Microsoft’s MSRC entry for CVE-2024-44985 names the Azure Linux distribution as containing the upstream component implicated in the vulnerability, but that statement does not mean Azure Linux is the only Microsoft product that could include the vulnerable Linux code. In plain terms: Azure Linux is the only Microsoft product Microsoft has attested (via CSAF/VEX) to include the component so far, but other Microsoft-distributed kernels and images may also carry the same vulnerable code depending on the kernel version, build configuration and backport history. This article explains why that distinction matters, walks through how to determine if your Microsoft-supplied systems are affected, and gives concrete remediation and mitigation steps for administrators and defenders.
CVE-2024-44985 is a Linux kernel vulnerability in the IPv6 transmit path — a use-after-free (UAF) condition in the ip6_xmit() routine that can occur when skb_expand_head() fails and frees resources that are later referenced. Upstream kernel maintainers fixed the code by extending RCU protection in the affected code paths to prevent the UAF. Multiple stable kernel series were patched, and distribution vendors subsequently released fixes in their kernel packages.
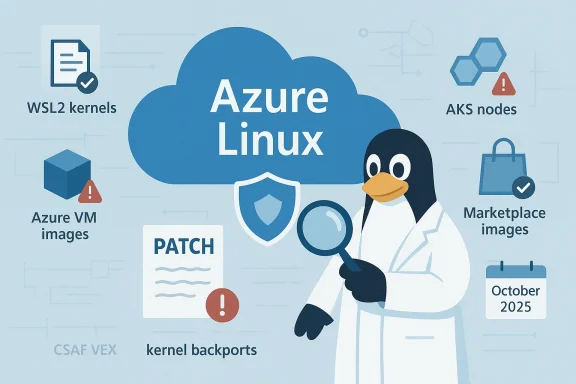
Microsoft’s Security Response Center (MSRC) entry for this CVE contains the FAQ language many administrators have seen: Azure Linux “includes this open-source library and is therefore potentially affected,” and Microsoft states it began publishing machine-readable CSAF/VEX attestations in October 2025 and will update CVEs if additional products are identified. That wording is deliberately scoped: it attests presence of the component in a named Microsoft product (Azure Linux) rather than asserting the component is absent from every other Microsoft product.
Why this matters operationally: Microsoft ships and maintains multiple Linux artifacts across its product portfolio — some of which include compiled Linux kernels or kernel images. Any artifact that ships a Linux kernel built from vulnerable versions may therefore be potentially affected. Administrators and risk owners must therefore treat the MSRC attestation as an authoritative confirm for Azure Linux while performing independent inventory on other Microsoft-supplied kernels and images.
Microsoft’s language around CVE-2024-44985 is accurate but narrowly scoped: Azure Linux is confirmed in-scope because Microsoft attested it, but that confirmation doesn’t equal exclusivity. Any Microsoft artifact that ships a Linux kernel must be checked individually. The defensible path for operators is straightforward: inventory, verify kernel versions, patch quickly, and — until vendors complete broader attestations — assume other Microsoft-distributed kernels are potentially in scope and verify them accordingly.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CVE-2024-44985 is a Linux kernel vulnerability in the IPv6 transmit path — a use-after-free (UAF) condition in the ip6_xmit() routine that can occur when skb_expand_head() fails and frees resources that are later referenced. Upstream kernel maintainers fixed the code by extending RCU protection in the affected code paths to prevent the UAF. Multiple stable kernel series were patched, and distribution vendors subsequently released fixes in their kernel packages.Microsoft’s Security Response Center (MSRC) entry for this CVE contains the FAQ language many administrators have seen: Azure Linux “includes this open-source library and is therefore potentially affected,” and Microsoft states it began publishing machine-readable CSAF/VEX attestations in October 2025 and will update CVEs if additional products are identified. That wording is deliberately scoped: it attests presence of the component in a named Microsoft product (Azure Linux) rather than asserting the component is absent from every other Microsoft product.
Why this matters operationally: Microsoft ships and maintains multiple Linux artifacts across its product portfolio — some of which include compiled Linux kernels or kernel images. Any artifact that ships a Linux kernel built from vulnerable versions may therefore be potentially affected. Administrators and risk owners must therefore treat the MSRC attestation as an authoritative confirm for Azure Linux while performing independent inventory on other Microsoft-supplied kernels and images.
What CVE-2024-44985 is and why it matters
The technical core, in plain language
- The vulnerability arises in the IPv6 packet transmit path when the kernel attempts to increase skb (socket buffer) headroom using skb_expand_head().
