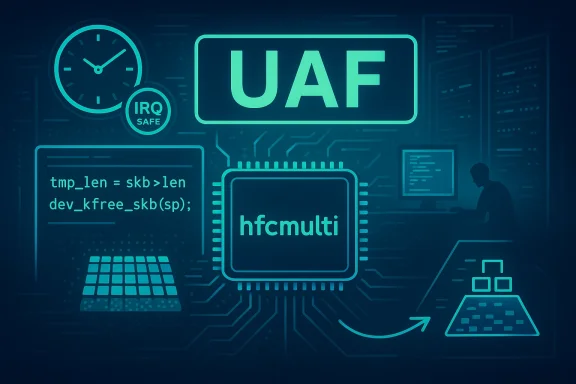
A subtle pointer mix-up in the Linux kernel’s mISDN telephony driver — a use‑after‑free in hfcmulti_tx() — landed as CVE‑2024‑42280 and serves as another clear reminder that tiny lifecycle mistakes in kernel code can produce outsized operational pain for operators and vendors alike. The flaw is simple to describe: the code frees an sk_buff and then later dereferences the same pointer; the upstream fix is equally small (capture the needed skb metadata before freeing and use the saved value), but the practical consequence can be a deterministic kernel oops or repeated instability that fully denies availability for affected hosts.
mISDN is the Linux kernel’s module set for supporting a variety of ISDN hardware, historically important for telephony and certain embedded communications appliances. The affected function, hfcmulti_tx(), lives in the hfcmulti driver (drivers/isdn/hardware/mISDN/hfcmulti.c) and is responsible for transmitting frames from kernel sk_buffs onto ISDN hardware FIFO queues. In short: it handles low‑level transmit path bookkeeping and is executed in performance- and timing-sensitive contexts, sometimes under spinlocks and in interrupt‑adjacent code paths.
CVE‑2024‑42280 was publicly recorded on 17 August 2024 and is classified as a kernel memory corruption / use‑after‑free (UAF) vulnerability. Public trackers assign it a high‑impact severity profile (commonly CVSS v3.1 ≈ 7.8) and label the primary attack vector as local — an untrusted or low‑privileged local actor with the ability to interact with the mISDN driver can trigger the problematic path.
Why this matters to admins: kernel UAFs are hostile to system stability. In practice the most reliable outcome is a kernel oops (crash) or persistent instability — immediately affecting availability — though, in theory, memory corruption in kernel context can be escalated to information disclosure or code execution in highly constrained exploit chains. Multiple vulnerability analyses emphasize availability as the most likely and actionable consequence.
Upstream maintainers fixed the bug with a small, surgical change: capture the value(s) needed from the skb (for example its length) into a temporary local before calling dev_kfree_skb(), then use the saved value afterwards instead of accessing the freed pointer. The actual diff shows the introduction of a tmp_len variable assigned from (sp)->len before the free, and later references that tmp_len rather than dereferencing *sp after free. This narrowly targeted change eliminates the UAF window while preserving the original logic.
Two operational facts make this class of bug more dangerous than its single‑line fix suggests:
Important operational note: some scanning tools and Nessus plugins flagged systems as vulnerable when vendor packages were not yet patched or when kernels compiled with the driver present were in use. If your environment uses custom kernels or long‑lived embedded images, the remediation burden will be higher because vendor backports may not align with your support cycle.
