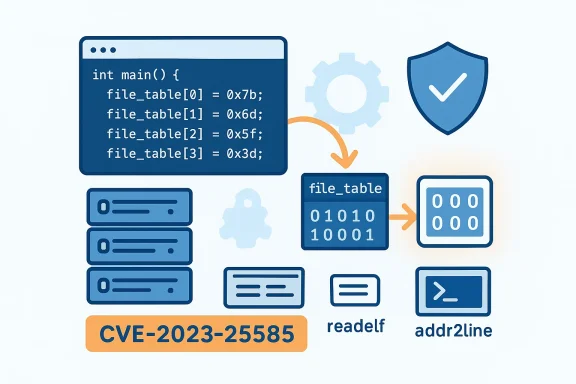
CVE-2023-25585 exposes a subtle, but operationally meaningful, uninitialized-variable bug in GNU Binutils: the field file_table in struct module could be left uninitialized, allowing crafted inputs or sequences to trigger application crashes and local denial-of-service conditions on systems that run the affected binutils code paths. This article unpacks the technical root cause, the patch, the real-world impact for developers and build environments, vendor responses, and a pragmatic remediation checklist for IT teams and developers who rely on Binutils in mixed Windows/Linux build pipelines.
Binutils is the standard GNU collection of binary utilities used on virtually every Unix-like developer toolchain: assemblers, linkers, objdump, readelf, addr2line and friends. Even though many distributions classify Binutils as a developer tool rather than a network-facing runtime, it processes untrusted or malformed object files during debugging, symbolization, and reverse-engineering tasks — making memory-safety and initialization bugs in its libraries (particularly libbfd) meaningful from an availability and reliability standpoint.
The Central Vulnerability Database (CVE-2023-25585) reports that an uninitialized field — file_table inside struct module — could be used in a way that leads to application crash and local denial of service. This is an availability-only issue (no confidential data exposure has been reported), but the ability to reliably crash developer tooling or automated build/CI processes is non-trivial for organizations that depend on those services. Multiple vendor advisories and the upstream patch confirm both the problem and the remediation approach. Ubuntu documents fixed package versions; the upstream commit rewrote allocation and reallocation code to guarantee zero-initialization of the table.
The problem is localized to Binutils’ module-parsing logic (the “module” here refers to a libbfd internal structure used by some object-file backends — the bug, as reported upstream, appears in the VMS alpha parser code path). The patch applied upstream replaces calls to non-zeroing allocators with zeroing allocators and adds an explicit memory-clear step when expanding the table. The upstream change is recorded in the Binutils mailing list/commit log and shows both the use of a zero-initializing allocator and a defensive memset for newly allocated table entries.
Note: different aggregators show slightly different numeric CVSS values (some list 4.7, others 5.5). This discrepancy is not uncommon when vendors or repositories supply their own vector strings or when NVD enrichment updates occur; treat the qualitative descriptors (Local / High availability impact / User interaction required) as the authoritative operational guidance and check vendor advisories for the exact vector string used in your environment.
---ty and vendors said — and how to interpret attestation
Vendor advisories for CVE-2023-25585 consistently acknowledge the bug and provide fixed packages. Distributors like Ubuntu and Debian published specific fixed package versions and issued security notices. Upstream maintainers documented the patch and code changes in the Binutils repository and associated mailing lists.
One recurring theme in vendor messaging for kernel and toolchain issues is product-scoped attestation — for example, some Microsoft advisories on Linux CVEs note that Azure Linux includes this open-source library and is therefore potentially affected, which is an inventory attestation rather than a blanket statement about all Microsoft products. When you see short vendor blurbs like that, treat them as useful inventory hints but verify whether your specific images or artifacts are covered. Internal artifact inventories and image scans are the only way to be certain about exposure in multi-vendor environments. The community discussion and internal attestation practices make this point repeatedly.
The patch is small and uncontroversial: ensure zero-initialization and safe reallocation semantics. Vendors and distributions have shipped updates, and upstream documentation and commits show the exact change made to guarantee deterministic initialization. For most organizations the correct, defensible response is: patch build and analysis hosts, rebuild images, and treat toolchain packages as part of your production vulnerability lifecycle.
