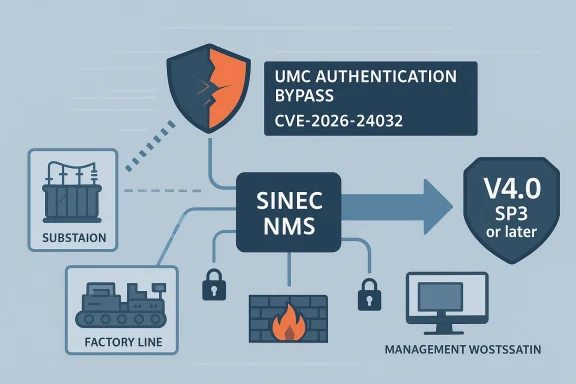
Siemens has patched a high-severity authentication bypass in SINEC NMS that affects installations using the User Management Component (UMC), and the security significance is hard to overstate: a remote attacker may be able to skip authentication entirely and reach the application without valid credentials. The flaw, tracked as CVE-2026-24032, is rated CVSS 3.1 7.3, and Siemens’ fix path is straightforward: update to V4.0 SP3 or later. In industrial environments, that kind of issue is more than a software bug; it is an access-control failure in a product used to centrally monitor and manage network infrastructure.
SINEC NMS sits in Siemens’ industrial networking portfolio as a network management system for OT environments, where it helps operators centrally monitor, manage, and configure networks. Siemens positions the product as part of a broader SINEC family built around network management, security monitoring, and zero-trust-oriented connectivity, which makes its trust model especially important. If the management plane is weakened, the impact can spread beyond a single UI session and into the operational visibility layer that administrators depend on.
This latest advisory lands in a pattern that has become familiar across industrial software: the product is useful precisely because it is privileged, and that privilege makes bugs unusually consequential. Siemens has repeatedly advised customers to move to the latest SINEC NMS release in prior advisories, including multiple vulnerability disclosures in 2024 and 2025, which shows the product has been under sustained security scrutiny. The new authentication bypass now extends that story from code-hardening issues into identity assurance, which is usually the first line of defense in any remote-access workflow.
The vulnerability was published by CISA as ICSA-26-111-03 on April 21, 2026, with the underlying Siemens advisory identified as SSA-801704. CISA notes that the issue was reported by Siemens ProductCERT, and the advisory classifies the flaw as an unauthenticated remote attack vector with confidentiality, integrity, and availability impact rated as low but meaningful in the aggregate. That combination matters because exploitation does not require local access or user interaction, making exposure largely a question of reachability and deployment hygiene.
What makes this especially relevant to industrial operators is the role UMC plays in managing identities and access for the environment. Siemens’ own documentation for SINEC NMS highlights two-factor authentication for UMC users, which underscores how central authentication controls are to the product’s operating model. When a bypass exists in that same component, it is not just another CVE on a checklist; it becomes a direct challenge to the boundary between legitimate administration and unauthorized access.
The affected scope is concise but important: all versions earlier than V4.0 SP3 with UMC. That wording suggests the bug is tied not to every deployment of SINEC NMS in every possible mode, but specifically to installations using the UMC management environment. In practice, that is enough to concern any organization that enabled centralized user handling or exposed the management stack to wider networks than intended.
The CVSS score of 7.3 reflects that this is not a speculative weakness. The vector is network-based, requires no privileges, no user interaction, and can affect confidentiality, integrity, and availability. That mix is a classic sign of an attack path that security teams should treat as a priority even if they have not observed active exploitation in their own estate. (cvepremium.circl.lu)
For enterprise IT readers, this is comparable to a directory or SSO control failure in a high-privilege console. For OT operators, it is even more fraught because the management plane may be separated from the business network only by policy, not by immutable technical isolation. Once an attacker can impersonate a trusted user or bypass that identity check altogether, the rest of the platform may simply assume the request is legitimate.
This is also where industrial software differs from consumer apps. A consumer service account may expose one person’s inbox or photos, but an industrial management tool can reveal topology, device names, configuration state, and operator workflows. In the wrong hands, that information can support not just immediate compromise but also reconnaissance for a broader intrusion campaign.
That said, patching in OT is rarely as easy as it sounds. Many organizations maintain change windows, validation steps, and staged rollout procedures because network-management software can be tightly coupled to production visibility or maintenance workflows. A patch may be technically urgent but operationally delayed, which is exactly why layered containment remains so important.
Organizations should also verify whether their deployment actually uses UMC in the affected way. The advisory scope indicates the issue is tied to SINEC NMS with UMC, so confirming the exact installed components and versions is a worthwhile first step before making changes. In other words, inventory is part of remediation, not just a housekeeping task.
