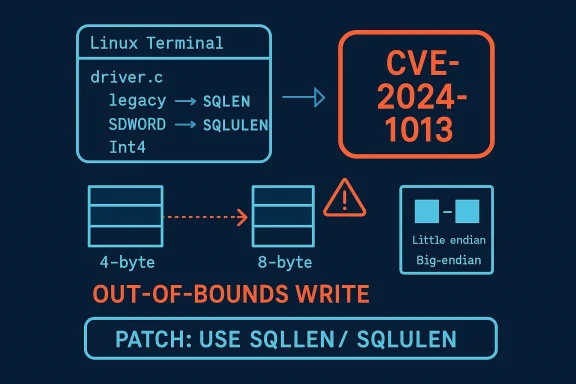
unixODBC has a newly minted CVE — CVE-2024-1013 — describing an out-of-bounds stack write triggered by incompatible pointer-to-integer type usage in an example PostgreSQL driver. The root cause is trivial to state but subtle in practice: on 64‑bit platforms the code assumed 4‑byte integer sizes in places where the callee actually writes 8 bytes, producing a stack overwrite that can corrupt memory. Upstream maintainers merged a tiny, targeted fix in late January 2024, and vendors issued patch advisories; however, exposure varies significantly between distributions because the vulnerable code lives in historical/example driver sources that are often not built or shipped by default.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
What is unixODBC and why it matters
unixODBC is an open-source ODBC (Open Database Connectivity) driver manager widely used on Linux and Unix-like systems to provide a standard API for applications to talk to many different database backends. Because it sits between applications and database-specific driver libraries, unixODBC appears in many server, desktop, and embedded stacks — and is therefore a common dependency in container images, VM templates, and appliances. Its ubiquity means even a relatively small bug can have outsized operational impact when it affects shipped or built artifacts.The flaw in plain language
The vulnerability is an out‑of‑bounds stack write caused by mismatched pointer-to-integer or integer-type assumptions between caller and callee code. In the affected example PostgreSQL driver code, some variables were declared as older 4-byte integer types while the ODBC API and modern platforms use 8-byte types (for example,SQLLEN) on 64‑bit builds. When the callee writes an 8‑byte value where the stack frame had been allocated for a 4‑byte value, bytes beyond the intended storage are corrupted — producing undefined behavior that can crash the process or, in theory, be leveraged for more serious memory-corruption attacks. The upstream fix replaced the legacy 4‑byte types with the correct SQLLEN/SQLULEN types to avoid the mismatch. (github.com)Little‑endian vs big‑endian nuance
A critical detail that makes the vulnerability confusing is endianness. On little‑endian architectures (x86_64, the dominant server and desktop architecture), certain mis‑sized writes may appear to “work” because the overwritten low-order bytes don’t immediately disturb other stack data in an obvious way. Big‑endian architectures may manifest breakage immediately because byte order makes the out-of-bounds writes collide with adjacent fields differently. The upstream notes specifically call out that the bug could go unnoticed on little‑endian systems while being more visible on big‑endian machines. That nuance influenced both the detection timeline and vendor responses. (github.com)The public timeline and vendor posture
Upstream: a tiny, deliberate change
The upstream repository accepted a single small pull request that renames a few variables from legacy integer types (SDWORD, Int4, etc.) to the proper SQLLEN/SQLULEN types used by the ODBC API. The commit diff is three lines of type adjustments in an example driver file (Drivers/Postgre7.1/info.c) and was merged on January 29, 2024; Red Hat Product Security then assigned CVE‑2024‑1013 to the issue. The change is straightforward and targeted — the kind of fix that eliminates the mismatch at the source. (github.com)Vendor advisories: mixed exposure, timely updates
Major distributions produced security notices and packages that reflect their packaging decisions:- Ubuntu / Canonical issued security notices (USN-6715-1 and USN-6715-2) and shipped updated unixODBC package builds for supported releases. Ubuntu’s advisories also clarify that the problematic code resides in example drivers that are not built in some Ubuntu packages, but they still pushed updates for completeness. Fixed package versions are published for affected releases.
