The short answer is: No — Azure Linux is the only Microsoft product Microsoft has publicly attested, so far, to include the upstream VMCI code linked to CVE‑2025‑38102, but that attestation is product‑scoped and not an exclusivity guarantee. Microsoft’s MSRC inventory statement is authoritative for Azure Linux images that the company inspected, but any Microsoft artifact that ships a Linux kernel build containing the same upstream code (and the same build-time configuration) could also carry the same vulnerability until it is explicitly inventoried and marked Not Affected or Fixed.
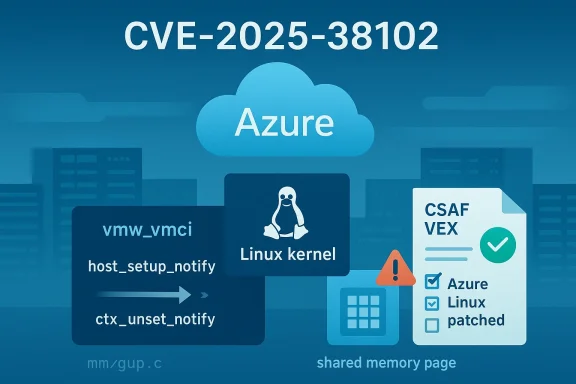
On July 3, 2025 the vulnerability tracked as CVE‑2025‑38102 was publicly disclosed upstream in the Linux kernel: a race condition in the VMCI (Virtual Machine Communication Interface) implementation that can occur between the functions vmci_host_setup_notify and vmci_ctx_unset_notify. The bug manifests as a concurrency window where a page pointer used for guest‑host notifications can be observed or freed before it is safely initialized; during tests this produced a kernel warning originating from the page‑grab path (a try_grab_folio / get_user_pages_fast interaction in mm/gup.c).
Vendor advisories and vulnerability databases (Linux upstream stable tree, several distribution advisories and OSV/NVD aggregations) record that the defect was fixed in kernel trees and that downstream distributions have released or are releasing patches for affected kernel branches. Microsoft’s Security Response Center (MSRC) published a product mapping that explicitly says Azure Linux “includes this open‑source library and is therefore potentially affected,” and also announced that Microsoft began publishing machine‑readable CSAF/VEX attestations in October 2025 and will update CVE mappings if additional Microsoft products are identified.
This article explains what that MSRC phrase means, why it does not equate to an absolute guarantee that no other Microsoft product contains the vulnerable code, what artifacts you should check in your estate, and what practical steps both Azure Linux customers and customers who run other Microsoft‑supplied artifacts must take right now.
Strengths:
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
On July 3, 2025 the vulnerability tracked as CVE‑2025‑38102 was publicly disclosed upstream in the Linux kernel: a race condition in the VMCI (Virtual Machine Communication Interface) implementation that can occur between the functions vmci_host_setup_notify and vmci_ctx_unset_notify. The bug manifests as a concurrency window where a page pointer used for guest‑host notifications can be observed or freed before it is safely initialized; during tests this produced a kernel warning originating from the page‑grab path (a try_grab_folio / get_user_pages_fast interaction in mm/gup.c).Vendor advisories and vulnerability databases (Linux upstream stable tree, several distribution advisories and OSV/NVD aggregations) record that the defect was fixed in kernel trees and that downstream distributions have released or are releasing patches for affected kernel branches. Microsoft’s Security Response Center (MSRC) published a product mapping that explicitly says Azure Linux “includes this open‑source library and is therefore potentially affected,” and also announced that Microsoft began publishing machine‑readable CSAF/VEX attestations in October 2025 and will update CVE mappings if additional Microsoft products are identified.
This article explains what that MSRC phrase means, why it does not equate to an absolute guarantee that no other Microsoft product contains the vulnerable code, what artifacts you should check in your estate, and what practical steps both Azure Linux customers and customers who run other Microsoft‑supplied artifacts must take right now.