In many industrial environments, the management layer is reachable from engineering workstations, jump hosts, or secure remote-access paths. Those routes are not necessarily unsafe, but they do create a broader trust corridor than a fully air-gapped model. If authentication can be bypassed, any reachable management endpoint becomes a much more attractive target for opportunistic scanning or targeted abuse.
Security teams should also review whether older assumptions about internal-only risk still apply. Industrial networks are increasingly connected to remote support tools, analytics platforms, and centralized operations centers, which means “internal” often means reachable from multiple trust domains. That widening of exposure is one reason authentication bugs are now among the most watched classes of vulnerabilities in OT products.
For competitors, the lesson is uncomfortable but clear: customers buying industrial management software now expect not only feature depth but also a visible, disciplined patch cadence. A vendor that can show rapid disclosure, a clear remediation version, and repeat advisories is signaling maturity, but it is also signaling the complexity of maintaining secure OT software over time. The market increasingly rewards security operations around the product, not just the product features.
It also nudges the industry toward zero-trust thinking in places where legacy trust models still linger. If the management plane can be bypassed, then segmentation, MFA, allowlists, and logging stop being nice-to-haves and become essential compensating controls. That is a strategic shift, not just a patch-cycle issue.
The pattern is important because each advisory reveals a different class of trust failure. Earlier disclosures touched on memory safety, authorization checks, and input validation in dependencies, while the April 2026 issue concerns identity validation inside the management component. In aggregate, the message is that industrial administration software must be designed as though hostile inputs are normal, because attackers are very willing to treat it that way.
Security teams should therefore review not just the latest CVE but also their overall SINEC NMS deployment posture. If the platform is central to network operations, then management network segmentation, MFA, and logging should be treated as operational requirements rather than optional hardening. The objective is to make one flaw less likely to become a full incident.
Consumer users are not the audience here, but the comparison is useful. In a consumer app, an auth bypass might expose a private profile. In OT, the same class of bug can expose the layout of a plant network or grant control over the system used to configure it. That is why industrial software advisories often sound similar to IT advisories but carry a very different operational weight.
This also changes how organizations should think about insurance, audit, and compliance. A platform that centralizes network control should be covered by stronger monitoring and recovery controls than a typical internal web app. If the application is reachable, it is part of the operational attack surface, whether or not it sits in an IT server room.
There is also a constructive lesson here for industrial operators: the vulnerability can serve as a forcing function to improve identity governance, logging, and segmentation. If an organization uses the patch window to re-audit UMC access paths, it may emerge with a stronger baseline than it had before the advisory. In security terms, urgent work can become useful hardening.
A second concern is operational inertia. Industrial teams often know about vulnerabilities quickly but cannot patch immediately because changes must be tested and scheduled. The delay is understandable, but it creates a window in which compensating controls must do the heavy lifting. Without them, the organization is effectively betting on obscurity.
This is also another data point in the growing convergence of OT and enterprise security expectations. Buyers increasingly want products that not only manage industrial assets but also embody secure design, strong authentication, and rapid patch support. Vendors that can answer those expectations transparently will have an advantage; those that cannot will face tougher procurement scrutiny and more conservative deployments.
Source: CISA Siemens SINEC NMS | CISA
 Overview
Overview
SINEC NMS sits in Siemens’ industrial networking portfolio as a network management system for OT environments, where it helps operators centrally monitor, manage, and configure networks. Siemens positions the product as part of a broader SINEC family built around network management, security monitoring, and zero-trust-oriented connectivity, which makes its trust model especially important. If the management plane is weakened, the impact can spread beyond a single UI session and into the operational visibility layer that administrators depend on.This latest advisory lands in a pattern that has become familiar across industrial software: the product is useful precisely because it is privileged, and that privilege makes bugs unusually consequential. Siemens has repeatedly advised customers to move to the latest SINEC NMS release in prior advisories, including multiple vulnerability disclosures in 2024 and 2025, which shows the product has been under sustained security scrutiny. The new authentication bypass now extends that story from code-hardening issues into identity assurance, which is usually the first line of defense in any remote-access workflow.
The vulnerability was published by CISA as ICSA-26-111-03 on April 21, 2026, with the underlying Siemens advisory identified as SSA-801704. CISA notes that the issue was reported by Siemens ProductCERT, and the advisory classifies the flaw as an unauthenticated remote attack vector with confidentiality, integrity, and availability impact rated as low but meaningful in the aggregate. That combination matters because exploitation does not require local access or user interaction, making exposure largely a question of reachability and deployment hygiene.
