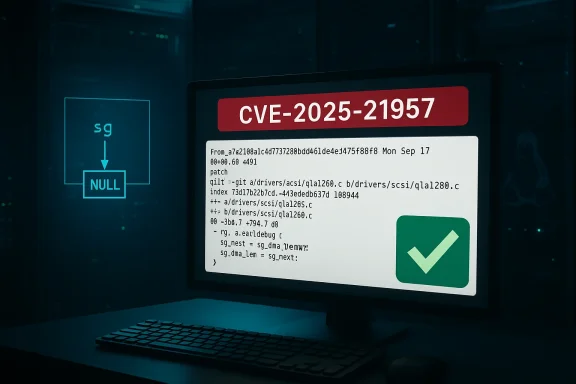
A small, targeted fix landed upstream this spring to close CVE-2025-21957 — a null‑dereference in the Linux SCSI qla1280 driver that can trigger a kernel oops (and therefore a denial-of-service) when the driver is built with its debugging path enabled and the runtime debug level exceeds 2.
The qla1280 driver family implements support for QLogic 12xx-series SCSI/FC devices in the Linux kernel. The issue tracked as CVE‑2025‑21957 is not a logic bug in normal I/O processing; instead, it appears in a debug-only path that prints scatter‑gather list information. When compiled with the kernel config symbol that enables QLA1280 debug helpers (commonly surfaced as DEBUG_QLA1280), and when the module’s runtime debug verbosity (ql_debug_level) is set high (greater than 2), the code prints an incorrect quantity from the scatter‑gather chain — using the wrong helper and ultimately dereferencing a NULL pointer. The upstream change corrects the debug print to use the intended length helper and prevents the oops.
Why this matters beyond a one‑liner: kernel oopses stop kernel threads, can destabilize the host, and in production environments they frequently require reboots or manual intervention. While the bug’s trigger sits inside debug-only code, production kernels can and do sometimes include debugging helpers (especially in vendor or appliance builds), and runtime debug knobs can be turned up for troubleshooting — which makes what sounds like a narrow defect practically important for operators.
For teams responsible for appliances or embedded devices, the takeaways are sharper: confirm whether vendor images include DEBUG_QLA1280, engage the vendor for a patched image if needed, and add kernel debug flags to your SBOM/inventory so small developer-facing changes do not become large operational outages. History shows that tiny correctness fixes in kernel debug or teardown paths repeatedly translate into meaningful availability incidents; preventing those incidents is a matter of disciplined image management, fast patching, and limiting debug exposure.
Appendix: quick reference (one‑page)
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
The qla1280 driver family implements support for QLogic 12xx-series SCSI/FC devices in the Linux kernel. The issue tracked as CVE‑2025‑21957 is not a logic bug in normal I/O processing; instead, it appears in a debug-only path that prints scatter‑gather list information. When compiled with the kernel config symbol that enables QLA1280 debug helpers (commonly surfaced as DEBUG_QLA1280), and when the module’s runtime debug verbosity (ql_debug_level) is set high (greater than 2), the code prints an incorrect quantity from the scatter‑gather chain — using the wrong helper and ultimately dereferencing a NULL pointer. The upstream change corrects the debug print to use the intended length helper and prevents the oops.Why this matters beyond a one‑liner: kernel oopses stop kernel threads, can destabilize the host, and in production environments they frequently require reboots or manual intervention. While the bug’s trigger sits inside debug-only code, production kernels can and do sometimes include debugging helpers (especially in vendor or appliance builds), and runtime debug knobs can be turned up for troubleshooting — which makes what sounds like a narrow defect practically important for operators.
What the bug looks like (technical summary)
- Root cause: a debug print path uses the wrong SG (scatter‑gather) accessor — reporting or walking sg_next(s) where the intent was to use sg_dma_len(s) — and that misuse allows a NULL pointer to be dereferenced when certain SG list shapes are present.
- Trigger conditions:
- The driver is compiled with DEBUG_QLA1280 enabled (compile‑time).
- The runtime debug verbosity ql_debug_level is set to a value greater than 2.
- The specific SG/list shape that exposes the mistaken dereference occurs during execution.
- Consequence: a kernel oops (NULL dereference) which typically kills the offending kernel thread and can lead to system instability or a hard reboot, creating an availability (DoS) impact but not, in the reported analysis, confidentiality or integrity loss.