Technical summary: what the bug is and why it matters
What VMCI is
- VMCI (Virtual Machine Communication Interface) is a VMware‑originated kernel component that exposes a high‑speed mechanism for communication between a virtual machine guest and its host (and, in some configurations, selected host services). On Linux it is commonly provided by the vmw_vmci driver (module name often shown as vmw_vmci or vmci depending on packaging).
- Presence of VMCI in a build is a build‑time decision driven by kernel configuration options such as CONFIG_VMWARE_VMCI. Not every Linux kernel build includes VMCI; the driver is enabled in kernels intended to run inside VMware guests or when distributions choose to upstream the module.
What CVE‑2025‑38102 is
- The vulnerability is a classic race condition: two concurrent code paths can interact with the same notification page pointer — one path that sets up a notification (vmci_host_setup_notify) and another that unsets it (vmci_ctx_unset_notify).
- The race occurs because the page pointer used for notifications may be visible to the unset path before get_user_pages_fast (or equivalent) has fully initialized it. Test traces show warnings in the memory‑acquisition codepath (try_grab_folio at mm/gup.c).
- Practical impact observed and reported by multiple vendors is a kernel warning and potential instability or crash (denial of service). There is no broadly‑reported, reliable public proof‑of‑concept for remote code execution tied to this specific race at the time of disclosure; the most plausible immediate risk is local crash / DoS or memory‑corruption scenarios if the race leads to use‑after‑free or uninitialized memory reads. Whether an attacker can escalate this into code execution depends on platform specifics, kernel hardening, CPU architecture, and the details of the race in any particular kernel build.
The fix
- The upstream fix is a synchronization/ordering change: the code ensures that the notification page is held in a local variable and only used after get_user_pages_fast completes and the pointer is validated. In short: access the page only after it is safely grabbed and synchronized.
- That fix was merged into the kernel trees and backported into many distribution kernels; downstream vendors published advisories and package updates on a rolling basis.
What Microsoft actually said — parsing the MSRC statement
Microsoft’s advisory language follows a conservative, inventory‑first model. The phrasing you quoted — that Azure Linux includes this open‑source library and is therefore potentially affected — carries two distinct, co‑existing meanings that are easy to conflate:- Definitive: Microsoft has performed a product‑level inventory for Azure Linux and found the implicated VMCI kernel component inside the images or kernels it examined. For Azure Linux customers, that is actionable: Microsoft has confirmed the product is in scope and should be patched where Microsoft has published updates.
- Non‑exclusive: The sentence is not an implicit guarantee that no other Microsoft product ships the component. It is a product attestation, not a global exclusivity statement. Microsoft also said it has started publishing CSAF/VEX attestations (a machine‑readable provenance/impact format) and will update CVE mappings if additional Microsoft products are later identified as carriers.
Why that distinction matters for customers
Large vendors ship a very wide array of artifacts: VM images, Marketplace images, Virtual Machine Scale Set images, AKS node images, WSL2 kernel builds, container base images, OEM‑style appliance images, and internal service kernels. The presence or absence of a given upstream kernel file is a build‑time property that depends on:- Kernel version and upstream commit range included in the build.
- Kernel config flags (e.g., CONFIG_VMWARE_VMCI) and which drivers were selected or built as modules.
- Distribution packaging choices and whether the vendor backported the relevant fix or dropped the driver.
- Whether the image is a generic distro, an Azure‑curated image, or a Microsoft‑custom kernel build (like some WSL2 kernels).
Microsoft‑owned artifacts to treat as candidates for additional inspection
If you run Microsoft‑supplied images, kernels, or appliances, treat the following as a priority inventory list to check for copy of the VMCI code (or other vulnerable upstream drivers):- WSL2 kernel builds distributed by Microsoft (the WSL2 kernel is a Microsoft‑packaged Linux kernel).
- Azure Marketplace images and vendor images published via Microsoft channels.
