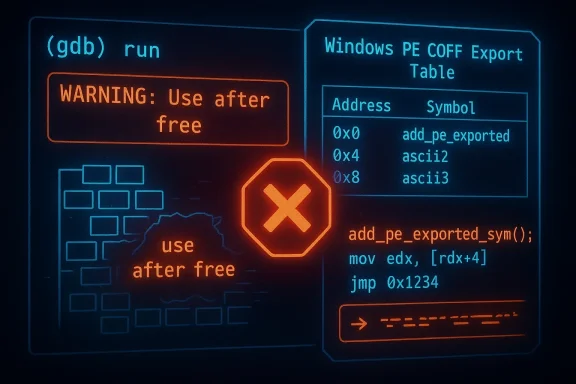
The discovery of CVE-2023-39129 — a heap use‑after‑free in GNU Debugger (GDB) located in the PE/COFF reader path — is a textbook reminder that even long‑standing, developer‑only tools can become operational hazards when they parse untrusted inputs. The bug, traced to the function add_pe_exported_sym() in gdb/coff-pe-read.c, can be triggered when GDB processes specially crafted PE/COFF export information and may cause the debugger to crash or otherwise become unavailable; multiple vulnerability databases assign a Medium severity but agree that the primary impact is on availability rather than confidentiality or integrity.
GDB is the de facto debugger for GNU toolchains and is used across Linux distributions, in build farms, continuous integration (CI) pipelines, reverse‑engineering environments, and occasionally by developers who debug Windows PE files on cross‑platform toolchains. The vulnerable code resides in the PE/COFF reader — the component that allows GDB to parse Windows‑format binaries — specifically inside the routine that ingests exported symbol records. When that code path mishandles memory lifetimes, a use‑after‑free occurs: code continues to dereference memory that has already been returned to the allocator. This class of flaw is well understood to produce crashes and, under fortunate attacker conditions, enable further memory corruption impacts.
From published records, the affected upstream snapshot is identified as GDB 13.0.50.20220805‑git. Public advisories and vulnerability databases first recorded the flaw in late July 2023 and consolidated the technical description through the latter half of 2023. Several independent vulnerability databases and vendor advisories reference the same root cause and point to the Sourceware/GDB bug tracking entry associated with this issue.
In this GDB bug, the immediate observable effect is a crash when the problematic path is exercised, which translates to a denial of service against the debugging session or any automated process that depends on GDB to parse a PE/COFF file. Memory corruption beyond a crash is technically possible but depends on fragile runtime conditions; public statements emphasize availability impact foremost while treating remote code execution as speculative.
However, the attack surface increases in mixed development shops where cross‑platform debugging is routine — for example when a Linux developer opens a Windows executable sent by a colleague, or when a developer debugs a Windows binary under Wine. In those cases, a maliciously crafted binary supplied via email, repo, or artifact could trigger the crash when opened in GDB.
If patching is not immediately possible, apply the following mitigations to reduce risk:
Note: vendor scoring differences are intentional and reflect product context. For example, a distribution may assign a lower product severity if they assess that typical packaging or runtime constraints reduce exploitability; this is not a contradiction of the upstream technical description but a product‑scoped assessment. Always treat the upstream technical description as authoritative for the code defect and use vendor advisories to shape remediation urgency in your environment.
CVE‑2023‑39129 is not a theoretical footnote; it is a practical reminder that tools we trust to inspect and debug binary artifacts are themselves software and must be treated with the same patching discipline we apply to runtime services. Inventory your GDB usage, patch aggressively where pipelines and sandboxes process untrusted files, and isolate any remaining instances until they are updated. The combination of vendor advisories, centralized vulnerability databases, and targeted operational mitigations provides a clear, achievable path to neutralize the availability risk this defect represents.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
GDB is the de facto debugger for GNU toolchains and is used across Linux distributions, in build farms, continuous integration (CI) pipelines, reverse‑engineering environments, and occasionally by developers who debug Windows PE files on cross‑platform toolchains. The vulnerable code resides in the PE/COFF reader — the component that allows GDB to parse Windows‑format binaries — specifically inside the routine that ingests exported symbol records. When that code path mishandles memory lifetimes, a use‑after‑free occurs: code continues to dereference memory that has already been returned to the allocator. This class of flaw is well understood to produce crashes and, under fortunate attacker conditions, enable further memory corruption impacts.From published records, the affected upstream snapshot is identified as GDB 13.0.50.20220805‑git. Public advisories and vulnerability databases first recorded the flaw in late July 2023 and consolidated the technical description through the latter half of 2023. Several independent vulnerability databases and vendor advisories reference the same root cause and point to the Sourceware/GDB bug tracking entry associated with this issue.
Technical analysis
What a use‑after‑free means in practice
A use‑after‑free (CWE‑416) happens when a program frees (deallocates) a memory object and later continues to use a pointer to the freed region. The actual hazard depends on allocator behavior and process memory layout: the freed memory may still hold the original data for a short time, it may be immediately reallocated for another purpose, or it may be overwritten — each scenario produces different attack outcomes.In this GDB bug, the immediate observable effect is a crash when the problematic path is exercised, which translates to a denial of service against the debugging session or any automated process that depends on GDB to parse a PE/COFF file. Memory corruption beyond a crash is technically possible but depends on fragile runtime conditions; public statements emphasize availability impact foremost while treating remote code execution as speculative.