Affected versions and scope
Public vulnerability trackers and vendor errata list kernel series that received the upstream correction and backports. The practical mapping varies by distribution because maintainers routinely backport fixes into different stable kernel streams:- Broadly reported affected trees include kernels across the 5.x and 6.x stable branches; distribution advisories give precise package-level mappings. Operators should consult their vendor’s kernel security advisory to determine the exact package and fixed version for their distribution.
- Several distributions published errata incorporating the fix into point releases (for example, ALT Linux updated 5.4.292 builds). Where vendors supply livepatch-style updates, those may also include the change for supported kernels. Do not assume every vendor build is identical — the presence or absence of DEBUG_QLA1280 and the shipped debug knobs determine real exposure.
Impact analysis: what administrators need to know
- Primary impact: Availability (Denial-of-Service). The CVSS assessments aggregated in public trackers classify the impact as medium overall (CVSS v3.1 base score commonly cited ~5.5) with a high availability consequence in the worst case. The attack vector is local — an unprivileged user or local process could trigger the debug path if the runtime knob is accessible.
- Exploitability: Low-to-moderate difficulty for DoS, high difficulty for privileges or code execution. Because this is a NULL dereference in debug printing, turning it into arbitrary code execution would be extremely difficult and is not the expected impact. However, crashing kernels in multi‑tenant or shared environments is a valuable capability for an attacker aiming to disrupt service.
- Likely targets: devices or servers running QLogic hardware with vendor kernels that enable QLA1280 debugging, storage appliances, embedded systems, and any environment where operators temporarily elevate driver debug levels for troubleshooting. Cloud images built from standard distribution kernels are less likely to be vulnerable unless the distributor ships a debug-enabled qla1280 module.
- Public exploitation: at disclosure time there were no credible reports of weaponized public proof‑of‑concepts or active exploitation campaigns. The absence of public exploit code reduces immediate panic but does not lower the operational priority for affected deployments: a reproducible kernel oops is a legitimate operational risk.
Detection and indicators
If you suspect exposure or want to detect attempted triggers, look for the following signals:- Kernel logs and console output: watch dmesg, journal, and serial console logs for oops traces that reference qla1280, scatter‑gather operations, or a NULL dereference trace during SCSI or FC operations. A sudden kernel oops during storage I/O or during driver debugging increases suspicion.
- Runtime debug settings: check whether the qla1280 module is present and whether ql_debug_level is writable in sysfs or via module parameters. On many systems, ql_debug_level is adjustable via sysfs or module param, so auditing its value fleet‑wide will identify risky hosts.
- Module build flags: for bespoke or vendor kernels, confirm whether DEBUG_QLA1280 was compiled in. This often requires checking the kernel config used to build the running kernel (e.g., /proc/config.gz or the distribution kernel config packages). If the debug symbol is not present, the code path is unlikely to be reachable.
- Repeated crashes correlated with elevated debug verbosity or diagnostic windows: if an appliance is unstable only while support teams raise driver debug levels, that pattern is a match for this class of bug.
Mitigation and remediation steps
- Identify affected hosts
- Check for the qla1280 module: lsmod | grep qla1280.
- Inspect kernel logs for qla1280 load messages and call traces around OOPS events.
- Verify the running kernel’s configuration for DEBUG_QLA1280 (look at /proc/config.gz or vendor kernel config packages).
- Patch promptly
- Apply vendor/distribution kernel updates that include the upstream fix. Major distributors have backported the change into stable builds and published advisories; follow your packaging and change‑control processes to install the fixed kernel package and reboot.
- Short‑term workarounds (if you cannot patch immediately)
- Lower or lock down ql_debug_level: set it to 0 or otherwise remove write access from untrusted users so diagnostic probing cannot be used to reach the problematic print path.
- Unload or blacklist the qla1280 module when the hardware is not required. That prevents the driver code from running entirely, at the cost of losing attached QLogic device functionality.
- Restrict local access: tighten role‑based access so only trusted operators can raise driver debug levels or run the commands that exercise storage paths.
- Verify after remediation
- Reboot with the patched kernel and confirm uname -r and your package manager show the fixed build.
- Re-run the pre-deployment debug scenario (if possible) in a test environment to ensure that raising ql_debug_level does not produce an OOPS.
- Resume service gradually and monitor dmesg/journal for any recurrence.
- Long‑term hardening
- Maintain an inventory of kernel config options used in vendor/appliance images so you can quickly identify shipped debug flags.
