The container build toolchain that many organizations treat as a routine developer utility just produced a reminder: a single badly-validated path can break the isolation model that makes containers safe. In March 2024 Buildah (and downstream Podman Build) was assigned CVE-2024-1753 — a high‑severity link‑following vulnerability that allows a malicious Containerfile to mount arbitrary host locations into a build step, giving commands executed during the RUN phase read‑write access to the host filesystem and enabling a full container escape at build time.
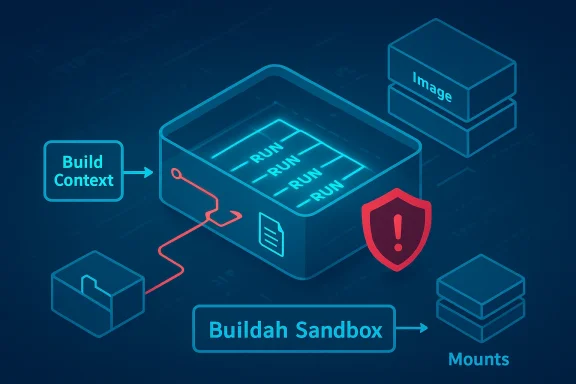
Container builds are supposed to be ephemeral: you feed a Containerfile (or Dockerfile), the builder composes layers and runs build steps inside an isolated environment, and the resulting image leaves no direct writable imprint on the host. Buildah — a key OCI image build tool used independently and inside Podman — implements many features such as multi-stage builds and the extended RUN --mount functionality that mirrors BuildKit-like behavior. CVE-2024-1753 subverts that model by abusing how Buildah resolves mount sources during build-time volume processing: a specially-crafted dummy image containing a symbolic link to the host root (or other host path) can be used as a mount source. Because the builder resolves that link incorrectly, the mount ends up placing host directories into the container’s build namespace, and any commands executed in the RUN step operate directly on host files.
The root cause is a classic filesystem-validation mistake: improper link resolution before file access (CWE‑59), sometimes called a symlink or link‑following vulnerability. The practical result is that a path which appears to be inside the build context or inside an image’s filesystem actually resolves to an attacker-controlled or attacker-accessible host location. Several platform and distribution security trackers recorded the issue with a CVSS v3.1 base score of 8.6 (High).
Public intelligence sources and vulnerability feeds have reported proof‑of‑concept writeups in community repositories or referenced PoCs; however, availability of working exploits in the wild is not equivalent to active widespread exploitation. Some trackers report PoCs in public repositories but security teams should treat those claims cautiously: a variety of automated feeds index code snippets and experimental repos, and not all are reliable or complete. If your environment exposed Buildah or Podman to untrusted inputs prior to the patch, assume the potential for targeted local exploitation is real and prioritize remediation.
If you run Buildah or Podman build workflows, treat this as a high‑priority operational risk: inventory build hosts, apply vendor fixes now, and harden build infrastructure so that a single crafted Containerfile cannot turn a build into a system compromise. The vulnerability is both a technical and procedural warning — container builders are powerful tools, and they must be managed like any privileged system component.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
Container builds are supposed to be ephemeral: you feed a Containerfile (or Dockerfile), the builder composes layers and runs build steps inside an isolated environment, and the resulting image leaves no direct writable imprint on the host. Buildah — a key OCI image build tool used independently and inside Podman — implements many features such as multi-stage builds and the extended RUN --mount functionality that mirrors BuildKit-like behavior. CVE-2024-1753 subverts that model by abusing how Buildah resolves mount sources during build-time volume processing: a specially-crafted dummy image containing a symbolic link to the host root (or other host path) can be used as a mount source. Because the builder resolves that link incorrectly, the mount ends up placing host directories into the container’s build namespace, and any commands executed in the RUN step operate directly on host files.The root cause is a classic filesystem-validation mistake: improper link resolution before file access (CWE‑59), sometimes called a symlink or link‑following vulnerability. The practical result is that a path which appears to be inside the build context or inside an image’s filesystem actually resolves to an attacker-controlled or attacker-accessible host location. Several platform and distribution security trackers recorded the issue with a CVSS v3.1 base score of 8.6 (High).
Why this matters: the risk in plain language
- Containment assumptions break. Developers and CI/CD systems routinely run builds without expecting the build to alter host system files. This bug lets a build step “escape” that assumption and modify host critical files.
- Local, low-complexity exploit path. The attack is executed during an ordinary build. It requires creating or using a crafted Containerfile (or an untrusted build context) rather than a remote network exploit, which makes the practical attack surface the set of users and processes that can run builds. Many build systems allow many developers, CI runners, or automation accounts to run builds — an attacker only needs that level of access.
