Microsoft’s one-line attestation that “Azure Linux includes this open‑source library and is therefore potentially affected” is an important, actionable statement — but it is not a technical guarantee that no other Microsoft product contains the same vulnerable NFS server code. The fix for CVE‑2024‑42078 addresses an upstream Linux kernel bug in the NFS server (nfsd) code — a component that appears in many different kernel builds and images — and Microsoft both publishes multiple Linux kernel artifacts and ships Linux kernels in other products such as WSL2 and Azure-targeted kernels. Organizations should therefore treat Azure Linux as a confirmed remediation priority while also performing artifact-level discovery across any Microsoft-supplied kernels, images, and appliances in their environment rather than assuming “only Azure Linux” is in scope.
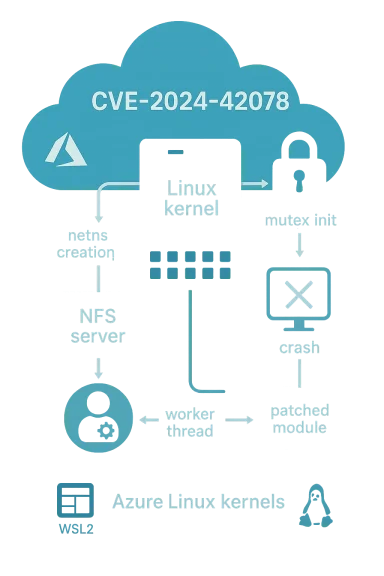
CVE‑2024‑42078 is an availability‑impacting bug in the Linux kernel’s NFS server (nfsd) code. The defect arises because the kernel’s nfsd_info.mutex is initialized too late in the netns setup path, allowing a worker (svc_pool_stats_start()) to dereference the mutex before it exists and potentially trigger a kernel oops or panic. Upstream kernel maintainers fixed this by moving the mutex initialization earlier so it cannot be dereferenced before it’s created. The issue is classified as a local‑attack, medium‑severity availability problem (CVSS ~5.5).
Microsoft’s public advisory for this CVE explicitly calls out Azure Linux as a product that “includes this open‑source library and is therefore potentially affected,” and notes that Microsoft began publishing machine‑readable CSAF/VEX attestations (a product‑by‑product attestation process) and will update the CVE mapping if other Microsoft products are identified as affected. That phrasing is precise: it confirms Azure Linux is in scope, and it promises further updates — but it does not assert exclusivity across all Microsoft artifacts. (msrc.microsoft.com)
Important caveat: having the configuration option present in the kernel config does not alone prove the runtime instance is vulnerable. You must verify the running kernel version, whether the vulnerable commit is present or backported, and whether nfsd is built-in or provided as a module.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CVE‑2024‑42078 is an availability‑impacting bug in the Linux kernel’s NFS server (nfsd) code. The defect arises because the kernel’s nfsd_info.mutex is initialized too late in the netns setup path, allowing a worker (svc_pool_stats_start()) to dereference the mutex before it exists and potentially trigger a kernel oops or panic. Upstream kernel maintainers fixed this by moving the mutex initialization earlier so it cannot be dereferenced before it’s created. The issue is classified as a local‑attack, medium‑severity availability problem (CVSS ~5.5).Microsoft’s public advisory for this CVE explicitly calls out Azure Linux as a product that “includes this open‑source library and is therefore potentially affected,” and notes that Microsoft began publishing machine‑readable CSAF/VEX attestations (a product‑by‑product attestation process) and will update the CVE mapping if other Microsoft products are identified as affected. That phrasing is precise: it confirms Azure Linux is in scope, and it promises further updates — but it does not assert exclusivity across all Microsoft artifacts. (msrc.microsoft.com)
What the vulnerability actually is (technical summary)
- The bug is in the Linux kernel’s nfsd (Network File System server) subsystem. It’s an improper initialization / race issue: nfsd_info.mutex can be dereferenced by svc_pool_stats_start() immediately after a new network namespace (netns) is created, before the mutex has been initialized. The result is a kernel oops or panic (availability/DoS).
