Microsoft’s short public mapping that “Azure Linux includes this open‑source library and is therefore potentially affected” is an important and accurate inventory statement — but it is not a categorical guarantee that no other Microsoft product can contain the same vulnerable Linux kernel code. erview
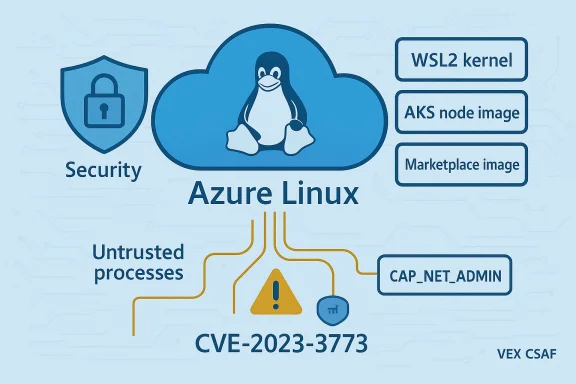
CVE‑2023‑3773 is a moderate‑severity Linux kernel vulnerability in the XFRM (IPsec transformation) subsystem that can cause a four‑byte out‑of‑bounds read of the XFRMA_MTIMER_THRESH netlink attribute during attribute parsing. The defect can be triggered by a local actor with CAP_NET_ADMIN privileges and may result in leakage of small amounts of kernel heap data to user space. This is a local information‑disclosure issue rather than a remote code‑execution or straightforward denial‑of‑service vulnerability.
The Microsoft Security Response Center (MSRC) entry you quoted uses a concise, product‑scoped attestation: Azure Linux (the Microsoft distribution formerly known as CBL‑Mariner used for many cloud images) includes the implicated upstream kernel component and is therefore potentially affected. Microsoft has also communicated, through its CSAF/VEX rollout, that it will expand VEX/CSAF mappings if additional Microsoft products are later found to ship the same upstream component. That programmatic approach to attestation is part of MSRC’s tranat launched machine‑readable VEX attestations starting in October 2025.
This article explains what the MSRC wording actually means, why Azure Linux being named is not the same as an exclusivity statement, how the vulnerability maps into real Microsoft artifacts (kernels, images, and containers), and how operators and incident responders should triage, detect, and remediate risk across an enterprise with mixed Microsoft and Linux distributions.
Multiple independent analyses and community commentary make the same point: the Azure Linux attestation means “known affected” for Azure Linux and “not yet attested” for others — not “not affected.” Treating the absence of attestations as evidence of absence is risky.
Externally maintained distro and vendor advisories (Ubuntu, Red Hat, Debian, Oracle, Amazon Linux, etc.) list CVE‑2023‑3773 as a kernel fix in their kernel packages. Several cloud kernels and distribution kernels etplaces (for example linux‑azure kernels used in Ubuntu’s cloud builds) were explicitly patched as part of common upstream Linux kernel rollups. That demonstrates the underlying kernel code touched by CVE‑2023‑3773 is widely distributed beyond any single vendor, including Microsoft’s cloud kernel variants. (ubuntu.com)
Examples of Microsoft artifacts that could plausibly contain the same kernel code:
Source: MSRC Security Update Guide - Microsoft Security Response Center
CVE‑2023‑3773 is a moderate‑severity Linux kernel vulnerability in the XFRM (IPsec transformation) subsystem that can cause a four‑byte out‑of‑bounds read of the XFRMA_MTIMER_THRESH netlink attribute during attribute parsing. The defect can be triggered by a local actor with CAP_NET_ADMIN privileges and may result in leakage of small amounts of kernel heap data to user space. This is a local information‑disclosure issue rather than a remote code‑execution or straightforward denial‑of‑service vulnerability.
The Microsoft Security Response Center (MSRC) entry you quoted uses a concise, product‑scoped attestation: Azure Linux (the Microsoft distribution formerly known as CBL‑Mariner used for many cloud images) includes the implicated upstream kernel component and is therefore potentially affected. Microsoft has also communicated, through its CSAF/VEX rollout, that it will expand VEX/CSAF mappings if additional Microsoft products are later found to ship the same upstream component. That programmatic approach to attestation is part of MSRC’s tranat launched machine‑readable VEX attestations starting in October 2025.
This article explains what the MSRC wording actually means, why Azure Linux being named is not the same as an exclusivity statement, how the vulnerability maps into real Microsoft artifacts (kernels, images, and containers), and how operators and incident responders should triage, detect, and remediate risk across an enterprise with mixed Microsoft and Linux distributions.
