with guest‑side utilities. Because it runs in the guest, the guest agent necessarily installs with elevated service permissions — which makes the security posture of its installer and any repair or maintenance flows critical. (lists.nongnu.org)
CVE‑2023‑0664 is not a hypervisor escape. It does not let a guest user break out into the host or other guests. Instead, the vulnerability is a classic local elevation of privilege (EoP) inside the guest: an attacker who already has an account in the Windows guest — even a standard, non‑administrator account — can misuse the Windows MSI repair functionality and the agent’s installer artifacts to run code as the SYSTEM user on that same guest. That elevated access is still high‑impact for defenders: SYSTEM can disable security controls, harvest credentials, and abuse virtualized host integration features for persistence and lateral movement. (bugzilla.redhat.com)
Put simply: an attacker with local user access could trigger an MSI repair that executed a command shell as SYSTEM via an installer custom action that lacked impersonation and invoked cmd.exe — a textbook privilege escalation through installer repair logic. The QEMU developers accepted the report, documented it upstream, and issued two coordinated patches addressing the installer behavior. (gitlab.com)
Remaining responsibilities include:
From a defensive perspective, the remediation is also straightforward: apply the upstream patches (or downstream vendor packages) that remove the repair UI vector and stop spawning interactive shells from installer custom actions. But because the vulnerable component lives inside the guest, remediation responsibilities are shared: guest owners must update, and virtualization operators must ensure that shipped images and templates are likewise fixed.
For organizations that operate many Windows guests across VDI, cloud, or lab fleets, the combination of easy local exploitation and high impact inside the guest elevates this CVE from a niche development bug to an important operational security item. Apply fixes, hunt for suspicious MSI repair activity, and treat SYSTEM compromise of guests as a high‑impact incident — even if the attack cannot escape the VM boundary. (bugzilla.redhat.com)
In short: CVE‑2023‑0664 is a local Windows guest privilege escalation through MSI repair custom actions in qemu‑ga; upstream fixes exist (two focused installer patches), downstream vendors published updates, and the correct defensive posture is to patch guest agents and hunt for installer‑repair activity that indicates attempted or successful abuse. (gitlab.com)
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
Virtualized environments rely on a small set of guest‑side services to provide cooperative features between host and guest. The QEMU Guest Agent (qemu‑ga) is one such component for Windows guests: it enables coordinated operations such as file copy, clean shutdowns, and integration with guest‑side utilities. Because it runs in the guest, the guest agent necessarily installs with elevated service permissions — which makes the security posture of its installer and any repair or maintenance flows critical. (lists.nongnu.org)CVE‑2023‑0664 is not a hypervisor escape. It does not let a guest user break out into the host or other guests. Instead, the vulnerability is a classic local elevation of privilege (EoP) inside the guest: an attacker who already has an account in the Windows guest — even a standard, non‑administrator account — can misuse the Windows MSI repair functionality and the agent’s installer artifacts to run code as the SYSTEM user on that same guest. That elevated access is still high‑impact for defenders: SYSTEM can disable security controls, harvest credentials, and abuse virtualized host integration features for persistence and lateral movement. (bugzilla.redhat.com)
What went wrong: the installer repair attack surface
The Windows Installer cache and repair custom actions
Windows Installer (MSI) keeps cached installation packages in C:\Windows\Installer and exposes a repair capability that can be invoked by msiexec to re‑run installer custom actions without a full reinstallation. That repair path is useful — and potentially dangerous — because MSI custom actions can be executed by elevated system contexts if the package and the action’s impersonation settings are misconfigured. In the case of the QEMU Guest Agent, the cached MSI and its repair actions provided an avenue for privilege escalation when the custom actions were executed under SYSTEM without proper impersonation checks. (bugzilla.redhat.com)The concrete mistakes in qemu‑ga.wxs
