A specially crafted Helm chart archive can expand into an enormous decompressed payload that exhausts available memory and kills the Helm process — a denial‑of‑service vector tracked as CVE‑2025‑32386 — and while Microsoft’s update guide currently names Azure Linux as a product that “includes this open‑source library and is therefore potentially affected,” that phrasing is an inventory attestation, not a categorical statement that no other Microsoft product could carry the same vulnerable code.
Helm is the de facto package manager for Kubernetes charts. Charts are compressed archives (typically .tgz/.tar.gz) that contain YAML templates, metadata and auxiliary files such as JSON Schema validators. Because charts travel between authors, chart repositories, CI pipelines and operator workstations, trust boundaries can be wide and attack surface exposed. Attackers can weaponize compressed archives by constructing them so that a small compressed file expands into a vastly larger decompressed form — a classic “decompression bomb” — and exploit any consumer that decompresses without reasonable limits.
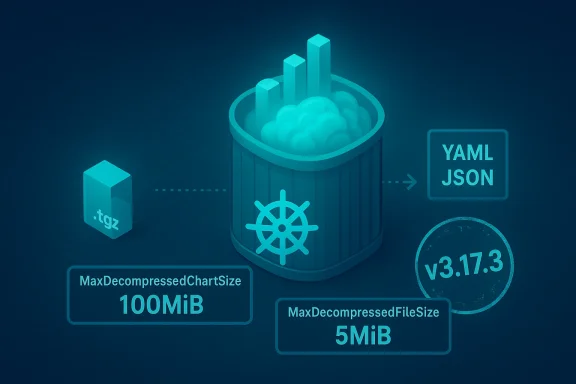
In April 2025 Helm maintainers and security researchers published advisories describing two related issues in Helm 3.x: (1) a chart archive decompression problem that can exhaust memory when a chart is unusually compressible (CVE‑2025‑32386), and (2) JSON Schema parsing recursion that can trigger stack exhaustion (CVE‑2025‑32387). Both problems were fixed in the same maintenance release: Helm v3.17.3. The package‑level fix for the decompression/vector-of‑memory exhaustion issue introduced reasonable decompressed-size limits to prevent explosive allocation.
Look for Helm (or the helm library) in:
Operationally, the fastest way for most organizations to reduce exposure to CVE‑2025‑32386 is:
Conclusion
CVE‑2025‑32386 is a realistic availability threat for any environment that unpacks or validates Helm charts without limits. Helm’s upstream fix (v3.17.3) adopts a pragmatic, safer default by enforcing decompressed‑size limits, but the operational reality — broken charts, lagging upgrades, and multiple places Helm appears in modern cloud workflows — means defenders must act on multiple fronts: patch, inventory, harden ingestion, apply resource constraints, and rely on SBOMs while vendor attestations continue to roll out. Microsoft’s explicit attestation that Azure Linux includes the library is valuable and should spur immediate action for that product, but it is not an assurance that the rest of Microsoft’s product catalog is unaffected; customers must treat each artifact the same way and verify or patch accordingly.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
Helm is the de facto package manager for Kubernetes charts. Charts are compressed archives (typically .tgz/.tar.gz) that contain YAML templates, metadata and auxiliary files such as JSON Schema validators. Because charts travel between authors, chart repositories, CI pipelines and operator workstations, trust boundaries can be wide and attack surface exposed. Attackers can weaponize compressed archives by constructing them so that a small compressed file expands into a vastly larger decompressed form — a classic “decompression bomb” — and exploit any consumer that decompresses without reasonable limits.In April 2025 Helm maintainers and security researchers published advisories describing two related issues in Helm 3.x: (1) a chart archive decompression problem that can exhaust memory when a chart is unusually compressible (CVE‑2025‑32386), and (2) JSON Schema parsing recursion that can trigger stack exhaustion (CVE‑2025‑32387). Both problems were fixed in the same maintenance release: Helm v3.17.3. The package‑level fix for the decompression/vector-of‑memory exhaustion issue introduced reasonable decompressed-size limits to prevent explosive allocation.