 What CVE‑2023‑3773 actually is — technical snapshot
What CVE‑2023‑3773 actually is — technical snapshot
The vulnerable code path
The bug sits in the Linux kernel’s XFRM netlink handling. When user space requests or dumps certain XFRM structures over netlink, the kernel parses netlink attributes (nlattrs) such as XFRMA_MTIMER_THRESH. Improper length or bounds checking in that parser allows a four‑byte read beyond the intended attribute buffer. The result is a small information leak — a read of heap bytes that should not be disclosed to unprivileged users. The condition is reachable only by processes with CAP_NET_ADMIN.Exploitability and impact
- Attack vector: local. An attacker needs CAP_NET_ADMIN (or an equivalent privileged capability).
- Impact: confidentiality (small kernel heap disclosure). Not a remote root exploit by itself.
- Severity: commonly scored as medium (CVSS v3 ~5.5 in several advisories), reflecting local access and limited data leakage.
How Microsoft’s Azure Linux attestation should be read
Product‑scoped attestation, not product‑exclusive guarantee
When MSRC writes “Azure pen‑source library and is therefore potentially affected,” the statement does three things:- Confirms Microsoft has inventory‑checked the Azure Linux distribution and found the upstream component present in the artifacts MSRC examined.
- Signals that customers running Azure Linux images should treat those images as in‑scope and apply the vendor patches or mitigation guidance provided.
- Promises Microsoft will update the CVE/VEX mapping if other Microsoft products are later found to ship the same upstream code.
Multiple independent analyses and community commentary make the same point: the Azure Linux attestation means “known affected” for Azure Linux and “not yet attested” for others — not “not affected.” Treating the absence of attestations as evidence of absence is risky.
Why Microsoft focuses first on Azure Linux
Azure Linux is Microsoft’s own Linux distro used to build many cloud images, and it represents a tractable first surface for VEX/CSAF attestation: a single product family, with a manageable build pipeline and package list, makes it feasible to generate definitive, machine‑readable mappings quickly. MSRC made the deliberate choice to crawl / walk / run — validating their processes before broad expansion. That is a transparency and operational control decision, not a technical statement that other Microsoft artifacts cannot include the same upstream code.Where the ambiguity comes from — real examples
Several recent CVE pages use identical MSRC FAQ language that mirrors the quote you supplied: it emphasizes Azure Linux as the product Microsoft inspected while promising to expand mappings if it finds more carriers. You can see the same phrasing repeated across Microsoft CVE entries and in archived MSRC pages for other Linux kernel CVEs. That repetition drives confusion: many readers assume Microsoft named the only affected Microsoft product, when the actual meaning is narrower.Externally maintained distro and vendor advisories (Ubuntu, Red Hat, Debian, Oracle, Amazon Linux, etc.) list CVE‑2023‑3773 as a kernel fix in their kernel packages. Several cloud kernels and distribution kernels etplaces (for example linux‑azure kernels used in Ubuntu’s cloud builds) were explicitly patched as part of common upstream Linux kernel rollups. That demonstrates the underlying kernel code touched by CVE‑2023‑3773 is widely distributed beyond any single vendor, including Microsoft’s cloud kernel variants. (ubuntu.com)
Is Azure Linux the only Microsoft product that includes the vulnerable code?
Short, practical answer: No — *noLinux is the only Microsoft product MSRC has publicly attested to include the implicated open‑source component for this CVE at the time of its advisory, but that attestation does not guarantee exclusivity. Any Microsoft product that ships a Linux kernel build containing the same XFRM subsystem source files or compiled modules could also include the vulnerability until that artifact is explicitly attested as Not Affected or Fixed.Examples of Microsoft artifacts that could plausibly contain the same kernel code:
- Azure Marketplace Linux VM images that include vendor kernels or Microsoft‑built cloud kernels (linux‑azure).
- WSL2/Windows Subsystem for Linux kernel images distributed by Microsoft (they include a Microsoft‑built Linux keernetes Service (AKS) node images that derive from Azure‑published images or use Microsoft‑provided kernel builds.
- Any container host images, custom images, or managed offerings that embed an Azure Linux kernel or a kernel binary compiled from the same upstream commit set.
How security teams should treat Microsoft’s attestation (practical guidance)
Triage checklist — immediate steps
- Identify Azure Linux hosts and images in your environment. If you run Azure Linux images, treat them as known in‑scope and apply vendor updates promptly. MSRC’s attestation is definitive for that product family.
