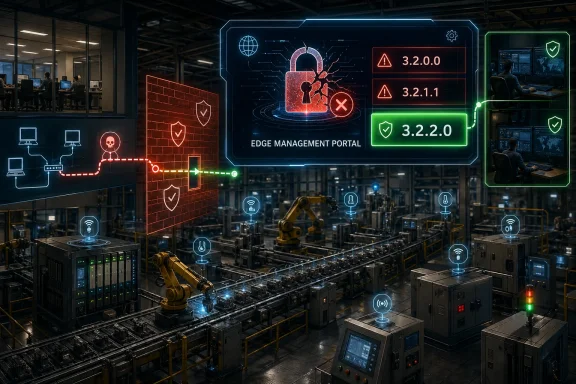
CISA on April 30, 2026 republished ABB’s advisory for CVE-2025-10571, a critical authentication-bypass flaw in ABB Ability Edgenius Management Portal versions 3.2.0.0 and 3.2.1.1 that can let a network-adjacent attacker run code and alter deployed applications. The uncomfortable part is not merely the 9.6 CVSS score. It is that the weak point sits in the management layer of an industrial edge platform, exactly where modern factories increasingly concentrate power, automation, and trust. ABB has a fix in Ability Edgenius 3.2.2.0, but the deeper lesson is that edge management planes have become industrial control systems’ new soft underbelly.
Industrial cybersecurity used to have a relatively legible center of gravity. Protect the PLCs, segment the control network, lock down engineering workstations, and treat remote access like a hazardous material. That model has not disappeared, but it has been complicated by the rise of edge platforms that sit between operational technology, enterprise IT, analytics systems, and cloud-adjacent workflows.
ABB Ability Edgenius belongs to that world. Its value proposition is exactly what makes it sensitive: it gives industrial operators a way to manage applications and compute closer to the machines, sensors, and production processes that generate the data. That is useful, and in many environments increasingly necessary, but it also means the management portal is not just a convenience UI. It is a command surface.
CVE-2025-10571 is therefore not a routine web bug in an obscure admin page. According to the advisory language, successful exploitation could allow an attacker to send a specially crafted message to a system node, then install and run arbitrary code, uninstall applications, and modify the configuration of installed applications. In industrial terms, that is not just “access.” That is leverage.
The advisory says exploitation requires access to the network where Edgenius has been deployed and requires the Management Portal to be running. That narrows the blast radius compared with an internet-exposed wormable flaw, but it should not soothe anyone responsible for a plant network. In OT security, “adjacent network” is often where real intrusions begin to matter.
That “changed scope” element is important. It signals that the vulnerable component can affect resources beyond its own immediate security authority. For a management portal tasked with deploying or configuring edge applications, that is intuitive: compromise the thing that manages other things, and the damage is no longer contained to the login screen that failed.
The weakness classification, CWE-288, is also telling. “Authentication Bypass Using an Alternate Path or Channel” is the kind of phrase that sounds academic until it shows up in a production system. It usually means the main door may be guarded, but another route into the same privileged function was not held to the same standard.
That is a recurring pattern in enterprise and industrial software alike. Products often accumulate APIs, service channels, agent communications, maintenance endpoints, upgrade paths, and emergency workflows. The user-facing portal may look tidy, while the machinery behind it contains older assumptions about trust. Attackers do not care which door the vendor intended them to use.
In industrial environments, the calculus is messier. Edge management systems may support production monitoring, local analytics, application lifecycle management, or integrations that operations teams have quietly come to rely on. Disabling a portal can be the right security move and still create real operational friction.
That friction is why critical OT vulnerabilities so often become exercises in governance rather than mere patching. The security team sees a 9.6. The operations team sees a production dependency. The plant manager sees downtime risk. The vendor sees the latest roll-up. The attacker, if present, sees a window.
The right answer is not to romanticize uptime as an excuse for delay. It is to recognize that “upgrade as soon as possible” has to become a concrete plan: identify affected instances, validate backups, test the update path, schedule the change, restrict access in the meantime, and confirm the portal is no longer reachable from any network that does not absolutely require it.