What makes this especially relevant to industrial operators is the role UMC plays in managing identities and access for the environment. Siemens’ own documentation for SINEC NMS highlights two-factor authentication for UMC users, which underscores how central authentication controls are to the product’s operating model. When a bypass exists in that same component, it is not just another CVE on a checklist; it becomes a direct challenge to the boundary between legitimate administration and unauthorized access.
What Siemens Says Was Vulnerable
Siemens’ advisory, as republished by CISA, states that the affected application contains an authentication weakness because of insufficient validation of user identity in the UMC component. The result is an authentication bypass, meaning an attacker who reaches the interface may be able to gain unauthorized access without knowing valid credentials. The vendor fix is to move to SINEC NMS V4.0 SP3 or later, which Siemens says resolves the issue.The affected scope is concise but important: all versions earlier than V4.0 SP3 with UMC. That wording suggests the bug is tied not to every deployment of SINEC NMS in every possible mode, but specifically to installations using the UMC management environment. In practice, that is enough to concern any organization that enabled centralized user handling or exposed the management stack to wider networks than intended.
Why “insufficient validation” is serious
Authentication bypass flaws often sound abstract, but in reality they are among the most operationally dangerous vulnerabilities because they strike at the front door. If the software fails to reliably prove who is on the other end of a request, all downstream controls become less meaningful. In an industrial management platform, that can mean unauthorized visibility into assets, configuration changes, or a launch point for deeper lateral movement.The CVSS score of 7.3 reflects that this is not a speculative weakness. The vector is network-based, requires no privileges, no user interaction, and can affect confidentiality, integrity, and availability. That mix is a classic sign of an attack path that security teams should treat as a priority even if they have not observed active exploitation in their own estate. (cvepremium.circl.lu)
- Network reachable: attackers do not need local access.
- No credentials required: the bypass removes the normal trust gate.
- No user interaction: exploitation does not depend on a click.
- Management-plane exposure: the affected component is central to administration.
- Potentially broad impact: unauthorized access can cascade into misconfiguration or surveillance.
Why UMC Matters in the Real World
UMC, or User Management Component, is not a peripheral helper service. In Siemens’ SINEC ecosystem, it is part of the identity and access management layer used to organize who can log in and what they can do. That means a flaw here can have disproportionate consequences because the component is upstream of nearly every administrative action.For enterprise IT readers, this is comparable to a directory or SSO control failure in a high-privilege console. For OT operators, it is even more fraught because the management plane may be separated from the business network only by policy, not by immutable technical isolation. Once an attacker can impersonate a trusted user or bypass that identity check altogether, the rest of the platform may simply assume the request is legitimate.
Identity bugs tend to be chainable
Authentication bypasses are often most dangerous when combined with other flaws. A single weakness may not deliver full takeover on its own, but it can be chained with information disclosure, weak authorization checks, or insecure defaults to expand the attack surface. That is why the presence of prior SINEC NMS advisories matters: it shows the product is already a target-rich environment for attackers who know how to combine smaller mistakes.This is also where industrial software differs from consumer apps. A consumer service account may expose one person’s inbox or photos, but an industrial management tool can reveal topology, device names, configuration state, and operator workflows. In the wrong hands, that information can support not just immediate compromise but also reconnaissance for a broader intrusion campaign.
- Identity is upstream of everything.
- Bypass once, trust collapses everywhere.
- Recon data can be as valuable as control data.
- OT environments often have fewer compensating controls than IT.
- Legacy assumptions about internal trust no longer hold.
Siemens’ Remediation Path
Siemens’ recommended remediation is simple: upgrade to V4.0 SP3 or later. In industrial security, simplicity is a virtue because it reduces the chance that an organization will attempt a fragile workaround instead of applying the vendor patch. CISA’s republication also repeats Siemens’ general guidance to protect network access to devices with appropriate mechanisms and to follow Siemens’ industrial security operational guidelines.That said, patching in OT is rarely as easy as it sounds. Many organizations maintain change windows, validation steps, and staged rollout procedures because network-management software can be tightly coupled to production visibility or maintenance workflows. A patch may be technically urgent but operationally delayed, which is exactly why layered containment remains so important.
Practical rollout considerations
The most sensible approach is to treat the update as a managed maintenance event rather than a routine desktop patch. Operators should confirm version compatibility, validate backups, and ensure administrators know how to recover if login workflows or device visibility changes after the upgrade. That is especially true when the vulnerable component governs user management, because a failed migration can become an access outage.Organizations should also verify whether their deployment actually uses UMC in the affected way. The advisory scope indicates the issue is tied to SINEC NMS with UMC, so confirming the exact installed components and versions is a worthwhile first step before making changes. In other words, inventory is part of remediation, not just a housekeeping task.
