The Linux kernel fix tracked as CVE-2025-38170 addresses a subtle ARM64 context-switch bug in the FPSIMD/SME handling: under certain preemption and trap conditions the kernel could reuse stale floating-point/vector state, triggering unexpected SME traps and kernel warnings. Microsoft’s Security Response Center (MSRC) has published a product-level attestation saying, in essence, that Azure Linux includes the implicated open‑source component and is therefore potentially affected — and that Microsoft began publishing machine‑readable CSAF/VEX attestations in October 2025 and will update CVE records if additional Microsoft products are found to ship the same library. That MSRC wording is an authoritative inventory statement for Azure Linux customers, but it is not a technical guarantee that no other Microsoft product may include the same upstream kernel code. / Overview
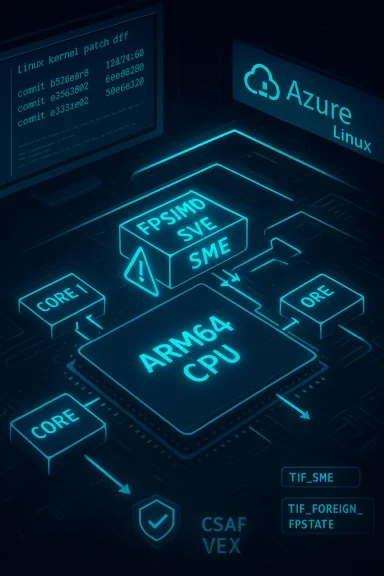
CVE-2025-38170 is an ARM64 architecture vulnerability in the kernel’s fpsimd (floating point / SIMD) handling related to SME (Scalable Matrix Extension) trap processing. The upstream kernel change description and multiple vulnerability trackers summarize the root cause as follows: the SME trap handler manipulates saved FPSIMD/SVE/SME state in a way that, when combined with preemption and migration, can leave a task with TIF_SME set and TIF_FOREIGN_FPSTATE clear even though the actual CPU state is stale. That mismatch can lead to warnings from do_sme_acc() and, in certain sequences, could result in incorrect behavior when userspace executes SME/SVE instructions.
Multiple vendor and distro trackers recorded and repackaged the fix after upstream kernel commits were applied; the public records show varying CVSS/Vendor severity assessments depending on vendor context. For example, Amazon Linux’s advisory lists a CVSS v3 base score of 7.0 (Important) for affected kernel channels, while Debian’s security tracker and other aggregators list a medium (≈5.5) rating for some releases — a discrepancy that reflects differing scoring decisions, attack-surface assumptions, and product contexts rather than contradictory technical facts about the bug itself. Administrators should treat both data points as inputs to prioritization rather than absolute contradiction.
Important clarifications:
Source: MSRC Security Update Guide - Microsoft Security Response Center
CVE-2025-38170 is an ARM64 architecture vulnerability in the kernel’s fpsimd (floating point / SIMD) handling related to SME (Scalable Matrix Extension) trap processing. The upstream kernel change description and multiple vulnerability trackers summarize the root cause as follows: the SME trap handler manipulates saved FPSIMD/SVE/SME state in a way that, when combined with preemption and migration, can leave a task with TIF_SME set and TIF_FOREIGN_FPSTATE clear even though the actual CPU state is stale. That mismatch can lead to warnings from do_sme_acc() and, in certain sequences, could result in incorrect behavior when userspace executes SME/SVE instructions.
Multiple vendor and distro trackers recorded and repackaged the fix after upstream kernel commits were applied; the public records show varying CVSS/Vendor severity assessments depending on vendor context. For example, Amazon Linux’s advisory lists a CVSS v3 base score of 7.0 (Important) for affected kernel channels, while Debian’s security tracker and other aggregators list a medium (≈5.5) rating for some releases — a discrepancy that reflects differing scoring decisions, attack-surface assumptions, and product contexts rather than contradictory technical facts about the bug itself. Administrators should treat both data points as inputs to prioritization rather than absolute contradiction.
 What the bug actually is — technical anatomy
What the bug actually is — technical anatomy
SME, FPSIMD and the kernel’s state model
ARM64 supports several floating/vector extensions with different register models: FPSIMD is the baseline FP/SIMD state; SVE (Scalable Vector Extension) and SME (Scalable Matrix Extension) build on that with larger or more complex contexts. The kernel keeps track of which task last used which hardware register state via per-task and per-CPU metadata, and it defers expensive state restores until userspace actually executes an instruction that requires that state (the “trap on first use” model). To do this safely the kernel uses flags such as:- TIF_SME / TIF_SVE / TIF_SVE: thread flags indicating the task expects SME/SVE features.
- TIF_FOREIGN_FPSTATE: indicates the CPU’s saved floating-point/vector state belongs to a different task and that a full restore may be required.
The race and stale-state reuse
In simplified terms the dangerous sequence is:- A task triggers an SME trap on CPU A; the trap handler manipulates saved FPSIMD/SME state and sets TIF_SME for that task.