That condition is meaningful, but not rare. Many industrial incidents begin with an enterprise compromise, a misconfigured VPN, stolen remote-access credentials, a contractor laptop, or a poorly segmented network path. Once an attacker has that initial foothold, management systems inside the industrial environment become attractive precisely because they can turn limited access into control.
This is why CISA’s standard recommendations still matter, even when they read like familiar boilerplate. Minimize exposure. Keep control systems off the public internet. Put firewalls between plant networks and business networks. Treat VPNs as one component of access control, not as magic armor. In an era of credential theft and appliance exploitation, a VPN is only as trustworthy as the devices and identities behind it.
The Edgenius case also illustrates the limits of perimeter thinking. If the management portal is reachable from broad internal ranges, then “not internet exposed” may be a small comfort. The real question is whether the portal is reachable only from tightly controlled administration workstations, through monitored pathways, by authenticated personnel, with logging that someone actually reviews.
Industrial edge systems intensify that pattern because they inherit risk from both sides. From IT, they inherit web portals, APIs, application deployment models, certificates, identity integrations, and update channels. From OT, they inherit long maintenance cycles, uptime constraints, network segmentation challenges, and a safety culture that cannot treat every patch as routine.
That hybrid nature is the point of the product category, but it is also where risk accumulates. A traditional HMI compromise is bad because it can mislead operators or expose process controls. A compromised edge management portal may be worse in a different way: it can become a staging area for persistence, configuration tampering, or malicious application deployment across systems intended to bridge operational data and enterprise workflows.
The advisory’s language about installing and uninstalling applications deserves attention. In many modern environments, application lifecycle control is infrastructure control. If an attacker can install code through an accepted management mechanism, they may not need a noisy exploit chain afterward. They can ride the platform.
Edgenius Management Portal sits squarely in that category. An organization may know it has ABB equipment, may know it runs industrial edge workloads, and may still not have an immediately accessible list of which portal versions are deployed where. Version strings such as 3.2.0.0 and 3.2.1.1 sound precise, but precision in an advisory is only useful if defenders can map it to reality.
That is where many vulnerability management programs still fail in OT. A scanner might not be allowed on the control network. A CMDB may not cover plant-floor appliances. The vendor portal may not be integrated into enterprise patch tracking. A system integrator may have installed the product, while the internal team now owns the risk without owning the documentation.
The fix for this class of problem is not just another scanner. It is a living register of management planes: what they control, who administers them, which network zones can reach them, how they authenticate users and services, how they are updated, and what happens if they are disabled. Without that, every critical advisory becomes a rediscovery project.
The exploitability conditions are not exotic. Low attack complexity, no privileges, no user interaction, and a high-impact management function are enough to make defenders take notice. Even if exploit details are not public, advisories themselves provide a roadmap for prioritization. Attackers do not need every industrial organization to be vulnerable; they need one reachable target where the portal is still running and unpatched.
There is also a lag problem. Public exploitation often becomes visible only after defenders know what to look for, after victims share telemetry, or after incident response firms connect scattered evidence. OT networks can be especially opaque, with less endpoint telemetry, fewer modern detections, and more reluctance to disturb fragile systems. “No known exploitation” can mean exactly that, or it can mean the industry has not yet seen enough.
The rational response is urgency without panic. If the portal is internet exposed, that is a severe architecture failure even beyond this CVE and should be corrected immediately. If it is reachable from broad enterprise ranges, narrow that access now. If it is only reachable from a controlled management subnet, verify the controls rather than assuming the diagram is still true.
For Edgenius operators, the immediate compensating control is to disable the Management Portal until the fixed roll-up is installed, if operations can tolerate it. Where the portal must remain available temporarily, access should be reduced to the smallest possible set of administration hosts and users. Firewall rules should be explicit, logged, and reviewed for exceptions that accumulated during commissioning or troubleshooting.
Monitoring should focus on behavior consistent with the advisory’s impact. Unexpected application installation, application removal, configuration changes, new services, unusual node communication, and administrative actions outside maintenance windows deserve scrutiny. If the platform maintains audit logs, those logs should be exported or protected so a compromised portal cannot quietly rewrite the story.