- Identify all SINEC NMS instances and record exact versions.
- Confirm whether UMC is enabled and exposed to reachable networks.
- Test the V4.0 SP3 or later upgrade in a controlled environment.
- Validate admin authentication, role assignments, and access logs after patching.
- Restrict management-plane access until the update is complete.
Exposure and Attack Surface
The question most readers will ask is simple: how reachable is this bug? The answer depends on where SINEC NMS is deployed and how the management interface is segmented. CISA’s best-practice guidance remains familiar but relevant: minimize network exposure, keep control systems off the internet, and isolate them behind firewalls from business networks where possible.In many industrial environments, the management layer is reachable from engineering workstations, jump hosts, or secure remote-access paths. Those routes are not necessarily unsafe, but they do create a broader trust corridor than a fully air-gapped model. If authentication can be bypassed, any reachable management endpoint becomes a much more attractive target for opportunistic scanning or targeted abuse.
Where defenders should look first
Exposure analysis should focus on the interfaces that handle authentication and session setup. Even if the vulnerability is not directly internet-facing, it may still be reachable from partner networks, VPN concentrators, or shared admin subnets. Attackers often do not need a public IP if they can find a path through a trusted foothold.Security teams should also review whether older assumptions about internal-only risk still apply. Industrial networks are increasingly connected to remote support tools, analytics platforms, and centralized operations centers, which means “internal” often means reachable from multiple trust domains. That widening of exposure is one reason authentication bugs are now among the most watched classes of vulnerabilities in OT products.
- Internet exposure should be treated as unacceptable.
- VPN reachability still counts as exposure.
- Partner and contractor access expands the attack surface.
- Jump hosts can become attack launchpads.
- Management endpoints deserve the same scrutiny as production systems.
Competitive and Industry Implications
This advisory also says something broader about the industrial security market. Siemens has been building out a SINEC ecosystem that includes Security Guard, Security Inspector, Security Monitor, and related tools designed to improve visibility and response across OT networks. When one of the core management products develops an authentication bypass, it reinforces why vendors increasingly bundle monitoring and remediation products alongside the management plane itself.For competitors, the lesson is uncomfortable but clear: customers buying industrial management software now expect not only feature depth but also a visible, disciplined patch cadence. A vendor that can show rapid disclosure, a clear remediation version, and repeat advisories is signaling maturity, but it is also signaling the complexity of maintaining secure OT software over time. The market increasingly rewards security operations around the product, not just the product features.
Why this matters beyond Siemens
Industrial customers are becoming more sensitive to whether management tools can be used as stepping stones into production environments. That sensitivity is amplified by the rise of regulatory pressure, including resilience expectations and supply-chain transparency. A high-profile authentication bypass pushes buyers to ask harder questions about update support, identity architecture, and how often the vendor’s trust model is re-evaluated.It also nudges the industry toward zero-trust thinking in places where legacy trust models still linger. If the management plane can be bypassed, then segmentation, MFA, allowlists, and logging stop being nice-to-haves and become essential compensating controls. That is a strategic shift, not just a patch-cycle issue.
- Vendors are judged on patch velocity.
- OT security now includes identity architecture.
- Management tools are prime attack targets.
- Visibility products are becoming security products.
- Zero-trust concepts are moving into industrial operations.
How This Compares With Recent SINEC NMS Advisories
This is not the first time SINEC NMS has appeared in the vulnerability spotlight. Siemens published multiple advisories in 2024 and 2025 covering a range of issues, including code execution, privilege escalation, authorization weakness, and third-party component problems. That history does not mean the product is uniquely flawed, but it does suggest that SINEC NMS has become a frequent focal point for security research.The pattern is important because each advisory reveals a different class of trust failure. Earlier disclosures touched on memory safety, authorization checks, and input validation in dependencies, while the April 2026 issue concerns identity validation inside the management component. In aggregate, the message is that industrial administration software must be designed as though hostile inputs are normal, because attackers are very willing to treat it that way.
The cumulative risk problem
A single vulnerability may be survivable if it is patched quickly and never exposed. A product with repeated advisories, however, forces defenders to think in terms of cumulative trust erosion. That does not imply the product is unusable; it means the control environment around it must be disciplined, monitored, and updated more aggressively than many organizations are used to.Security teams should therefore review not just the latest CVE but also their overall SINEC NMS deployment posture. If the platform is central to network operations, then management network segmentation, MFA, and logging should be treated as operational requirements rather than optional hardening. The objective is to make one flaw less likely to become a full incident.