- The trap handler is preempted or the task migrates across CPUs such that the per-CPU pointers and flags become inconsistent relative to the live hardware registers.
- Because the kernel’s logic sees TIF_SME set and TIF_FOREIGN_FPSTATE not set, it may assume the CPU state is fresh when in reality the hardware registers reflect a different context (stale).
- Returning to userspace proceeds without a safe restore, and SME instructions execute against incorrect register contents or unexpected trap behavior.
Practical impact and exploitability
What an attacker needs and realistic risks
This is primarily a local kernel correctness issue. The exploitability profile is constrained by:- Requirement for SME-capable hardware and kernel builds where SME is enabled.
- A precise interleaving of traps, preemption, and migration to create the stale-state reuse window.
- Local code execution privileges (untrusted workloads co-located on the same kernel) or guest-level code in virtualized environments with access to the SME-related instruction paths.
Symptoms administrators will see
- Log warnings or kernel WARN_ON triggers originating from do_sme_acc() complaining about unexpected SME traps.
- Potential incorrect execution of SME instructions, abnormal process behavior, or very rarely data corruption if state corruption manifests in computational results.
- Stability or correctness anomalies in workloads that depend on speculative heavy vector/SIMD usage.
Microsoft’s MSRC wording: what it says, and what it does not
Microsoft’s MSRC entries for many Linux kernel CVEs have adopted a concise product mapping line that reads along the lines of: “Azure Linux includes this open‑source library and is therefore potentially affected by this vulnerability.” The company also stated it began publishing CSAF/VEX attestations in October 2025 and will update the CVE when/if additional Microsoft products are discovered to ship the implicated component. That sentence is intentionally precise: it is a product‑scoped attestation that Microsoft inspected the Azure Linux build outputs and foonent in question.Important clarifications:
- Microsoft’s statement is an authoritative inventory result for Azure Linux only at time of publication. Treat it as a confirmed “Known Affected” signal for Azure Linux artifacts that Microsoft examined.
- The statement is not a universal negative for all other Microsoft products. It does not assert that no other Microsoft artifact or product includes the same upstream kernel code. The MSRC attestation is intentionally phased and product‑by‑product. Absence of a product name elsewhere in the CVE page typically means Microsoft hasn’t yet completed the inventory for that product—not that the product is Microsoft explicitly commits to updating CVE/VEX records if more products are found to include the library. That is an operational promise to expand coverage rather than an implicit exclusivity claim.
Is Azure Linux the only Microsoft product that includes the library and is therefore potentially affected?
Short answer: No, not necessarily — but with an important nuance.- Strictly speaking, Azure Linux is the only Microsoft produccly attested (so far) to include the implicated upstream component for this CVE. That makes Azure Linux a confirmed carrier for remediation prioritization.
- Technically and operationally, however, other Microsoft artifacts could include the same upstream kernel code. Microsoft ships many kernel-derived artifacts — for example, WSL2 kernel builds, specialized linux-azure kernels used in some Azure VM SKUs, Azure Marketplace images, AKS node images, and curated container base images. Whether any one of those artifacts includes the vulnerable code is an artifact‑level fact determined by kernel version, build-time configuration (CONFIG_ flags), and any vendor backports. Until those artifacts are individually inventoried or Microsoft publishes specific VEX attestations for them, they should be treated as unknown* rather than conclusively clean.
How to verify exposure across Microsoft-sourced artifacts (practical steps)
If you operate Microsoft-supplied images, kernels, or appliances, follow these prioritized steps to determine exposure and mitigate risk.- Prioritize Azure Linux (immediate)
- If you run Azure Linux (the Microsoft-maintained distro previously known as CBL-Mariner), apply Microsoft’s published securitaffected hosts. Microsoft’s attestation and VEX files give a direct remediation path for those images.
- Inventory all Microsoft-provided artifacts in your environment (24–72 hours)
- Enumerate:
- Azure Marketplace VM images you consume.
- AKS node images and node pool definitions.
- WSL2 kernels on Windows clients and servers where WSL is used.
- Any container base images from Microsoft registries.
- Marketplace or partner appliances and curated images.
- For each artifact, record the kernel version, package provenance, and build metadata. If metadata is missing, treat the artifact as Under Investigation. Community guidance repeatedly emphasizes artifact-level verification as the defensible posture.
- Use machine‑readable VEX/CSAF where available (automate)
- Ingest Microsoft’s VEX/CSAF feed into your vulnerability management system to automate triage for Azure Linux artifacts. Microsoft’s phased VEX rollout is designed to make this automation possible and reduce false positives. coverage is currently phased product-by-product.
- Inspect kernel binaries and images directly (artifact-level checks)
- Where possible, check kernel .config and build metadata; look for presence of SME/SVE support and the commit ranges listed in upstream advisories (vendor advisories and kernel.org patch references identify exact commits that introduced or fixed the behavior).