What CVE‑2025‑32386 is, technically
The attack surface: chart archives and the loader
A Helm chart archive is a gzipped tarball (.tgz) that Helm extracts when you run commands such as helm install, helm template, helm lint, or when controllers and tooling (for example GitOps operators) fetch and inspect charts. Helm’s chart loader historically read archive contents and materialized them into memory structures without enforcing strict upper bounds on decompressed data sizes. That left a window where a crafted archive — tiny compressed, huge decompressed — could force Helm to allocate more memory than the host process or system could provide, leading to OOM termination or panics.How the exploit works
- An attacker builds an archive that uses repeated patterns or crafted tar entries so that gzip compression yields a very small on‑disk footprint but decompresses into a very large payload.
- When Helm’s loader unpacks the archive and attempts to read files into memory, the decompressed sizes exceed available memory or sensible resource limits.
- The process attempts to allocate the expanded memory and then is either terminated by the OS OOM killer or the process itself fails catastrophically, producing a denial‑of‑service condition in CI runners, developer machines, or automated tooling.
Remediation in Helm and concrete limits
Helm fixed the issue in v3.17.3 by introducing explicit upper bounds on decompressed sizes. The upstream changes added variables such as MaxDecompressedChartSize (default: 100 MiB) and MaxDecompressedFileSize (default: 5 MiB) to enforce sensible limits while unpacking archives; if an extracted file or the total decompressed archive exceeds those thresholds, Helm returns an error rather than attempting unbounded allocation. This is the core technical mitigation you should expect to see in patched Helm builds. Note: the new limits also created operational friction for some users because some legitimate charts exceeded those thresholds and required repackaging or vendor coordination.Why Microsoft named Azure Linux — and what that means
Microsoft’s product‑scoped attestation model
When Microsoft’s Security Response Center (MSRC) maps an upstream open‑source component to a Microsoft product, the update guide often includes a short FAQ that reads like the wording you quoted: “Azure Linux includes this open‑source library and is therefore potentially affected by this vulnerability.” That is a statement of fact about Microsoft’s inventory for that specific product artifact — it means Microsoft inspected Azure Linux (its packages and images) and found the affected upstream component there. Microsoft has also committed to publishing machine‑readable CSAF/VEX attestations and to updating CVE mappings if additional Microsoft products are discovered to include the impacted component. In short: when Microsoft names Azure Linux, it is saying “we checked this product and it contains the component,” not “this is the only product in the entire company that could contain it.”Why the distinction between “attested” and “exclusive” matters
- An attestation is product‑scoped: Microsoft checked Azure Linux and is telling customers “if you use Azure Linux, treat this as in‑scope.” That guidance is actionable for Azure Linux operators and customers (patch the distro packages or update Helm).
- Software reuse is pervasive: the same upstream library or binary can be included in many artifacts across a vendor’s catalog — container images, developer tools, managed services, VM images, or packaged bundles. Unless Microsoft explicitly lists all artifacts that contain the component, you can’t assume they’re unaffected just because they aren’t named.
- Microsoft’s pledge to publish CSAF/VEX statements and update CVE pages as they discover additional impacted products is important: it means the company intends to expand the attestation map over time, but that process is phased and not instantaneous. Customers must therefore do their own artifact inventory while the vendor completes its mapping.
Practical reading of the MSRC line
- If you run Azure Linux images, containers, or Cloud Shell instances, treat Microsoft’s attestation as evidence that you may be affected and follow the remediation guidance immediately.
- If you run other Microsoft‑supplied artifacts — for example, Azure Marketplace VM images, AKS node images, WSL2 kernels, or Microsoft developer tooling that bundles Helm — do not assume they are untouched. Those artifacts must either be validated via Microsoft’s CSAF/VEX rollouts or inspected locally.
Cross‑checks and independent verification
To avoid over‑reliance on a single source, here are the cross‑references you should use when validating impact and remediation:- Helm maintainers’ advisory and the upstream commit that introduced size limits and other safety checks (the fix is included in the release tagged v3.17.3). External vulnerability databases and OSV indexes record the fix and the affected version ranges.
- Linux distro and vendor advisories (for example SUSE, distributions that package Helm) mirrored the upstream fix in their security updates, confirming the same version and the same mitigation strategy. This independent packaging and vendor confirmation helps validate the upstream commit.
