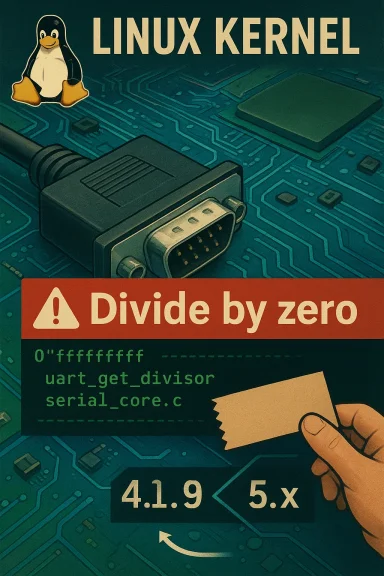
A divide‑by‑zero bug in the Linux kernel’s serial core — tracked as CVE‑2024‑43893 — can be triggered by a malformed TIOCSSERIAL ioctl and lead to a kernel oops that knocks a host offline; the defect has been fixed upstream and backported into stable trees, but administrators and embedded device operators must treat this as an availability‑first risk and patch or mitigate promptly.
The Linux kernel’s serial subsystem provides the low‑level plumbing for UART (Universal Asynchronous Receiver/Transmitter) ports. One of the ioctl interfaces used to manipulate serial port parameters is TIOCSSERIAL, which accepts a user‑supplied structure containing, among other fields, a
CVE‑2024‑43893 describes a short but consequential logic error: if an attacker (or buggy local program) supplies an invalid
This is explicitly an availability issue: confidentiality and integrity are not directly affected by the bug as reported, but the impact is a hard crash or sustained denial of service (DoS) for the host (or at least its serial subsystem), matching worst‑case availability outcomes described by canonical advisories.
Why the timing matters: if the zero‑check happens only after other fields are modified, a malformed TIOCSSERIAL can leave the port state inconsistent, allowing repeated calls to re‑trigger the bad path; the fix prevents the dangerous transition by failing fast.
Important operational nuance: not every kernel build that includes serial code is necessarily exploitable in practice. Factors that constrain real exposure include:
1.) Inventory and patch servers exposing serial devices to untrusted users.
2.) Apply kernel updates from vendor channels or canonical upstream backports.
3.) Add short‑term restrictions on device node permissions and enable kernel logging alerts.
4.) For appliances/devices under vendor support, coordinate OEM firmware/kernel patches.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
The Linux kernel’s serial subsystem provides the low‑level plumbing for UART (Universal Asynchronous Receiver/Transmitter) ports. One of the ioctl interfaces used to manipulate serial port parameters is TIOCSSERIAL, which accepts a user‑supplied structure containing, among other fields, a baud_base value used in calculating rate divisors.CVE‑2024‑43893 describes a short but consequential logic error: if an attacker (or buggy local program) supplies an invalid
baud_base so that the computed uartclk becomes zero, a subsequent call into the divisor computation — uart_get_divisor() — will perform a division by uartclk and trigger a kernel divide‑by‑zero panic. The fatal trace points to drivers/tty/serial/serial_core.c and the usual serial8250 helper paths. Public vulnerability trackers and vendor advisories summarize the flaw in consistent terms.This is explicitly an availability issue: confidentiality and integrity are not directly affected by the bug as reported, but the impact is a hard crash or sustained denial of service (DoS) for the host (or at least its serial subsystem), matching worst‑case availability outcomes described by canonical advisories.
Why this matters (threat model and real‑world exposure)
- Attack vector: Local. The vulnerability requires the ability to call ioctl on a serial device node or otherwise interact with the kernel’s serial ioctl paths. That typically means either local user access or a privileged local process. The accepted CVSS vector reflects an AV:L attack vector.
- Impact: Availability (kernel oops / panic). The bug leads to a divide‑by‑zero inside kernel space; the observed result is a kernel oops and service disruption. The official scoring and vendor advisories characterize the incident as “Medium” overall with a high availability consequence.
- Complexity & prerequisites: Low to moderate. An unprivileged local process that can open and ioctl a serial device may be sufficient; in other environments additional constraints (device present, driver loaded, device permissions) reduce exposure. There are no widely reported remote exploitation paths that allow an unauthenticated network actor to reach these code paths without prior local access.
- Typical targets: Systems that expose serial device nodes to untrusted local users, embedded devices and appliances that rely on UART for management consoles, and development or vendor builds that grant broader access to serial interfaces. Cloud images are less likely to be exposed unless a serial device node is present and accessible in a multi‑tenant environment.