- For container images, extract the kernel headers or package lists used to build the image; for VMs, check installed kernel package versions and compare against distro advisories. Upstream commit IDs are published in many CVE trackers if you need to script binary provenance checks.
- Short-term mitigations where immediate patching is impractical
- Reduce exposure by isolating hosts where untrusted workloads might exploit local kernel invariants.
- Avoid multi-tenant consolidation patterns that permit untrusted users to run concurrent workloads on the same node.
- For high-assurance workloads, consider enforcing stricter scheduling/isolation and disabling unneeded kermized builds. These are temporary mitigations and do not replace patching.
- Patch and reboot (definitive remediation)
- The long-term fix is to apply vendor-supplied kernel updates that include the upstream SME trap handling commits, and to reboot into the patched kernel. Rebuilding statically linked binaries or container images that embed a vulnerable kernel userland is rarely necessary for this specific kernel-level issue, but ensure you update any bespoke kernels you build and ship. Upstream patches are available and distro vendors have repackaged them into fixed kernels; consult your distro advisory for exact package names and versions.
Why vendor attestation matters — and its limits
Large vendors cannot instantly inventory every binary, image, or SKU they ship. Microsoft’s decision to publish CSAF/VEX attestations starting with Azure Linux is operationally sensible: the Azure Linux product family is a single, well-scoped distribution Microsoft maintains, so it’s tractable to produce precise attestations for it first. That attestation materially helps customers automate triage and reduces scanner noise for that product family. However, the attestation’s product scope means:- It is a high-confidence signal for the named product.
- It is not an exhaustive inventory of every Microsoft artifact — vendors commonly commit to phased attestations precisely because of the operational difficulty of complete coverage. Treat absence-of-attestation as “not yet attested,” not “proven safe.”
Cross-checking the technical facts — independent sources
To avoid single-source reliance we validated key technical claims against multiple independent channels:- Upstream kernel commit summaries and patch listings available via kernel trackers and CVE aggregators document the exact code changes to fpsimd SME trap handling. These commits are referenced by multiple CVE aggregators and patch repositories.
- Vendor/distribution trackers (Amazon Linux advisory, Debian security tracker, OSV/NVD aggregators, Rapid7) independently describe the same root cause and list affected kernel branches and package remediations; they differ only in severity scoring and how they map affected product versions. This cross-check confirms the technical description and that fixes were backported across stable branches.
Operational checklist for Windows and Azure administrators
- If you run Azure Linux images: treat MSRC’s attestation as authoritative and patch immediately using the Microsoft guidance or the Azure image update path.
- For WSL2 and Windows-hosted kernels: review the WSL kernel builds your organization deploys (e.g., Microsoft-provided ones). Confirm the kernel version and whether SME/SVE support is present; if uncertain, treat them as unknown and either temporarily restrict SME-capable workloads or patch when fixed kernels are available.
- For Azure Marketplace images, AKS node images, and curated containers: inventory the kernel versions used by those images. If you cannot determine build provenance quickly, isolate or avoid high-risk multi-tenant configurations until the images are verified or updated.
- Automate ingestiCSAF feed and your distro vendor advisories into your vulnerability management and orchestration systems so you can triage, schedule patch windows, and track rollout status across fleets.
Final assessment — what administrators should take away
- Microsoft’s MSRC statement that “Azure Linux includes thisand is therefore potentially affected” is an authoritative, product-scoped attestation for Azure Linux — and it should be acted on by Azure Linux users immediately.
- That attestation does not prove that no other Microsoft product includes the same upstream component. Other Microsoft artifacts that embed Linux kernels can be unknown carriers until product-level VEX attestations or artifact inspections confirm otherwise. Treat un‑attested Microsoft artifacts as unverified and perform artifact-level checks.
- CVE-2025-38170 is a concrete kernel-level correctness bug with a realistic local-privilege or co-residency attack model. The definitive remediation is vendor-supplied kernel updates and reboots. In the meantime, isolate untrusted workloads and prioritize patch windows for affected images. (osv.dev)
Concluding recommendations (action plan)
- Apply patches to Azure Linux systems now — Microsoft’s attestation makes these a top priority.
- Inventory all Microsoft-supplien your environment and map kernel versions to upstream fixes. If you can’t verify an artifact quickly, mark it Under Investigation.
- Ingest VEX/CSAF data and distro advisories into your vulneraipeline to automate triage for Azure Linux and to catch new product attestations as Microsoft expands coverage.
- Deploy short-term isolation mitigations for high-risk multi-tenant workloads while planning rollouts for patched kernels. These are temporary; patching and rebooting is the final fix.
- Track vendor advisories for updated attestations — Microsoft has pledged to updateitional products are identified, so revisit MSRC/VEX entries for changes.
Source: MSRC Security Update Guide - Microsoft Security Response Center