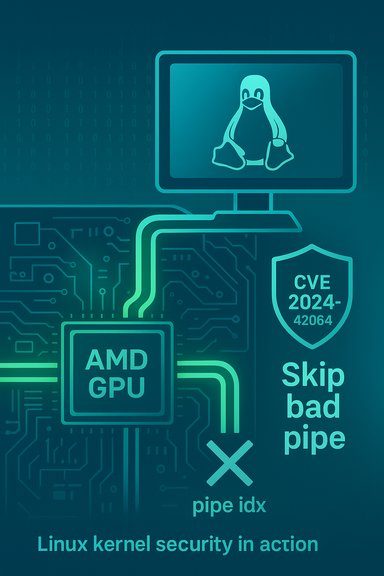
In the Linux kernel security landscape, a medium‑severity vulnerability tracked as CVE‑2024‑42064 was disclosed affecting the AMD DRM display driver: a defect in drm/amd/display that can cause the driver to crash when a pipe index (pipe idx) is not set properly, and the upstream remedy is to skip the problematic pipe rather than attempt to program it.
The vulnerability lives in the Linux kernel's AMD DRM display stack (the amdgpu driver portion under drivers/gpu/drm/amd/display). When the driver attempts to program display hardware, it enumerates pipes (CRTCs/streams) and expects certain state, including a valid pipe index. If that index is missing or not properly set, the driver could attempt to use invalid state and crash. The fix applied upstream is deliberately conservative: add logic to skip any pipe whose index has not been properly initialized, avoiding attempts to program absent or phantom hardware and thereby preventing the crash. Multiple major Linux distributions have catalogued and fixed the issue in their kernel packages; Ubuntu and Debian both reference the remedial change in their advisories and classify the issue as medium severity with a CVSS v3 base score of 5.5.
The upstream remediation is intentionally minimal and defensive:
Nevertheless, timely patching matters because:
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
The vulnerability lives in the Linux kernel's AMD DRM display stack (the amdgpu driver portion under drivers/gpu/drm/amd/display). When the driver attempts to program display hardware, it enumerates pipes (CRTCs/streams) and expects certain state, including a valid pipe index. If that index is missing or not properly set, the driver could attempt to use invalid state and crash. The fix applied upstream is deliberately conservative: add logic to skip any pipe whose index has not been properly initialized, avoiding attempts to program absent or phantom hardware and thereby preventing the crash. Multiple major Linux distributions have catalogued and fixed the issue in their kernel packages; Ubuntu and Debian both reference the remedial change in their advisories and classify the issue as medium severity with a CVSS v3 base score of 5.5. Why this matters: impact and real‑world context
Modern display stacks are complex. The kernel driver is responsible for safely programming hardware registers and sequencing clocks, and bugs in those code paths typically lead to availability impacts (driver oops, frozen displays, pageflip timeouts) rather than silent data theft. For CVE‑2024‑42064 the primary impact is availability: an unprivileged local action that triggers modesetting or stream programming on affected hardware can cause the driver to crash and may require a reboot to recover. Distribution advisories and public trackers consistently treat this as an availability‑focused issue. Key operational points:- Attack vector: Local — an attacker or unprivileged user that can interact with DRM device nodes or a compositor may be able to trigger the faulty code path.
- Privileges required: Low in typical desktop configurations where /dev/dri devices are accessible to user sessions; higher on hardened servers with restricted device access.
- Severity: Medium (CVSS v3 ≈ 5.5) as reported by distribution and vendor trackers.
Technical anatomy: what the code did wrong
At a high level, the bug arises from insufficient state validation in the display sequencing code that handles per‑pipe setup. The driver iterates pipes and expects a valid pipe idx to be present; when that index is not set (for example in certain hot‑plug, MST, phantom pipe, or hardware topology corner cases), the code proceeds anyway and attempts to program hardware with incomplete state, triggering a crash in privileged kernel context.The upstream remediation is intentionally minimal and defensive:
- detect that pipe idx is not set for the current pipe;
- skip the pipe so no register programming or clock switching is attempted for an invalid pipe; and
- allow the rest of the display sequencing to continue for valid pipes.
Affected versions and distributions
Independent trackers and distribution advisories indicate the vulnerable code existed in upstream kernel trees prior to the fix landing in stable kernels. Published advisory mappings show the fix landed in and was backported to multiple kernel series. Specific distro references include:- Ubuntu security advisories list the kernel vulnerabilities including CVE‑2024‑42064 and map fixed package versions for affected Ubuntu releases.
- Debian’s security tracker lists fixed versions and indicates the upstream commit ranges where the remedial changes are present.
- NVD, OSV and vendor trackers mirror this mapping and reflect a medium severity classification.
How to detect whether you are affected
Start with quick host‑level checks to determine whether your systems load the AMD driver and whether your kernel predates the fix:- Check running kernel:
uname -r - Check whether amdgpu driver is loaded:
lsmod | grep amdgpu - Inspect whether DRM device nodes are present and who can access them:
ls -l /dev/dri/* - If you distribute or run vendor kernels or embedded images, consult the distribution or vendor CVE advisories and the kernel package changelog to confirm the presence of the fix.
- Repeated pageflip timed out messages or amdgpu/reset watchdog entries in
dmesgorjournalctl -k. - Kernel oops or stack traces that reference amdgpu display sequencing routines around modeset/enable_streams code paths.
- A single monitor freezing in a multi‑display setup while the rest of the system remains responsive.
dmesg, serial console, journal) immediately for post‑mortem and patch verification.Remediation: patching and verification
The primary remediation is to update to a kernel package that includes the upstream fix and then reboot into the patched kernel. The general steps:- Identify affected systems using the detection checklist above.
