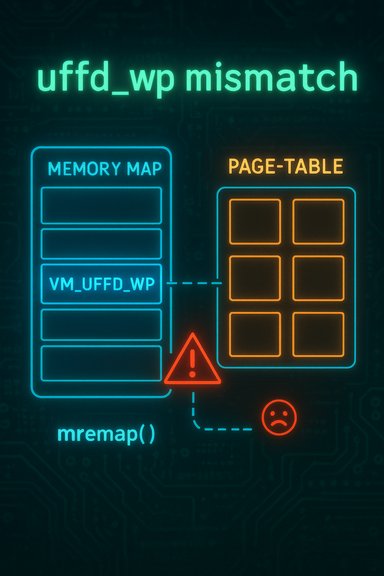
The Linux kernel vulnerability tracked as CVE-2025-21696 — described upstream as “mm: clear uffd-wp PTE/PMD state on mremap” — is a correctness bug in the kernel’s memory-management paths that can produce kernel warnings, oopses, and denial-of-service conditions when specific userfaultfd and mremap sequences are exercised. The defect stems from inconsistent clearing of the uffd-wp (userfaultfd write‑protect) bit: after an mremap of memory previously registered with userfaultfd in a write‑protected state but without the UFFD_FEATURE_EVENT_REMAP capability, the VMA flags are cleared while corresponding PTE/PMD-level flags are not. That mismatch can make a later mprotect(PROT_WRITE) attempt trigger kernel checks that raise warnings or panic the kernel, impacting availability.
Background
What userfaultfd, uffd‑wp and mremap are
The Linux userfaultfd (UFFD) mechanism provides userland the ability to handle page faults for user mappings. One UFFD mode supports write‑protection: the kernel can mark pages so that the next write causes a userfaultfd event instead of a normal write, allowing userland to mediate writes for live migration, copy‑on‑write tooling, and other advanced memory workflows.The kernel represents UFFD state at multiple levels: as a VMA (vm_area_struct) flag such as VM_UFFD_WP and as bits in page table entries (PTEs/PMDs) — the uffd‑wp logical flag. When the kernel performs memory operations like mremap (which moves or resizes mappings), it must keep those representations in sync. If the VMA-level flag is cleared but the PTE/PMD flags remain set, subsequent operations that consult the PTEs (for example, mprotect to add write permission) will see a PTE marked as uffd‑wp while the VMA says otherwise — that inconsistency can trip diagnostic checks inside page_table_check_pte_flags and cause warnings or oopses.
How the bug arises (in plain terms)
- A process registers a memory region with userfaultfd in write‑protected mode but does not request UFFD_FEATURE_EVENT_REMAP (the event that tells userland about remap events).
- That region is later subject to mremap, which upstream code already clears the VMA VM_UFFD_WP bit but — in the affected code paths — does not always clear the uffd‑wp bit in the PTE/PMD entries (including swap/PTE marker forms and hugetlb/huge PMD paths).
- A later call to mprotect(PROT_WRITE) tries to set the PTE writable while the PTE still carries the uffd‑wp bit. The page_table_check_pte_flags validation notices the inconsistency (a writable PTE with uffd‑wp) and emits warnings or triggers kernel oops behavior.
This is the precise technical mismatch the upstream fix addresses: always clear the logical uffd‑wp bit at the PTE/PMD level on any mremap path so the VMA and page-table representations remain consistent.
Why this matters: impact and attack model
Primary impact — availability (DoS)
This vulnerability is an availability‑first correctness bug. When triggered on a vulnerable kernel, it can produce kernel warnings, oopses or crashes that disrupt services and require reboot or manual recovery — in short, a denial of service. Multiple vulnerability trackers and vendor advisories classify the impact as a medium severity availability issue with a CVSS v3.1 base score commonly recorded at 5.5 (vector AV:L/AC:L/PR:L/S:U/C:N/I:N/A:H). That scoring reflects the requirement for local or host‑adjacent privileges to exercise the sequence and the primary impact being host instability rather than confidential data loss.Who can exploit it
The exploit model is local or host‑adjacent. To reproduce the condition, an attacker (or buggy/malicious local process) must be able to:- Create a userfaultfd registration in write‑protected mode (UFFD WP),
- Perform an mremap in the affected pattern, and
- Later cause an mprotect(PROT_WRITE) to the region or otherwise touch the PTEs in a way that exercises the inconsistent state.