Backups matter, too, but not in the abstract. Operators should know how to restore Edgenius configuration and workloads to a known-good state, and they should verify that backup copies are not writable from the same environment that an attacker could reach through the portal. In ransomware-era IT, that principle is familiar. In OT edge systems, it is becoming just as important.
The industrial edge is absorbing the complexity that enterprise IT has wrestled with for years. It has web management, software-defined deployment, distributed agents, remote updates, service APIs, identity handoffs, and a growing expectation that data should move quickly from machines to dashboards to analytics platforms. Every one of those capabilities creates a control point. Every control point needs authentication that is consistent across all paths, not just the front door.
Enterprise IT learned, painfully, that management software is a favorite target because it is trusted by design. Endpoint management tools can become malware distribution systems. Remote monitoring tools can become persistence mechanisms. Backup consoles can become extortion accelerants. The industrial sector is now living through its own version of that realization, with the added complication that the things being managed may sit near physical processes.
That does not mean industrial edge platforms are a mistake. The opposite is true: they are likely to become more important as manufacturers chase efficiency, predictive maintenance, local analytics, and AI-assisted operations. But the security model has to mature with the architecture. A management portal that can change production-adjacent software must be treated less like a dashboard and more like a domain controller for the plant floor.
Alternate paths and channels are particularly dangerous in complex products because they often arise from legitimate engineering needs. A node needs to talk to a controller. An installer needs a bootstrap flow. A service account needs to perform maintenance. A recovery mechanism needs to function when the normal UI is unavailable. Each exception may be reasonable on its own, while the aggregate becomes an authentication bypass waiting for a researcher or attacker to notice.
Secure design for these systems should make privileged operations hard to reach even after one layer fails. Sensitive actions should require strong authorization checks at the function level, not merely at the gateway. Service-to-service channels should be authenticated and scoped. Administrative actions should be auditable. Dangerous operations, such as application deployment or configuration modification, should be constrained by role, origin, and policy.
Customers should demand that level of architecture from industrial vendors, but they should also prepare to operate imperfect products safely. No vendor advisory can retrofit segmentation into a flat plant network. No roll-up can compensate for shared admin accounts. No CVSS score can tell a plant exactly which production dependency will break if a portal is shut off. That work remains local, operational, and unavoidable.
CVE-2025-10571 will not be the last critical bug in an industrial edge management plane, and it will not be the last reminder that “inside the network” is no longer a defensible security boundary. The factories that handle this well will be the ones that treat edge consoles as high-value infrastructure, patch them with the seriousness of production systems, and design their networks so that a failed login check does not become a failed plant.
Source: CISA ABB Edgenius Management Portal | CISA
 The Edge Console Has Become the New Plant-Floor Crown Jewel
The Edge Console Has Become the New Plant-Floor Crown Jewel
Industrial cybersecurity used to have a relatively legible center of gravity. Protect the PLCs, segment the control network, lock down engineering workstations, and treat remote access like a hazardous material. That model has not disappeared, but it has been complicated by the rise of edge platforms that sit between operational technology, enterprise IT, analytics systems, and cloud-adjacent workflows.ABB Ability Edgenius belongs to that world. Its value proposition is exactly what makes it sensitive: it gives industrial operators a way to manage applications and compute closer to the machines, sensors, and production processes that generate the data. That is useful, and in many environments increasingly necessary, but it also means the management portal is not just a convenience UI. It is a command surface.
CVE-2025-10571 is therefore not a routine web bug in an obscure admin page. According to the advisory language, successful exploitation could allow an attacker to send a specially crafted message to a system node, then install and run arbitrary code, uninstall applications, and modify the configuration of installed applications. In industrial terms, that is not just “access.” That is leverage.
The advisory says exploitation requires access to the network where Edgenius has been deployed and requires the Management Portal to be running. That narrows the blast radius compared with an internet-exposed wormable flaw, but it should not soothe anyone responsible for a plant network. In OT security, “adjacent network” is often where real intrusions begin to matter.