Where the call path lives and who can reach it
- The vulnerable function is triggered in the code that reads exported symbols from PE/COFF objects. That means the attack vector requires that GDB open or inspect a Windows binary or object file whose export table has been crafted to exercise the faulty code path.
- The attack vector is local in the standard scoring: an attacker must persuade a user or a process that runs GDB to open the malicious file, or must have local access to the host running an automated GDB‑driven analysis service. The Common Vulnerability Scoring System (CVSS) vector recorded by NVD and other sources reflects Local/Low complexity/User interaction semantics.
How security databases rate the risk
Different vendors and databases apply different scoring methodologies and sometimes arrive at different numeric severity values. Notable entries:- NVD and several aggregators list a CVSSv3.1 Base Score 5.5 (Medium), emphasizing High impact to availability while confidentiality and integrity are rated None.
- Some platform vendors that maintain their own advisories (for example distribution teams) may list a lower effective severity for their packaging contexts, e.g., Amazon Linux ALAS shows a vendor‑specific score that reflects product scope and mitigations. Differences do not negate the underlying defect; they reflect product‑scoped risk assessments.
Practical impact: who should care
Individual developers and workstations
For most desktop developers who use GDB to debug local code (compiled from source on Linux) and who do not open foreign PE/COFF files, the direct risk is low. The vulnerability requires parsing a specially crafted Windows binary to reach the faulty export‑symbol path.However, the attack surface increases in mixed development shops where cross‑platform debugging is routine — for example when a Linux developer opens a Windows executable sent by a colleague, or when a developer debugs a Windows binary under Wine. In those cases, a maliciously crafted binary supplied via email, repo, or artifact could trigger the crash when opened in GDB.
CI/build systems, automated analysis, and malware sandboxes
The real operational risk surfaces where GDB is used in automated pipelines that ingest untrusted binaries:- Continuous integration servers that perform debug‑level symbol extraction or binary analyses (for example to generate stack traces or symbol maps) may use GDB headlessly.
- Malware analysis sandboxes and automated triage systems often rely on debugging utilities to inspect PE export tables and symbol layouts. Such systems may be exposed to a steady stream of malformed binaries crafted by threat actors.
Supply chain and targeted attack considerations
While the bug is not a remotely exploitable service vulnerability (the attack requires local execution or user action), attackers who control an artifact delivery channel — compromised open‑source packages, tainted build artifacts, or misleading pull requests — can weaponize a crafted PE binary to cause disruption. In high‑stakes environments, that disruption can have ripple effects across testing, release automation, and incident response pipelines, especially where GDB is a component of automation templates.Remediation and mitigation: immediate steps
The core remediation is straightforward: update to a GDB release that includes the upstream fix or apply the upstream patch and rebuild the package for your environment. Multiple distributors and downstream products have incorporated fixes or provided vendor advisories referencing the vulnerability.If patching is not immediately possible, apply the following mitigations to reduce risk:
- Avoid opening untrusted PE/COFF binaries in GDB. Treat PE files from unknown sources as untrusted artifacts and process them in isolated sandboxes.
- Where possible, run GDB‑based parsing steps in containers or ephemeral VMs that are isolated from critical CI infrastructure.
- In automated pipelines that analyze binaries, add input validation or filtering to block malformed export tables or to prefer safer parsing libraries when symbol extraction is the only required function.
- Limit privilege for the GDB process: avoid running debugging or analysis agents as privileged users; drop capabilities and enforce least privilege.
- Add monitoring and alerting for repeated GDB crashes in automated systems — a spike in crashes often indicates input‑based exploitation attempts.
- If you build GDB from source, consider enabling memory safety tooling during testing (ASan/UBSan) in development builds to catch regressions early, though note these tools are not a runtime mitigation for production workloads.
Recommended patching action list (ordered)
- Inventory: Identify all systems where GDB is installed — developer workstations, CI agents, analysis sandboxes, and vendor appliances that bundle GDB.
- Confirm version: Check installed GDB versions and match against the affected snapshot(s) — e.g., upstream snapshot 13.0.50.20220805‑git and downstream package versions that incorporate that code.
- Prioritize: Immediately patch automated systems and sandboxes that process untrusted PE artifacts; schedule developer workstation updates based on exposure.
- Apply fixes: Update packages from your distribution vendor (preferred) or rebuild GDB from a patched upstream tree if necessary.
- Validate: After updating, run representative test suites and exercise PE parsing paths to ensure the fix is effective and no regressions are introduced.
- Monitor: Continue monitoring crash rates and vendor advisories for follow‑up patches or additional mitigations.