If you run systems that might touch ISDN hardware or custom kernels with mISDN support, prioritize this CVE: confirm whether the hfcmulti driver is present or loaded, apply vendor patches or upstream commits that include the tmp_len-style fix, and add detections for kernel oops patterns tied to the hfcmulti stack. The fix is simple — but the cost of ignoring it can be a full outage at precisely the wrong moment.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
mISDN is the Linux kernel’s module set for supporting a variety of ISDN hardware, historically important for telephony and certain embedded communications appliances. The affected function, hfcmulti_tx(), lives in the hfcmulti driver (drivers/isdn/hardware/mISDN/hfcmulti.c) and is responsible for transmitting frames from kernel sk_buffs onto ISDN hardware FIFO queues. In short: it handles low‑level transmit path bookkeeping and is executed in performance- and timing-sensitive contexts, sometimes under spinlocks and in interrupt‑adjacent code paths.CVE‑2024‑42280 was publicly recorded on 17 August 2024 and is classified as a kernel memory corruption / use‑after‑free (UAF) vulnerability. Public trackers assign it a high‑impact severity profile (commonly CVSS v3.1 ≈ 7.8) and label the primary attack vector as local — an untrusted or low‑privileged local actor with the ability to interact with the mISDN driver can trigger the problematic path.
Why this matters to admins: kernel UAFs are hostile to system stability. In practice the most reliable outcome is a kernel oops (crash) or persistent instability — immediately affecting availability — though, in theory, memory corruption in kernel context can be escalated to information disclosure or code execution in highly constrained exploit chains. Multiple vulnerability analyses emphasize availability as the most likely and actionable consequence.
The technical root cause — what actually went wrong
At the heart of CVE‑2024‑42280 is a classic lifetime management error: the code frees an sk_buff via dev_kfree_skb(sp) but later uses sp (for example to read skb->len). Because freeing an skb returns that memory to the kernel heap, any subsequent dereference of sp becomes a use‑after‑free — undefined behavior that can crash the kernel or corrupt adjacent data.Upstream maintainers fixed the bug with a small, surgical change: capture the value(s) needed from the skb (for example its length) into a temporary local before calling dev_kfree_skb(), then use the saved value afterwards instead of accessing the freed pointer. The actual diff shows the introduction of a tmp_len variable assigned from (sp)->len before the free, and later references that tmp_len rather than dereferencing *sp after free. This narrowly targeted change eliminates the UAF window while preserving the original logic.
Two operational facts make this class of bug more dangerous than its single‑line fix suggests:
- hfcmulti_tx() executes in tight transmit paths and, historically, parts of the hfcmulti/hfcpci drivers have performed skb frees or queue manipulations while holding spinlocks or in contexts where freeing must be done with IRQ‑safe helpers. Upstream commit messaging and related fixes explicitly call out the rule that certain skb free paths must use IRQ‑safe variants (for example, dev_kfree_skb_irq) or must move work out of the locked region. Improperly freeing or consuming skbs under spinlocks is itself a recipe for timing-dependent failures.
- The kernel’s allocator and slab layout can make UAF outcomes non‑deterministic across kernel versions and architectures: sometimes the immediately freed memory still holds the old contents and dereferences read valid-looking values, other times the memory is reused quickly and dereferences produce immediate panics. For maintainers and operators this unpredictability translates into intermittent, hard‑to‑diagnose crashes.
Impact and attack surface
What the vulnerability can actually do in deployed environments depends on three factors: whether the host kernel includes the hfcmulti/hfcpci driver, whether the device is present and the driver is loaded, and whether an attacker (or a misbehaving local process) can exercise the transmit path in a way that triggers the free‑then‑use sequence.- Primary impact: Availability. A triggered kernel oops or repeated crashes will cause immediate loss of service on the host until reboot or until the faulty code path is eliminated. For single‑node appliances this means a full denial‑of‑service. In clustered or redundant architectures the blast radius is smaller but still operationally expensive (reconvergence, session loss, control‑plane instability).
- Secondary risk: memory corruption / potential escalation. While turning a UAF into reliable code execution in kernel context is a difficult and environment‑specific task, the theoretical potential exists. Most public analyses emphasize DoS as the realistic threat, but they prudently classify confidentiality and integrity impacts as non‑impossible.
- Attack vector: Local. The NVD/trackers describe the attack vector as AV:L (local). That means an attacker must have local access or the ability to submit transactions that exercise the hfcmulti transmit path. In real-world deployment this can be low‑privilege local access, a misconfigured service that bridges user inputs to the driver, or even a malicious guest in a virtualized environment that can manipulate passthrough devices.