- Community reporting and issue trackers show both the fix and consequences: after v3.17.3 was published, several users reported breakage for charts that exceeded the new decompressed file size limits — confirming that the fix introduced real operational constraints and therefore requires attention from maintainers and operators.
Operational impact: where you should look inside your environment
Helm is not just a CLI on a developer laptop — it’s embedded across cloud developer workflows. Microsoft itself documents Helm as included in Cloud Shell and supported in multiple Azure developer flows (AKS integration, Azure Developer CLI). That means a vulnerable Helm binary or an embedded vulnerable Helm library surface can appear in many places across a cloud environment.Look for Helm (or the helm library) in:
- Developer workstations and laptops (local installations of helm CLI).
- CI/CD runners and GitHub Actions runners (self‑hosted or managed) that run helm commands.
- GitOps agents and controllers that fetch and template charts (Flux, ArgoCD, helm‑controller, etc.).
- Cloud provider‑managed shells and images (Azure Cloud Shell runs on Azure Linux and includes Helm).
- Marketplace VM images, container images, AKS node base images, and packaged Microsoft tooling that might vendor the helm binary or library.
Practical mitigation checklist (prioritized)
Apply the following steps immediately, in order of practical impact:- Patch Helm where you control it.
- Upgrade any helm CLI installations to v3.17.3 or later. This is the primary technical fix for CVE‑2025‑32386. Confirm upgrades in all environments: local workstations, CI runners, operator containers, and any image that packages Helm.
- Inventory Microsoft artifacts and other images.
- Treat Microsoft’s attestation for Azure Linux as a confirmed hit for that artifact and patch accordingly. For other Microsoft artifacts (WSL2 kernels, AKS node images, Marketplace VM images, Cloud Shell), do not assume “not affected” — either consult Microsoft’s CSAF/VEX machine‑readable attestations (as they are published) or run a local artifact inspection to find any helm binaries or the helm Go module.
- Add compensating controls in CI/CD and automation.
- Run Helm in sandboxes with process memory limits (cgroups, container memory limits, or ulimit) so an abusive decompression cannot exhaust host memory.
- Limit who can push charts to internal chart repos; require chart signing and provenance checks for published charts.
- Scan incoming charts (for example with tar/gzip heuristics and uncompressed size checks) before passing them to Helm. Consider enforcing maximum uncompress sizes as part of repository ingestion pipelines.
- Harden chart repositories and registries.
- If you host chart repositories (Azure Container Registry with OCI charts, ChartMuseum, Harbor, etc.), add server‑side checks that refuse uploads with suspicious compression ratios or that exceed decompressed size quotas. Azure ACR and other registry tooling often support server‑side admission controls — use them.
- Monitor for symptoms of OOM and process churn.
- Instrument CI runners, Cloud Shell nodes, and operator hosts for OOM events, frequent helm crashes, or rapid memory spikes during chart operations. Configure alerting on OOM events and on repeated helm failures originating from chart handling code paths.
- Coordinate with chart maintainers if you’re pinned to older Helm versions.
- If you can’t upgrade to v3.17.3 immediately, ensure your chart sources are vetted and that charts do not include large binary blobs or suspicious compressed content. For long‑lived charts that legitimately exceed the new limits, work with upstream maintainers to repackage assets (use container image registries for big binaries rather than embedding them in charts).
- Use SBOMs and artifact inspection tools.
- Maintain software bills‑of‑materials (SBOMs) for images and VM images. SBOMs make it far easier to answer “which artifacts contain helm?” and to prioritize updates. Microsoft is rolling out machine‑readable CSAF/VEX attestations to aid this process, but until vendor attestations cover your full artifact set, internal SBOMs are essential.
What Microsoft’s wording does and does not promise
Microsoft’s messaging — that Azure Linux includes the open‑source library and therefore is potentially affected — is important and trustworthy for the artifact it names. But customers should not read that sentence as global denial (i.e., “no other Microsoft product ships this library”). Real‑world software supply chains are messy:- Microsoft’s attestation represents what the company has inspected and mapped so far. The vendor’s promise to publish CSAF/VEX and to update CVE entries when they find additional affected products means the mapping will improve over time.
