Microsoft’s short advisory that “Azure Linux includes this open‑source library and is therefore potentially affected” is accurate — but it is a product‑scoped inventory statement, not a categorical guarantee that no other Microsoft product can include the same vulnerable Go library.
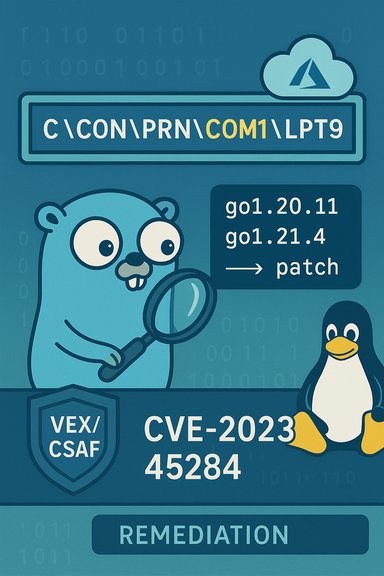
CVE‑2023‑45284 is a vulnerability in the Go standard library’s path/filepath package (the IsLocal function) that causes certain Windows reserved device names to be misclassified as “local.” The bug manifests when names such as COM1 with trailing spaces or the strings COM and LPT followed by certain superscript characters are treated as ordinary file names instead of special device names; that can lead to incorrect path handling and logic errors in programs that rely on IsLocal for security decisions. The upstream Go project fixed the bug in the Go releases that started with go1.20.11 and go1.21.4; operators are therefore advised to update builds that were compiled with vulnerable toolchains. Microsoft’s MSRC advisory (the short paragraph quoted by the user) states that Azure Linux “includes this open‑source library and is therefore potentially affected” and notes that Microsoft began publishing machine‑readable CSAF/VEX attestations and will update the CVE if additional Microsoft products are identified. That language is important because it reflects what Microsoft has inventory‑checked and attested so far, not a blanket exclusion for every other Microsoft product or artifact.
This article explains, in plain but technical terms, what CVE‑2023‑45284 is, why the MSRC wording matters, which Microsoft artifacts are plausible carriers of the vulnerable Go code, what practical remediation and triage steps teams should take, and what the attestation process means — including the strengths and the latent risks of the current approach.
For the core technical facts about the vulnerability and the fix, consult authoritative vulnerability trackers and the Go project advisory: the IsLocal fix and the fixed releases are documented in the Go project and CVE/NVD/OSV trackers — update builds to go1.20.11 or go1.21.4 (or later) where appropriate and rebuild any affected binaries that may run on Windows. Microsoft’s attestation model is a useful step toward clearer vendor transparency; it materially helps customers running the named product (Azure Linux) to take decisive action. But the operational burden — verifying all other artifacts, rebuilding static binaries, and scanning WSL/Marketplace/agent fleets — still sits with engineering and security teams. Treat the VEX/CSAF attestation as a high‑quality signal for the product it names, and use aggressive artifact inventory and SBOM tooling to reduce the “unknowns” that remain across a heterogeneous estate.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CVE‑2023‑45284 is a vulnerability in the Go standard library’s path/filepath package (the IsLocal function) that causes certain Windows reserved device names to be misclassified as “local.” The bug manifests when names such as COM1 with trailing spaces or the strings COM and LPT followed by certain superscript characters are treated as ordinary file names instead of special device names; that can lead to incorrect path handling and logic errors in programs that rely on IsLocal for security decisions. The upstream Go project fixed the bug in the Go releases that started with go1.20.11 and go1.21.4; operators are therefore advised to update builds that were compiled with vulnerable toolchains. Microsoft’s MSRC advisory (the short paragraph quoted by the user) states that Azure Linux “includes this open‑source library and is therefore potentially affected” and notes that Microsoft began publishing machine‑readable CSAF/VEX attestations and will update the CVE if additional Microsoft products are identified. That language is important because it reflects what Microsoft has inventory‑checked and attested so far, not a blanket exclusion for every other Microsoft product or artifact.This article explains, in plain but technical terms, what CVE‑2023‑45284 is, why the MSRC wording matters, which Microsoft artifacts are plausible carriers of the vulnerable Go code, what practical remediation and triage steps teams should take, and what the attestation process means — including the strengths and the latent risks of the current approach.
What CVE‑2023‑45284 actually is
The technical bug in brief
- The vulnerable code lives in Go’s standard library package path/filepath, specifically in the IsLocal helper.
- On Windows, certain strings represent legacy device interfaces (for example CON, PRN, AUX, NUL, COM0..COM9, LPT0..LPT9). The OS treats those strings specially no matter where they appear in a path.
- The IsLocal function historically failed to correctly recognize some variants of those reserved names — for example, device names followed by trailing spaces or unusual superscript characters — and therefore incorrectly classified them as normal file names.
- The fix normalizes and recognizes those edge forms so that IsLocal returns “non‑local” for those names on Windows and programs that rely on IsLocal are no longer misled.