A Critical Score With a Very Specific Shape
The CVSS 3.1 vector tells a compact story: adjacent attack vector, low complexity, no privileges required, no user interaction, changed scope, and high impact to confidentiality, integrity, and availability. In plain English, an attacker does not need a password or a tricked user, but does need a path onto the relevant network segment. Once there, the consequences can cross a trust boundary.That “changed scope” element is important. It signals that the vulnerable component can affect resources beyond its own immediate security authority. For a management portal tasked with deploying or configuring edge applications, that is intuitive: compromise the thing that manages other things, and the damage is no longer contained to the login screen that failed.
The weakness classification, CWE-288, is also telling. “Authentication Bypass Using an Alternate Path or Channel” is the kind of phrase that sounds academic until it shows up in a production system. It usually means the main door may be guarded, but another route into the same privileged function was not held to the same standard.
That is a recurring pattern in enterprise and industrial software alike. Products often accumulate APIs, service channels, agent communications, maintenance endpoints, upgrade paths, and emergency workflows. The user-facing portal may look tidy, while the machinery behind it contains older assumptions about trust. Attackers do not care which door the vendor intended them to use.
ABB’s Fix Is Straightforward, but the Operational Decision Is Not
ABB’s remediation is clear: upgrade to ABB Ability Edgenius 3.2.2.0, where the vulnerability is fixed. Until that upgrade is applied, ABB advises disabling the Edgenius Management Portal to mitigate exposure. For a conventional business application, that might sound like a weekend change window and a short outage notice.In industrial environments, the calculus is messier. Edge management systems may support production monitoring, local analytics, application lifecycle management, or integrations that operations teams have quietly come to rely on. Disabling a portal can be the right security move and still create real operational friction.
That friction is why critical OT vulnerabilities so often become exercises in governance rather than mere patching. The security team sees a 9.6. The operations team sees a production dependency. The plant manager sees downtime risk. The vendor sees the latest roll-up. The attacker, if present, sees a window.
The right answer is not to romanticize uptime as an excuse for delay. It is to recognize that “upgrade as soon as possible” has to become a concrete plan: identify affected instances, validate backups, test the update path, schedule the change, restrict access in the meantime, and confirm the portal is no longer reachable from any network that does not absolutely require it.
“Not Remotely Exploitable” Is Not the Same as “Low Risk”
CISA’s note that the vulnerability is not exploitable remotely is useful, but it is easy to misread. In ICS advisories, remote exploitability often means exploitable across the internet or from a remote network without prior positioning. This advisory instead describes an adjacent-network condition: the attacker must have gained access to the network where Edgenius is deployed.That condition is meaningful, but not rare. Many industrial incidents begin with an enterprise compromise, a misconfigured VPN, stolen remote-access credentials, a contractor laptop, or a poorly segmented network path. Once an attacker has that initial foothold, management systems inside the industrial environment become attractive precisely because they can turn limited access into control.
This is why CISA’s standard recommendations still matter, even when they read like familiar boilerplate. Minimize exposure. Keep control systems off the public internet. Put firewalls between plant networks and business networks. Treat VPNs as one component of access control, not as magic armor. In an era of credential theft and appliance exploitation, a VPN is only as trustworthy as the devices and identities behind it.
The Edgenius case also illustrates the limits of perimeter thinking. If the management portal is reachable from broad internal ranges, then “not internet exposed” may be a small comfort. The real question is whether the portal is reachable only from tightly controlled administration workstations, through monitored pathways, by authenticated personnel, with logging that someone actually reviews.
The Management Plane Is Where IT and OT Now Collide
For WindowsForum readers, the Edgenius advisory should feel familiar even if the product itself is niche. The same architectural problem appears in hypervisors, endpoint management suites, backup consoles, firewall managers, Kubernetes dashboards, and cloud control planes. Once a management interface can deploy code, change configuration, or orchestrate other systems, it becomes a privileged platform.Industrial edge systems intensify that pattern because they inherit risk from both sides. From IT, they inherit web portals, APIs, application deployment models, certificates, identity integrations, and update channels. From OT, they inherit long maintenance cycles, uptime constraints, network segmentation challenges, and a safety culture that cannot treat every patch as routine.