Red Hat’s Bugzilla entry and QEMU developer notes spell out the technical root cause in plain terms: the agent’s MSI defined repair custom actions named RegisterCom and UnregisterCom that were not configured for impersonation. In other words, a repair invocation could cause those actions to run as the SYSTEM account. The MSI also used cmd.exe to invoke qemu‑ga.exe in the custom action path; because qemu‑ga.exe is a console application, this launched an interactive shell under SYSTEM despite the MSI being marked non‑interactive — giving an attacker a powerful execution context to run arbitrary commands as SYSTEM. (bugzilla.redhat.com)Put simply: an attacker with local user access could trigger an MSI repair that executed a command shell as SYSTEM via an installer custom action that lacked impersonation and invoked cmd.exe — a textbook privilege escalation through installer repair logic. The QEMU developers accepted the report, documented it upstream, and issued two coordinated patches addressing the installer behavior. (gitlab.com)
How the upstream fixes changed the installer
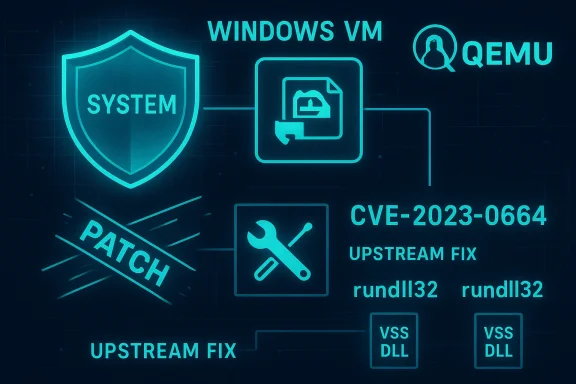
QEMU’s fixes were implemented as two focused commits (presented as a two‑part patch) that eliminate the installer pathways an attacker could abuse:- Remove the “Change” action from the MSI UI: the first fix removes the unnecessary change entry for the agent in Programs and Features, because the package doesn’t expose component selection and the change pathway could be invoked by non‑administrative users. Eliminating that entry avoids a UI vector that could start a repair or similar operation without appropriate checks. (gitlab.com)
- Replace cmd.exe calls with rundll32 wrappers for VSS DLL entry points: the second fix reworks the Volume Shadow Service (VSS) service install/uninstall path to call the installer code via rundll32.exe entry points rather than launching a command shell to run qemu‑ga.exe. Because the VSS operations are implemented in a DLL, calling the DLL directly avoids spawning an interactive console and reduces the privilege‑escalation risk. (gitlab.com)
Who is affected and how badly
- Affected software: the vulnerability affects Windows guests that have the QEMU Guest Agent (qemu‑ga) installed using the vulnerable MSI; multiple vendor distributions tracked the issue and released downstream patches. QEMU’s upstream metadata shows the issue was reported in February 2023 and fixed in the 8.0.0‑rc0 branch. (bugzilla.redhat.com)
- Attack vector: local — an attacker must already have a user account inside the affected Windows guest. This makes the bug a local EoP; it does not enable a remote attacker to penetrate a guest from the network unless they already have local execution. (bugzilla.redhat.com)
- Severity: multiple security catalogs assign a High impact severity with CVSS v3.1 base score in the high‑7 range (commonly 7.8), reflecting a low complexity, local attack that yields full confidentiality, integrity, and availability impacts inside the guest. Commercial and distribution advisories (SUSE, Red Hat, Oracle Linux) and databases (NVD, Rapid7) list the issue and concord on the severity profile.
- Real‑world risk: while the issue does not escape the VM boundary, its practical danger is straightforward. If an attacker can elevate to SYSTEM inside a guest, they can disable or tamper with endpoint protections, extract secrets, create persistent administrator accounts, and — depending on the environment — use guest‑side capabilities (for example, cloud guest tools or storage snapshots) to facilitate later stages of an intrusion. Because some managed cloud environments permit broad use of virtual‑to‑host integration, defenders must treat guest SYSTEM compromises as high‑impact incidents. (bugzilla.redhat.com)
Patching and remediation: what admins need to do now
The good news: upstream fixes exist and were applied to QEMU’s code base. The practical steps for administrators and security teams are layered and depend on whether you manage the host, the guest, or both.1) Update the QEMU guest agent in Windows guests (primary and urgent action)
- Install the fixed QEMU Guest Agent packages inside each Windows VM. Upstream QEMU commits were included in QEMU 8.0.0‑rc0; downstream OS vendors (Red Hat, SUSE, Oracle Linux, etc.) published advisories and packages referencing the CVE. If you manage images or templates with qemu‑ga installed, update those images and redeploy or patch actively running guests. (gitlab.com)
- If you rely on vendor images (cloud marketplace images or vendor virtualization appliances), check vendor security bulletins and apply their updated images or in‑place patches as provided. Distribution packaging teams tracked and rolled fixes into their respective releases.