Affected versions and scope
- Affected Go versions include releases before go1.20.11 and before go1.21.4 (the fixed releases). Systems or binaries built with toolchains in those ranges are potentially vulnerable if the resulting program runs on Windows and exercises code paths that depend on IsLocal.
- Importantly, this vulnerability is platform‑specific in its effect: it only produces the problematic Windows semantics when the program runs on Windows. Binaries built and run exclusively on Linux/macOS are not impacted by the Windows device‑name semantics. However, cross‑compiled or multi‑platform deployments and container images that are later run on Windows are relevant to an organization’s exposure profile.
Reading Microsoft’s phrasing: “Azure Linux includes this open‑source library and is therefore potentially affected”
What an MSRC product attestation means
Microsoft’s short advisory about Azure Linux is an explicit, machine‑readable attestation: it documents that Microsoft has inspected the Azure Linux product artifacts, found the third‑party component (in this case, the Go standard library or a Go runtime), and therefore treats that product as potentially affected for the CVE in question. That attestation is useful and authoritative for Azure Linux — operators running those images can prioritize patching based on Microsoft’s statement.What the attestation does not mean
- It does not mean Microsoft has scanned every single Microsoft product, image, container, or binary and verified they do not contain the component.
- It does not prove that other Microsoft SKUs — such as WSL2 kernels or Marketplace images, packaged VMs, agent logic, or statically linked Go binaries inside other Microsoft services — are free of the vulnerable code.
- In short, absence of a VEX/CSAF attestation for a given Microsoft product is absence of evidence, not evidence of absence. Microsoft’s own wording commits to updating the CVE and VEX/CSAF output if additional products are identified. That is a procedural promise to expand coverage, not an exclusionary technical statement.
Which Microsoft products and artifacts could plausibly carry the vulnerable Go code?
Even though Azure Linux is the only Microsoft product explicitly attested so far (per Microsoft’s advisory), there are multiple plausible artifact classes that could include the same open‑source library or a binary compiled with a vulnerable Go toolchain:- Azure Linux images (attested) — Microsoft has checked and confirmed these images include the vulnerable component and therefore flagged them. Treat their VEX/CSAF attestation as authoritative for those images.
- Windows Subsystem for Linux (WSL) — Microsoft publishes and ships WSL kernels and has previously shipped userland artifacts. If any WSL userland or distribution image was built with a vulnerable Go toolchain or includes a bundled Go runtime using the affected path/filepath behavior, WSL‑hosted processes on Windows could be impacted. WSL kernels and images are separate artifacts that require independent inventory.
- Azure VM image families (linux‑azure, Marketplace images) — Microsoft maintains multiple kernel and image lines for Azure VMs; those builds may differ in configuration and packaged components. Any image that embeds a vulnerable Go runtime or packages a vulnerable binary could be a carrier.
- Managed service components and cloud agents — Microsoft agents, telemetry components, and containerized services could include statically linked Go binaries or vendor builds compiled with the affected toolchain. These are artifact‑level concerns and must be checked individually.
- Third‑party or partner Marketplace appliances that rely on Microsoft images or include Microsoft‑supplied components in their build pipeline could also be indirectly affected.
- Statically linked or embedded Go binaries — a binary built with an older, vulnerable Go release carries the vulnerability regardless of the runtime OS, but the faulty behavior only manifests on Windows due to device name semantics. Still, if those binaries are later run on Windows systems, they become relevant risk points.
Practical triage and remediation checklist (for IT / Security teams)
Below is a prioritized, actionable runbook to triage and remediate exposure across mixed environments that include Microsoft‑provided artifacts.- Inventory first — identify candidate artifacts and hosts.
- Query package manifests, SBOMs, and distribution package versions for Go and for user binaries that embed Go runtimes.
- For VMs and containers, run commands to detect the Go toolchain or binaries (for example, check package lists, run go version where available, inspect binary file metadata).
- Prioritize Azure Linux images (authoritative Microsoft attestation).
- If you run Azure Linux images, update them to the patched Go packages or apply vendor updates from Microsoft/Azure images immediately. Microsoft’s VEX/CSAF attestation is an authoritative signal for Azure Linux.
- Check Windows hosts that run Go‑based services (including services migrated from Linux).
- Any Go binary that has the path/filepath dependency and runs on Windows should be considered for rebuild with patched Go releases (>= go1.20.11 or >= go1.21.4 as applicable).
- Inspect WSL and developer fleets.
- WSL instances and developer machines are frequent vectors where old toolchains persist. Verify WSL distributions and any developer images for vulnerable Go versions.
- For containerized apps, rebuild images with patched Go releases.
- Rebuild and redeploy containers using fixed Go toolchains; do not assume base images on Linux are safe just because the bug’s bad path only shows up on Windows — containers may be run on Windows Server/containers or exported to different environments later.
- Apply compensating controls while you patch.
- Where immediate patching or rebuilds are not possible, consider network isolation, application‑level filters, or reducing attack surfaces (for example, block endpoints that accept arbitrary path components from untrusted clients).
- Monitor Microsoft’s CVE entry and VEX/CSAF feed for updates.
