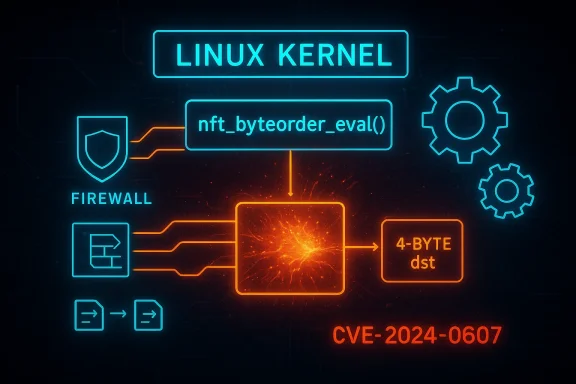
A subtle pointer‑math mistake in the Linux kernel’s Netfilter nf_tables code — tracked as CVE‑2024‑0607 — lets a local actor corrupt internal data by writing eight bytes into a four‑byte slot inside nft_byteorder_eval(), producing memory corruption that leads to kernel instability and reliable denial‑of‑service (DoS) conditions against packet‑filtering functionality.
Background
nf_tables is the modern Netfilter packet‑filtering engine used by Linux distributions to implement firewall rulesets, sets, maps, and complex packet‑processing expressions. The subsystem exposes a VM‑like evaluation engine that operates on typed registers and data values; expressions such as nft_byteorder are used to manipulate endianness and byte ordering inside rules. Because nftables executes in kernel context and touches networking‑critical structures, even small logic errors can quickly become crash primitives or, in rarer cases, escalation vectors.In January 2024 a pointer math bug was assigned CVE‑2024‑0607 after maintainers discovered that nft_byteorder_eval() could write 8 bytes into a destination buffer declared as an array of u32 (4‑byte elements). Each loop iteration overwrote half of the prior element, corrupting the register array and allowing a local user with the ability to trigger the expression to crash the kernel or break Netfilter operations. The vulnerability was classified as medium severity with a CVSSv3 score clustered around 6.1–6.6 depending on vendor assessment.
What the bug actually is: a plain‑English technical summary
- The vulnerable function, nft_byteorder_eval(), iterates over bytes and writes converted values into a destination array named
dst. The surrounding code expectsdstto contain 32‑bit words (u32). - The flawed logic performs 64‑bit writes (8 bytes) into
dston each pass, butdst’s elements are only 4 bytes. The result is predictable overwriting of adjacent elements and corruption of the internal register array used by nftables. - Because nftables runs in kernel mode and the corrupted data is used later in packet filtering operations, the corruption commonly manifests as kernel oopses, panic, or persistent failure of Netfilter state — effectively a local Denial‑of‑Service.
How maintainers fixed it (and where to find the fix)
Upstream kernel maintainers applied a targeted patch that corrects the pointer arithmetic and ensures the code writes the correct element size todst. The fix was merged into the stable trees and backported by multiple vendors to distribution kernels; Debian, SUSE, Amazon Linux and others list fixed package versions in their security trackers. The upstream commit is referenced in vendor advisories and the official vulnerability records.Two independent, authoritative attestations covering the same facts are:
- The National Vulnerability Database (NVD), which describes the root cause and impact.
- Distribution security trackers (for example, Debian’s tracker) that list the fixed package versions and link to the kernel commit used for remediation.
Affected systems and distribution status
The vulnerability was reported upstream and subsequently tracked by vendor advisories. The scope and availability of fixes vary by kernel series and distribution:- Debian lists fixed versions across its supported suites and shows the specific patched kernel packages and backports for older kernels. Operators running Debian kernels should upgrade to the fixed package versions identified in the tracker.
- Enterprise vendors and mainstream distributions (Red Hat, SUSE, Ubuntu, Amazon Linux) reported fixes and issued patches for the affected kernel series; many backported the correction into long‑term kernel branches used in enterprise releases.