- Azure VM images, including curated distro images and custom images created from snapshots.
- AKS node images and any managed node images based on Microsoft kernels.
- Container base images published by Microsoft or in Marketplace that include a kernel userland pairing (less commonly vulnerable but worth verifying).
- Appliances and partner images that ship a kernel compiled by or for Microsoft use.
Practical checks customers should run now
Here are concrete, prioritized steps you can follow to determine exposure and remediate. Use them for Azure Linux tenants first and then broaden to other Microsoft artifacts in your estate.- Inventory and prioritize:
- List every Microsoft‑supplied image, VM, WSL2 instance, Kubernetes node image and Marketplace image you run.
- Prioritize public‑facing systems, privileged systems, and any environment where untrusted local users can trigger kernel interfaces.
- Check whether VMCI is present:
- On a running system, check for the VMCI driver/module: run lsmod | grep -i vmw_vmci or modinfo vmw_vmci (or check /proc/modules).
- Inspect the kernel config: zcat /proc/config.gz | grep -i VMWARE_VMCI or check /boot/config-$(uname -r).
- If /dev/vmci exists or modprobe vmw_vmci succeeds, that kernel includes VMCI support.
- Map kernel versions to upstream fixes:
- Use your vendor CVE advisory mapping (Microsoft’s VEX/CSAF data for Azure Linux, distro advisories for other images) to confirm whether your kernel includes the fixed commit range.
- If you cannot find a product attestation, treat the artifact as unverified and proceed to patch or rebuild.
- Patch or replace:
- For Azure Linux: apply Microsoft’s published updates for Azure Linux images promptly.
- For other images: upgrade the kernel to a vendor‑supplied patched release or rebuild the kernel with the upstream fix backported, and deploy the updated images.
- Mitigation / interim controls:
- If a patch cannot be applied immediately, reduce exposure by limiting untrusted local user access, disabling services that require VMCI if those services are not needed, or by running instances on hypervisors that do not present the VMCI device to guests.
- Continuous monitoring:
- Monitor vendor CVE feeds and Microsoft CSAF/VEX outputs for new attestations confirming additional Microsoft products.
- Enable kernel crash and dmesg logging aggregation so you can detect warning signs such as try_grab_folio stacks.
Why you cannot rely solely on the MSRC sentence for your estate
Microsoft’s MSRC attestation is helpful — it provides a clean, deterministic signal for Azure Linux customers — but it has these operational limits:- It is product‑scoped. It tells you MSRC confirmed the component in a specific Microsoft product family (Azure Linux). It does not imply an exhaustive search across all Microsoft products and artifacts.
- It is point‑in‑time. The attestation applies to the images and builds Microsoft inspected at the time of the inventory. New images, updates, or curated kernels introduced later may or may not include the code.
- It is tied to machine‑readable VEX rollout timelines. Microsoft committed to publish CSAF/VEX in October 2025 and to update CVE mappings when they find additional affected products, but the VEX rollout is a process; customers should not wait for VEX to finish to do artifact verification on their most critical systems.
Risk analysis: likelihood and impact
- Exploitability: the bug is a local concurrency race; exploitation requires conditions that allow the race to be reliably triggered. That typically means local code execution or the ability to induce the kernel to perform the specific VMCI notify/unset sequences under contention. Historically, VMCI vulnerabilities have been exploited in local contexts inside VMware guests, but widespread remote exploitability is not typical for this class of bug.
- Impact: vendor advisories describe kernel warnings and potential system instability. Distributions have scored the vulnerability in the medium severity range (examples of CVSS scores reported by downstream vendors vary; some advisories show scores in the mid‑5s, while other aggregators may show higher scores depending on local enrichment). The canonical, immediate concern is denial of service / instability; escalation to code execution is plausible in theory but not demonstrated publicly at disclosure time.