- Where possible, avoid shipping production kernels with debug‑heavy compile options enabled. If debug symbols are necessary for support, constrain access to them and use gated diagnostic windows.
Operational checklist (prioritized)
- Immediate (0–48 hours)
- Query which hosts load qla1280 and whether ql_debug_level is writable.
- If any production host shows debug enabled, schedule a maintenance window to apply the vendor kernel update or temporarily restrict debug level access.
- Short term (days)
- Apply vendor kernel packages that include the fix and reboot hosts in controlled waves.
- For embedded appliances without vendor updates, contact the vendor for a patched firmware/kernel or plan controlled containment (module blacklist, isolation).
- Medium term (weeks)
- Add kernel config and module‑level checks to your inventory system and vulnerability scanning to identify future exposures quickly.
- Where feasible, convert support practices to avoid leaving debug knobs enabled in production.
- Long term
- Build or request vendor images that explicitly remove unnecessary debug code from production kernels.
- Implement a policy to treat shipped debug options as a security risk that triggers automatic review and mitigation.
Why a tiny fix still matters: critical analysis
- Strength of the response: The upstream patch is surgical — it corrects the debug print to use the intended sg_dma_len() helper and avoids the NULL dereference. Small, well‑documented fixes like this are precisely the kind of change that backports cleanly to many stable kernel trees, and vendors have generally reacted quickly with distribution updates and errata. That makes remediation straightforward for administrators who follow vendor advisories.
- Why it still creates operational risk: the vulnerability’s trigger lives in developer/debugging code. The long tail of risk comes from three places:
- Vendors and appliance makers sometimes enable extra debug for field support.
- Custom kernels used by OEMs or specialized appliances are frequently out of sync with distribution packages and can remain unpatched for months.
- Support teams occasionally raise debug verbosity in production to trace other problems, creating a transient attack surface for a vulnerability that otherwise would be inert.
- Detection difficulty and the false sense of security: simple CVE scanning that checks package versions can miss custom kernels with debug options compiled in. Operators must verify both package-level fixes and the presence/absence of debug code paths. This is the same operational lesson repeated across multiple kernel CVEs in recent years: correctness in edge paths matters.
- Residual risk: while this CVE is primarily a DoS vector, kernel oops primitives are the building blocks of more creative attack sequences. Security teams should not dismiss the bug as “only crashing” without considering multi‑stage chains or correlated vulnerabilities that might widen the impact. Keep monitoring for new public exploit information.
Forensic and logging guidance
- Preserve the kernel console and any serial/log captures around the time of OOPS; early logs often contain the only useful stack trace in systems that reboot automatically.
- Collect uname -a, the kernel config used to build the running kernel, and any module parameters for qla1280 when triaging.
- If you need vendor support, gather a reproduction trace (in a lab) that shows the debug level increase and the resulting oops; vendors will usually ask for a minimal reproduction or log sequences to validate the fix mapping.
Closing assessment and recommended next steps
CVE‑2025‑21957 is a practical, medium‑severity kernel defect: the fix is small and effective, but the operational consequences can be outsized because the bug causes kernel oops. Administrators should treat this as a targeted remediation item: verify whether your fleet actually has the qla1280 debug path enabled, apply vendor kernel updates where applicable, and if patching is delayed, restrict runtime debug control or unload the module on hosts that do not need QLogic SCSI/FC functionality.For teams responsible for appliances or embedded devices, the takeaways are sharper: confirm whether vendor images include DEBUG_QLA1280, engage the vendor for a patched image if needed, and add kernel debug flags to your SBOM/inventory so small developer-facing changes do not become large operational outages. History shows that tiny correctness fixes in kernel debug or teardown paths repeatedly translate into meaningful availability incidents; preventing those incidents is a matter of disciplined image management, fast patching, and limiting debug exposure.
Appendix: quick reference (one‑page)
- CVE: CVE‑2025‑21957.
- Symptom: kernel oops (NULL dereference) in qla1280 when ql_debug_level > 2 and debug build enabled.
- Primary impact: Availability / DoS.
- Exploit vector: Local; low privileges required to trigger diagnostics if runtime access allowed.
- Immediate mitigation: patch vendor kernel packages; if not possible, set ql_debug_level to 0/unwritable or blacklist qla1280.
Source: MSRC Security Update Guide - Microsoft Security Response Center