Exploitation realities and caveats
There is no authoritative public evidence that this specific CVE was used for privilege escalation or arbitrary code execution in the wild at disclosure. The publicly described behavior and vendor analysis focus on kernel correctness and availability — kernel warnings and oopses — rather than a direct RCE primitive. That said, kernel availability bugs in multi‑tenant contexts are operationally serious: an attacker who can reliably crash a hypervisor host or shared runner can cause outsized disruption. Treat claims about in‑the‑wild exploitation as unverified unless vendors or telemetry publicly confirm incidents.Technical analysis of the fix
What the patch changes
Upstream kernel maintainers corrected the mremap code paths so that whenever a mapping that was previously userfaultfd write‑protected is remapped (and VM_UFFD_WP is cleared on the VMA), the kernel also explicitly clears the uffd‑wp indicator at the PTE/PMD level. The fix is careful to account for the different physical representations of that logical flag: direct PTE bits, swap PTE bits, and PTE markers. It also covers typical PTE paths plus huge PMD and hugetlb paths so the correction is comprehensive across mapping granularities. The result is consistent VMA and page‑table state and a removal of the warning/oops condition when a subsequent mprotect(PROT_WRITE) is applied.Why the change is narrowly targeted and low‑risk
The correction is surgical — it does not restructure the memory subsystem or alter the semantics of userfaultfd. Instead, it enforces a consistency invariant the kernel should already maintain. Because the change is limited in scope, it is straightforward to backport to stable kernel series and is unlikely to introduce performance regressions. This is the typical pattern for upstream fixes that aim to remove a narrow correctness window without destabilizing unrelated functionality.Affected systems and vendor responses
Upstream / distribution mapping
Vendor advisories and security trackers mapped the CVE to kernel series and package versions. Representative vendor records show:- NVD and multiple vendor trackers published the upstream summary on 2025‑02‑12.
- Debian’s security tracker lists affected source packages and shows which releases were patched or remain vulnerable; some unstable/trunk kernels were marked fixed in later point releases while older stable branches required backports.
- Amazon Linux advisory listings note the CVSS 5.5 score and mark various Amazon Linux kernel branches as either not affected or “no fix planned” depending on the kernel variant.
- SUSE, Red Hat, Oracle Linux and other major trackers mirrored the upstream description and included stable backports or distribution advisories as they became available.
Microsoft and Azure context
Microsoft has begun publishing machine‑readable attestations (VEX/CSAF) for some Microsoft‑published Linux artefacts (for example, Azure Linux images). Those attestations are useful for automation and allow Azure customers to determine whether a particular Microsoft SKU contains the impacted upstream component. However, absence of an attestation for other Microsoft SKUs does not prove absence of the vulnerable component — each image or artifact must be verified individually until vendors map every product. For those running WSL kernels, Azure Marketplace images, or Microsoft‑curated images, explicitly verify the kernel version and vendor advisories.Detection, triage, and remediation playbook
Detection and telemetry signals to watch for
Admins and SREs should hunt for kernel messages and traces that indicate inconsistent userfaultfd/PTE state and page table checking failures. Common signals:- Kernel WARN/OOPS traces referencing mm/userfaultfd.c, page_table_check_pte_flags, or explicit text mentioning uffd‑wp or UFFD. These traces are the primary runtime indicator.
- Reproducible kernel warnings during workloads that call userfaultfd, mremap, mprotect, or that use KSM/MADV_UNMERGEABLE in combination with UFFD MINOR mode.
- Sudden or repeatable host reboots, dmesg traces, or kernel oops events on multi‑tenant hosts coincident with workloads that manipulate memory mappings or run guest workloads that exercise the host’s page‑table fastpaths.
- Confirm running kernel: uname -r.
- Check kernel config: zgrep CONFIG_KSM /boot/config-$(uname -r) (where applicable).
- Inspect kernel logs: journalctl -k or dmesg for UFFD‑related warnings; save and preserve crash dumps for forensic analysis.
Remediation: update, reboot, validate
The only authoritative remediation is to install a kernel package that contains the upstream fix (or vendor backport) and reboot into the patched kernel. Because the correction lives in the MM (memory management) path and touches PTE/PMD state, a reboot is necessary to fully eliminate the vulnerable in‑memory code path.Operational steps:
- Inventory and prioritize: Identify hosts that accept untrusted code or host multi‑tenant workloads (cloud hypervisors, CI runners, shared build hosts). Those get highest priority.