Finally, remember that developer tools are a legitimate attack surface in modern, automated development pipelines. CVE-2023-25585 is a reminder: robustness and initialization correctness in low-level libraries matter — not just for security researchers, but for operational reliability across the entire software supply chain.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
Binutils is the standard GNU collection of binary utilities used on virtually every Unix-like developer toolchain: assemblers, linkers, objdump, readelf, addr2line and friends. Even though many distributions classify Binutils as a developer tool rather than a network-facing runtime, it processes untrusted or malformed object files during debugging, symbolization, and reverse-engineering tasks — making memory-safety and initialization bugs in its libraries (particularly libbfd) meaningful from an availability and reliability standpoint.The Central Vulnerability Database (CVE-2023-25585) reports that an uninitialized field — file_table inside struct module — could be used in a way that leads to application crash and local denial of service. This is an availability-only issue (no confidential data exposure has been reported), but the ability to reliably crash developer tooling or automated build/CI processes is non-trivial for organizations that depend on those services. Multiple vendor advisories and the upstream patch confirm both the problem and the remediation approach. Ubuntu documents fixed package versions; the upstream commit rewrote allocation and reallocation code to guarantee zero-initialization of the table.
What went wrong: the technical root cause
The defect in plain terms
At the heart of CVE-2023-25585 is a classic C-language mistake: an allocated array of structures was not zero-initialized, and code later assumed unused entries started in a zero (NULL) state. When those entries were read or partially filled without explicit initialization, the code could dereference uninitialized pointers or otherwise act on garbage values, producing undefined behavior and, in practical terms, program crashes.The problem is localized to Binutils’ module-parsing logic (the “module” here refers to a libbfd internal structure used by some object-file backends — the bug, as reported upstream, appears in the VMS alpha parser code path). The patch applied upstream replaces calls to non-zeroing allocators with zeroing allocators and adds an explicit memory-clear step when expanding the table. The upstream change is recorded in the Binutils mailing list/commit log and shows both the use of a zero-initializing allocator and a defensive memset for newly allocated table entries.
Why uninitialized memory matters here
- Assumptions in legacy code: Existing code assumed newly allocated table slots were zeroed; this assumption is fragile across allocator APIs and refactors.
- Structured metadata: File tables and symbol tables in libbfd carry pointers and string references; uninitialized entries are especially dangerous because pointer garbage can lead to invalid pointer dereference or to interpretation of attacker-controlled memory as a filename.
- Fuzzing and crafted inputs: Object-file parsing is frequently targeted by fuzzers and adversaries; malformed DWARF or relocation records can trigger code paths that exercise table growth and file table assignments, making the bug practical to trigger on a local system.
Impact and exploitability: availability-focused but practical
Scoring and vendor assessments
Vulnerability scoring across sources varies slightly — CVSSv3 values published by different vendors place the issue in the Medium range with the following general characteristics: local attack vector, no required privileges, user interaction required, and an availability impact. The National Vulnerability Database (NVD) and multiple distro trackers mark the flaw as a correctness/uninitialized-variable issue that primarily affects availability. Some vendor notices (Ubuntu, Debian trackers and distribution advisories) publish concrete fixed versions and pragmatic remediation guidance.Note: different aggregators show slightly different numeric CVSS values (some list 4.7, others 5.5). This discrepancy is not uncommon when vendors or repositories supply their own vector strings or when NVD enrichment updates occur; treat the qualitative descriptors (Local / High availability impact / User interaction required) as the authoritative operational guidance and check vendor advisories for the exact vector string used in your environment.
What an attacker can do
- Cause an application crash of Binutils tools (addr2line, readelf, objdump, etc.) by supplying crafted object or debug files.
- Trigger denial-of-service conditions in local developer machines, CI runners, or packaging/build pipelines that rely on Binutils to process object artifacts.
- Repeated or automated exploitation can turn a low-severity local bug into a persistent availability problem for build infrastructure.
