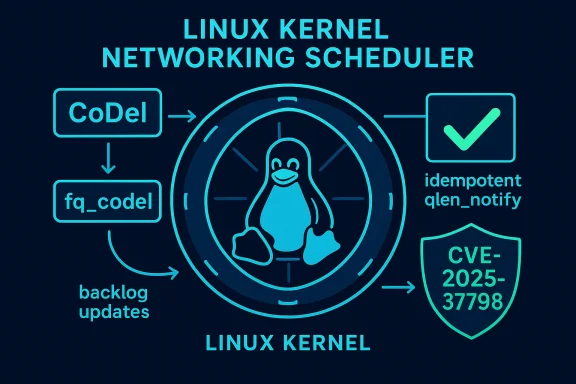
The Linux kernel networking scheduler received a surgical but consequential change that was recorded as CVE‑2025‑37798: maintainers removed the historical check of sch->q.qlen (the qdisc’s queue length) before calling qdisc_tree_reduce_backlog(), after first making all qlen_notify() callbacks idempotent—an apparently small code simplification that carries outsized operational impact for system administrators and cloud operators who run affected kernels.
The Linux traffic control (tc) subsystem implements multiple queueing disciplines (qdiscs) such as CoDel (Controlled Delay) and fq_codel (Fair Queueing + CoDel). These qdiscs are responsible for packet scheduling and accounting, including maintaining per-queue backlog counts and notifying parent qdiscs when child queues transition to empty. Historically, the code guarded calls to qdisc_tree_reduce_backlog() with a check of sch->q.qlen != 0 to avoid redundant or problematic qlen_notify() invocations. That guard has now been removed because the qlen_notify() handlers were rewritten to be idempotent—safe to call multiple times without causing incorrect state transitions.
The change was packaged into the Linux stable tree and referenced by multiple vendor advisories and trackers as CVE‑2025‑37798. Distributors subsequently released kernel updates or backports that incorporate the fix; vendors listing affected or fixed packages include Debian, Ubuntu, Oracle Linux, Amazon Linux (ALAS), SUSE, and others. The public vulnerability entries emphasize the local‑attack, availability impact: a local unprivileged actor with the ability to interact with traffic control APIs or inject specially crafted qdisc/class operations could trigger conditions that lead to service disruption (High availability impact).
For operators, the conclusion is simple and uncompromising: treat this as an availability bug you should patch. Ensure your inventories are complete, apply vendor kernel updates promptly, and harden access to traffic control operations in multi-tenant contexts. The patch itself reduces future fragility, but the operational reality is that until every affected host is updated, the environment remains at measurable risk.
By focusing on sound patching practices, monitoring for kernel oopses, and narrowing access to qdisc manipulation APIs, administrators can eliminate the attack surface this class of bug exploits and restore reliable, predictable behavior in the Linux traffic control stack.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
The Linux traffic control (tc) subsystem implements multiple queueing disciplines (qdiscs) such as CoDel (Controlled Delay) and fq_codel (Fair Queueing + CoDel). These qdiscs are responsible for packet scheduling and accounting, including maintaining per-queue backlog counts and notifying parent qdiscs when child queues transition to empty. Historically, the code guarded calls to qdisc_tree_reduce_backlog() with a check of sch->q.qlen != 0 to avoid redundant or problematic qlen_notify() invocations. That guard has now been removed because the qlen_notify() handlers were rewritten to be idempotent—safe to call multiple times without causing incorrect state transitions.The change was packaged into the Linux stable tree and referenced by multiple vendor advisories and trackers as CVE‑2025‑37798. Distributors subsequently released kernel updates or backports that incorporate the fix; vendors listing affected or fixed packages include Debian, Ubuntu, Oracle Linux, Amazon Linux (ALAS), SUSE, and others. The public vulnerability entries emphasize the local‑attack, availability impact: a local unprivileged actor with the ability to interact with traffic control APIs or inject specially crafted qdisc/class operations could trigger conditions that lead to service disruption (High availability impact).
