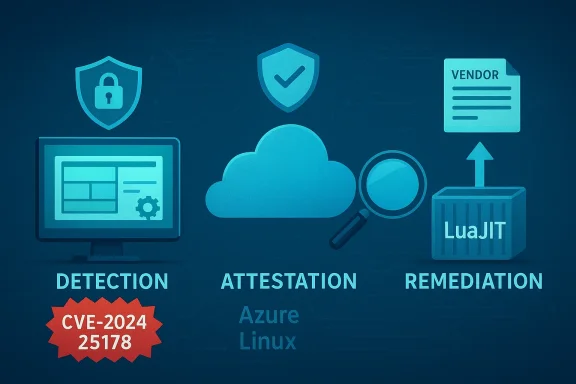
CVE-2024-25178 is a real-world reminder that even tiny pieces of high‑performance open‑source software can become a critical link in the supply‑chain security story — Microsoft has publicly attested that Azure Linux includes the vulnerable LuaJIT component, but that attestation is a product‑scoped statement, not definitive proof that no other Microsoft product bundles the same code.
LuaJIT is a high‑performance just‑in‑time compiler and runtime for the Lua programming language that has been widely adopted in performance‑sensitive components across the Linux ecosystem. Because LuaJIT is embeddable and small, it frequently appears in two different ways inside software stacks:
Microsoft’s public messaging on this CVE states that the company has identified the component in its Azure Linux distribution and that Microsoft publishes VEX/CSAF attestations starting October 2025 for Azure Linux to make these product‑level dependencies transparent. The wording Microsoft used makes a very specific claim: they have attested that Azure Linux includes the affected upstream library and is therefore potentially affected; if other Microsoft products are found to be impacted, Microsoft will update the CVE/VEX records to reflect that. That wording is accurate and important to parse carefully.
Out‑of‑bounds reads have different security consequences from writes. A read can leak memory contents, potentially disclosing sensitive data. It can also cause crashes that affect availability. The exploitability — and whether a read can be turned into a more severe impact — depends strongly on how the runtime is used in a given product (e.g., whether attacker‑controlled input can force the vulnerable code path and whether that memory contains anything of value).
Patches applied by distributors typically include the upstream commit that reworks the stack‑overflow handling logic and additional downstream hardening. Distributions that ship LuaJIT or packages that bundle it have been publishing updates in the weeks following the public disclosure.
Why that distinction matters:
Bottom line: treat the vulnerability seriously for affected hosts and images, prioritize patching for exposed systems, and verify the absence of the vulnerable component in other critical Microsoft artifacts you rely on.
Open‑source dependencies travel in multiple ways: as distro packages, as static links inside binaries, and as embedded runtimes inside software. Each requires a different discovery and remediation path. Security teams should combine vendor attestations (VEX/SBOM), automated scanning, and targeted manual inspection to close the visibility gap that a single attestation cannot address alone.
The good news: Microsoft’s move toward machine‑readable attestations and the broader ecosystem’s quick patching of LuaJIT show that the modern open‑source supply chain can respond — but only when defenders treat attestations as helpful signals, not exhaustive proofs. Prioritize patching where confirmed, verify where unconfirmed, and require attestations or SBOMs for critical third‑party artifacts to reduce future uncertainty.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
LuaJIT is a high‑performance just‑in‑time compiler and runtime for the Lua programming language that has been widely adopted in performance‑sensitive components across the Linux ecosystem. Because LuaJIT is embeddable and small, it frequently appears in two different ways inside software stacks:- As a distribution package (for example: luajit shipped by a distro and available via apt/yum/zypper).
- As an embedded runtime, statically linked or bundled inside applications such as web server modules, telemetry agents, benchmarking tools (sysbench), or middleware.
Microsoft’s public messaging on this CVE states that the company has identified the component in its Azure Linux distribution and that Microsoft publishes VEX/CSAF attestations starting October 2025 for Azure Linux to make these product‑level dependencies transparent. The wording Microsoft used makes a very specific claim: they have attested that Azure Linux includes the affected upstream library and is therefore potentially affected; if other Microsoft products are found to be impacted, Microsoft will update the CVE/VEX records to reflect that. That wording is accurate and important to parse carefully.
What the vulnerability actually is
The technical root cause
At a code level, CVE‑2024‑25178 involves an out‑of‑bounds read within the LuaJIT stack overflow handler. The handler is responsible for detecting and responding to stack exhaustion / overflow conditions and doing so safely. A bug in that handler caused the runtime to read memory outside the intended buffer windows under certain stack overflow conditions.Out‑of‑bounds reads have different security consequences from writes. A read can leak memory contents, potentially disclosing sensitive data. It can also cause crashes that affect availability. The exploitability — and whether a read can be turned into a more severe impact — depends strongly on how the runtime is used in a given product (e.g., whether attacker‑controlled input can force the vulnerable code path and whether that memory contains anything of value).