- The practical impact is availability-related: an attacker with the ability to exercise the vulnerable code path locally (or to create the necessary timing conditions inside a VM/container) could cause a crash or kernel panic. There is no public evidence this CVE enables remote code execution. Multiple Linux distributors have published fixes and backported patches that neutralize the race by initializing the mutex earlier.
Why Microsoft named Azure Linux — and why that wording matters
When Microsoft says “Azure Linux includes this open‑source library and is therefore potentially affected,” they are doing two things:- Providing an authoritative, product‑level inventory attestation for Azure Linux — meaning Microsoft inspected that product family and found the implicated upstream kernel component in those builds. Customers running Azure Linux should treat that attestation and any associated VEX/CSAF metadata as the canonical signal to triage and patch. (msrc.microsoft.com)
- Describing a phased disclosure process: Microsoft’s VEX/CSAF rollout starts with specific product families (Azure Linux) and expands as inventories complete. The company’s promise to “update the CVE to reflect additional products if identified” is procedural; it does not prove other Microsoft artifacts are free of the code. In short: Azure Linux = confirmed; other Microsoft artifacts = unknown until verified. (msrc.microsoft.com)
Are other Microsoft products plausibly affected?
Short answer: Yes — it’s plausible that other Microsoft products could carry the same vulnerable code. Azure Linux is the only Microsoft product Microsoft has publicly attested to include the implicated nfsd code so far, but Microsoft maintains and distributes multiple Linux kernel artifacts that can, depending on build configuration and upstream commits, include nfsd:- WSL2 (Windows Subsystem for Linux): Microsoft publishes and ships a Microsoft‑maintained Linux kernel for WSL2. The WSL2 kernel configuration historically includes a number of optional subsystems; public kernel configs used by WSL kernels show NFS server options present in at least some WSL kernel builds (evidence: publicly available WSL kernel config samples include CONFIGNFSD entries). That means some WSL kernel builds can, and have, shipped with NFS server support enabled. Whether your* WSL installation is vulnerable depends on the specific WSL kernel version and config that is running.
- linux‑azure / Azure-targeted kernels and Marketplace images: Microsoft builds cloud-targeted kernels for use by Azure VM images and Marketplace offerings. Those kernel artifacts are a likely carrier for kernel subsystems used by server workloads, and they can diverge by build configuration and backport policy. If such kernels include the vulnerable upstream commit range or lack the backport, they may be affected.
- AKS node images, container host images, Marketplace appliances: Any Microsoft-supplied image that embeds a Linux kernel — or a third‑party Marketplace image that used Microsoft’s kernel build pipeline — should be treated as “unknown” until verified.
- Other specialized Microsoft artifacts: internal images, partner appliances, and test artifacts may also ship custom kernel builds. Those are not automatically covered by a single product-level attestation and must be checked separately.
Evidence that WSL kernels can include nfsd (why this matters)
Microsoft’s WSL kernel artifacts and the public kernel configuration templates used for WSL show that NFS-related kernel options are present in at least some WSL kernel configs. Publicly available WSL kernel config samples and community reproductions display CONFIGNFSD options (NFSv2/v3/v4, pNFS, block/scsi/flexfilelayout), which indicates that Microsoft’s WSL kernel can* include NFS server support depending on the build. That makes a blanket statement that “only Azure Linux includes the library” risky — a small number of WSL kernel builds may contain the same code-paths that CVE‑2024‑42078 fixes.Important caveat: having the configuration option present in the kernel config does not alone prove the runtime instance is vulnerable. You must verify the running kernel version, whether the vulnerable commit is present or backported, and whether nfsd is built-in or provided as a module.
How to verify exposure on systems you manage
Verification is an artifact‑level process. Below are practical, reproducible checks for Azure VMs, on‑prem Linux hosts, WSL2 instances, and other Microsoft-supplied images.Quick host checks (run as root or with sudo)
- Check the runtime kernel version:
- uname -a or cat /proc/version
- Inspect the kernel config (if present):
- zgrep CONFIG_NFSD /proc/config.gz || grep CONFIG_NFSD /boot/config-$(uname -r) || grep -i nfsd /boot/config-*
- If CONFIG*NFSD** values are set to “y” (built-in) or “m” (module), the kernel includes NFS server support at build time.
