Microsoft’s brief advisory — “Azure Linux includes this open‑source library and is therefore potentially affected” — is accurate for the inventory Microsoft has completed, but it is not a technical guarantee that no other Microsoft product could contain the same vulnerable CIFS code. ]
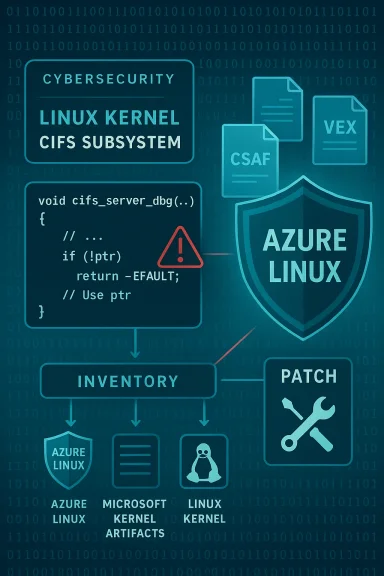
CVE‑2025‑37844 is a Linux‑kernel vulnerability in the CIFS subsystem: a NULL pointer dereference in the cifs_server_dbg() call that assumes the server pointer is non‑NULL. The fix moved the dbg call under a conditional so the function is only invoked when the server pointer is present. This is a robustness/availability bug that can cause a kernel oops or host crash when the code path is exercised.
The vulnerability was reported by the Linux Verification Center (using SVACE) and assigned by the Linux kernel CVE team. Multiple downstream vendors and distributions quickly mapped the upstream fix into their kernel packages and advisories. The issue carries a CVSS v3.1 base score commonly reported as 5.5 (local, low‑privilege, availability impact) in vendor trackers.
This article explains the technical nature of the bug, summarizes how Microsoft has described its product exposure, examines whether Azure Linux is the only Microsoft product that could be affected, and provides practical guidance for administrators and security teams who need to inventory, mitigate, and verify exposure across Microsoft‑delivered artifacts.
A NULL pointer dereference occurs when the code calls cifs_server_dbg() without checking whether the server pointer is NULL. In kernel space a dereference of NULL generally triggers an oops or panic — an availability issue, not a direct code‑execution vector. Attackers with local access (or misbehaving in‑kernel triggers) can cause a denial‑of‑service by forcing that code path.
The exploitability is limited: an attacker typically needs local access or to trigger kernel code paths that lead to the debug call. That said, in multi‑tenant cloud environments or shared platforms, local access can be available to untrusted actors (for example, in container escape scenarios or misconfigured multi‑tenant services), so the local vector is not trivial in those environments.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CVE‑2025‑37844 is a Linux‑kernel vulnerability in the CIFS subsystem: a NULL pointer dereference in the cifs_server_dbg() call that assumes the server pointer is non‑NULL. The fix moved the dbg call under a conditional so the function is only invoked when the server pointer is present. This is a robustness/availability bug that can cause a kernel oops or host crash when the code path is exercised.The vulnerability was reported by the Linux Verification Center (using SVACE) and assigned by the Linux kernel CVE team. Multiple downstream vendors and distributions quickly mapped the upstream fix into their kernel packages and advisories. The issue carries a CVSS v3.1 base score commonly reported as 5.5 (local, low‑privilege, availability impact) in vendor trackers.
This article explains the technical nature of the bug, summarizes how Microsoft has described its product exposure, examines whether Azure Linux is the only Microsoft product that could be affected, and provides practical guidance for administrators and security teams who need to inventory, mitigate, and verify exposure across Microsoft‑delivered artifacts.
The technical problem: what the code does and why the bug matters
CIFS, debug calls, and NULL pointer dereferences
CIFS (Common Internet File System) is the in‑kernel client and server code for SMB/CIFS functionality. Inside the CIFS server/client code there are debug helpers that log or export state to tracepoints and debugfs. The cifs_server_dbg() function is a debug helper that expects to be called with a valid server object reference.A NULL pointer dereference occurs when the code calls cifs_server_dbg() without checking whether the server pointer is NULL. In kernel space a dereference of NULL generally triggers an oops or panic — an availability issue, not a direct code‑execution vector. Attackers with local access (or misbehaving in‑kernel triggers) can cause a denial‑of‑service by forcing that code path.
Why upstream changed the call site
Upstream maintainers fixed the problem by moving the dbg call under a guard that verifies the server object exists before calling server->ops or any function that dereferences the pointer. This is a standard defensive pattern in kernel development: validate pointers before use, because many driver and filesystem helpers can be invoked in error paths or under shutdown sequences where the expected object has already been freed or not yet initialized. The kernel‑announce and downstream advisories list the fixed commits and the affected commit range (introduced in 5.7; fixed in stable kernels such as 5.10.237 and equivalent backports).Who published what: vendor responses and timelines
- The Linux kernel CVE announcement (linux‑cve‑announce) published the CVE description and the affected/fixed versions and commits.