Versions affected and remediation
The upstream description of affected versions is straightforward: LuaJIT through 2.1 and OpenRusty luajit2 before v2.1‑20240314 contained the issue; later upstream commits and downstream vendor patches addressed the problem. Distributors and maintainers released updated packages incorporating the fix; many Linux distros issued updates to their packaged luajit or to packages that embed it.Patches applied by distributors typically include the upstream commit that reworks the stack‑overflow handling logic and additional downstream hardening. Distributions that ship LuaJIT or packages that bundle it have been publishing updates in the weeks following the public disclosure.
Microsoft’s statement: what it does—and what it doesn’t—mean
Microsoft’s public advisory language around this CVE, and its broader policy of publishing VEX/CSAF attestations for Azure Linux, contains two important points:- Microsoft explicitly attested that Azure Linux includes the upstream LuaJIT code path implicated in CVE‑2024‑25178 — and that Azure Linux customers should treat the distribution as potentially affected and apply the published Azure Linux security updates.
- Microsoft also said that if additional Microsoft products are identified to include the upstream component, MSRC will update the CVE to reflect those products. In other words, currently Microsoft has only published evidence (the VEX attestation) for Azure Linux, not for its other products.
Is Azure Linux the only Microsoft product that includes LuaJIT?
Short answer: No — at least not necessarily. Azure Linux is the only Microsoft product Microsoft has publicly attested to include the vulnerable LuaJIT upstream component so far, but Microsoft’s attestation is product‑scoped and does not constitute exhaustive inventory for every Microsoft project, image, or binary.Why that distinction matters:
- A component like LuaJIT can appear as a packaged dependency in one place (Azure Linux), yet also be statically linked into an application binary, bundled inside a container image, or embedded into tooling distributed by other teams. Those cases require different discovery techniques.
- Microsoft’s transparency work (VEX/CSAF and publishing product attestations) is a huge improvement for product‑level clarity, but it is an opt‑in, product‑scoped process that started with Azure Linux. MSRC has committed to updating CVEs/VEX records if/when additional affected Microsoft products are found.
- Absence of public attestation for a product could mean any of these things: the product was inspected and is clean; the product hasn’t been inspected yet; or the product includes an embedded copy but the supply‑chain tracking has not yet associated it with the CVE.
How LuaJIT commonly surfaces inside software — attack surface considerations
To assess whether a product likely contains the vulnerable library, look at the ways LuaJIT typically appears:- Distribution package: a distro ships a separate luajit package that other packages or users can install. This is the clearest case for Azure Linux and is easy to patch.
- Bundled with an application: sysbench, some Redis modules, web server modules (OpenResty/nginx lua), telemetry agents, or custom appliances may package or statically link LuaJIT.
- Within container images: container images published in registries or used in microservices can contain luajit either as a package or embedded in application binaries.
- Games, middleware, or performance‑sensitive tooling that use Lua for scripting — these might include LuaJIT inside shipped binaries.
Practical guidance for Azure Linux customers
If you run Azure Linux (the product Microsoft attested), treat this CVE as actionable and follow these steps immediately:- Verify installed luajit versions on affected nodes:
- For RPM‑based Azure Linux: run rpm -q luajit or rpm -qa | grep -i luajit.
- For APT‑based or Debian‑derived images: run dpkg -l | grep -i luajit.
- Apply Microsoft’s Azure Linux security updates:
- Use your standard node image update path or the package manager (dnf/yum/zypper/apt) to update the luajit package to the vendor‑supplied fixed version. Microsoft published Azure Linux updates addressing LuaJIT in the days after disclosure.
- Reboot or restart affected services where the library is loaded into long‑running processes. Static linking into a binary requires replacing the binary or upgrading the package that produced it.
- If you run containerized workloads on Azure that use Azure Linux node images, ensure node image updates are applied and rebuild container images if they include luajit as a userland package.
- Use your organization’s patch‑management and vulnerability‑scanning workflows to prioritize and verify remediation. Tenable, Qualys, and other scanners published checks for Azure Linux images soon after advisories were issued.
- Reduce exposure of services operating on the affected host.
- Apply network‑level controls (firewall rules) to limit attack vectors.
- Add monitoring for crashes or anomalous behavior in services that embed LuaJIT.
How to check other Microsoft artifacts and third‑party images
For customers who consume other Microsoft products (containers in Azure Container Registry, marketplace images, Azure PaaS services, SDKs, or Windows features), do not assume they are unaffected just because Azure Linux was the only attested product. Use these steps:- Review published VEX/CSAF attestations and MSRC advisories for the product in question. If Microsoft has issued a VEX statement for that product, treat it as authoritative for that product.
- Inspect the product SBOM or ask Microsoft support for an SBOM or VEX attestation for the artifact you use. Increasingly, vendors produce SBOMs for images and managed services upon request.
- Locally inspect images and binaries:
- Unpack container images and run package manager queries inside the image root to locate luajit packages.
- Use binary string scanning or static analysis to detect statically linked instances of LuaJIT symbols.
- Search filesystem images for typical LuaJIT shared object names (e.g., libluajit‑5.1.so) and LuaJIT symbol names such as lj_state_growstack or lj_err_throw.
- Use your vulnerability scanner to fingerprint the artifact and flag any embedded luajit packages or matching binary signatures.