- Exploitability: Low-to-moderate for DoS; difficult for remote RCE. DoS is straightforward (a well‑crafted sequence can repetitively hit the errant path); remote code execution would require precise heap manipulation and is considered less likely absent additional kernel flaws. Public telemetry does not show widespread active exploitation tied to a PoC at disclosure, but the presence of the bug in widely distributed kernel trees made it an urgent remediation target for affected vendors.
Affected kernels, distributions and patch status
Public vulnerability trackers and distributor advisories map the issue across many upstream trees because the mISDN code exists across long‑lived kernel series. Multiple trackers list patched thresholds and backports; representative guidance includes:- NVD / MITRE summary of the vulnerability and the canonical description of the free‑then‑dereference error.
- CVE aggregators (CVE Details / OpenCVE) that list affected kernel ranges and typical patched versions (several 5.x and 6.x series thresholds were included in various trackers).
- Vendor trackers and distribution advisories — Debian, Oracle Linux, Amazon Linux and Tenable’s plugin listings — show divergent patch coverage: some distributions issued fixed packages quickly, others required backports, and a small number of vendor packages were initially listed as “no fix” or “deferred” until the stable backports were applied. Always check your distribution advisory for the definitive package name and fixed version.
Important operational note: some scanning tools and Nessus plugins flagged systems as vulnerable when vendor packages were not yet patched or when kernels compiled with the driver present were in use. If your environment uses custom kernels or long‑lived embedded images, the remediation burden will be higher because vendor backports may not align with your support cycle.
Mitigation, detection and verification
Immediate steps (minutes to hours)- If the mISDN functionality is not required on a host, blacklist or unload the hfcmulti/hfcpci modules. Removing the driver eliminates the local attack surface. Use your distribution’s module blacklist mechanism (for example add a blacklist entry under /etc/modprobe.d/) and remove loaded modules with rmmod if safe to do so. Community practice for disabling hfcmulti has long existed for operators who do not use the B410P and similar hardware. Only remove modules after confirming that the module isn’t providing essential device services for that host.
- Where you cannot remove the module, consider isolating the host: restrict local access and harden user namespaces or container capabilities so unprivileged users cannot reach device interfaces that exercise the transmit path. Tighten NET_RAW / NET_ADMIN controls and any facility that allows userland to hand skbs into kernel transmit paths.
- Patch / upgrade to the vendor’s fixed kernel package as soon as it is available. If you build kernels from upstream sources, apply the upstream hfcmulti commit that saves the needed skb metadata prior to free (the tmp_len fix) and rebuild. Confirm the fix by checking for the commit in your kernel’s changelog or by grepping the local source for the tmp_len pattern introduced in the patch.
- Verify package status on your distro’s security tracker (Debian Security Tracker, Red Hat Errata, Oracle Linux CVE repo, etc.). If your vendor has published an erratum or livepatch, follow the vendor’s recommended update path for production safety.
- Watch for kernel oops traces referencing the hfcmulti/hfcpci stack frames and for repeated kernel panics correlated with ISDN device use or module unload/load sequences. Preserve crash dumps (kdump) and the kernel ring buffer (dmesg/journalctl -k) for analysis.
- In controlled labs only: reproduce using the upstream test vectors or targeted exercises that trigger the hfcmulti transmit path after applying the fix to ensure the crash no longer occurs. Do not execute PoCs in production. Several advisories show minimal reproducer steps for other kernel CVEs; for this UAF, the authoritative verification is presence of the upstream commit in your deployed kernel tree.
Remediation playbook — a prioritized checklist
- Inventory: Enumerate hosts with hfcmulti/hfcpci code present in the kernel and list those where the module is loaded and devices are bound. Use uname -r, lsmod, and your CMDB to identify affected builds.
- Immediate containment: If mISDN is unused, blacklist hfcmulti/hfcpci and unload modules where safe. Verify that services depending on those modules are not impacted.