- High impact on confidentiality, integrity, availability. Because the attacker can read and write the host filesystem, secrets, configuration, and the system itself can be exfiltrated or destroyed; services can be altered or disabled. Security scoring and vendor advisories classify the impact as High across confidentiality, integrity, and availability.
Technical analysis
How the exploit works (in technical terms)
- Buildah processes a Containerfile and handles a RUN instruction that uses a mount from a source image or directory.
- An attacker supplies a dummy image or build context that contains a symbolic link whose resolved target points to a host path (for example, the root filesystem or /etc).
- Buildah resolves the mount source but fails to correctly restrict or canonicalize the resolved path to the safe build context; it treats the resolved target as an acceptable source and issues a mount operation.
- The mount operation places the host path inside the build container’s namespace for the RUN step, giving the RUN command read-write access to the host files that were mounted.
- The attacker’s RUN commands then read, modify, or remove host files — culminating in a full container escape at build time.
Variations and related attack patterns
- The vulnerability is a form of symlink traversal or path canonicalization failure. Attackers can exploit similar mistakes by crafting build contexts or images that rely on symlinks, bind mounts, or specially-named files.
- There are related Buildah/Podman issues (separate CVEs) where cache path handling or other mount semantics allowed host access; those are conceptually similar but distinct vulnerabilities. Administrators should treat the whole family of mount-and-cache handling bugs as a class and patch comprehensively.
Affected products and versions
- Buildah: multiple releases prior to the patched commits were affected. Vendor advisories and package trackers identify vulnerable Buildah releases; Buildah maintainers fixed the issue and published updates. GitLab advisory data and the Buildah advisory list the fix and the fixed version (for example, Buildah 1.35.1 contains the corrective changes).
- Podman: Podman includes a vendored Buildah for build operations. Podman’s security advisories name affected Podman releases v4.0 through v4.9.3 and v5.0, and they list patched podman releases (for example, v4.9.4 and v5.0.1). Patch shipping in Podman occurred after the Buildah fix was finalized.
- Distributions: Red Hat, Debian, Ubuntu, SUSE, and others published security advisories and package updates. Red Hat released multiple RHSA updates to distribute the fix into RHEL channel packages and the container-tools module; Debian and Ubuntu trackers list fixed package revisions in their repositories. Systems using packaged Buildah/Podman should consult their distro advisories and install the vendor-provided updates.
Severity, exploitability, and real‑world exploitation
Security trackers uniformly treat CVE‑2024‑1753 as high risk, with CVSS v3.1 assessments around 8.6 and impact metrics calling out severe confidentiality, integrity, and availability loss. The vulnerability’s attack vector is local and requires a build step using the crafted Containerfile, but it has low complexity and minimal privilege requirements in typical workflows — making the practical risk to developer machines, CI runners, and build hosts high.Public intelligence sources and vulnerability feeds have reported proof‑of‑concept writeups in community repositories or referenced PoCs; however, availability of working exploits in the wild is not equivalent to active widespread exploitation. Some trackers report PoCs in public repositories but security teams should treat those claims cautiously: a variety of automated feeds index code snippets and experimental repos, and not all are reliable or complete. If your environment exposed Buildah or Podman to untrusted inputs prior to the patch, assume the potential for targeted local exploitation is real and prioritize remediation.
Detection, response, and forensic guidance
Quick detection signals
- Unexpected modifications to host files directly following an image build step.
- Build logs that show RUN commands accessing / listing / modifying paths like /etc, /root, or files normally outside the build context.
- Presence of unexpected mount operations in the build logs or kernel mount tables coincident with build runs.
- CI jobs that run build tasks using untrusted Containerfiles or images from public registries should be treated as suspicious after the fact.
Incident response checklist
- Stop further builds using Buildah/Podman on the impacted host until it’s patched or isolated.
- Collect forensic artifacts: build logs, container runtime logs, kernel dmesg, /proc/mounts snapshot, and timestamps of suspicious file writes.
- Check for persistence: look for new accounts, modified systemd units, scheduled jobs, or altered package lists.
- Rebuild/restore from known good: if host integrity cannot be guaranteed, restore from a clean image or reinstall the host after gathering forensic data.
- Rotate secrets exposed to impacted hosts: keys, tokens, and credentials that may have been accessible during builds should be considered compromised.
Mitigations and recommended fixes
There are immediate operational mitigations and permanent fixes.Apply vendor patches (primary action)
- Upgrade Buildah to the patched release (example fixed Buildah release: 1.35.1 and later).
- Upgrade Podman if you rely on Podman’s build functionality (patched Podman versions include v4.9.4 and v5.0.1 or later).