- The upstream kernel commit that resolves the issue is present in the stable trees referenced by vendor advisories; maintainers indicated the change is present as of the 6.7‑rc2 lineage and in multiple backport commits for older stable series.
Exploitation scenarios and operational risk
The immediate risk from CVE‑2024‑0607 is availability‑first: a remote attacker cannot exploit it directly to run code, but a local attacker can reliably cause kernel crashes or persistent Netfilter disruption. Consider the following realistic attack chains:- Container misuse: An unprivileged container that has been granted networking capabilities (for example, CAP_NET_ADMIN or a user namespace that permits privileged nftables operations) could be used by a container user to feed crafted rules or expressions into nftables that hit nft_byteorder_eval(). This could crash the host kernel or make the host’s firewall nonfunctional.
- Multi‑tenant hosts: Shared build or CI workers hosting untrusted jobs sometimes allow temporary network namespace creation. If those worker jobs are able to load or manipulate nftables state, an attacker can weaponize that ability to induce continuous system instability and deny service to other tenants.
- Local privilege escalation chains (indirect): While CVE‑2024‑0607 itself is not an LPE (local privilege escalation) in published advisories, memory corruption bugs in kernel networking code historically have been combined with other flaws or misconfigurations to elevate impact; defenders should assume exploitation could be a stepping stone in complex attack chains where local code execution paths are present. This is especially true on systems where kernel hardening is inconsistent.
Detection, screening and immediate mitigations
If you cannot apply a kernel update immediately, prioritize the following mitigations in order of operational feasibility:- Identify hosts with exposed nftables evaluation surface. Search for:
- Active nftables rules that use byteorder conversions or complex expressions.
- Running containers with CAP_NET_ADMIN or unprivileged user namespaces enabled.
- Hardening measures that reduce the attack surface:
- Disable unprivileged user namespace cloning where not needed (kernel.unprivileged_userns_clone = 0). This prevents many containerized local attacks from creating the conditions necessary to exploit nftables expressions. Note that disabling user namespaces can break some container workflows.
- Remove CAP_NET_ADMIN from untrusted workloads and avoid granting nftables‑manipulation capability to multi‑tenant services.
- Runtime detection:
- Monitor kernel logs for repeated nftables oops messages or stack traces referencing nft_byteorder_eval or nft_eval paths.
- Configure crash dump collection (kdump) so that kernel oopses can be triaged and used to confirm exploit attempts.
- As a short‑term emergency control, consider isolating hosts that cannot be patched from sensitive traffic or moving workloads to patched hosts. This is conservative but effective in limiting blast radius.
Patching strategy and vendor guidance
A robust patching plan for CVE‑2024‑0607 should include:- Inventory: enumerate kernels across your estate and identify those whose vendor / kernel package versions are listed as vulnerable in distribution trackers. Use the vendor bulletin to map CVE to package names.
- Test: validate the patched kernel in a staging environment that mirrors your production network stack, particularly any nftables rulesets, container networking overlays, or custom nft expressions. Because nftables is central to firewalling, regressions from kernel upgrades can have outsized impact — test thoroughly.
- Rollout:
- Prioritize edge and gateway hosts first (firewalls, NAT gateways, load balancers), then virtualization and container hosts.
- Consider vendor livepatching where available to avoid full reboots for kernel updates; many enterprise distributions provide livepatch solutions for high‑availability infrastructure.
- Verification: after patching, monitor for recurrence of kernel logs, nftables errors, or unexplained reboots. Confirm that identical crash signatures no longer occur.
Why this matters — analysis and context
Several contextual points explain why a pointer math problem like CVE‑2024‑0607 merits attention beyond its “medium” severity label:- Kernel networking code is shared infrastructure. A single unstable firewall host can interrupt entire services. Vulnerabilities that allow reliable local DoS against Netfilter therefore have a high operational impact even if they’re not remotely exploitable.