Fix availability and vendor responses
Upstream and several downstream vendors recorded fixes or advisories after the public disclosure. Some vendors integrated the upstream patch in routine package updates; others issued product‑scoped advisories indicating which shipped products or appliance versions were impacted. Because GDB is packaged and redistributed in many Linux distributions and specialized products, remediation timelines vary by vendor. Where you rely on vendor packages, prefer the vendor update channel rather than ad‑hoc upstream rebuilds to ensure compatibility with your distro’s packaging and security backports.Note: vendor scoring differences are intentional and reflect product context. For example, a distribution may assign a lower product severity if they assess that typical packaging or runtime constraints reduce exploitability; this is not a contradiction of the upstream technical description but a product‑scoped assessment. Always treat the upstream technical description as authoritative for the code defect and use vendor advisories to shape remediation urgency in your environment.
Critical analysis — strengths, limitations, and real‑world risk
Clear strengths in the response ecosystem
- The vulnerability was recorded and cataloged by multiple independent sources quickly after disclosure; that breadth of coverage helps administrators find vendor‑specific guidance and correct packages for remediation. Registries and security vendors aggregated the same technical root cause and highlighted the availability impact, giving teams consistent data to act upon.
- Because the attack requires either local access or convincing a user/process to open a malicious file, standard operational controls (sandboxing, least privilege, artifact provenance checks) are effective mitigations while patches are rolled out.
Practical limitations and residual risks
- The primary limitation is distribution and deployment inertia. GDB ships widely and may be embedded in appliances or custom analysis stacks where package updates are not applied daily. Those environments can remain vulnerable for an extended period unless administrators actively inventory and patch.
- Automated ingestion systems and CI infrastructures are particularly sensitive: a single tainted input source can repeatedly crash services and, if not contained, may produce operational downtime. The denial‑of‑service nature of the vulnerability makes it attractive for low‑cost disruption in targeted campaigns.
- Although current public materials emphasize availability and treat remote code execution as speculative, memory corruption bugs historically evolve as researchers and attackers discover new exploitation chains. Over time, what begins as a crash‑only bug can, under very specific allocator and control‑flow conditions, be extended into a higher‑impact primitive. Organizations should not treat "no RCE seen" as permanent.
Likelihood of widespread exploitation
Multiple vulnerability trackers show low EPSS or exploitability predictions for this CVE, reflecting its local/user interaction attack vector and the requirement to supply a crafted PE file to vulnerable GDB instances. That indicates a low probability of mass broad exploitation across the internet, but a meaningful risk in high‑value, targeted scenarios (for instance when attackers deliberately supply crafted artifacts to a build pipeline used by many projects). Distribution and vendor advisories remain the best indicators of exploitation in the wild; at time of reporting, there were no public widespread exploit campaigns focused on this CVE.For security teams: detection and response playbook
- Detection:
- Watch for increases in GDB process crashes or core dumps on systems that process or debug PE files.
- In CI pipelines, instrument tasks that call GDB to emit structured logs when they crash; correlate spikes with incoming artifact sources.
- Response:
- Isolate affected CI agents or analysis sandboxes when repeated crashes are observed, and triage individual offending artifacts in an isolated VM.
- If an untrusted artifact caused a crash, treat the source as suspicious until proven otherwise and run malware‑analysis best practices.
- After patching, re‑run a set of known‑good samples and the problematic artifact in a controlled environment to confirm remediation.
- Long‑term:
- Harden build and test infrastructure so that tools which parse untrusted binaries run in disposable, ephemeral agents with minimal permissions.
- Consider replacing fragile parsing steps with dedicated, well‑maintained libraries or services that have stronger input‑validation guarantees if PE parsing is a regular requirement.
Key takeaways and final recommendations
- The defect in add_pe_exported_sym() is a credible, exploitable use‑after‑free that primarily yields denial of service against the GDB process; it is not, by published evidence, a mass‑remote code execution vector. Still, the potential for more serious memory corruption exists under specific runtime conditions.
- Prioritize patching and remediation for hosts where GDB processes untrusted PE/COFF files: automated analysis sandboxes, CI/build hosts that accept external artifacts, and any production appliances that embed GDB for binary inspection. Desktop developer machines that never open PE files are lower priority but should still follow normal patch cycles.
- Use containment and least‑privilege controls as immediate mitigations: sandbox GDB usage, avoid running it as a privileged service, and restrict exposure to untrusted inputs. Combine those operational mitigations with a plan to deploy vendor or upstream patches.
- Finally, maintain a posture that accepts memory‑safety bugs can evolve: treat "crash only" vulnerabilities as high enough priority to patch in automation contexts, because the operational impact (sustained or persistent denial of availability) can be severe even without demonstrated remote code execution.
CVE‑2023‑39129 is not a theoretical footnote; it is a practical reminder that tools we trust to inspect and debug binary artifacts are themselves software and must be treated with the same patching discipline we apply to runtime services. Inventory your GDB usage, patch aggressively where pipelines and sandboxes process untrusted files, and isolate any remaining instances until they are updated. The combination of vendor advisories, centralized vulnerability databases, and targeted operational mitigations provides a clear, achievable path to neutralize the availability risk this defect represents.
Source: MSRC Security Update Guide - Microsoft Security Response Center