- Check for loaded NFS server modules:
- lsmod | grep -E 'nfsd|sunrpc'
- modinfo nfsd (returns module info if present)
- Check NFS server runtime artifacts:
- test for /proc/fs/nfsd or /proc/net/rpc/nfsd or /proc/keys (varies by kernel) — presence indicates NFS server is active or available.
- Confirm whether the kernel includes the upstream fix:
- Compare the running kernel’s exact version and vendor changelog with the upstream commit ID(s) listed in distro advisories or the upstream kernel git log. If vendor advisories list the fix as applied, the binary is no longer vulnerable. Consult vendor security bulletins (Ubuntu, SUSE, Oracle, etc.) for mapping.
WSL2-specific checks
- In WSL2, run uname -r to get the kernel version string (it usually contains “microsoft‑standard‑WSL2”).
- Check for /proc/config.gz or /boot/config-$(uname -r); many WSL kernels include the config. zgrep CONFIG_NFSD /proc/config.gz will reveal if NFS server support was compiled in. If the WSL kernel is Microsoft-supplied and includes CONFIG_NFSD set to y/m, that WSL kernel build could surface the vulnerable code-path.
Azure VM images and cloud instances
- Identify the image SKU and kernel package (linux-azure / linux-image-azure / vendor kernel) and consult that vendor’s advisory mapping for CVE‑2024‑42078.
- For Azure Linux instances specifically, follow Microsoft’s guidance and apply the published kernel updates for Azure Linux images. Microsoft committed to publishing VEX/CSAF attestations and updating CVE pages as additional products are identified. (msrc.microsoft.com)
Recommended mitigation and remediation steps
Treat the Azure Linux attestation as high priority; then expand verification and remediation across potentially impacted Microsoft artifacts in your estate.Immediate actions (within hours)
- If you run Azure Linux images, apply Microsoft’s kernel/image updates and reboot per the advisory. Azure Linux is the confirmed product Microsoft attested to. (msrc.microsoft.com)
- On any host where NFS server features are enabled and the kernel is in the affected version range (and the fix is not present), either:
- Install the vendor-supplied kernel patch and reboot; or
- Temporarily disable the NFS server functionality (stop and disable nfs-server / remove nfs-utils) if you do not require NFS server on that host.
- For WSL2 instances where NFS server support is present and you cannot immediately update the kernel, consider:
- Switching to a patched WSL kernel (if Microsoft has released one) via WSL updates; or
- Using a custom kernel that has the fix applied (advanced steps, requires care and testing).
Short‑term configuration mitigations (if patching or rebooting is delayed)
- Blacklist or unload the NFS server module (if modular):
- echo "blacklist nfsd" > /etc/modprobe.d/disable-nfsd.conf and rmmod nfsd (only if module usage allows safe unload).
- Remove or stop userland NFS server services:
- systemctl stop nfs-server && systemctl disable nfs-server
- Remove nfs-utils packages where they are not required.
- Limit local unprivileged access to the host and use host hardening until a patch is applied (strict RBAC, EDR/endpoint monitoring, restrict container access).
Long‑term steps (weeks)
- Inventory all Microsoft-supplied Linux kernel artifacts in your environment:
- Azure Linux images, linux‑azure kernels, WSL2 installations, AKS node images, Marketplace images, and any Microsoft-distributed container base images.
- Automate detection:
- Ingest Microsoft’s CSAF/VEX feeds (as they become available) into your vulnerability management system and correlate with your image inventory.
- Patch management:
- Maintain a prioritized patch plan: Azure Linux first (confirmed), then WSL2 endpoints and Azure Marketplace / AKS images as you verify exposure.
- Verify vendor fixes:
- Cross‑reference upstream kernel commit IDs with vendor changelogs or advisory mappings to ensure the fix was backported correctly.