- Containers and modern orchestration platforms increase the attack surface for "local" kernel bugs. Workloads that once ran on single‑tenant hosts now live in multi‑tenant clusters where an unprivileged job may have just enough capability to trigger nftables paths. The boundary between local and remote exploitation is blurred in cloud infrastructures.
- The nft_byteorder area has been the source of multiple kernel fixes in successive years; complexity in the expression evaluation and register handling has historically been a rich source of out‑of‑bounds reads/writes when combined with uninitialized registers or malformed user input. While CVE‑2024‑0607 is a pointer math bug, it sits inside a class of kernel bugs that administrators should monitor closely.
Potential risks and caveats
- Not every system is likely exploitable in practice. Exploitation typically requires the ability to craft or influence nftables expressions or rule state, which many hardened systems restrict to administrators. Nevertheless, environments that permit dynamic rulesets, containerized CI runners, developer machines, or untrusted jobs should be treated as at risk.
- Public advisories do not indicate an active, public exploit for CVE‑2024‑0607 at the time of vendor disclosures. That said, disclosure of a reliable crash primitive often leads to rapid proof‑of‑concept code; treat an unpatched kernel as an emergency until the patch is applied.
- Some mitigations (like disabling unprivileged user namespaces) can break legitimate developer workflows and container functionality. Test any temporary control thoroughly before wide deployment.
- Vendor CVSS scores and narrative details vary slightly; when planning mitigation windows, rely on vendor patch availability rather than score differences alone.
Practical checklist for administrators (quick action plan)
- Inventory all hosts and identify kernel package versions; flag those reported as vulnerable by your vendor.
- If patches are available from the vendor, schedule staged upgrades with a rollback plan; prioritize network edge and virtualization hosts.
- If you cannot patch immediately, reduce attack surface: remove CAP_NET_ADMIN from untrusted containers, disable unprivileged user namespaces where feasible, and isolate workload classes that manipulate nftables. ([wiz.io]lnerability-database/cve/cve-2024-0607)
- Enable/collect kernel crash dumps and monitor logs for nftables‑related oopses to detect attempted exploitation.
- Validate patched kernels in staging using the same nftables rulesets and container network topology as production.
What to tell development and security teams
- Development teams should avoid granting elevated network capabilities to untrusted containers and should push for least‑privilege builds that do not require CAP_NET_ADMIN. This reduces the chance an attacker gains the leverage needed to trigger kernel nftables expressions.
- Security teams should add this CVE to the organization’s urgent patch list and treat it as an availability risk rather than a confidentiality one. While not a remote RCE, the operational cost of ignoring it can be high.
- Audit code that programmatically manipulates nftables expressions (for example, tooling that dynamically compiles complex rules) and add guards or input validation so malformed or attacker‑injected expressions cannot reach the kernel without sanity checks. Defence in depth at the orchestration layer reduces risk.
Conclusion
CVE‑2024‑0607 is a textbook example of how a small pointer‑math mistake inside a kernel expression evaluation path can generate outsized operational pain. The core bug is simple to describe — 8‑byte writes into a 4‑byte array — but the consequences are real for any infrastructure that relies on stable nf_tables behavior: firewalls, multi‑tenant hosts, container clusters, and network appliances.The remedy is straightforward: apply vendor patches or upstream stable fixes, prioritize network‑critical hosts, and harden any environment that allows untrusted components to manipulate nftables state. Where immediate patching is impossible, use the mitigations described above (remove CAP_NET_ADMIN from untrusted workloads, disable unprivileged namespaces if acceptable, monitor kernel logs, and stage tested rollouts).
Our forum has covered related nf_tables advisories and vendor attestations in previous threads, and operators should consult their distribution security tracker to map CVE to the exact package and fixed kernel for their environment before applying updates.
If you manage Linux infrastructure, treat this as a high‑priority availability patch: the bug’s simplicity makes it a reliable crash primitive, and in modern, containerized environments “local” vulnerabilities often translate into meaningful operational outages unless remediated quickly.
Source: MSRC Security Update Guide - Microsoft Security Response Center