- Attack surface: systems that run inside VMware guests with the VMCI device present are the highest risk. Systems with no VMCI driver, or kernels built without CONFIG_VMWARE_VMCI, are not vulnerable to this specific VMCI race.
Microsoft’s transparency move: CSAF/VEX and its pros and cons
Microsoft’s pledge to publish machine‑readable CSAF/VEX attestations (beginning October 2025) is a notable step for vendor transparency. VEX enables vendors to mark which products are affected, which are not, and which are under review — machine‑consumable data that scales far better than plain HTML advisories.Strengths:
- Precision: VEX lets Microsoft say “this product is affected” or “this product is not affected” with explicit artifact and version metadata, which helps automation in large estates.
- Automation: customers can ingest VEX and automatically flag in‑scope assets.
- Rollout scope: VEX adoption is a process; early VEX attestation for one product (Azure Linux) is useful, but it does not mean other Microsoft products are already attested.
- Artifact granularity: VEX is only as good as the artifact and metadata Microsoft publishes. Customers still need to ensure their in‑house images or partner images are mapped correctly to VEX entries.
- Timing: there is an inevitable lag between discovery, patching, attestation, and downstream image rebuilds; exposure windows remain.
Recommendations for Microsoft and distro maintainers (critical analysis)
From a defender and vendor‑transparency perspective, the following would improve security outcomes for customers:- Publish per‑artifact kernel configuration and exact upstream commit ranges for all Microsoft‑packaged kernels (including WSL2, Azure VM images and Marketplace images). That makes it trivial to map upstream CVE fixes to shipped artifacts.
- Expand VEX/CSAF coverage quickly beyond Azure Linux to other Microsoft distributions and images that ship kernels. Attestations should explicitly list kernel versions and configs.
- For managed cloud images, publish an SBOM or lightweight kernel manifest indicating which drivers or modules were enabled; this reduces uncertainty for customers.
- Offer a clear, searchable inventory page for customers to query whether a specific Marketplace image or WSL kernel is attested as affected, not affected, or under review.
- For kernel bugs that have potential high impact, provide companion mitigation scripts or temporary configuration guidance (for example, how to disable VMCI device exposure where feasible).
Closing checklist — what to do right now
- If you run Azure Linux: apply Microsoft’s published Azure Linux updates without delay. Treat the MSRC attestation as an authoritative signal for Azure Linux images.
- If you run any Microsoft‑published images or kernels (WSL2, AKS nodes, Marketplace images, Azure VM images): perform artifact‑level checks (lsmod/modinfo, kernel config inspection, SBOM/image manifest review). Do not assume “not attested = not affected.”
- If you host VMware guest VMs on Azure or elsewhere and allow untrusted users inside the guest: treat this vulnerability as higher priority due to the presence of VMCI in many VMware virtual hardware configurations.
- Use automation: ingest vendor VEX/CSAF feeds when available, but also run your own scanning and SBOM checks across all images.
- Monitor vendor advisories for updated attestations: Microsoft has committed to updating CVE mapping if additional products are identified; subscribe to those feeds and pipeline updates into your patching workflows.
Conclusion
Microsoft’s MSRC statement that “Azure Linux includes this open‑source library and is therefore potentially affected” is an important and useful product‑level attestation — but it is not a blanket statement that no other Microsoft product contains the vulnerable VMCI code. The correct operational response for defenders is to treat the MSRC attestation as authoritative for Azure Linux, to act on it urgently for those images, and simultaneously to perform artifact‑level discovery across all Microsoft‑supplied kernels and images you run. Until Microsoft’s CSAF/VEX attestations explicitly declare other Microsoft artifacts as Not Affected or Fixed, customers must assume the possibility of exposure and verify each artifact’s kernel version and configuration. The best defense is a combination of vendor patches, automated attestation ingestion, and pragmatic-inventory work: patch Azure Linux now, inventory everything else, and close the gaps.Source: MSRC Security Update Guide - Microsoft Security Response Center