That hybrid nature is the point of the product category, but it is also where risk accumulates. A traditional HMI compromise is bad because it can mislead operators or expose process controls. A compromised edge management portal may be worse in a different way: it can become a staging area for persistence, configuration tampering, or malicious application deployment across systems intended to bridge operational data and enterprise workflows.
The advisory’s language about installing and uninstalling applications deserves attention. In many modern environments, application lifecycle control is infrastructure control. If an attacker can install code through an accepted management mechanism, they may not need a noisy exploit chain afterward. They can ride the platform.
Patch Management Has to Include the Things That Patch Other Things
The security industry has spent years telling organizations to inventory assets. The hard part is that the most important assets are not always the obvious production endpoints. Management portals, update services, jump hosts, remote access brokers, backup systems, and orchestration tools can be less visible than the machines they control, yet far more powerful.Edgenius Management Portal sits squarely in that category. An organization may know it has ABB equipment, may know it runs industrial edge workloads, and may still not have an immediately accessible list of which portal versions are deployed where. Version strings such as 3.2.0.0 and 3.2.1.1 sound precise, but precision in an advisory is only useful if defenders can map it to reality.
That is where many vulnerability management programs still fail in OT. A scanner might not be allowed on the control network. A CMDB may not cover plant-floor appliances. The vendor portal may not be integrated into enterprise patch tracking. A system integrator may have installed the product, while the internal team now owns the risk without owning the documentation.
The fix for this class of problem is not just another scanner. It is a living register of management planes: what they control, who administers them, which network zones can reach them, how they authenticate users and services, how they are updated, and what happens if they are disabled. Without that, every critical advisory becomes a rediscovery project.
The Absence of Known Exploitation Buys Time, Not Permission
CISA says it has no known public exploitation specifically targeting this vulnerability at the time of the advisory. That is good news. It is not a reason to defer action.The exploitability conditions are not exotic. Low attack complexity, no privileges, no user interaction, and a high-impact management function are enough to make defenders take notice. Even if exploit details are not public, advisories themselves provide a roadmap for prioritization. Attackers do not need every industrial organization to be vulnerable; they need one reachable target where the portal is still running and unpatched.
There is also a lag problem. Public exploitation often becomes visible only after defenders know what to look for, after victims share telemetry, or after incident response firms connect scattered evidence. OT networks can be especially opaque, with less endpoint telemetry, fewer modern detections, and more reluctance to disturb fragile systems. “No known exploitation” can mean exactly that, or it can mean the industry has not yet seen enough.
The rational response is urgency without panic. If the portal is internet exposed, that is a severe architecture failure even beyond this CVE and should be corrected immediately. If it is reachable from broad enterprise ranges, narrow that access now. If it is only reachable from a controlled management subnet, verify the controls rather than assuming the diagram is still true.
Defense-in-Depth Is Boring Until the Login Screen Fails
Authentication bypass vulnerabilities are a test of whether the rest of the security model exists. If a login screen is the only meaningful barrier between an attacker and administrative capability, the system has already been designed too thinly. When authentication breaks, segmentation, allowlisting, monitoring, least privilege, and change control are supposed to catch the fall.For Edgenius operators, the immediate compensating control is to disable the Management Portal until the fixed roll-up is installed, if operations can tolerate it. Where the portal must remain available temporarily, access should be reduced to the smallest possible set of administration hosts and users. Firewall rules should be explicit, logged, and reviewed for exceptions that accumulated during commissioning or troubleshooting.
Monitoring should focus on behavior consistent with the advisory’s impact. Unexpected application installation, application removal, configuration changes, new services, unusual node communication, and administrative actions outside maintenance windows deserve scrutiny. If the platform maintains audit logs, those logs should be exported or protected so a compromised portal cannot quietly rewrite the story.