- Distribution and vendor advisories followed: SUSE, Debian, Amazon Linux, Red Hat trackers and others recorded the CVE and listed fixed package versions or backpo advisories confirm the fix was picked up across major kernels and backported into distribution maintenance streams.
- Microsoft’s Security Response Center (MSRC) published a product‑scoped mapping that reads: “Azure Linux includes this open‑source library and is therefore potenis vulnerability” and announced Microsoft is publishing machine‑readable CSAF/VEX attestations (with a rollout that began in October 2025), promising to update CVE mappings if additional Microsoft products are identified as affected. That MSRC phrasing is the basis for the customer question this article answers.
Is Azure Linux the only Microsoft product that includes the library?
Short answer: No — but with an important qualifier.- Strictly speaking, Microsoft has publicly attested only Azure Linux as containing the implicated upstream component so far. That attestation is authoritative for Azure Linux images and kernels that Microsoft inspected and mapped.
- Technically, however, the vulnerable CIFS code lives in upstream Linux kernel source. Any Microsoft product or artifact that ships a Linux kernel build containing the same upstream commit range and kernel configuration could carry the same code and therefore be potentially affected. That means other Microsoft artifacts that include kernels — for example WSL2 kernel builds, Azure VM image kernels, or bespoke kernel packages used by other Azure services — could be affected until they are inventoried and declared either Not Affected or Fixed.
Practical examples of other Microsoft artifacts you should consider
If you are asking whether only Azure Linux images need attention, be aware that Microsoft maintains and publishes multiple kernel artifacts. Consider these as potential carriers until proven otherwise:- Windows Subsystem for Linux (WSL / WSL2) kernels Microsoft builds and publishes are compiled from upstream sources and can include a broad set of drivers depending on configuration. A WSL kernel built from a pre‑fix fix commit range could include the vulnerable CIFS code.
- Azure VM images and tuned kernels (the linux‑azure or azl3 kernel families) are Microsoft‑owned artifacts: Azure Linux is the first target for VEX attestations, but other Azure marketplace images or specialized kernels used by platform services may still require inventory checks.
- Microsoft containers or appliance images that embed a Linux kernel or kernel modules could also be carriers if they include a kernel binary or modules compiled from an affected commit. This is less common but feasible in specialized service stacks.
What to do now: verification, mitigation, and remediation checklist
Below is a practical, prioritized checklist for security teams and administrators responsible for Microsoft‑delivered artifacts or systems running on Microsoft infrastructure.1. For Azure Linux customers (immediate)
- Apply the vendor‑backported kernel or the distribution update Microsoft published for the Azure Linux image as soon as it’s available. Azure Linux customers should treat the MSRC statement as actionable.
- Reboot hosts when kernel updates are installed, because this is a kernel robustness fix. Plan short maintenance windows where necessary.
2. Inventory Microsoft artifacts you consume
- Identify any Microsoft artifacts you run that include Linux kernels: WSL2 instances provided by Microsoft updates, Azure Marketplace images, custom images built from Microsoft base images, platform kernels used by managed services.
- For each artifact, determine the kernel version and, if possible, the exact commit range. Compare against upstream commit information and the fixed commit noted in the kernel CVE announcement. The linux‑cve‑announce and vendor trackers list the commit ranges that introduced and fixed the problem.
3. How to check a kernel build for the vulnerable code (technical verification)
- If you can run commands on the host, check the kernel version and compile‑time information:
- uname -a
- zcat /proc/config.gz | grep -E 'CIFS|CONFIG_CIFS'
- If youce archive or the build tree used to produce the kernel, search for the affected function and the commit ID range referenced by the upstream announcement (the commit hashes are provided in the linux‑cve‑announce and OSV entries). If the build includes the pre‑fix commit, it may be vulnerable.
4. Mitigations when immediate patching is not possible
- Apply host‑level mitigations: if your threat model allows, avoid mounting or exposing CIFS server debug interfaces to local untrusted users. The attack surface for this particular bug is largely local, so reducing local user privileges and hardening container host separation helps.
- For cloud images, use image rotation: replace an image with a patched image and redeploy, then retire older instances. Automation that updates kernel images in your pipeline is the long‑term fix.
5. Validation and attestation
- Where Microsoft publishes CSAF/VEX machine‑readable attestations for an artifact, consume those artifacts programmatically. Microsoft has said it began publishing CSAF/VEX attestations in October 2025 and will extend them beytime; treat published VEX results as authoritative for the artifact they describe.
- For artifacts without a Microsoft attestation, perform local artifact verification (kernel checksums, build provenance) or ask your Microsoft support contacts for an inventory mapping.
Risk analysis and threat model: how worried should you be?