Exploitability in real environments
While the flaw requires local access to a machine or a service that runs binary-processing tasks, many enterprise environments run Binutils inside:- centralized build services and CI runners,
- shared developer containers,
- automated symbolization services for crash logs,
- debuggers and crash-analysis tools on developer workstations.
Upstream fix and vendor responses
The upstream patch
The upstream fix (committed by a Binutils maintainer) took a simple, robust approach:- Replace non-zeroing allocators with zero-initializing allocators when creating the file_table array.
- When the table is expanded, explicitly zero the newly allocated slots to avoid leaving residual data uninitialized.
- Simplify the reallocation logic to ensure deterministic initialization regardless of growth patterns.
Distribution patches and advisories
Multiple Linux distributions and tracking services published advisories and fixed package versions:- Ubuntu published a security notice listing the fixed binutils package versions across supported releases and provided a USN entry describing which Ubuntu releases were affected and which packages were updated. Ubuntu’s advisory is explicit about the fixed versions and recommended updates.
- Debian’s security tracker marks the issue and lists fixed upstream package releases and the version that includes the patch.
- SUSE, Red Hat and other vendors listed the flaw and treated it as a moderate/medium severity problem for developer toolchain packages, with appropriate package updates.
Detecting and verifying exposure in your environment
If you run Linux systems (especially build servers, CI runners, or developer workstations), verify exposure using these checks:- Check installed Binutils package version:
- Debian/Ubuntu: run apt list --installed binutils or dpkg -l binutils and compare to the fixed versions indicated in vendor advisories.
- RHEL/Fedora/SUSE: use rpm -q binutils and consult the vendor security advisory for fixed RPM versions. (access.redhat.com)
- Identify services that call Binutils tools automatically:
- CI runners that run addr2line, objdump, readelf or other binutils invocations as part of artifact processing.
- Crash-symbolization services or automated log-processing containers.
- Review rebuild or image pipelines:
- Container images that include binutils may inherit vulnerable versions; catalog images and rebuild with updated packages where necessary.
- Check for presence of repo artifacts with suspicious object/DWARF data:
- Repositories that accept uploaded or generated object files, packages or debug symbols could be an attack vector when their processing is automated.
- Look for crash patterns:
- If you see repeated crashes in addr2line/readelf invoked by your builds or symbolization services, correlate timestamps and filenames with the processing code path and consider isolating the artifact for analysis.
Practical remediation and mitigation steps
Because this CVE is fixed upstream and by major distributors, the fastest path to safety is to patch and, where feasible, rebuild dependent images. Here’s a prioritized action plan for operators and developers.Immediate actions (first 24–72 hours)
- Patch build hosts and developer images: Apply vendor-released binutils updates. On Ubuntu/Debian systems run a standard package update (apt update && apt upgrade) and verify the installed binutils version matches the fixed version reported in the security notice.
- Isolate automated processing: If you cannot immediately patch, isolate services that automatically process untrusted object files (CI runners, symbolization daemons). Restrict their access to only trusted repositories or run them inside isolated VMs or containers with strict resource limits.
- Add runtime resource guards: Use container / process-level limits to prevent a single crash from taking down shared services — for example, restart policies, per-job cgroups and hardened service supervision.
- Harden artifact ingestion: Introduce validation gates for uploaded artifacts where possible. For symbolization and analysis services, require artifacts to come from authenticated sources, and scan artifacts in sandboxed environments prior to bulk processing.
Medium-term actions (1–4 weeks)
- Rebuild images and containers: Recreate CI images and base containers with patched binutils and redeploy runners. If your images are immutable, this is a mandatory step.
- Update package blacklists/allowlists in automation: Ensure your automation uses package repositories with security updates enabled and pinned to safe versions for reproducible builds.
- Audit build logs: Search retained logs for addr2line/readelf crashes or unusual object-processing errors correlated with untrusted inputs.
Long-term actions (quarterly strategy)
- Treat developer toolchain as part of your attack surface: Add build tools like Binutils to your vulnerability management scope — track advisories and enforce timely updates for toolchain packages in build environments.
- Segment build infrastructure: Separate trusted production build runners from general-purpose developer runners. Apply stricter controls where untrusted inputs are accepted.