- Map kernel packages to vendor advisories: use your distro’s security tracker and package changelogs to confirm the presence of the upstream commit or the distributor’s fixed package version.
- Stage and test: Apply patched kernels in a pilot group, exercise the workloads that previously triggered UFFD or KSM interactions, and validate there are no regressions.
- Roll out and reboot: Schedule coordinated reboots and keep rollback points. Monitor kernel logs for recurrence.
- Implement compensating controls: restrict which users or containers can perform userfaultfd registrations; isolate untrusted workloads to dedicated hosts; limit access to virtualization management planes and image mounting services.
Practical guidance for WindowsForum readers
If you run Linux servers or host VMs (including on Azure)
- Treat this as an operations‑level availability risk: inventory kernels, prioritize hypervisors and shared hosts, and plan reboots into patched kernels as soon as your distribution publishes fixed packages.
- For Azure customers: verify whether your specific Azure images (Azure Linux, Marketplace images, WSL kernels, etc. include the vulnerable upstream component. Use vendor attestations where available, but do not assume coverage across all Microsoft artifacts — check each image’s kernel version.
If you run desktops, WSL, or developer machines
- The typical desktop risk is lower because exploitation requires local interaction and the use of userfaultfd/KSM patterns. However, developer tools that manipulate memory mappings or run untrusted images (for example, when building or testing VM images) could expose your system. Keep your kernel packages updated and monitor distro advisories.
For cloud and multi‑tenant operators
- Prioritize host patching and staged reboots for hypervisors, shared CI runners, and any host running untrusted tenant code. The local attack vector plus severe availability impact make this a high operational priority.
- Add SIEM/EDR rules to flag repeated kernel WARN/OOPS messages matching userfaultfd or page_table_check_pte_flags traces; consider automated host quarantine for repeat events pending remediation.
Strengths, limitations and residual risk
Strengths of the upstream fix
- The change is narrow and correct: it enforces an invariant (VMA and PTE state consistency) that the kernel should maintain, without broad behavior changes.
- Low regression risk: the patch is small and was accepted into stable trees and backports, making it practical for distributors to include in stable kernel releases.
What the fix does not change
- It does not change the fundamental userfaultfd semantics or expose new system calls.
- It does not remove the need for reboots: kernel code is in‑memory and requires a reboot to be replaced.
- It does not remove the operational reality that local code with sufficient privileges can cause kernel instability; it simply closes a specific correctness window.
Residual risk and monitoring
- Long‑tail vendors and embedded device images may not receive timely backports. Operators should verify vendor images and OEM kernels explicitly.
- Because some vendor trackers and packaging trees differ in status (some kernels marked “no fix planned” for specific Amazon Linux kernel branches, for example), confirm per‑platform remediation plans rather than relying on generic CVSS-derived prioritization.
Final checklist (actionable, prioritized)
- Inventory hosts that run as multi‑tenant hypervisors, CI runners, or that host untrusted workloads: uname -r; collect /boot/config and package metadata.
- Consult your distributor’s security tracker (Debian, Ubuntu, Red Hat, SUSE, Amazon ALAS, etc. to find the fixed package name/version or the upstream commit ID. Confirm that your installed kernel/package contains the corresponding fix.
- Stage the vendor’s patched kernel in a pilot group, exercise critical workloads that interact with UFFD/KSM or heavy memory remapping, and validate behavior.
- Roll out patched kernels and schedule reboots; monitor kernel logs for recurrence (journalctl -k, dmesg). Preserve crash dumps when possible.
- If immediate patching is infeasible, reduce exposure: disable or limit untrusted workloads, restrict memory‑mapping features for untrusted users, and increase logging/alerting for UFFD-related kernel traces.
Conclusion
CVE‑2025‑21696 is a memory‑management correctness issue that can cause kernel warnings and denial‑of‑service by leaving uffd‑wp state inconsistent between VMAs and PTE/PMD entries after mremap. The technical fix upstream is narrowly scoped and designed to restore invariants: explicitly clear the uffd‑wp PTE/PMD bits during mremap so VMA and page‑table state remain consistent. The operational consequence is clear — patch and reboot high‑value, multi‑tenant, or untrusted‑workload hosts as a priority, and verify vendor package mappings for your distributions and cloud images. While there is no confirmed public evidence of exploitation for privilege escalation, the availability impact alone makes this a practical priority for cloud operators and shared infrastructure owners; timely remediation and vigilant log monitoring are the appropriate responses.Source: MSRC Security Update Guide - Microsoft Security Response Center