What changed, in plain technical terms
The old behavior: a defensive qlen check
Prior to the change, code paths in scheduling modules such as fq_codel_dequeue() and codel_qdisc_dequeue() checked the qdisc’s queue length (sch->q.qlen) before calling the tree-level accounting helper qdisc_tree_reduce_backlog(). The intent was simple: avoid invoking parent‑notification logic when the child qdisc still had packets, thereby preventing duplicate notifications and preventing subtle races or incorrect bookkeeping in some classful qdisc implementations (notably DRR and others that relied on qlen_notify to maintain active lists). This defensive pattern prevented a class from being reported empty multiple times accidentally.The new behavior: idempotent qlen_notify() + removed guard
Kernel developers made a series of changes to ensure every qlen_notify() callback is idempotent—that is, calling it multiple times in the same state does not change correctness. Once callbacks were made safe against repeated invocations, the earlier guard check (qlen != 0) became unnecessary and was removed. Removing the conditional simplifies the code path and ensures qdisc_tree_reduce_backlog() always executes when it should, removing a class of subtle ordering bugs that depended on the prior guard to avoid missed notifications during qdisc deletion or reset. The net effect is that parent backlog counters and classful qdisc bookkeeping get consistent updates across all qdisc types even in corner cases.Why this is recorded as a CVE (and what “fixed” means here)
At first glance, removing a redundant check looks like a code-cleanup. In kernel CVE practice, however, the entry often documents the exact change that fixed a prior correctness or safety problem—or that required prior changes elsewhere to make safe. In this case, the vulnerability narrative is tied to the interaction between qlen_notify semantics and when qdisc_tree_reduce_backlog() is invoked:- If qlen_notify callbacks were not idempotent, then repeated notifications or notifications at unexpected times could lead to incorrect internal lists (for example, DRR’s active list), causing use‑after‑free, NULL dereference, or other kernel OOPSes resulting in availability loss.
- Making qlen_notify idempotent removed that class of fragility, allowing the removal of a prior guard that had been compensating for non‑idempotent handlers. The commit series thus both fixed the root cause (non‑idempotent handlers) and consolidated behavior by removing the guard.
Technical analysis: where things can go wrong (attack and failure scenarios)
Below are realistic scenarios and root causes that make this issue operationally significant.- Race conditions during qdisc deletion or reset: When qdiscs or classes are removed, internal code paths reset qlen to zero. If qdisc_tree_reduce_backlog() is invoked at the wrong time, parents may not be notified of a child becoming empty, or may be notified multiple times, leaving parent bookkeeping inconsistent. This can corrupt dependent structures (e.g., DRR’s active list), creating crashes or hangs. The idempotency changes aim to make duplicate notifications harmless, but the transitional window before all code paths were updated left potential for instability.
- Dependency on qlen_notify side effects: Some qdisc implementations relied on qlen_notify() not being called redundantly to maintain auxiliary lists. Repeated or out‑of‑order calls could cause the same element to be enqueued multiple times, removed wrongly, or referenced after free—classic use‑after‑free and double‑free patterns at kernel level. Because these are memory‑safety issues inside the kernel, the resulting symptom is often a kernel panic or oops—i.e., a denial‑of‑service for the host.
- Local attacker model: Exploitation is generally local—the attacker must have the ability to create or manipulate traffic control settings (via privileged or unprivileged APIs where allowed), or to craft packet flows that stress specific qdisc code paths. In multi‑tenant or containerized environments, a low‑privilege tenant may still exercise these APIs (or exploit a misconfiguration) to impact the host’s network stack, making the issue relevant to cloud providers and shared infrastructure. Several vendor trackers therefore flagged the availability impact as high while keeping confidentiality and integrity impacts as low or none.
Affected versions and vendor guidance
Multiple trackers collate the kernel commits and identify affected stable kernel versions. The vulnerable range and backport status vary by distributor; typical guidance is to upgrade to the vendor-supplied kernel update that includes the stable patch.- Ubuntu lists the CVE and indicates which distro kernels contain the fix in their respective release series. Administrators should follow Ubuntu’s security notices and apply the kernel updates flagged as fixed.
- Amazon Linux (ALAS) and SUSE published advisories and errata referencing the fix; Amazon and SUSE also provide package identifiers and updated kernel package versions for their distributions.
- Debian’s security tracker and the upstream OSV/NVD entries list the CVE and reference the kernel commits and Debian LTS advisories.
Detection and mitigation strategies for administrators
Operational defenders should treat CVE‑2025‑37798 as an availability‑focused risk and apply layered mitigation and detection:- Immediate detection signals
- Monitor kernel logs for qdisc, DRR, or CoDel related oopses, stack traces, or WARN_ON messages. Kernel oops text often includes file/line or function names such as qdisc_tree_reduce_backlog, codel_qdisc_dequeue, or fq_codel_dequeue.
- Watch for increased unexplained kernel panics or network interface instability on hosts that run containerized workloads or allow unprivileged netlink operations from tenants.
- Use host integrity SCOM/EDR/Nessus/Nessus‑plugin checks to match installed kernel versions against vendor advisories (many scanners already include plugins for this CVE).
- Hardening mitigations (short term)
- Apply vendor kernel updates as the primary mitigation. This is the only reliable remediation.
- Where immediate kernel upgrades are impossible, limit access to traffic control APIs: restrict unprivileged netlink and tc operations, and enforce strong container runtime policies prohibiting privileged networking operations.
- For multi‑tenant hosts, isolate network namespaces and avoid exposing host qdisc manipulation interfaces to untrusted tenants.
- Consider rate‑limiting and control plane filters to prevent tenants from submitting rapid, malformed qdisc/class creation sequences that could trigger problematic state transitions.