- Customers must operate defensively: you should inventory and patch the artifacts that run in your estate, including both vendor‑provided and self‑managed images, and you should not defer to a single product‑scoped bulletin to cover all of Microsoft’s outputs.
Notable strengths and the residual risks
What’s good about the response
- The Helm project produced a targeted fix (v3.17.3) that adds explicit resource bounds rather than brittle heuristics. That is the right engineering approach: fail fast on suspicious archives and avoid unbounded allocations.
- Vendors and distributions picked up the fix promptly; multiple vendor advisories and distro security updates reference v3.17.3. This reduces the window of exposure for operators who follow standard update channels.
- Microsoft’s increasing use of machine‑readable CSAF/VEX attestations makes it more practical — in the medium term — for customers to automate product‑level inventory checks and to correlate vendor attestations with internal SBOMs.
Residual and practical risks
- Patch friction: the newly introduced default limits (100 MiB chart / 5 MiB file) broke some legitimate charts and ecosystem tooling, causing operators to delay upgrades or to pursue risky workarounds (for example, downgrading or compiling custom Helm clients). That means unpatched, vulnerable Helm instances likely persist in many environments.
- Broad attack surface: Helm is used widely, from individual workstations to automated controllers, and in many places you might not expect it. Any automated process that unpacks or inspects charts should be treated as in‑scope for risk mitigation.
- Vendor attestation lag: MSRC’s product‑scoped mapping is helpful but not exhaustive. Microsoft’s pledge to expand machine‑readable attestations is positive — but while that work is in progress, customers must maintain their own inventory discipline.
Recommended detection and validation steps (quick playbook)
- Search your environment for helm binaries and the helm Go module:
- grep for “helm” in image layers, packages, and container run paths.
- Inspect AKS node images, Marketplace VM images, Cloud Shell containers, and any VM/AMI catalog items you consume.
- Verify versions:
- For CLI/packaged installs, run helm version and verify Release is v3.17.3+.
- For container images, check package manifests or SBOMs for helm versions.
- Test pipeline behavior:
- In a staging environment, enable v3.17.3 and run existing chart installs and templates to surface breakage caused by the new decompression limits; coordinate with chart owners to repack large files out of charts.
- Harden ingestion points:
- Add pre‑ingest checks for charts pushed to internal registries (reject charts whose compressed:size decompress ratio is suspicious, or which include files larger than policy).
- Monitor:
- Set alerts for OOM kills, Helm process crashes, or unusual memory usage during chart operations.
Final analysis and guidance
Microsoft’s statement that Azure Linux includes the open‑source library is authoritative for Azure Linux and should be treated as actionable guidance: patch Azure Linux packages, ensure Cloud Shell and any managed Azure Linux images you control are updated, and apply the Helm v3.17.3 (or newer) fix where possible. But that sentence is not an exhaustive warranty about the presence (or absence) of the same upstream code in other Microsoft artifacts. Software reuse and packaging mean the same vulnerable code can appear in multiple different artifacts and products unless every artifact is inventoried and attested.Operationally, the fastest way for most organizations to reduce exposure to CVE‑2025‑32386 is:
- Patch Helm to v3.17.3+ everywhere you run it.
- Add resource limits and pre‑ingest chart checks in CI/CD and chart repositories.
- Maintain SBOMs and scan images for embedded helm binaries or libraries while waiting for vendors’ machine‑readable VEX attestations to cover all products you consume.
Conclusion
CVE‑2025‑32386 is a realistic availability threat for any environment that unpacks or validates Helm charts without limits. Helm’s upstream fix (v3.17.3) adopts a pragmatic, safer default by enforcing decompressed‑size limits, but the operational reality — broken charts, lagging upgrades, and multiple places Helm appears in modern cloud workflows — means defenders must act on multiple fronts: patch, inventory, harden ingestion, apply resource constraints, and rely on SBOMs while vendor attestations continue to roll out. Microsoft’s explicit attestation that Azure Linux includes the library is valuable and should spur immediate action for that product, but it is not an assurance that the rest of Microsoft’s product catalog is unaffected; customers must treat each artifact the same way and verify or patch accordingly.
Source: MSRC Security Update Guide - Microsoft Security Response Center