- Repeated advisories demand stronger governance.
- Different bug classes point to different control gaps.
- Patch urgency increases with product centrality.
- Monitoring is a mitigation, not a substitute for remediation.
- Authentication flaws deserve top-tier triage.
Enterprise vs Consumer Impact
Enterprise buyers should view this as a management-plane event with possible downstream operational consequences. Even if the flaw is “only” an authentication bypass, unauthorized access to a network-management platform can expose inventory data, topology, configuration state, and administrator workflows. In industrial settings, those are not abstract assets; they can directly affect uptime, maintenance planning, and incident response.Consumer users are not the audience here, but the comparison is useful. In a consumer app, an auth bypass might expose a private profile. In OT, the same class of bug can expose the layout of a plant network or grant control over the system used to configure it. That is why industrial software advisories often sound similar to IT advisories but carry a very different operational weight.
Operational consequences
A compromised management console can create confusion even before overt damage occurs. Administrators may see unexpected device states, altered settings, or inconsistent user behavior, and response time matters because industrial environments are tuned for availability. The most damaging outcome is often not dramatic sabotage but quiet administrative compromise that erodes confidence in the environment.This also changes how organizations should think about insurance, audit, and compliance. A platform that centralizes network control should be covered by stronger monitoring and recovery controls than a typical internal web app. If the application is reachable, it is part of the operational attack surface, whether or not it sits in an IT server room.
- Enterprise impact is operational, not just informational.
- Management-plane compromise can ripple outward.
- Industrial environments prize availability, making stealthy abuse dangerous.
- Audit and compliance expectations should reflect the platform’s privilege.
- Consumer analogies understate the seriousness of OT exposure.
Strengths and Opportunities
The good news is that Siemens has already issued a fix, CISA has amplified the advisory, and the affected version boundary is clearly defined. That gives defenders a concrete remediation target instead of a vague “watch this space” warning. It also creates an opportunity to tighten broader access controls around the management plane while the patch is being rolled out.There is also a constructive lesson here for industrial operators: the vulnerability can serve as a forcing function to improve identity governance, logging, and segmentation. If an organization uses the patch window to re-audit UMC access paths, it may emerge with a stronger baseline than it had before the advisory. In security terms, urgent work can become useful hardening.
- A fixed version is available now.
- The affected scope is specific and identifiable.
- The advisory is explicit about remediation.
- Patch efforts can be paired with access review.
- This is a good moment to test backup and recovery processes.
- Organizations can harden segmentation while updating.
- MFA and logging can reduce residual risk.
Risks and Concerns
The biggest concern is obvious: if the management interface is reachable, an unauthenticated attacker may be able to get in before the patch is applied. That makes exposure management urgent, especially in environments where remote support, shared admin access, or flat internal networks are still common. The bug is also attractive because it is conceptually simple and does not depend on user interaction.A second concern is operational inertia. Industrial teams often know about vulnerabilities quickly but cannot patch immediately because changes must be tested and scheduled. The delay is understandable, but it creates a window in which compensating controls must do the heavy lifting. Without them, the organization is effectively betting on obscurity.
- Reachable systems may be exposed before maintenance windows open.
- Change-control delays can outlast attacker scanning cycles.
- Management networks are sometimes broader than operators realize.
- Authentication bypasses can be chained with other weaknesses.
- Flat internal segmentation magnifies impact.
- Legacy trust assumptions may no longer be valid.
- Visibility gaps make abuse harder to detect.
Looking Ahead
The next few weeks will likely tell us whether defenders treat CVE-2026-24032 as a routine vendor patch or as a signal to reassess SINEC NMS exposure more broadly. If organizations rush to update, the impact should be limited; if they defer because the issue is “just” an auth problem, the risk remains open on a network that many teams consider highly privileged. In industrial security, small trust failures can have outsized consequences.This is also another data point in the growing convergence of OT and enterprise security expectations. Buyers increasingly want products that not only manage industrial assets but also embody secure design, strong authentication, and rapid patch support. Vendors that can answer those expectations transparently will have an advantage; those that cannot will face tougher procurement scrutiny and more conservative deployments.
- Watch for patch adoption rates in OT environments.
- Monitor whether exploit proof-of-concept code appears.
- Check whether management interfaces are internet-reachable or VPN-reachable.
- Review UMC configurations and MFA usage.
- Look for follow-on advisories involving adjacent SINEC components.
Source: CISA Siemens SINEC NMS | CISA