The Linux kernel patch tracked as CVE-2025-37860 fixes a small but consequential ordering and defensive‑coding error in the Solarflare/ef100
The vulnerability was disclosed as CVE‑2025‑37860 in April 2025 and has been indexed across mainstream trackers and distribution advisories. The public technical summary is concise: because
Action checklist (practical, ordered):
Organizations should prioritize: (1) inventorying hosts and vendor images running the ef100/Solarflare driver, (2) applying distribution or vendor kernel updates that include the upstream stable commit, and (3) hardening multi‑tenant or long‑lived embedded fleets where vendor backport cycles may be slow. Ongoing monitoring for kernel oops traces and careful coordination with OEM vendors remain essential to close the long tail of exposure.
Source: MSRC Security Update Guide - Microsoft Security Response Center
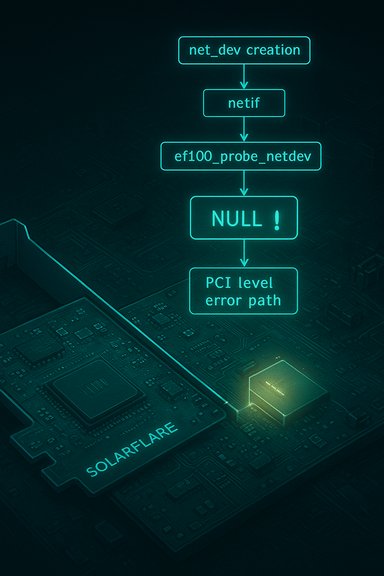
sfc driver: ef100_process_design[I]param could dereference netif pointers before the network device had been created, producing kernel NULL pointer dereferences and an availability‑impacting crash. The upstream remedy moves certain netif[/I]* calls into ef100_probe_netdev and replaces netif_err usage with pci_err inside the design‑parameter parsing path, eliminating the premature dereference and turning an unpredictable crash into a deterministic, recoverable failure path.
 Background / Overview
Background / Overview
The vulnerability was disclosed as CVE‑2025‑37860 in April 2025 and has been indexed across mainstream trackers and distribution advisories. The public technical summary is concise: because ef100_probe_main (and by extension ef100_check_design_params) now runs before efx->net_dev exists, calling netif_set_tso_max_size or netif_set_max[I]segs at that point is unsafe. The patch reorganizes probe sequencing so those netif invocations only occur when the network device has actually been created, and it replaces logging that assumed a netdev context with PCI‑level logging to reflect the correct probe stage. This is a classic kernel [/I]robustness* fix: a missing ordering/NULL‑check leads to a kernel NULL dereference (CWE‑476) that results in an oops/panic or an unstable subsystem. In kernel space, those consequences are more severe than a userland segfault because they can crash the entire host or require manual recovery, raising the operational priority even when confidentiality or integrity are not at risk. Community analysis of similar kernel defects repeatedly emphasizes this availability-first impact and the small, surgical nature of the correct patch.Technical anatomy: what went wrong
The code path and the mistaken assumption
At the heart of CVE‑2025‑37860 is a call ordering assumption introduced during probe sequencing:ef100_probe_main performs topology and design‑parameter checks (ef100_check_design_params) before the network device structure efx->net_dev is allocated and initialized. Within the design‑param path, code attempted to call netif_set_tso_max[I]size / related netif helpers and logged errors using netif_err. Those operations assume a valid struct net_device [/I] (netdev) and thus are unsafe before efx->net_dev exists. If efx->net_dev is NULL, invoking those helpers or dereferencing fields leads straight to a kernel NULL pointer dereference and an oops. The upstream patch removes that hazard by moving the netif calls into ef100_probe_netdev (the stage that runs after netdev creation) and by converting logging to pci_err where a netdev context is not yet available. Why a small reorder fixes a huge class of failures
Kernel drivers often perform multi‑stage initialization: early probe checks, resource allocations, netdev creation, and final device registration. A single step executed too soon — or a small log helper that assumes a target object exists — can touch address zero in kernel mode. The fix here is intentionally surgical:- Delay
netif_*calls until the net device exists (move intoef100_probe_netdev). - Replace
netif_errwithpci_errin code that runs before netdev allocation. - Avoid dereferencing
efx->net_devuntil it is guaranteed to be valid.
Affected systems, versions and exposure
Multiple vendors and distribution trackers list the CVE and map it to kernel commit ranges. Public vulnerability feeds indicate the defect affects Linux kernel sources that include the affectedsfc/ef100 probe ordering prior to the stable commit that implements the change; distribution package status varies by series and vendor. For example, Ubuntu lists the CVSS v3.1 base score as 5.5 (Medium) and provides package mapping and status for specific releases; Debian’s tracker shows which branches are fixed versus still vulnerable in their package sets. OSV and SUSE also index the issue and list the stable commits referenced by the CVE metadata. Practical exposure considerations:- Desktop/workstation hosts running kernels with the
sfc(Solarflare) ef100 driver compiled in and where users or local workloads can interact with the NIC stack are candidates for impact. - Multi‑tenant systems, CI runners, container hosts, and GPU/accelerator hosts that expose NIC device nodes or load the ef100 driver for passthrough are higher priority because a local unprivileged process may be able to trigger probe/teardown flows.
- Embedded appliances, vendor images (OEM kernels), and appliances that ship a vendor forked kernel are often the long tail of risk because those vendors may lag in applying upstream stable commits or backports.