Technical analysis: what goes wrong in the code
At a technical level the sequence is straightforward and small‑scale, which makes it easy to reason about yet still impactful:- An application issues TIOCSSERIAL with a struct_serial that contains a
baud_basevalue. - Kernel code computes uartclk (the effective UART clock source) using that input.
- If
baud_baseis invalid (or otherwise leads to a computeduartclk == 0), subsequent calls into uart_get_divisor() perform arithmetic that divides by uartclk. - The divide by zero results in a kernel exception (oops), and the thread (and possibly the system) crashes or becomes unavailable.
uartclk == 0 early in uart_set_info() (before making other state changes) so that invalid, zero, or nonsensical values are rejected and do not poison subsequent calls for the same port. This protective check was merged into upstream and backported into multiple stable branches.Why the timing matters: if the zero‑check happens only after other fields are modified, a malformed TIOCSSERIAL can leave the port state inconsistent, allowing repeated calls to re‑trigger the bad path; the fix prevents the dangerous transition by failing fast.
What versions and builds are affected
Public trackers and vendor advisories map this defect to many kernel stable series because the fix was backported widely. Broadly reported affected ranges and backports include kernels across older and current stable trees; distributors have applied fixes into their packaged kernels. Real exposure depends on whether the serial driver used on the host is present and whether runtime/device permission configurations allow untrusted code toioctl serial nodes. Representative references include NVD, vendor advisories (Ubuntu, Oracle, Amazon Linux), and stable commit lists showing the fix propagated into 4.19, 5.x and relevant 6.x stable maintenance branches.Important operational nuance: not every kernel build that includes serial code is necessarily exploitable in practice. Factors that constrain real exposure include:
- Whether the target device exposes a serial character device that unprivileged users can open.
- Whether the particular serial driver (e.g., serial8250) is loaded and used for that device.
- Distribution kernel build flags and runtime protections around device nodes and ioctl access.
Exploitation likelihood and observed activity
- As of public advisories and aggregator dashboards at disclosure, there were no credible reports of widespread weaponized exploitation targeting CVE‑2024‑43893. Trackers report low EPSS / exploit probabilities relative to high‑priority remote‑code vulnerabilities. That said, the bug is straightforward to trigger when prerequisites are met, so targeted local DoS is plausible.
- The most likely real‑world exploit would be a local script or process that opens the serial device, issues crafted ioctl calls with a bad
baud_base, and either crashes the kernel or leaves the port in a bad state that prevents new serial sessions. The attacker doesn’t gain code execution or data leaks from the bug (per current public analysis), but they can deny service.
Vendor response and patch status
- Upstream kernel: the patch to add a
uartclk == 0check was accepted into upstream and merged into stable trees; maintainers and Greg KH’s stable backports list show the patch present in multiple stable branches. - Distributions & vendors: major vendors and distributors — Ubuntu, Debian, Oracle Linux, Amazon Linux (ALAS notifications), and others — listed the fix in their security advisories and produced updated kernel packages or backports. Administrators should consult their vendor advisory to identify the fixed package name and version for their distribution.
- Workarounds and livepatches: some vendors may provide livepatch updates or kernel livepatch modules that include this change for supported kernels; otherwise the standard remediation is to install the updated kernel package and reboot (or apply a vendor livepatch where available).
Detection: telemetry and indicators-of‑compromise
Because this is a kernel availability issue, detection focuses on kernel logs and device behavior:- Watch dmesg / systemd journal for oops traces mentioning uart_get_divisor, serial_core.c, or the serial8250 call stack. The vulnerability description and example stack traces are explicit about where the crash will land.
- Monitor for repeated unexplained kernel oopses or sudden loss of serial console responsiveness on devices that rely on UART.
- Audit device node permissions for
/dev/ttyS[I],/dev/ttyUSB[/I], and other serial endpoints. Unexpected writable access for untrusted users is a red flag. - For embedded fleets, correlate support tickets or device reboots with changes in device configuration or with local tasks that might open serial devices.
Mitigation and remediation playbook (recommended actions)
- Inventory serial exposure
- Identify devices that expose serial character devices and note whether those nodes are available to unprivileged users.
- Check which serial drivers are present (lsmod, dmesg) and whether serial8250 or similar modules are loaded.
- Patch promptly
- Install vendor/distribution kernel updates that include the upstream fix. Confirm package names and exact versions with your vendor advisory and schedule reboots where needed. For many Linux distros, the fix is already packaged in point releases; consult Ubuntu/Debian/Oracle/ALAS advisories for exact versions.