2) Patch or update virtualization toolchains where appropriate
- If you maintain your own QEMU builds on hosts or in appliances, rebuild from or upgrade to a QEMU release that contains the upstream commits (look for the commits listed as fixes for CVE‑2023‑0664). The two installer changes are narrow and safe, but the only reliable remediation is to use software with the fixes merged. (gitlab.com)
3) Detection and hunting (immediate interim defenses)
While deploying fixes, use detection to identify attempts to exploit the repair flow:- Monitor for unexpected msiexec repair invocations originating from standard accounts or unexpected processes, and correlate such events with calls that spawn cmd.exe or qemu‑ga.exe under elevated contexts.
- Hunt for processes spawned from C:\Windows\Installer or for repair flows that result in a console process running as SYSTEM. Because the exploit relies on launching a console under SYSTEM, suspicious interactive shells from the installer cache are reliable indicators.
- Use endpoint telemetry to watch for abrupt privilege changes, new local accounts, service registration actions, or attempts to register/unregister COM components from non‑admin users. These behaviors are valuable triage signals when combined with MSI activity. (lists.nongnu.org)
4) Temporary mitigation if patching is impossible immediately (use with caution)
Some administrators will ask if it's feasible to mitigate by changing file permissions on the Windows Installer cache or removing the cached MSI. There are tradeoffs:- Tightening ACLs on C:\Windows\Installer to prevent non‑administrators from reading or executing cached MSI files can reduce the immediate attack surface, but it risks breaking legitimate installer/repair behavior and future updates delivered via the cached MSI.
- Removing or deleting the cached qemu‑ga MSI may prevent repair‑based exploits, but it may also render the product unrepairable and break servicing; do this only with careful change control and image backups.
- Any filesystem or ACL changes should be tested in non‑production VMs first. Where possible, prioritize applying the vendor patch over filesystem workarounds because the patch eliminates the vulnerable code path without undermining Windows Installer semantics. (gitlab.com)
Detection examples and forensic hints
Investigators and hunters should focus on a few telltale signs that map directly to the vulnerability’s mechanics:- MSI repair sequences (msiexec /f* or related repair flags) executed by non‑privileged users or occurring outside maintenance windows.
- Instances where msiexec’s repair actions lead to cmd.exe or rundll32.exe executing qemu‑ga.exe or other QEMU guest‑agent binaries. Note that after the upstream fix, VSS actions should use rundll32 wrappers rather than spawning cmd.exe; spotting cmd.exe launches tied to qemu‑ga indicates a pre‑patch binary or attempted exploitation. (gitlab.com)
- Unexpected registrations/unregistrations of COM classes originating from installer contexts, particularly where RegisterCom/UnregisterCom are invoked. MSI logs (Windows Installer verbose logs) and EDR process trees can reveal the parentage of such events.
- Creation of new services, changes to service registration, or sudden attempts to manipulate VSS components from user contexts that shouldn’t have permission. These actions are consistent with post‑escalation activity and should trigger containment. (bugzilla.redhat.com)
Broader implications and risk assessment
CVE‑2023‑0664 highlights several recurring themes in virtualization‑era security:- Supply‑chain parity: guest components (drivers, agents, tooling) often come from separate upstream projects and package ecosystems. Even if the host hypervisor is hardened, a vulnerable guest component can still produce catastrophic outcomes inside the VM.
- Installer logic is dangerous: MSI custom actions and installer repair flows are legitimate Windows features but have a long history of producing privilege escalation vectors when the authoring omits impersonation or misuses console‑mode programs in non‑interactive contexts.
- Attack surface overlaps: defenders must consider both the host‑side hypervisor attack surface and the guest’s local attack surface. A VM that is otherwise isolated from network threats can still be compromised by a local adversary or by compromised user accounts inside the guest.