- Patch path: For each affected host, determine whether to (a) install vendor-supplied patched kernel packages; (b) apply vendor livepatches; or (c) rebuild a kernel with the upstream hfcmulti commit applied. Prefer vendor packages for ease of maintenance unless your environment requires custom kernels.
- Validate: Confirm the fix is present in the running kernel by inspecting /proc/config.gz or your kernel source tree for the commit, or by verifying that the crash no longer repros in an isolated lab.
- Monitor: Add alerts for unexpected kernel oopses and for repeated module load/unload events connected to the ISDN device stack. Correlate these with user sessions and container/VM guest events to detect potential targeted attempts to trigger the path.
Why the fix is small — but why the risk persists
The remediation for CVE‑2024‑42280 is conceptually tiny: read what you need from the skb before freeing it and never touch freed memory. The git diff and commit message reflect that surgical change. But small patches in source code do not always translate into fast operational remediation for three practical reasons:- Distribution and vendor packaging lag: vendors must decide whether to backport the fix into supported stable kernel branches, build and test packages, and then publish them. That pipeline takes time, and operators using vendor kernels must wait for the vendor’s cadence. Public trackers showed a mix of fast and deferred vendor responses.
- Embedded / appliance images: many telephony, industrial and embedded devices run long‑lived kernel images that are not updated frequently. The “patch is small” reality does not help devices that are not reachable via a vendor firmware pipeline. These long tails are the most enduring operational risk.
- Debugging and operational practices: freeing mistakes commonly occur in code paths that were written for performance or that run under locks; fixing them requires care to avoid regressions (e.g., moving frees outside spinlocks or switching to IRQ‑safe free helpers). That makes the change safe but requires diligent testing to avoid introducing new races. Upstream patch notes in related commits explicitly call out the need to avoid kfree_skb under spin_lock_irqsave and to use queue reorderings when necessary.
Broader lessons for kernel engineering and operations
- Treat diagnostic and fast‑path code with equal rigor. Debugging helpers and transmit/receive optimizations are often written quickly; their privileges and timing assumptions mean small errors become large outages. The hfcmulti fix is a reminder that diagnostic convenience is not a substitute for lifecycle correctness.
- Defensive coding: always capture necessary metadata before destroying objects, and enforce strict rules about what can be done under spinlocks or interrupt-disabled regions. Use the kernel’s documented helpers (dev_kfree_skb_irq, skb_queue_splice_init, etc.) when freeing in sensitive contexts. The upstream fixes for related mISDN commits expressly adopt these patterns.
- Inventory and least privilege: shrink the local attack surface by keeping drivers and modules out of hosts that don’t use them. Blacklist unused modules in images and enforce strict capabilities for untrusted processes to prevent local actors from exercising hardware paths.
- Timely patching plus compensating controls: because vendor backports can be uneven, operators must combine quick mitigations (module blacklist, isolation) with a prioritized patch plan and strong monitoring to shorten the window of exposure.
Conclusion
CVE‑2024‑42280 is an archetypal kernel vulnerability: the coding mistake—dereferencing sp after dev_kfree_skb(sp)—is a concise human error, the upstream fix is a handful of lines, and the real-world impact is acute: repeated or deterministic kernel oopses that fully deny availability for affected systems. The hard work after such a fix is not the code change itself, but the operational cleanup: inventorying affected hosts, coordinating vendor backports or rebuilds, applying mitigations where immediate patching is infeasible, and instituting development controls that prevent the next life‑cycle bug from slipping through.If you run systems that might touch ISDN hardware or custom kernels with mISDN support, prioritize this CVE: confirm whether the hfcmulti driver is present or loaded, apply vendor patches or upstream commits that include the tmp_len-style fix, and add detections for kernel oops patterns tied to the hfcmulti stack. The fix is simple — but the cost of ignoring it can be a full outage at precisely the wrong moment.
Source: MSRC Security Update Guide - Microsoft Security Response Center