- Red Hat / Fedora tracked the problem but concluded that, due to how they package unixODBC, the vulnerable “main driver” is deleted during package build and therefore RHEL and Fedora are not affected in shipping artifacts. The Red Hat Bugzilla discussion explains packaging differences (main driver vs. setup driver) and why shipped packages do not include the vulnerable binary. Red Hat nevertheless tracked the issue and coordinated with upstream. (bugzilla.redhat.com)
- SUSE issued updates where its packaged releases were affected and published patches and patch instructions for customers.
- Public vulnerability databases (NVD, CVE aggregators) enumerated the flaw, assigned a high impact rating (CVSS-style scores place confidentiality, integrity and availability impacts as high given the potential for memory corruption), and linked to vendor notes. However, the actual exploitability in practice depends on whether an environment builds and ships the specific example driver or otherwise exposes the buggy code path.
Exploit availability and real-world risk
At the time of writing, there are no widely circulated proof‑of‑concept exploits attributed to CVE‑2024‑1013 in public exploit repositories. EPSS/other exploitability scoring indicated a low probability of in‑the‑wild exploitation compared to many vulnerabilities, reflecting the local attack vector and the packaging realities described above. Nonetheless, the vulnerability was given a high impact score because if an attacker can trigger the vulnerable code path on an affected binary, outcomes range from process crashes (DoS) to potential arbitrary-code scenarios depending on the surrounding memory layout. Administrators should treat this as a real, fixable risk — but one whose practical exposure is often limited by distribution packaging choices.Technical analysis: what made this bug happen, and why it’s instructive
Type sizes and historical baggage
The bug is classical C/C++ maintenance entanglement: historical type aliases for older database drivers assumed 32‑bit integer widths. Over time, ODBC standardized on types such asSQLLEN and SQLULEN that map to platform-appropriate widths (8 bytes on LP64 platforms). When older driver code continues to use legacy fixed-width types, mismatches appear on 64‑bit builds. The result is not a language bug, but a maintenance hazard: implicit assumptions about integer width combined with low‑level data handling. The upstream fix standardizes types to the right, portable definitions. (github.com)Stack layout and exploitation vectors
A stack overwrite from a size mismatch may corrupt adjacent local variables, saved registers, return addresses, or control‑flow data. The severity depends on:- Compiler flags and mitigations active at build time (stack canaries, -fstack-protector, ASLR).
- Whether the vulnerable code is compiled into a binary that is shipped and used by real connections.
- How easy it is for an attacker to interact with the vulnerable function (local process, privileged contexts, or remote network calls via a wrapped service).
Endianness: why little‑endian systems “hide” some bugs
Little‑endian architectures store least significant bytes first; when a 4‑byte slot is overwritten with an 8‑byte write, the low-order bytes (which the program may read) can appear correct while the high-order bytes corrupt other stack locations. That can cause the bug to be silent or manifest only under certain conditions, making testing and fuzzing less likely to catch issues unless you test on big‑endian hardware or with instrumentation (ASAN, ubsan, kernel sanitizers) that will flag out‑of‑bounds writes irrespective of observed behavior. Upstream comments explicitly referenced that little‑endian machines may have “gone unnoticed” while big‑endian machines break. (github.com)Practical guidance for administrators and developers
Below are prioritized steps for defenders: short, actionable, and designed to reduce risk quickly.1. Inventory and identify affected systems
- Check whether unixODBC is installed and which binary packages are present (package managers:
dpkg -l | grep unixodbcfor Debian/Ubuntu,rpm -q unixODBC/dnf list installed unixODBCfor RHEL/Fedora/SUSE). - Specifically look for shipped driver libraries that match the example driver names mentioned in vendor discussions (for example
libodbcpsql.sovslibodbcpsqlS.so) and determine whether the “main driver” binary was packaged or removed. (bugzilla.redhat.com)
2. Apply vendor patches where provided
- Update your system packages via your standard patch process. On Debian/Ubuntu-based systems use your package manager to upgrade
unixodbc,libodbc1and related packages to the vendor-supplied fixed versions (Ubuntu published USN advisories with fixed versions for affected releases). SUSE and other vendors published fixes where applicable. - If you maintain custom builds of unixODBC (embedded appliances, bespoke ISOs, container images), pull the upstream commit that replaces legacy types with
SQLLEN/SQLULENor upgrade to a release that includes the fix (the change is tiny but important). The upstream commit merged Jan 29, 2024 contains the fix. (github.com)
3. If you cannot patch immediately, apply mitigations
- Prevent untrusted local users from executing applications that link to unixODBC or that could trigger the example driver code paths. Tighten file permissions and use container profiles to limit execution.