What vendors and maintainers did — and what they still must do
Upstream QEMU accepted the vulnerability report, implemented the targeted fixes, and documented the changes in the project’s commit history. Distribution packaging teams mapped the upstream fixes into downstream packages and advisories; major vendor databases and security feeds (NVD, SUSE, Red Hat, Oracle Linux, and others) reflected the CVE and the recommended update actions. Administrators should rely on these vendor packages rather than attempting home‑grown source patches unless they are comfortable building and validating QEMU from source. (gitlab.com)Remaining responsibilities include:
- Ensuring cloud marketplace images and prebuilt templates incorporate the fixed qemu‑ga.
- Updating organizational imaging and build pipelines to remove vulnerable agent binaries from base images.
- Educating operations teams that previously accepted the “installer cache is sacrosanct” assumption — it isn’t safe to ignore cached installers in multi‑tenant or shared environments.
Checklist for IT and security teams (quick action list)
- Inventory: identify Windows guests running QEMU Guest Agent (qemu‑ga). Check image templates and active VMs. (bugzilla.redhat.com)
- Patch guests: update qemu‑ga in every Windows VM to a package that includes the CVE‑2023‑0664 fixes. Prefer vendor packages from your distribution or cloud provider. (gitlab.com)
- Patch hosts/tooling: if you build or ship QEMU yourself, upgrade host QEMU images and tools to releases that include the commits referenced for the fix. (gitlab.com)
- Hunt: search for msiexec repair activity tied to the qemu‑ga MSI, unexpected cmd.exe instances running as SYSTEM, and COM registration/unregistration events from installer contexts. (lists.nongnu.org)
- Harden access: reduce unnecessary user access to shared VMs and apply least privilege to user accounts. Consider temporary ACL hardening for C:\Windows\Installer only after validating the side effects. (bugzilla.redhat.com)
Caveats and unverifiable points
- The bug is well‑documented by upstream QEMU commits and Red Hat’s tracking entry; those are the authoritative technical sources for the fix and for the installer‑level root cause. The exact exploit tooling used in the wild — if any — and any active exploitation campaigns associated with this CVE were not documented in the upstream or vendor advisories we reviewed; defenders should not assume public weaponization without telemetry indicating exploitation in their environments. If you see signs of exploitation, treat the incident as urgent. (gitlab.com)
- Some downstream advisories may include additional contextual mitigations or packaging‑specific instructions beyond the upstream commits. Always follow the guidance of your OS vendor or cloud provider when applying packages in production environments. Where vendor guidance differs, prefer vendor‑issued instructions.
Final analysis: why this matters to Windows administrators
CVE‑2023‑0664 is a sober reminder that high‑privilege functionality exposed through installer pathways can be an Achilles’ heel for otherwise well‑configured virtual machines. The vulnerability’s exploitation path — abusing MSI repair custom actions that run without impersonating the calling user and that invoke console programs from the installer cache — is straightforward and conceptually avoidable with correct MSI authoring and minimal attack surface in the installer UI.From a defensive perspective, the remediation is also straightforward: apply the upstream patches (or downstream vendor packages) that remove the repair UI vector and stop spawning interactive shells from installer custom actions. But because the vulnerable component lives inside the guest, remediation responsibilities are shared: guest owners must update, and virtualization operators must ensure that shipped images and templates are likewise fixed.
For organizations that operate many Windows guests across VDI, cloud, or lab fleets, the combination of easy local exploitation and high impact inside the guest elevates this CVE from a niche development bug to an important operational security item. Apply fixes, hunt for suspicious MSI repair activity, and treat SYSTEM compromise of guests as a high‑impact incident — even if the attack cannot escape the VM boundary. (bugzilla.redhat.com)
In short: CVE‑2023‑0664 is a local Windows guest privilege escalation through MSI repair custom actions in qemu‑ga; upstream fixes exist (two focused installer patches), downstream vendors published updates, and the correct defensive posture is to patch guest agents and hunt for installer‑repair activity that indicates attempted or successful abuse. (gitlab.com)
Source: MSRC Security Update Guide - Microsoft Security Response Center