- Install distribution errata: use your distro’s package management (RHEL/CentOS streams, Debian/Ubuntu updates, SUSE patches) to pick up vendor-curated fixes; Red Hat published RHSA advisories that include the Buildah fix in the container-tools module and related packages.
Short‑term and compensating controls
- Restrict who can run builds. Limit Buildah/Podman build execution to trusted accounts and to isolated build hosts or VMs that minimize blast radius.
- Run builds as unprivileged/rootless where feasible. Rootless Buildah/Podman reduces the impact of host writes in many cases; however, rootless operation is not a panacea — verify behavior in your environment and platform-specific constraints.
- Enforce SELinux/mandatory access control. Several advisories note that enabled SELinux reduces the severity of a successful exploit by restricting what container processes can access on the host. Enforce SELinux in enforcing mode where possible and validate container policies. Note: SELinux reduces, but does not necessarily eliminate, the risk.
- Treat build inputs as untrusted. Avoid building images from unknown Containerfiles or images; sanitize build contexts and avoid including arbitrary external artifacts directly in builds.
- Audit and harden CI/CD. Restrict registries, require image signing/verification for base images, and run builds in ephemeral VMs or isolated runners that are re-provisioned frequently.
- Network and file-system controls. Use host-level apparmor/selinux profiles, seccomp filters, or container-aware file-system protections to limit what build processes can reach on the host.
Developer and CI safeguards
- Disallow or carefully review use of RUN --mount in Containerfiles pulled from third parties.
- Use reproducible build practices and hermetic build environments: prefer base images hosted in trusted registries and pinned digests.
- Add automated checks to CI that verify Containerfiles do not include suspicious mount directives or symlinks in the build context.
Practical checklist for ops teams (actionable steps)
- Identify all hosts where Buildah or Podman build is used (developer machines, CI runners, release hosts).
- Apply vendor/security updates to Buildah and Podman immediately. Verify package versions match vendor fixed versions.
- Enable or verify SELinux enforcement on hosts where feasible; test builds after enabling to ensure no operational regressions.
- Restrict build execution to hardened, monitored runners; revoke or rotate credentials accessible to untrusted build agents.
- Search CI logs for builds that created or mounted unexpected host paths; treat any suspicious activity as a high-priority incident.
- Rotate keys and secrets that may have been mounted or exposed during unpatched builds.
Broader implications and lessons learned
This vulnerability underscores two persistent realities in container security:- Container builders and developer tooling are part of the trusted computing base for modern devops. Tools that run with broad filesystem privileges or that programmatically perform mounts must be designed with the same threat modeling and defensive coding practices we demand from production runtimes. CVE‑2024‑1753 is a reminder that build‑time features (mounts, caches, bind propagation) are high-risk surfaces when validation is incomplete.
- The local threat model is underrated. Attackers often start from developer workstations or compromised CI runners. Local files, local symlinks, and bad build artifacts can lead to catastrophic host compromise. Security teams must treat build infrastructure as a first-class security boundary and invest accordingly.
- Defense-in-depth works: mandatory access controls (SELinux), rootless operation, limited privilege accounts, hardened runners, and rapid patching together reduce overall risk. No single control is sufficient on its own — but layered mitigations reduce attack surface and blast radius.
What to watch next
- Confirm that every build host and CI runner has the patched Buildah/Podman releases installed (vendors published advisories and RBAC-aware package updates). Consult your distro’s security tracker and the upstream Buildah/Podman advisories for final fixed versions and backport guidance.
- Monitor community trusted feeds for any credible proof‑of‑concept code that demonstrates exploitation; if public PoCs appear, treat them as high-priority indicators and accelerate mitigations for any remaining unpatched hosts. Some third‑party vulnerability feeds reported PoCs or proof descriptions — treat those feeds as early warning while relying on vendor advisories for authoritative patches.
- Re-evaluate build-related features (for example, RUN --mount, cache mounts, and bind-propagation) in your organization’s standard Containerfile templates and training. If a feature is not required, consider forbidding it in untrusted or automated builds.
Conclusion
CVE‑2024‑1753 is a high‑severity, practical vulnerability that converts a benign developer activity — building container images — into an opportunity for full host compromise when Buildah (or vendored Buildah inside Podman) fails to validate mount sources correctly. The fix is straightforward in concept (patch the path resolution and enforce canonicalization and access checks), but remediation requires coordinated, timely patching across developer workstations, CI/CD runners, and distribution packages.If you run Buildah or Podman build workflows, treat this as a high‑priority operational risk: inventory build hosts, apply vendor fixes now, and harden build infrastructure so that a single crafted Containerfile cannot turn a build into a system compromise. The vulnerability is both a technical and procedural warning — container builders are powerful tools, and they must be managed like any privileged system component.
Source: MSRC Security Update Guide - Microsoft Security Response Center