Detection, monitoring, and incident response guidance
Detection of exploitation attempts for this class of bug can be tricky because an out‑of‑bounds read may produce subtle information disclosure or may simply crash a process.- Instrument logging and monitoring for sudden crashes in processes known to embed LuaJIT.
- Monitor for unusual process behavior or repeated stack‑overflow exceptions.
- Watch for known public proof‑of‑concepts or exploit scanner activity targeting LuaJIT code paths. Threat intel and public exploit repositories published PoC material soon after disclosure — treat those signals seriously.
- Collect memory dumps for crashed processes and analyze whether the crash occurred in lj_state.c or related frames.
- If you suspect compromise, isolate affected hosts, preserve forensic artifacts (memory, disk images), and rebuild from known‑good images after remediation.
Risk analysis: how severe is this in practice?
The raw description — an out‑of‑bounds read in a stack‑overflow handler — can be rated differently by different vendors depending on usage context and exploitability assumptions. Several important factors influence practical risk:- Attack surface: Is the vulnerable LuaJIT instance reachable from attacker‑controlled input? If the LuaJIT context is exposed to network inputs (for example, in a web service using embedded Lua code), exploitation risk is higher.
- Privilege and sandboxing: Even if the library is accessible, is it running in a tightly sandboxed environment? Lower privileges and robust process isolation reduce risk.
- Data at memory locations: A read that returns non‑sensitive memory is less harmful; if it returns secrets or credentials, the impact is much higher.
- Availability of exploit code: Public proof‑of‑concepts make exploitation easier for attackers. After PoCs were publicly visible, some scanners began flagging systems as exploitable.
Bottom line: treat the vulnerability seriously for affected hosts and images, prioritize patching for exposed systems, and verify the absence of the vulnerable component in other critical Microsoft artifacts you rely on.
Strengths and weaknesses of Microsoft’s current approach
Notable strengths
- Microsoft’s move to publish VEX/CSAF attestations for Azure Linux is significant progress in supply‑chain transparency. Product‑level attestations eliminate guesswork for that product and give defenders concrete actions.
- Acting quickly to attest and push Azure Linux updates demonstrates a clear commitment to the distribution’s security lifecycle.
- Public acknowledgement that additional products will be updated if affected is good accountability.
Potential risks and limitations
- Product‑scoped attestations create a visibility gap: other Microsoft artifacts may still include the vulnerable code without a public attestation yet, leaving customers to discover those instances themselves.
- Many Microsoft customers run a mix of vendor images, marketplace images, and third‑party containers; this fragmentation complicates a single, authoritative inventory.
- Customers may misinterpret “Azure Linux attested” as “only Azure Linux has this problem,” which is incorrect from an inventory perspective. That misunderstanding could delay important checks in other contexts.
- Some Microsoft products are large and built by many teams; internal component reuse across teams can lead to hidden inclusions that are not automatically captured by product‑level attestations.
Action checklist: what security teams should do now
- Treat Azure Linux instances as affected until patched. Prioritize patch rollouts for node images and containers running on those nodes.
- Audit your usage of Microsoft images and artifacts:
- Request VEX/SBOM attestations where available.
- Run local scans to hunt for luajit packages and statically linked instances.
- Patch and rebuild:
- Update distribution packages (yum/dnf/apt/zypper) where luajit is a package.
- Rebuild container images that include luajit in the userland or base images.
- Replace or patch binaries that statically link luajit by obtaining vendor updates or recompiling.
- Harden and monitor:
- Apply network controls to limit access to services that might reach LuaJIT code paths.
- Increase monitoring for process crashes and anomalous behavior related to LuaJIT.
- Communicate with vendors:
- If you find LuaJIT included inside a Microsoft product or other vendor image without a public attestation, file a support ticket and request a VEX/CSAF statement or a security bulletin.
- Prepare an incident playbook entry:
- Document steps for isolating, collecting artifacts, and rebuilding affected hosts or images.
Final assessment and tone for IT leaders
Microsoft’s public attestation that Azure Linux includes the LuaJIT code involved in CVE‑2024‑25178 is an important, constructive step that helps Azure Linux customers respond quickly. However, defenders must not conflate an attestation for a single product with an exhaustive supply‑chain inventory across an entire vendor. The correct operational stance is to treat the attested product as confirmed affected and to proactively verify other Microsoft‑provided artifacts that you consume.Open‑source dependencies travel in multiple ways: as distro packages, as static links inside binaries, and as embedded runtimes inside software. Each requires a different discovery and remediation path. Security teams should combine vendor attestations (VEX/SBOM), automated scanning, and targeted manual inspection to close the visibility gap that a single attestation cannot address alone.
The good news: Microsoft’s move toward machine‑readable attestations and the broader ecosystem’s quick patching of LuaJIT show that the modern open‑source supply chain can respond — but only when defenders treat attestations as helpful signals, not exhaustive proofs. Prioritize patching where confirmed, verify where unconfirmed, and require attestations or SBOMs for critical third‑party artifacts to reduce future uncertainty.
Source: MSRC Security Update Guide - Microsoft Security Response Center