Backups matter, too, but not in the abstract. Operators should know how to restore Edgenius configuration and workloads to a known-good state, and they should verify that backup copies are not writable from the same environment that an attacker could reach through the portal. In ransomware-era IT, that principle is familiar. In OT edge systems, it is becoming just as important.
The Industrial Edge Is Still Learning Enterprise Security’s Old Lessons
There is a temptation to treat this advisory as a product-specific blip: ABB found or received a report, ABB issued a fix, CISA republished the notice, customers patch. That would be the tidy version. It would also miss the structural issue.The industrial edge is absorbing the complexity that enterprise IT has wrestled with for years. It has web management, software-defined deployment, distributed agents, remote updates, service APIs, identity handoffs, and a growing expectation that data should move quickly from machines to dashboards to analytics platforms. Every one of those capabilities creates a control point. Every control point needs authentication that is consistent across all paths, not just the front door.
Enterprise IT learned, painfully, that management software is a favorite target because it is trusted by design. Endpoint management tools can become malware distribution systems. Remote monitoring tools can become persistence mechanisms. Backup consoles can become extortion accelerants. The industrial sector is now living through its own version of that realization, with the added complication that the things being managed may sit near physical processes.
That does not mean industrial edge platforms are a mistake. The opposite is true: they are likely to become more important as manufacturers chase efficiency, predictive maintenance, local analytics, and AI-assisted operations. But the security model has to mature with the architecture. A management portal that can change production-adjacent software must be treated less like a dashboard and more like a domain controller for the plant floor.
Vendors Need to Design for the Day the Portal Is Under Attack
ABB’s advisory is commendably direct about impact and remediation. Still, the broader vendor challenge is to assume that management portals will be probed, abused, and occasionally broken. That assumption should shape product design long before a CVE lands.Alternate paths and channels are particularly dangerous in complex products because they often arise from legitimate engineering needs. A node needs to talk to a controller. An installer needs a bootstrap flow. A service account needs to perform maintenance. A recovery mechanism needs to function when the normal UI is unavailable. Each exception may be reasonable on its own, while the aggregate becomes an authentication bypass waiting for a researcher or attacker to notice.
Secure design for these systems should make privileged operations hard to reach even after one layer fails. Sensitive actions should require strong authorization checks at the function level, not merely at the gateway. Service-to-service channels should be authenticated and scoped. Administrative actions should be auditable. Dangerous operations, such as application deployment or configuration modification, should be constrained by role, origin, and policy.
Customers should demand that level of architecture from industrial vendors, but they should also prepare to operate imperfect products safely. No vendor advisory can retrofit segmentation into a flat plant network. No roll-up can compensate for shared admin accounts. No CVSS score can tell a plant exactly which production dependency will break if a portal is shut off. That work remains local, operational, and unavoidable.
The Edgenius Checklist That Belongs in This Week’s Change Meeting
The practical response to CVE-2025-10571 is not complicated, but it does need ownership. Security teams should not simply forward the advisory to operations, and operations teams should not wait for a quarterly maintenance cycle to discover whether the affected versions are present.- Organizations running ABB Ability Edgenius should verify immediately whether Management Portal versions 3.2.0.0 or 3.2.1.1 are deployed.
- Affected environments should plan an upgrade to ABB Ability Edgenius 3.2.2.0, the fixed version identified by ABB.
- If the update cannot be applied promptly, administrators should disable the Edgenius Management Portal where operationally feasible.
- Network access to the portal should be restricted to dedicated administration paths rather than broad plant or enterprise subnets.
- Teams should review logs and configuration history for unexpected application installation, removal, or modification.
- Asset inventories should treat edge management portals as privileged infrastructure, not ordinary application servers.
CVE-2025-10571 will not be the last critical bug in an industrial edge management plane, and it will not be the last reminder that “inside the network” is no longer a defensible security boundary. The factories that handle this well will be the ones that treat edge consoles as high-value infrastructure, patch them with the seriousness of production systems, and design their networks so that a failed login check does not become a failed plant.
Source: CISA ABB Edgenius Management Portal | CISA