- If that call fails (returns NULL), the skb and associated destination/device pointers can be freed while later code still references them, creating a use-after-free situation.
- The upstream fix adds RCU (read-copy-update) protection around the relevant operations so that the references remain valid while used, preventing the UAF.
- Exploitation potential: depending on environment and attacker capabilities, UAFs in the kernel can cause crashes (denial of service) or, in the worst case and given suitable memory layout primitives, enable arbitrary code execution in kernel context. At minimum this is a high-risk integrity/availability issue for affected kernels.
Which kernel series are implicated
The vulnerability was fixed in multiple stable kernel branches. The affected ranges published by vulnerability databases and vendor advisories cover several kernel versions (for example: kernel series starting with 5.15, 5.16, 6.2 and others had vulnerable commits until their respective stable releases incorporated the fix). Whether a specific kernel is vulnerable depends on the exact kernel version and the commit range applied (including vendor backports). This makes per-system verification essential.What Microsoft actually said — and what they didn’t say
Microsoft’s public language about the CVE does three things:- Confirms Microsoft scanned the Azure Linux product family and found the implicated upstream component — hence Azure Linux is listed as “potentially affected.”
- Explains Microsoft’s transparency work (CSAF/VEX) and that they began publishing machine-readable attestations starting October 2025.
- Commits to updating CVE entries if additional Microsoft products are found to include the component.
- It does not say Microsoft exhaustively scanned every Microsoft image, kernel binary, Marketplace VM, AKS node image, WSL kernel build, or appliance and proved the component is absent from all other product families.
- It does not guarantee that other Microsoft-distributed artifacts do not include the vulnerable code.
Why other Microsoft products might also be candidates
Microsoft distributes multiple artifacts that can include the Linux kernel or components of it:- Azure Linux (attested): Microsoft’s cloud-optimized Linux distribution (formerly CBL-Mariner or branded as the Azure Linux distro) was scanned and attested as including the implicated code.
- WSL2 (Windows Subsystem for Linux): Microsoft builds and ships a Linux kernel for WSL2. The WSL2 kernel source and configuration are publicly available, and Microsoft issues kernel builds and updates via Windows Update. That kernel line may include vulnerable commits depending on the branch and the build’s patch level.
- Azure VM images, curated kernels and linux-azure builds: Some Azure VM SKUs and Marketplace images use Microsoft-maintained kernel builds or Azure-tuned kernel packages. Those kernels differ by image and may carry backports or differing CONFIG_* options that affect whether the vulnerable code is present or reachable.
- AKS node images and managed offerings: Node images used by managed Kubernetes services can include kernels provided by Microsoft or by partners, again depending on image choice and image lifecycle.
- Partner-supplied images distributed through Microsoft channels: Marketplace images or partner appliances can ship kernels built by third parties; Microsoft’s attestation does not automatically cover third-party marketplace artifacts.
- Specialized appliances and internal images: Internal appliance kernels, management appliances, or container host images used in managed services are separate artifacts and may include vulnerable code.
How to determine if your Microsoft-supplied system is affected
Detection is straightforward if you have access to the system. The essential steps are:- Inventory Microsoft-supplied artifacts in your environment
- List Windows hosts running WSL2.
- List Azure VMs that use Microsoft-published images (for example, Azure Linux, Azure Marketplace images, or images that use linux-azure kernels).
- List AKS cluster node images and any managed appliance images you host.
- Check the runtime kernel version on each Linux endpoint
- Run uname -r (or uname -a) inside the distribution or VM to capture the kernel release string.
- Check /proc/version and /boot/* for packaged kernel names where applicable.
- For WSL2, run a WSL shell and execute uname -r to see the kernel version used by that WSL instance.
- Compare kernel versions to the published affected ranges
- Use vendor advisories and the authoritative CVE details to check whether your kernel version falls inside a vulnerable range. Remember that vendor backports may mean a kernel version number doesn’t tell the full story; a distro may backport the fix into an older-looking version.
- Inspect kernel package changelogs or vendor advisories
- For Azure Linux or any distribution, check the vendor-supplied kernel package changelog or patch advisory to confirm whether the CVE fix was applied.
- Use Microsoft’s CSAF/VEX attestations and published advisories
- Consult MSRC product attestations for Azure Linux and monitor the MSRC update guide for changes that add other product families to the attestation list.
- When in doubt, treat it as “unvalidated” and apply mitigation/patching
- If an artifact’s build provenance or kernel patch level is unknown, treat it as candidate-affected until verified otherwise.