- Obtain and apply vendor/distribution kernel updates that list CVE‑2024‑42064 or that include the upstream commits that implement the skip‑pipe guard. On many distributions, these are standard kernel security updates.
- Reboot the host to activate the patched kernel (kernel code changes require reboot).
- Verify the fix by reproducing relevant display sequences (hot‑plug, docking station connect/disconnect, MST hub usage) in a staging environment and confirming no pageflip timeouts, oopses or related log entries appear over a representative workload window (24–72 hours recommended for intermittent issues).
- Request a vendor timeline / patched image; or
- Build a custom kernel that cherry‑picks the upstream stable commit(s) into the vendor kernel tree and redeploy (requires careful hardware smoke testing).
Temporary mitigations and compensating controls
When you cannot patch immediately, apply compensations that reduce exposure:- Restrict access to DRM devices: change udev rules or device node permissions so that only trusted groups can access
/dev/dri/*. Removing /dev/dri from untrusted containers reduces the risk for multi‑tenant workloads. - Avoid exposing GPUs to untrusted workloads via passthrough or
--device=/dev/driin containerized environments. - Increase monitoring: set alerts for pageflip timeouts, amdgpu oopses, and display driver resets in your host monitoring or SIEM. Capture and retain kernel logs for forensics.
Testing and verification guidance for operators
A safe, reproducible verification path is essential after applying the patch:- Boot into the patched kernel on a test host representative of production hardware.
- Run display workloads covering hot‑plug, MST hub, and docking station usage. If feasible, include automated compositor and pageflip stress tests for several hours to increase confidence.
- Monitor kernel logs for the duration of the test for driver oops or pageflip timeouts.
- If you maintain CI or test rigs with GPUs, add kernel upgrade and display‑stress test cases to detect regressions before broad rollout.
Why the fix is low‑risk and why you should still patch quickly
The upstream change is surgical: it adds a simple guard to skip pipes that lack a valid index. Because the fix is narrow and behavior‑preserving for correct hardware configurations, it is straightforward for maintainers to backport into stable kernel branches and for distributions to include in security updates. That reduces regression risk and makes mass deployment pragmatic.Nevertheless, timely patching matters because:
- The issue provides a reliable availability primitive in exposed environments (multi‑tenant hosts, shared CI runners, VDI). Even without evidence of widespread weaponization, local DoS bugs have real operational cost.
- Vendor and embedded kernels that lag upstream may remain vulnerable for extended periods; auditors and asset owners must track those devices and either secure them or plan replacement/repair.
Cross‑validation and sources
Key factual claims in this feature are corroborated by independent trackers and advisories:- Ubuntu’s official security page lists CVE‑2024‑42064, describes the issue as “drm/amd/display: Skip pipe if the pipe idx not set properly” and classifies the priority as medium.
- Debian’s security tracker entry for the CVE documents the same description and maps fixed package versions across Debian releases.
- NVD’s CVE record and OSV mirror provide the canonical CVE registration and reflect the vulnerability description.
Risk analysis and critical perspective
Strengths of the upstream remediation- Surgical fix: The upstream change is limited in scope, minimizing the chance of unintended side effects and easing backport into stable kernel trees.
- Clear verification signals: The change affects discrete code paths and therefore is easy for packagers to test and for administrators to verify via changelogs and behavior tests.
- Long tail in embedded/OEM kernels: Devices and appliances that run vendor kernels and are not regularly updated may remain vulnerable for months or years, creating persistent risk. This long tail is the most significant operational concern for kernel driver CVEs.
- Exposure through configuration: Hosts that intentionally expose GPU devices to untrusted containers or guests are at materially higher risk and should prioritize patching or apply stricter device controls.
- Detection blind spots: Production kernels normally lack sanitizers like UBSAN; detection therefore depends on symptoms (pageflip timeouts, oopses) rather than explicit sanitizer traces, which can make low‑frequency triggers hard to find without proactive testing.
- There is no public evidence that CVE‑2024‑42064 has been weaponized in a mass exploitation campaign as of the available advisory publications. That absence of evidence is not proof of absence; local DoS primitives have historically been used opportunistically. Treat the lack of public exploit reports as cautionary rather than comforting.
Action checklist for administrators and desktop engineers
- Inventory: find systems with AMD GPUs and check
uname -r,lsmod | grep amdgpu, and/dev/driexposure. - Confirm: consult your distribution’s security tracker or package changelog to verify whether the kernel package includes the fix for CVE‑2024‑42064.
- Patch: install vendor kernel updates that include the remediation and reboot into the patched kernel.
- Verify: run representative display and hot‑plug tests in staging; monitor kernel logs for regressions.
- Compensate: until patched, restrict access to
/dev/dri/*, avoid GPU passthrough to untrusted containers, and add SIEM/alerting rules for driver oops/pageflip timeouts.
Conclusion
CVE‑2024‑42064 is a practical, medium‑severity Linux kernel vulnerability in the AMD DRM display stack that can cause driver crashes when a pipe index is not set properly. The upstream community responded with a focused, low‑risk fix—to skip pipes that are not properly indexed—making the remediation straightforward for distributions to backport and for operators to deploy. Administrators should treat this as an important availability fix: verify whether affected kernels are present in their environments, apply vendor kernel updates, reboot into patched kernels, and implement compensations for hosts that cannot be immediately updated. Given the embedded kernel long tail and the potential for local DoS in exposed setups, the operational priority should be driven by exposure and configuration rather than a raw numeric score alone.Source: MSRC Security Update Guide - Microsoft Security Response Center