Severity and exploitability
CVE‑2025‑37844 is a robustness/availability vulnerability (NULL pointer dereference). The CVSS v3.1 score reported by multiple trackers is 5.5 (Medium), with a local attack vector and availability impact. The flaw does not appear to be an arbitrary code execution primitive; it’s a denial‑of‑service risk when the offending dbg call is executed on a vulnerable build.The exploitability is limited: an attacker typically needs local access or to trigger kernel code paths that lead to the debug call. That said, in multi‑tenant cloud environments or shared platforms, local access can be available to untrusted actors (for example, in container escape scenarios or misconfigured multi‑tenant services), so the local vector is not trivial in those environments.
Likely impact on Microsoft customers
- Azure Linux users: high priority to patch. Azure Linux is explicitly attested to include the affected component, so remediation is a clear, immediate action for those customers.
- WSL2 and other Microsoft kernel consumers: medium priority to inventory. Whether these artifacts are affected depends on the kernel version and configuration. WSL kernels are published and may use different upstream commit ranges. Until Microsoft or you confirm, treat them as potentially affected and verify.
- Windows client or server customers that do not run Linux kernels directly are not impacted by a Linux kernel CIFS NULL dereference — unless they run WSL2, Azure images, or other Microsoft artifacts that embed Linux. Always map your usage before concluding impact.
Supply‑chain and programmatic attestation implications
Microsoft’s rollout of CSAF/VEX attestations is a step toward deterministic supply‑chain transparency: customers can programmatically determine which Microsoft artifacts are Known Affected, Not Affected, Under Investigation, or Fixed. The MSRC language that started this practice is deliberately scoped — beginning with Azure Linux — and Microsoft has promised to expand it. The practical consequence for defenders is this: use the VEX output where available, but do not treat non‑attested artifacts as proven safe.Why Microsoft might name Azure Linux first (operational reasoning)
There are several practical reasons Microsoft began with Azure Linux when publishing these attestations:- Azure Linux is a single product family with a finite, controllable set of artifacts (kernel builds, images) that Microsoft owns end‑to‑end, making inventory and reproduction tractable. Starting there yields quick wins for customers.
- WSL kernels, Azure kernel images, and other artifacts are more numerous and sometimes built from different upstream commit ranges or with different CONFIG_* choices, requiring more time to inventory. Microsoft chose a pragmatic rollout rather than attempt to retroactively map every possible artifact in one pass.
How to demand and verify transparency from vendors (advice for customers)
- Require machine‑readable attestations (CSAF/VEX) as part of procurement and supplier security programs. VEX data lets you automate checks and integrate supplier attestations into your vulnerability management systems.
- Ask vendors for artifact provenance: ask for the exact kernel version, commit hash, and kernel configuration used to build a published kernel. Provenance short‑circuits ambiguity.
- Establish a routine to check vendor VEX/reference them with upstream CVE announcements and distribution advisories. Combining authoritative upstream commit data (linux‑cve‑announce) with vendor attestations and downstream distro advisories gives you a complete picture.
What we verified for this article
- The CVE description and upstream fixes were validated against the linux‑cve‑announce posting that documents the issue, the commit ranges that introduced and fixed the defect, and the attribution to the Linux Verification Center.
- Multiple distribution and vendor trackers (SUSE, Debian, Amazon Linux, Red Hat trackers) list the same CVE and describe the impact and fix status; these confirm the issue was patched and backported in downstream kernels.
- Microsoft’s public MSRC phrasing about Azure Linux was referenced in Microsoft’s Security Update Guide mapping and in subsequent community analysis that explains the scope/limits of that attestation; those community analyses align on the interpretation that the attestation is product‑scoped, not an exclusivity assertion.
Final recommendations (concise)
- Patch Azure Linux images immediately if you run them — Microsoft attested Azure Linux includes the implicated component.
- Inventory other Microsoft‑supplied artifacts (WSL kernels, Azure images) and verify kernel versions / commits; assume potential exposure until confirmed Not Affected.
- Use CSAF/VEX feeds where available to automate artifact‑level decisions, and incorporate upstream commit checks for kernel CVEs into your automation.
- Harden host local access and isolation policies to reduce the risk posed by local‑vector availability bugs, and apply standard least‑privilege controls on multi‑tenant systems.
Conclusion
Microsoft’s MSRC message that “Azure Linux includes this open‑source library and is therefore potentially affected” is a precise, product‑scoped attestation: it tells Azure Linux customers they should treat their images as in‑scope and update accordingly. However, that statement does not — and logically cannot — prove that no other Microsoft product includes the same upstream CIFS code. The vulnerable code lives in upstream Linux; any Microsoft artifact that ships a kernel build from the pre‑fix commit range and with the CIFS component enabled could carry the flaw until it is inventoried and remediated. Administrators should therefore treat the MSRC attestation as a clear signal to act for Azure Linux, and should also inventory and verify any other Microsoft artifacts they consume (WSL, Azure VM images, platform kernels) until Microsoft’s CSAF/VEX attestations or local verification prove otherwise.Source: MSRC Security Update Guide - Microsoft Security Response Center