Detection and telemetry: what to look for
Kernel NULL dereference events are noisy and leave distinct artifacts. Operationally, monitor the following:- Kernel oops/panic traces in
dmesgorjournalctl -kthat include phrases like “NULL pointer dereference” and stack frames referencingef100*,sfc, or Solarflare driver symbols. - Repeated driver probe failures during boot or when hot‑plugging devices; messages indicating a failure in
ef100_probe_mainoref100_check_design_params. - Unexpected host reboots, watchdog‑initiated restarts, or net subsystem failures correlated to NIC attach/detach events.
- SIEM/EDR alerts for rapid, repeated kernel warnings or automated orchestration actions triggered by kernel instability.
- journalctl -k | egrep -i 'ef100|sfc|NULL pointer dereference|BUG:'
- dmesg | egrep -i 'ef100|sfc|netif_set_tso_max_size|netif_set_max_segs'
Remediation and operational guidance
The single correct remediation is to run a kernel that contains the upstream stable commit(s) which implement the probe reorder and defensive logging change.Action checklist (practical, ordered):
- Inventory:
- Enumerate hosts that run kernels with Solarflare/ef100 (
sfc) support enabled. Uselsmod,modinfo sfc, andgrepover/proc/config.gzor/boot/config-*to detect driver presence. - Map:
- Cross‑reference your kernel package version against distribution security advisories (Debian, Ubuntu, SUSE, Amazon Linux, vendor advisories) to determine whether your installed package contains the upstream commit that fixes CVE‑2025‑37860.
- Patch:
- Apply vendor/distribution kernel updates that include the upstream stable commit. Reboot hosts into the patched kernel.
- Validate:
- After patching, exercise device attach/detach and probe flows on representative hardware and verify kernel logs are free of the previous oops stack traces.
- Compensate (if you cannot patch immediately):
- Restrict untrusted local code execution on exposed hosts (application allow‑listing, remove unnecessary local shells).
- Isolate hosts that present network interfaces directly to unprivileged workloads.
- Temporarily disable automatic device probing for ef100 if the vendor provides safe configuration knobs (rare; vendor guidance required).
- Vendor escalation:
- For appliances and vendor images (OEMs, embedded devices), require the vendor to provide a backported image or a mitigated kernel; escalate if the vendor’s timeline is unclear.
Risk analysis — strengths and residual dangers
Strengths of the upstream response- The upstream patch is small, surgical, and low risk — a simple probe reorder and a logging change. That makes it easy to accept into stable kernel trees and to backport into distribution kernels, accelerating remediation cadence.
- The technical root cause is well understood (ordering/assumption about
efx->net_devlifecycle), so verification is straightforward: either the netdev exists at the call site or it does not.
- Vendor/OEM lag remains the primary operational danger. Devices with vendor‑supplied kernels, appliance firmware, or long‑lived embedded images are likely to remain vulnerable longer than distribution packages. These long‑tail systems often host critical functions and should be inventoried and tracked.
- Kernel oopses can be leveraged in complex multi‑stage attacks as a reliability or availability disruption technique; while this CVE is not an RCE vector by default, adversaries can still leverage DoS for distraction, forced failover, or to shape an attack surface. Do not extrapolate availability impact into automatic code‑execution claims without a verified PoC.
- Automated vulnerability scanners sometimes flag the presence of a CVE without correctly mapping vendor backport versions. Always confirm package changelogs and commit IDs in vendor advisories rather than relying solely on CVE presence.
Developer and maintainer takeaways
Theef100 fix is instructive for driver authors and maintainers.- Always validate object lifecycles before calling functions that assume their existence. In multi‑stage probe sequences, annotate which helpers require
net_devvs which can run earlier. - Prefer context‑appropriate logging helpers: use
pci_error similar when netdev context is not present. Logging that itself dereferences a now‑missing resource is a surprisingly common source of null dereferences. - Keep probe and device registration semantics explicit: if a check depends on a later stage, either delay it or fail fast with a clear error.
- Small changes that convert undefined behavior into explicit error returns dramatically reduce operational risk and are typically easier to backport and accept into stable trees.
Recommended operational playbook (one page of actions)
- Inventory: find kernels with
sfc/Solarflare ef100. - Commands: modinfo sfc; grep -i sfc /lib/modules/$(uname -r)/modules.dep; check kernel config for
CONFIG_SFC=y. - Map: consult distribution advisories (Ubuntu, Debian, SUSE, Amazon Linux) for CVE‑2025‑37860 mapping.
- Patch: apply vendor/distribution kernel updates that include the fix; schedule reboots.
- Verify: run device attach/detach tests and check
dmesgfor any residualef100oops traces. - Compensate: isolate critical hosts from untrusted tenants; apply application allow‑listing on engineering or multi‑tenant systems until patched.
- Track: maintain a list of vendor/OEM images and follow up for patched images; escalate where no vendor timeline exists.
Conclusion
CVE‑2025‑37860 is not a dramatic new exploit class — it’s a textbook kernel robustness defect that demonstrates how tiny ordering mistakes translate to real operational consequences. The good news is the solution is equally simple: movenetif calls to the proper probe stage and avoid dereferencing netdev before it exists. That surgical patch converts a crash into a controlled error and should be rapidly applied where the sfc ef100 driver is present.Organizations should prioritize: (1) inventorying hosts and vendor images running the ef100/Solarflare driver, (2) applying distribution or vendor kernel updates that include the upstream stable commit, and (3) hardening multi‑tenant or long‑lived embedded fleets where vendor backport cycles may be slow. Ongoing monitoring for kernel oops traces and careful coordination with OEM vendors remain essential to close the long tail of exposure.
Source: MSRC Security Update Guide - Microsoft Security Response Center