- On a Linux host / VM:
- uname -r
- cat /proc/version
- rpm -q --changelog kernel | head -n 30 (for RPM systems)
- apt changelog linux-image-$(uname -r) (for Debian/Ubuntu)
- In WSL:
- wsl -d <distro> uname -r
- wsl --status (to see WSL version and default distro)
- In Azure:
- Azure Portal / CLI: list VM image SKU and published publisher name; verify whether the image is Azure Linux, Ubuntu-provided, or a partner image.
Specific considerations for WSL2, Azure VMs, and other Microsoft artifacts
WSL2 kernels
- Microsoft builds and ships a kernel image for WSL2, and those builds appear in Microsoft’s WSL kernel source repositories.
- The WSL2 kernel may track specific stable branches and include local patches or configuration changes. If the WSL2 kernel build is based on a vulnerable upstream commit range and has not had the CVE fix applied, that WSL2 instance would be affected.
- Practical check: open a WSL2 shell and run uname -r; then verify whether that kernel release contains the fix (check changelogs or the WSL kernel repo history).
Azure VM images and linux-azure kernels
- Azure images vary: some use distribution-supplied kernels, some use Azure-tuned kernels, and some use Microsoft-curated kernel packages.
- Azure Linux (the attested product) is authoritative for that distribution family; however, other images that ship a kernel compiled from the same upstream branch or that include the affected code could be vulnerable.
- Practical check: for a given VM, run uname -r and then consult the image publisher/vendor advisory or the Azure image details to determine the kernel lineage and whether a patched package has been applied.
Container workloads
- Containers do not contain the host kernel. A container image cannot be “patched” for a kernel vulnerability; mitigation is applied at the host kernel level.
- If a host kernel running containers is vulnerable, all containers on that host are at risk of host-level compromise or denial of service, even if container filesystem packages are patched.
- Practical step: prioritize patching host kernels (physical hosts, VMs, or nodes) in container clusters.
Remediation guidance — patching, mitigations, and interim controls
The single correct remediation for a kernel UAF is to apply a vendor-provided kernel patch that includes the upstream fix. Here’s how to approach remediation across typical Microsoft-supplied environments.Patching and updates
- Azure Linux (attested): follow Microsoft’s published security updates and apply patches via the distro’s package manager or image refresh mechanisms recommended by Microsoft.
- WSL2: install any Windows or WSL updates that include a new WSL kernel; if you manage WSL kernels centrally, ensure Windows Update is applying the latest WSL kernel packages. If you use a custom kernel for WSL, rebuild or obtain a patched kernel.
- Azure VMs and Marketplace images: apply kernel package updates using the distribution’s package manager (apt, yum, zypper, etc.) or redeploy from patched image SKUs if Microsoft or the image publisher has published updated images.
- AKS and node pools: update node pool images or apply the vendor-recommended kernel package updates; consider orchestrator-provided upgrade workflows to minimize disruption.
- On-prem or appliance images: follow vendor guidance or rebuild appliance images with patched kernels.
Interim mitigations (if immediate patching is not possible)
- Limit exposure: reduce or restrict IPv6 network exposure where feasible until kernels are patched. Because the flaw is in the IPv6 transmit path, restricting IPv6 connectivity to trusted networks can reduce risk surface for remote attack vectors.
- Network controls: apply network ingress filtering and host-based firewall rules to limit traffic sources and protocols that could be used to trigger the vulnerability.
- Privilege minimization: reduce privileges for local users and services that can generate raw network packets if operationally possible (many kernel exploits require local access or elevated rights).
- Monitoring and logging: increase syslog and audit monitoring for unusual kernel crashes or OOPS messages referencing ip6_xmit or skb operations. A surge in kernel oopses after an attempted exploit attempt is a strong signal.
Verification after patching
- Reboot into the patched kernel if required and validate kernel version and vendor changelog.
- Re-run the detection checks (uname -r, package changelog) to verify the fix is present.
- For WSL2: confirm WSL kernel version updated and validate by running uname inside the WSL distribution.
Operational checklist for defenders (step-by-step)
- Build an inventory of all Microsoft-supplied Linux artifacts in your estate:
- Azure Linux instances, WSL2 hosts, Azure VMs and Marketplace images, AKS nodes.
- For each artifact, capture the kernel version string (uname -r) and package metadata.
- Map each kernel or build to the upstream range and vendor advisory to determine whether it’s vulnerable.
- Prioritize patching assets that are:
- Internet-facing, exposed to untrusted IPv6 traffic.
- Running sensitive or critical workloads.
- Hosting containers or multi-tenant services.
- Apply vendor patches or redeploy updated images. For WSL2, ensure Windows Updates that contain the kernel updates are applied.