- Inventory all Microsoft‑distributed Linux artifacts you use: WSL2 kernel images, Azure Marketplace VM images, AKS node images, custom images built from Microsoft base images. Treat each artifact as a distinct binary and check whether it contains the vulnerable kernel or a patched kernel version.
- Cross‑reference vendor advisories and distribution CVEs (Ubuntu, Debian, Red Hat, Oracle, Amazon Linux) for kernel package updates that address CVE‑2023‑3773; these advisories often indicate which kernel releases were patched and which cloud kernels (linux‑azure, linux‑aws) were impacted.
Detection approaches
- Binary/version checks: identify the kernel version and vendor package release on each host. Compare against distribution advisories (for example, the Ubuntu USN notices or NVD entry) to determine whether the kernel has the upstream fix applied.
- Build‑time provenance: for Microsoft artifacts, check the published SBOM/CSAF/VEX artifact (where available) to see whether MSRC has published a “Known Affected / Fixed / Not Affected” status for that product. MSRC’s VEX files (once produced for a product) are machine‑readable and can be integrated into automation.
- Runtime indicators: because this is an OOB read in netlink handling, runtime detection is non‑trivial; look for anomalous netlink activity from untrusted processes or unexpected CAP_NET_ADMIN usage patterns. Use Linux auditing (auditd) to monitor privileged netlink calls and consider restricting CAP_NET_ADMIN where feasible.
Mitigation if patching is delayed or infeasible
- Principle: reduce the attack surface. This vulnerability requires CAP_NET_ADMIN. Restrict tainers and service accounts wherever possible.
- For containers: drop CAP_NET_ADMIN capability in container runtime configurations and use network namespaces with least privilege.
- For multi‑tenant hosts: enforce stricter isolation and host‑level controls, prefer kernel patches as the long‑term fix.
- Use defense‑in‑depth: network segmentation, stronger workload isolation (gVisor, Kata Containers), and host hardening reduce the likelihood that a local capability will be abused to escalate or exfiltrate sensitive kernel memory.
Why per‑artifact verification matters (a short supply‑chain lesson)
Open‑source kernel code is copied, configured, and compiled in many ways across distributions and cloud vendors. Small differences in kernel configuration, enabled drivers, or compile‑time flags can cause a given CVE to exist or not in a particular binary. Microsoft’s Azure Linux attestation is the first step in applying supply‑chain transparency to this problem: it tells you which named product family Microsoft has validated. But other Microsoft artifacts — WSL kernels, marketplace images, AKS node images — are independent build artifacts and must be verified separately. Treat the VEX/CSAF mapping as a helpful, authoritative data point for the named product, not as a blanket global statement about all Microsoft‑controlled Linux artifacts.Cross‑referenced evidence (what I checked and why it matters)
- NVD and distribution advisories provide canonical technical descriptions for CVE‑2023‑3773 and list affected kernel packages and kernel releases; these are primary references for CVE details and severity.
- Ubuntu and other distribution security notices (USN entries) explicitly list linux‑azure builds among the cloud kernels patched in December 2023, showing that cloud‑optimized kernel builds used by major cloud providers were part of the patch rollouts. That corroborates the notion that cloud vendor kernels (including Microsoft’s linux‑azure variants) can carry the same upstream code.
- MSRC’s public blog and its VEX/CSAF rollout statement explain the rationale behind starting with Azure Linux and promise future mapping expansion; this is key to understanding Microsoft’s process and the meaning of per‑product attestations.
- Internal/third‑party commentary and forum analysis (the uploaded file collection you provided) repeatedly emphasize: “Azure Linux is attested; absence of attestations for other Microroof they’re unaffected.” Those artifacts are useful because they reflect security‑ops expectations and real customer questions; I used them to interpret the MSRC wording in operational terms.