- Microsoft has committed to update the CVE and VEX output if additional products are identified; track those updates for newly attested Microsoft artifacts.
A short command‑level checklist (examples your ops team can run)
- Detect Go runtime on Linux/VM images:
- 1) rpm/apt list: check for golang package versions (example: apt list --installed | grep golang).
- 2) Identify Go binaries: find / -type f -executable -exec file {} \; | grep -i go
- Detect binaries compiled with Go (simple heuristics):
- 1) strings <binary> | grep -i 'go1.' or look for the module build information.
- On Windows, list running services built with Go or inspect deployed binaries:
- 1) Use Sysinternals or file metadata inspection to identify Go-compiled executables.
- For containers, inspect Dockerfiles and base images for "golang" lines and ensure base images are rebuilt with patched Go releases.
Why Microsoft’s attestation model is a meaningful improvement — and where it falls short
Strengths
- Deterministic, machine‑readable signals. Microsoft’s adoption of CSAF/VEX‑style attestations gives customers a clear, automatable answer for the product artifacts Microsoft has checked — when Microsoft says a product is “known affected,” that signal can drive automated triage and orchestration. This reduces noisy false positives in large estates.
- Operational clarity for Azure Linux customers. For teams that run Azure Linux images, Microsoft’s public statement is an immediate “patch this” directive backed by a vendor attestation.
- Commitment to expand coverage. Microsoft has stated it will update CVE/VEX entries if more products are identified. That procedural promise improves the vendor’s accountability and transparency posture.
Risks and gaps to be aware of
- Phased inventory leaves un‑attested products in an “unknown” bucket. Large vendors ship many artifacts and there will always be a window between CVE disclosure and complete product mapping. During that window, critical products can remain un‑attested and operators must assume the unknown artifacts could be affected.
- Static linking and embedded runtimes complicate triage. A Go binary shipped as a static executable or embedded inside another product doesn’t appear in package inventories the same way a distribution package does; it requires binary inspection and SBOM work to find. Microsoft’s attestation covers product images it inventoried, not every embedded binary shipped across the company.
- Customers must still do artifact‑level verification. Vendor attestations help but do not replace the need for each organization to perform their own inventory and SBOM‑driven verification of images and binaries they run. Treat the vendor attestation as one authoritative signal among several; do not let it replace active verification and monitoring.
Quick mythbusters
- Myth: “If MSRC only names Azure Linux, nothing else at Microsoft can be affected.”
Fact: Microsoft’s attestation names the products they have checked so far; it is not a promise that other Microsoft products are clean. Absence of attestation does not equal proof of absence. - Myth: “Only Linux users should care because the Go code is in Linux distributions.”
Fact: The underlying bug is about Windows device name semantics — it only triggers when the binary runs on Windows. But many artifacts (containers, VMs, WSL, cross‑platform apps) can move between platforms; rebuilds and patching are needed in any environment where the executable may later be run on Windows.
How to apply this to your Microsoft footprint — a prioritized checklist
- If you run Azure Linux images: treat Microsoft’s attestation as authoritative and apply the vendor‑provided updates now.
- If you run WSL at scale (developer fleets, CI runners): check WSL kernels and bundled userland images for Go versions and rebuild or update if needed.
- If you maintain Marketplace images or Microsoft VM images: verify whether your image uses a Go runtime or includes prebuilt Go binaries; rebuild images with patched Go releases where necessary.
- For application teams that ship binaries: enforce a build policy that uses patched Go toolchains and integrate SBOM generation to make future triage simpler.
- For security teams: add the CVE and vendor VEX/CSAF feed to your automation rules and mark Azure Linux as high priority for this CVE while you verify other artifacts.
Conclusion — the short, operational answer
No, Azure Linux is not necessarily the only Microsoft product that could include the vulnerable path/filepath library and be impacted by CVE‑2023‑45284. It is, however, the only Microsoft product Microsoft has publicly attested as including the component so far — and that attestation is authoritative for Azure Linux images. Absence of additional attestations is not the same as proof other Microsoft artifacts are unaffected; teams must inventory and verify other Microsoft images (WSL kernels, marketplace images, agent binaries, and any statically linked Go executables) until Microsoft expands its VEX/CSAF coverage or until artifact inspection proves the binary is patched.For the core technical facts about the vulnerability and the fix, consult authoritative vulnerability trackers and the Go project advisory: the IsLocal fix and the fixed releases are documented in the Go project and CVE/NVD/OSV trackers — update builds to go1.20.11 or go1.21.4 (or later) where appropriate and rebuild any affected binaries that may run on Windows. Microsoft’s attestation model is a useful step toward clearer vendor transparency; it materially helps customers running the named product (Azure Linux) to take decisive action. But the operational burden — verifying all other artifacts, rebuilding static binaries, and scanning WSL/Marketplace/agent fleets — still sits with engineering and security teams. Treat the VEX/CSAF attestation as a high‑quality signal for the product it names, and use aggressive artifact inventory and SBOM tooling to reduce the “unknowns” that remain across a heterogeneous estate.
Source: MSRC Security Update Guide - Microsoft Security Response Center