- If immediate patching isn’t feasible, implement the interim mitigations (IPv6 restrictions, firewalling, monitoring).
- Re-validate post-patch and document remediation in your vulnerability management system, linking to the applicable MSRC/CSAF/VEX attestation for Azure Linux and any additional vendor advisories discovered.
- Subscribe to MSRC product attestations and vendor security advisories for follow-up updates; Microsoft has committed to updating CVE mappings if it identifies further affected product families.
Practical Q&A: common questions answered
- Is Azure Linux the only Microsoft product that includes the library?
- Short, literal answer: Microsoft has publicly attested that Azure Linux includes the component and is potentially affected. That is an authoritative attestation for that product family.
- Practical answer: No — other Microsoft artifacts that ship a Linux kernel (WSL2 kernel builds, Azure VM images, etc.) are potential candidates and must be verified on a per-artifact basis because kernel content and patch levels vary.
- Should I assume WSL2 is safe?
- No. Do not assume WSL2 is safe without checking the WSL kernel version and whether the WSL build includes the upstream fix. If a WSL kernel’s version predates the patch or lacks the fix, the instance may be vulnerable.
- Can I fix containers by patching container images?
- No. Container images do not contain the host kernel. You must patch the host kernel (VM or physical host) to remediate kernel vulnerabilities.
- Where should I look for authoritative updates from Microsoft?
- MSRC security advisories and Microsoft’s CSAF/VEX attestations (for Azure Linux and subsequent product attestations) are the vendor’s authoritative channels. Microsoft committed to publishing machine-readable VEX/CSAF attestations starting October 2025 and to updating CVE entries as additional products are identified.
Critical analysis — strengths and limitations of Microsoft’s attestation approach
Strengths
- Product-scoped clarity: Microsoft’s use of CSAF/VEX to state “Azure Linux includes this open-source library” gives customers a machine-readable, authoritative signal for that product family — a strong improvement over opaque vendor statements.
- Operational practicality: By attesting per product family, Microsoft makes it possible for enterprises to automate patching and decision logic for Azure Linux customers quickly.
- Transparency commitment: Publishing VEX/CSAF attestations and a public blog about the program provides a predictable process and improves vendor accountability.
Limitations and risks
- Phased rollout risk: A phased VEX rollout inevitably leaves gaps: until Microsoft completes inventory and attestation across its broad portfolio, other Microsoft-supplied artifacts may remain unscanned and thus unreported. Administrators relying solely on MSRC attestations risk blind spots.
- Artifact heterogeneity: Microsoft distributes many kernel artifacts with different backport histories and config options. A single attestation (Azure Linux) can’t meaningfully assert absence across WSL kernels, Azure images, and partner-supplied marketplace images.
- Operational burden on customers: The product-by-product attestation model still places the onus on customers to inventory and verify other artifacts — a non-trivial task in large, complex estates.
- Potential for delayed updates: Some artifacts — especially custom marketplace images or long-lived appliances — may not be updated promptly by their maintainers, creating persistent risk even after Microsoft patches its own distributions.
Final recommendations
- Treat Microsoft’s MSRC attestation for Azure Linux as authoritative for Azure Linux, and act on it promptly if you run that distro.
- Do not assume other Microsoft products are unaffected. Inventory and verify any Microsoft-supplied artifacts that include a Linux kernel: WSL2 instances, Azure VM images, AKS nodes, and marketplace/appliance images.
- Apply vendor kernel patches as soon as possible. If you cannot immediately patch, implement interim mitigations (restrict IPv6 exposure, tighten network controls, increase monitoring).
- For WSL users: check the WSL kernel version inside your WSL2 distribution and ensure Windows and WSL updates that include kernel patches are applied.
- For cloud teams: automate kernel version detection across VM fleets and node pools, compare to published vulnerable ranges, and incorporate vendor attestations and SBOMs where available.
- Maintain a subscription to MSRC advisories and watch for updated CSAF/VEX attestations — Microsoft has committed to expanding these attestations as additional products are inventoried.
Microsoft’s language around CVE-2024-44985 is accurate but narrowly scoped: Azure Linux is confirmed in-scope because Microsoft attested it, but that confirmation doesn’t equal exclusivity. Any Microsoft artifact that ships a Linux kernel must be checked individually. The defensible path for operators is straightforward: inventory, verify kernel versions, patch quickly, and — until vendors complete broader attestations — assume other Microsoft-distributed kernels are potentially in scope and verify them accordingly.
Source: MSRC Security Update Guide - Microsoft Security Response Center