Risk analysis — what this means for different environments
Cloud tenants (Azure VM customers)
If you run Microsoft Azure Marketplace images that are built from or include Azure Linux artifacts, treat those images as in‑scope immediately and apply the vendor‑provided kernel updates. If you run third‑party images on Azure, consult the image vendor and your cloud‑cataloot assume the MSRC Azure Linux attestation covers non‑Microsoft or third‑party images.Kubernetes / AKS customers
AKS node images often use base images or kernels supplied or curated by Microsoft. If you use managed AKS node pools, verify whether the AKS node image includes the Azure Linux kernel or another patched kernel build. Microsoft’s VEX/CSAF outputs (when extended to AKS artifacts) should give precise status; until then, apply distro kernel updates and restrict CAP_NET_ADMIN in pods via PodSecurityPolicies or the equivalent admission controls.WSL2 and developer machines
Microsoft distributes a WSL2 kernel binary for Windows hosts. That kernel is a Microsoft‑built Linux kernel and therefore could contain the same upstream code unless explicitly patched. WSL users should monitor MSRC attestations and Microsoft’s WSL release notes, and update the WSL2 kernel when Microsoft releases a patched package. Do not assume the Azure Linux attestation covers WSL kernels.On‑prem corporate servers
If you run Azure‑branded or Microsoft‑supplied images on‑prem (for example, images you obtained through Microsoft channels), check those images’ kernel versions and their SBOMs where available. Otherwise, follow the distribution advisories (Ubuntu, Debian, Red Hat, etc.) for kernel package security updates.Recommendations — a prioritized checklist
- Patch Azure Linux instances immediately using the vendor update channel MSRC mapped to the CVE. MSRC’s attestation makes those images high‑priority.
- Inventory all Microsoft‑distributed Linux artifacts in use (WSL kernels, AKS nodes, Marketplace images) and compare kernel versions against vendor advisories and MSRC VEX/ach artifact as a separate item for verification.
- Where patching is impractical, drop CAP_NET_ADMIN for untrusted workloads and containers; use container capability whitelisting to reduce exploitation surface. ([clouddefense.ai](CVE-2023-3773: Linux Kernel XFRM Vulnerability VEX/CSAF machine‑readable outputs into your vulnerability triage automation (once available for your artifact families). This reduces false positives and automates the per‑artifact decision logic.
- For incident responders: treat evidence of local netlink attribute parsing by untrusted or unexpected processes as a higher‑priority investigation trigger while you confirm kernel versions. Use auditd, seccomp logs, and container runtime logs to triage suspicious CAP_NET_ADMIN usage.
Notable strengths and remaining risks in Microsoft’s approach
Strengths
- Transparent attestation model: Moving to machine‑readable CSAF/VEX is a real operational improvement. A single, authoritative VEX file per product reduces ambiguity about what Microsoft has inspected and what remains unverified.
- Focused, pragmatic rollout: Starting with Azure Linux allows Microsoft to validate processes and build automation before expanding to many product families — a sensible crawl / walk / run approach that reduces early errors in SBOM/VEX publication.
- Clear customer guidance for attested products: For products Microsoft has inspected, the attestation is a firm, actionable signal to cation priority.
Risks and limitations
- Per‑artifact uncertainty remains: Until MSRC expands VEX to other Microsoft artifacts, customers must assume non‑attested Microsoft artifacts are “not yet verified” rather than “not affected.” That creates operational burden for large, heterogeneous estates.
- Automation gap during rollout: Many organizations cannot immediately consume VEX/CSAF files if their vulnerability management tooling or SBOM pipelines are immature; this may slow uptake of the benefits VEX promises.
- Potential for human misinterpretation: Short MSRC FAQ blurbs are useful but also easy to misread as exclusivity claims. This is already causing confusion in community discussions and support tickets. The root cause is a mismatch between concise security advisory wording and the nuanced reality of software supply chains.
What I could not verify (cautionary notes)
- MSRC’s specific per‑artifact coverage for every Microsoft product at the present moment was not exhaustively verifiable from a single public listing. MSRC has committed to expanding VEX/CSAF where necessary; until those per‑product VEX files exist, the exact scope across all Microsoft artifacts remains an operational unknown and must be treated as such by defenders.
Conclusion — practical takeaway for operators
Microsoft’s advisory that “Azure Linux includes this open‑source library and is therefore potentially affected” is an authoritative signal for Azure Linux customers: patch Azure Linux now. But that statement is a scoped, product‑level inventory attestation — not a proof that no other Microsoft product can carry the same vulnerable XFRM code. Security teams must therefore:- Treat Azure Linux as known in‑scope and remediate per vendor guidance.
- Inventory and verify other Microsoft artifacts on a per‑artifact basis (WSL kernels, AKS node images, Marketplace images). Do not assume absence of a VEX attestation means absence of vulnerability.
- Use capability restriction (drop CAP_NET_ADMIN), container hardening, and runtime auditing as immediate mitigations when prompt patching is not possible.
Source: MSRC Security Update Guide - Microsoft Security Response Center