- Apply temporary controls if immediate patching is impossible
- Restrict local access to serial device nodes (change group ownership, remove world‑writable or world‑readable permissions).
- Where feasible, temporarily unbind or blacklist unused serial drivers, or remove device nodes for unused UARTs.
- If the device supports vendor livepatching, evaluate applying a livepatch that backports the fix without a full reboot.
- Harden host privileges
- Ensure untrusted accounts do not have elevated access to device nodes that can issue ioctls.
- Use mandatory access control (AppArmor, SELinux) to constrain processes from opening serial devices unless explicitly allowed.
- Monitor and respond
- Add kernel oops detection rules to SIEM and response playbooks. If a host shows the trace associated with uart_get_divisor, throttle access and schedule remediation.
- Document and notify
- For embedded/OEM fleets, coordinate a targeted update rollout. Devices in the field with long lifecycle must be mapped and vendor OEM updates tracked.
1.) Inventory and patch servers exposing serial devices to untrusted users.
2.) Apply kernel updates from vendor channels or canonical upstream backports.
3.) Add short‑term restrictions on device node permissions and enable kernel logging alerts.
4.) For appliances/devices under vendor support, coordinate OEM firmware/kernel patches.
Broader implications for embedded devices, IoT and multi‑tenant systems
This category of kernel bug highlights two recurring themes:- Small correctness bugs in rare ioctl paths can produce outsized operational pain for devices that expose hardware controls (serial, modem, etc.). Embedded appliances and IoT devices commonly expose UARTs for management; if those endpoints are reachable or can be controlled by untrusted local code (or by a compromised service), the availability risk becomes concrete.
- Vendor kernel builds and OEM appliances often ship with different configurations (debug knobs, module parameters) than mainstream distribution kernels, so assumptions about exposure must be verified per product. Security advisories from distributors may not map one‑to‑one to OEM firmware. Always validate whether a vendor’s device is actually shipping the vulnerable code path and whether an upstream patch is present in vendor firmware.
Critical appraisal: strengths of the upstream fix and residual risks
Strengths:- The upstream fix is minimal, well‑scoped and defensive: checking
uartclk == 0early prevents state corruption and stops repeated exploitation for the same port. It avoids heavy rewrites and is safe to backport. The change landed across stable trees, showing maintainers prioritized backporting. - Vendor adoption: multiple distributors (Ubuntu, Debian, Oracle, Amazon Linux) issued advisories and fixed packages, giving operators clear remediation routes.
- Patching lag: long‑lifecycle embedded devices and some OEM appliances may not receive timely firmware/kernel updates; those fleets remain exposed unless the vendor provides a backport. Operators must track vendor advisories and apply mitigations when patches aren’t available.
- Misclassification risk: public automated scorecards sometimes misclassify kernel defects (for example, suggesting a network vector or inflated CVSS). Analysts must validate vector and exploitation prerequisites against authoritative advisories rather than blindly trusting aggregated machine summaries. Several trackers cautioned about inconsistent scoring at first glance.
- Detection limitations: kernel oops traces are often noisy and can be missed in high‑volume telemetry without targeted alerting; organizations should add explicit rules for the function names and call traces referenced in advisories.
Quick checklist for sysadmins (actionable)
- Identify: run a quick inventory of hosts that expose serial device nodes and note which users/groups can access them.
- Patch: prioritize installing vendor kernel updates that include the upstream stable patch; reboot according to maintenance windows.ily restrict serial device access via file permissions or MAC policies if patching will be delayed.
- Monitor: add SIEM alerts for kernel oops traces referencing uart_get_divisor or serial_core functions.
- Verify: after patching, validate that serial device operations (normal termios calls) behave as expected and that no new oops traces appear.
Conclusion
CVE‑2024‑43893 is a compact, reproducible kernel vulnerability that underscores how small, defensive checks matter deeply in kernel code. The defect’s root cause — a missing check that allowed uartclk to be zero and then be used as a divisor — is trivial to explain and trivial to fix, yet the operational effect is material: a local attacker or faulty userland can cause a host outage. The community response was appropriate: a targeted upstream fix that was backported into stable trees and packaged by major distributors. Administrators should treat this as a straightforward patch‑and‑verify task: inventory serial exposure, apply vendor patches, restrict local access where necessary, and enable detection for the serial‑stack oops trace. For embedded and OEM device operators, the harder work is coordinating vendor firmware updates and ensuring that devices in the field receive backports or temporary mitigations.Source: MSRC Security Update Guide - Microsoft Security Response Center