- Remove or disable example drivers from packaging and builds so they are not present in shipped binaries (
Drivers/Postgre7.1was the file in question). If you don’t need the driver, exclude it from builds. (github.com)
4. Hardening and compiler mitigations (developers)
- Rebuild with stack-protector and other compiler hardening flags:
-fstack-protector-strong,-D_FORTIFY_SOURCE=2, and enable PIE if appropriate. - Use sanitizers (ASan, UBSan) and fuzz testing as part of your CI for any drivers or code paths that handle untrusted inputs. These tools catch mismatched writes and out-of-bounds behavior irrespective of endianness.
- Prefer portable API types (
SQLLEN,SQLULEN) — avoid direct use of legacy fixed-size integer types in new driver code. (github.com)
5. Logging, monitoring and detection
- Look for process crashes and repeated ODBC‑related failures in application logs; unexpected crashes in services that call ODBC drivers can indicate attempts to trigger the bug.
- Use EDR or host-based anomaly detection to flag unusual process terminations or suspicious local processes that interact with database drivers.
Risk assessment: how worried should you be?
- Impact: The vulnerability is rated high for confidentiality, integrity and availability in CVSS-style metrics because a successful memory corruption can have serious consequences (DoS or potential code execution).
- Exploitability: The attack vector is local in the documented advisories — you need code execution or at least the ability to run calls against the vulnerable driver on the host itself. This markedly lowers the immediate remote risk for most servers that do not grant untrusted local accounts. Public exploit evidence is low or non-existent at time of writing.
- Real-world exposure: Many modern Linux distributions do not ship the vulnerable example driver binary in their standard packages; where vendors do ship or backport, they have released updates. The greatest risk is custom builds, container images, or embedded appliances that include the historical example driver without modification — and environments that give untrusted users local access. Red Hat’s bug discussion documents exactly this packaging nuance and why RHEL/Fedora distributions may not actually ship the vulnerable artifact. (bugzilla.redhat.com)
- Recommendation summary: Treat CVE‑2024‑1013 as a high-impact but largely local vulnerability. Prioritize patches for systems that ship or use custom unixODBC builds, update standard distributions per vendor advisories, and apply hardening where immediate patching is infeasible.
Why this case matters beyond the immediate patch
- It’s a reminder that small, local type mismatches in old example code can become tracked CVEs and, depending on packaging, can create real-world risk. Even repository “examples” may end up in shipped artifacts or copied into production code. (github.com)
- The incident highlights the importance of compiler warnings and modern toolchains: newer compilers (GCC 14 and later) are stricter and prompted the upstream change, turning a latent mismatch into a build-time error that leads to the security fix. Modern toolchains and CI that treat warnings as errors will catch classes of such bugs earlier. (github.com)
- Endianness still matters for detection: relying solely on “it works on x86_64” is no proof that code is safe. Testing on multiple architectures, or better yet with sanitizers, will reveal latent issues that platform layout masks. (github.com)
Quick checklist for operations teams (summary)
- Inventory unixODBC presence and installed package versions on all hosts.
- Apply vendor updates (Ubuntu USN, SUSE security updates, or vendor-provided patches) per your patch cycles.
- If you maintain custom builds, merge the upstream type fixes or upgrade to a tagged release that includes them. (github.com)
- Remove or disable example drivers from builds/images unless explicitly needed. (github.com)
- Harden builds and enable runtime mitigations (stack canaries, ASLR, PIE, FORTIFY) and add sanitizer testing in CI. (github.com)
Conclusion
CVE‑2024‑1013 is a small but instructive vulnerability: the technical fix is trivial — replace legacy fixed-width types with the platform-correct ODBC types — yet the operational story is nuanced. The combination of historical example code, distribution packaging decisions, and architecture-dependent behavior created a situation where a serious memory-corruption bug earned a CVE but did not uniformly translate into broad real‑world exposure. That said, risk remains real for custom-built images, embedded systems, or environments that inadvertently ship the example driver binary. Administrators should prioritize vendor updates, audit custom builds for stale example code, and adopt compiler and runtime hardening to reduce the chance that similar type‑mismatch bugs survive into production. (github.com)Source: MSRC Security Update Guide - Microsoft Security Response Center