- Introduce fuzzing and hardening into the pipeline: If you run large-scale symbolization or binary-processing services, consider integrating fuzz testing for your internal pipelines and run libbfd-based code under memory sanitizers during development of the service.
Risk analysis: why a “developer tool” CVE matters
It’s tempting to deprioritize vulnerabilities in development-only packages, but that would miss the real operational risk vectors:- Shared infrastructure amplification: A single vulnerable binutils instance used by a cloud-based debugger or CI runner can impact dozens or hundreds of downstream builds and teams.
- Supply-chain exposure: Repositories that accept artifacts (for example, debug symbol uploads) may inadvertently accept crafted inputs that cause downstream processing to fail or to degrade service availability.
- Automation friction: Repeated availability issues in build tools translate to developer downtime and reduced productivity, and can force rushed, error-prone mitigations.
Detection signatures and monitoring recommendations
There is no simple network signature for CVE-2023-25585 because the exploit is triggered by crafted local artifacts. However, you can monitor the following to detect attempted exploitation or recurring instability:- Service logs for repeated addr2line/readelf/objdump crashes or exit codes.
- CI job failure burst patterns tied to artifact processing steps.
- Kernel oops or coredumps on build hosts correlated to objdump or readelf processes.
- Unusual artifact submissions in repositories that feed symbolization services.
---ty and vendors said — and how to interpret attestation
Vendor advisories for CVE-2023-25585 consistently acknowledge the bug and provide fixed packages. Distributors like Ubuntu and Debian published specific fixed package versions and issued security notices. Upstream maintainers documented the patch and code changes in the Binutils repository and associated mailing lists.
One recurring theme in vendor messaging for kernel and toolchain issues is product-scoped attestation — for example, some Microsoft advisories on Linux CVEs note that Azure Linux includes this open-source library and is therefore potentially affected, which is an inventory attestation rather than a blanket statement about all Microsoft products. When you see short vendor blurbs like that, treat them as useful inventory hints but verify whether your specific images or artifacts are covered. Internal artifact inventories and image scans are the only way to be certain about exposure in multi-vendor environments. The community discussion and internal attestation practices make this point repeatedly.
Final recommendations — an operational checklist
- Patch: Upgrade binutils on build hosts, CI images, developer images and symbolization servers to the fixed versions listed by your distribution. Confirm the installed package version matches vendor guidance.
- Isolate: If immediate patching isn’t possible, isolate automated artifact-processing services and apply strict resource and execution limits.
- Rebuild: Recreate container images and immutable artifacts that include binutils to ensure all deployed runners use patched images.
- Audit: Search for recent addr2line/readelf crashes in logs; verify artifacts processed in the window before fixes were applied.
- Harden: Add binutils and related toolchain packages to your vulnerability management and image-build policies. Treat toolchain CVEs as an expected operational risk for CI/CD infrastructure.
- Monitor: Alert on abnormal crash frequencies of binary-processing tools and collect artifact provenance for any processing failures.
- Educate: Inform developer teams that crafted object files can cause crashes in processing tools — require artifact validation where appropriate.
Closing analysis: scale the response to risk, not the CVSS number
CVE-2023-25585 is conceptually straightforward — an un es — and the upstream fix is surgical and low-risk. But the operational consequences scale with how broadly and automatically Binutils is used in your environment. If you maintain centralized CI, symbolization services, or shared developer images, this vulnerability deserves fast remediation even if it is a local, availability-only issue.The patch is small and uncontroversial: ensure zero-initialization and safe reallocation semantics. Vendors and distributions have shipped updates, and upstream documentation and commits show the exact change made to guarantee deterministic initialization. For most organizations the correct, defensible response is: patch build and analysis hosts, rebuild images, and treat toolchain packages as part of your production vulnerability lifecycle.
Finally, remember that developer tools are a legitimate attack surface in modern, automated development pipelines. CVE-2023-25585 is a reminder: robustness and initialization correctness in low-level libraries matter — not just for security researchers, but for operational reliability across the entire software supply chain.
Source: MSRC Security Update Guide - Microsoft Security Response Center