- Patching roadmap
- Prioritize patching hosts that carry high-density container workloads, network functions (NFVs), or any system that processes untrusted packet streams (edge routers, middleboxes).
- Validate fix by booting into the patched kernel in a staging environment and running established traffic-control test suites or stress tests that exercise CoDel/fq_codel and classful queueing scenarios. ([suse.comm/security/cve/CVE-2025-37798.html)
Why this matters to WindowsForum readers and Windows-centric operations
Even though the vulnerability lives in Linux kernel net_sched, Windows‑centric organizations must care because:- Windows servers interact with Linux platforms in hybrid cloud and edge deployments; availability incidents on Linux hosts (e.g., routers, virtual network appliances, directly impact cross‑platform services that Windows servers rely on.
- Cloud providers that supply images or managed services (Azure Linux, Amazon Linux) are mentioned specifically in advisories; organizations relying on those vendor kernels should follow their guidance. Public attestation patterns—where a vendor declares that a specific product image includes an upstream component—are commonly used to scope risk for large cloud artifacts. Our internal tracking of vendor attestation patterns demonstrates this operational nuance and the importance of verifying per‑artifact exposure rather than assuming exclusivity.
- Security scanners and asset inventories must be updated to detect vulnerable kernel versions; this prevents blind spots where Windows administrators might continue to trust networked Linux appliances without realizing they’re running an affected kernel. Recent activity on Linux kernel CVE reporting highlights the volume of small, high‑impact fixes and the need for integrated patch pipelines.
Strengths and risks of the upstream fix: a critical appraisal
Notable strengths
- The kernel developers addressed the root cause—non‑idempotent qlen_notify handlers—rather than masking the symptom. Making callbacks idempotent is the safer, more maintainable approach in the long run and reduces future fragility.
- The removal of the qlen guard simplifies the dequeue code paths, reducing the surface for future bugs and making qdisc tree bookkeeping more consistent across code paths.
- Vendors reacted quickly with advisories and backports for their kernel trees, demonstrating a mature response chain for a kernel-level availability issue.
Potential risks and residual concerns
- Transitional window: there is an implicit dependency ordering—maintainers first had to make every qlen_notify idempotent in every classful qdisc type. If any distribution or backport accidentally missed a corner-case or older qdisc module, calling qdisc_tree_reduce_backlog() without the guard could still surface buggy behavior on those kernels.
- Local attack vector: the vulnerability’s exploitation model is local but realistic in multi‑tenant and containerized environments; misconfigured or malicious tenants can trigger kernel instability from within normal API boundaries.
- Diverse CVSS assessments: different vendors assigned different severity scores (some Medium, some High). That inconsistency forces organizations to make risk decisions based on their exposure model—particularly cloud providers and shared‑hosting operators who must assume a worst‑case availability impact.
Practical checklist for system operators (what to do now)
- Inventory: Identify all Linux hosts and kernel versions in your environment. Flag kernels whose package versions predate the vendor advisories for CVE‑2025‑37798.
- Prioritize: Push updates to:
- Network appliances, routers, edge devices, and hosts running network functions.
- Kubernetes nodes, container hosts, and any multi‑tenant systems.
- Cloud provider images (verify whether the managed image was updated and whether you need to roll instances).
- Patch: Apply vendor kernel updates or backports as published in your distro security advisories; schedule reboots if required.
- Harden: Restrict unprivileged netlink/tc operations and enforce namespace isolation for tenants. Use LSM/AppArmor/SELinux to restrict unexpected manipulation of network qdiscs where possible.
- Monitor: Add kernel oops/trace alerts for qdisc, CoDel, and DRR symbols, and correlate with network instability and container events.
- Test: In staging, run traffic-control stress tests that exercise class creation, deletion, and extreme packet rate conditions to validate mitigations.
Final assessment and outlook
CVE‑2025‑37798 is a textbook example of how seemingly small internal invariants in low‑level kernel code can cascade into availability hazards for modern infrastructure. The fix—making qlen_notify() idempotent and removing an old defensive check—is correct from a software engineering perspective, and it cleans up a brittle interaction between qdisc bookkeeping and tree-level backlog reduction. At the same time, the timing and breadth of that change required careful coordination and vendor backports; the practical risk to operators during the transition justified public CVE tracking and vendor advisories.For operators, the conclusion is simple and uncompromising: treat this as an availability bug you should patch. Ensure your inventories are complete, apply vendor kernel updates promptly, and harden access to traffic control operations in multi-tenant contexts. The patch itself reduces future fragility, but the operational reality is that until every affected host is updated, the environment remains at measurable risk.
By focusing on sound patching practices, monitoring for kernel oopses, and narrowing access to qdisc manipulation APIs, administrators can eliminate the attack surface this class of bug exploits and restore reliable, predictable behavior in the Linux traffic control stack.
Source: MSRC Security Update Guide - Microsoft Security Response Center