- Identify all systems running Linux kernels in your estate (including WSL2 instances on developer machines).
- For each system, run the verification checks described above.
- Patch systems that are confirmed or likely affected; if patching is delayed, apply the configuration mitigations.
- Validate post‑patch: reboot and confirm the kernel version and the absence of the vulnerable behavior.
- Document the verification and remediation results and import Microsoft’s VEX/CSAF attestations as they are published.
Risk analysis and prioritization
- Attack complexity: Local and timing-dependent. Exploitation requires conditions that allow the vulnerable code path to run before the mutex is initialized. For that reason, the issue is less useful for remote attackers in default configurations but can be practically exploitable in multi‑tenant or containerized environments where an attacker can create the required race conditions.
- Impact: Availability (kernel oops/panic). Even if the bug cannot be turned into data theft or code execution, kernel panics in cloud VMs, hypervisor guests, or developer machines can cause significant operational outages and data loss risk if not mitigated.
- Likelihood on Microsoft platforms: Azure Linux — confirmed (MSRC attested). WSL2 — plausible (public WSL kernel configs show NFS server support in at least some builds). Other Microsoft artifacts — unknown until inventory and verification are completed. The operational posture should therefore be: patch Azure Linux immediately; assume WSL2 and Azure-targeted kernels could be affected until proven otherwise; verify and remediate other Microsoft artifacts on an artifact‑by‑artifact basis. (msrc.microsoft.com)
Why you can’t rely on an “only Azure Linux” interpretation
Two technical realities make an “only‑Azure‑Linux” assumption unsafe for defenders:- Kernel code is an artifact‑level property. Whether a particular image or product contains the vulnerable code depends on:
- The upstream commits merged or backported into that kernel build.
- The kernel configuration flags (CONFIG_NFSD, etc.) selected at compile time.
- Whether the module is built-in or shipped as a loadable module.
- Microsoft publishes multiple kernel artifacts. The company ships kernels for the cloud (linux‑azure), for WSL2, and for Azure Linux images. Each is a different build pipeline and requires separate inventory mapping. Microsoft’s decision to start VEX/CSAF with Azure Linux is pragmatic — it reduces ambiguity for that product — but it does not prove other products are unaffected. (msrc.microsoft.com)
Final takeaways for IT teams and administrators
- Treat Microsoft’s Azure Linux attestation as authoritative for Azure Linux images: apply Microsoft’s kernel updates for that product family without delay. (msrc.microsoft.com)
- Do not assume exclusivity. Other Microsoft-distributed kernels — notably WSL2 kernels and cloud-targeted kernel builds — can, depending on version and config, include the same NFS server code and therefore may be affected. Verify each artifact you run or distribute.
- Operational checklist: inventory, verify kernel configs, apply vendor patches, disable NFS server if unneeded, ingest Microsoft’s VEX/CSAF feed as it expands, and automate detection where possible.
- If you require a concise decision rule: patch Azure Linux now; treat other Microsoft-supplied Linux kernel artifacts as “unknown until verified” and prioritize those that run in multi‑tenant, production, or developer‑shared contexts.
Conclusion
CVE‑2024‑42078 is a Linux kernel NFS server bug that produces an availability risk. Microsoft’s statement that Azure Linux includes the implicated open‑source component is accurate and actionable for Azure Linux customers, but it is not a certificate that Azure Linux is the only Microsoft product that could possibly contain the vulnerable code. Microsoft ships multiple kernel artifacts — including the WSL2 kernel and Azure-targeted kernels — and public kernel configs demonstrate that NFS server features have been present in some Microsoft WSL kernel builds. The correct operational posture is clear: patch Azure Linux immediately, inventory and verify other Microsoft-supplied kernel artifacts (WSL2, linux‑azure, Marketplace/AKS images), and apply the configuration mitigations or module blacklists where immediate patching is not possible. Treat Microsoft’s VEX/CSAF outputs as an important automation input, but do your own artifact-level verification until Microsoft completes broader attestations. (msrc.microsoft.com)Source: MSRC Security Update Guide - Microsoft Security Response Center