A small, targeted fix in the Linux macb network driver — described in the CVE record as "net: macb: fix unregister_netdev call order in macb_remove" (CVE‑2025‑39805) — has prompted Microsoft to publish a product‑scoped attestation that Azure Linux includes the affected open‑source component and is therefore potentially affected; Microsoft also pledged to update the CVE/VEX record if additional Microsoft products are later identified as carriers. That wording is precise and important: it tells customers what Microsoft has validated so far, but it is not a blanket declaration that no other Microsoft product can include the same upstream driver. The operational reality is that whether any Microsoft product is affected depends on per‑artifact build choices and packaging, not a vendor‑wide binary decision.
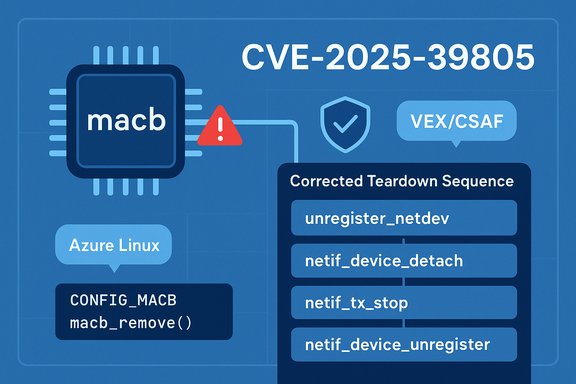
The macb driver is an in‑kernel Ethernet controller driver used for certain microcontroller and embedded network interfaces. The fix referenced by CVE‑2025‑39805 corrects the order of an unregister_netdev call in macb_remove, addressing a driver lifecycle / teardown ordering problem that could lead to kernel warnings, resource cleanup races, or device instability during module removal or device teardown.
Kernel lifecycle bugs of this class typically manifest as WARN_ON traces, refcount warnings, or device removal failures rather than immediate arbitrary code execution. In public vendor and distro advisories for similar kernel lifecycle issues, maintainers describe the practical impact as affecting availability and reliability (noisy logs, spurious reboots, device misbehavior) rather than an off‑the‑shelf remote code execution primitive. The upstream patch is usually small and focused on correct ordering and pointer/null management, making it straightforward — but important — to backport into stable kernels.
What Microsoft publicly stated about this CVE follows the company’s recent CSAF/VEX attestation rollout: Microsoft has published machine‑readable attestations starting with Azure Linux, and for this CVE the company mapped the vulnerable upstream kernel component into that product family and declared Azure Linux "potentially affected" while committing to update the mapping if other Microsoft products are later found to ship the same upstream code. That procedure is a pragmatic transparency model, but it requires careful interpretation.
Longer explanation:
Priority checks (ordered steps):
Operationally, the right posture is pragmatic and artifact‑centric: treat Microsoft’s Azure Linux attestation as a high‑priority signal and apply the vendor’s patches for those images immediately, while also inventorying and verifying any other Microsoft or third‑party images you run. The presence of the macb driver — and thus potential exposure to CVE‑2025‑39805 — is a per‑artifact property determined by kernel build choices and image provenance; the only way to be certain for non‑attested artifacts is to inspect the image, kernel config, or module set directly.
Key takeaways:
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
The macb driver is an in‑kernel Ethernet controller driver used for certain microcontroller and embedded network interfaces. The fix referenced by CVE‑2025‑39805 corrects the order of an unregister_netdev call in macb_remove, addressing a driver lifecycle / teardown ordering problem that could lead to kernel warnings, resource cleanup races, or device instability during module removal or device teardown.Kernel lifecycle bugs of this class typically manifest as WARN_ON traces, refcount warnings, or device removal failures rather than immediate arbitrary code execution. In public vendor and distro advisories for similar kernel lifecycle issues, maintainers describe the practical impact as affecting availability and reliability (noisy logs, spurious reboots, device misbehavior) rather than an off‑the‑shelf remote code execution primitive. The upstream patch is usually small and focused on correct ordering and pointer/null management, making it straightforward — but important — to backport into stable kernels.
What Microsoft publicly stated about this CVE follows the company’s recent CSAF/VEX attestation rollout: Microsoft has published machine‑readable attestations starting with Azure Linux, and for this CVE the company mapped the vulnerable upstream kernel component into that product family and declared Azure Linux "potentially affected" while committing to update the mapping if other Microsoft products are later found to ship the same upstream code. That procedure is a pragmatic transparency model, but it requires careful interpretation.
What the Microsoft statement actually means
Microsoft published product‑scoped attestations first for Azure Linux
- Microsoft’s CSAF/VEX rollout began with Azure Linux and the company is using machine‑readable attestations to map upstream components to Microsoft product artifacts.
- When Microsoft says Azure Linux “includes this open‑source library and is therefore potentially affected,” it is reporting the result of an inventory and validation for that particular product family — not making a universal statement about every Microsoft product.
The difference between “attested” and “exclusive”
- Attested (what Microsoft did): Microsoft has completed verification for Azure Linux and published the product mapping. That is an authoritative and automatable signal for customers who run Microsoft‑published Azure Linux images.
- Exclusive (what it is not): The attestation does not prove other Microsoft products are free of the same upstream component. Presence of upstream code is a per‑artifact, build‑time property (kernel config flags, module choices, statically compiled binaries, container images). Microsoft has explicitly said it will update the CVE/VEX entry if other internal SKUs are discovered to include the component.
Why vendors often publish attestations in phases
- Large vendors ship many artifacts and images. Completing a reliable, product‑level inventory is time‑consuming.
- Starting with one product family reduces time to publish a validated automation input for customers — but it leaves other product surfaces to be inventoried later.
- Thus, the correct operational reading of Microsoft’s wording is: Azure Linux is the only Microsoft product Microsoft has publicly validated and attested for this CVE so far; other Microsoft artifacts may or may not include the driver and require per‑artifact verification.
Is Azure Linux the only Microsoft product that could be affected?
Short answer: No — Azure Linux is not necessarily the only Microsoft product that could include the vulnerable macb driver or similar kernel code, but it is the only Microsoft product Microsoft has publicly attested as including the component at disclosure time.Longer explanation:
- Microsoft publishes and maintains multiple Linux kernel artifacts and images across Azure and other product lines: the linux‑azure kernel packages, Azure Linux distribution images, WSL2 kernels, curated container images, Marketplace VM images, and some first‑party service artifacts. Each of these is an independent artifact with its own build configuration and may or may not include the macb driver. Whether a given Microsoft product actually ships macb depends on kernel config flags and packaging choices at build time (e.g., CONFIG_MACB as built‑in or as a module).
- Some Microsoft artifacts (for example, WSL kernels) are published with explicit kernel configs that may omit or include hardware driver stacks depending on the operational goals of the artifact. A default WSL kernel build often strips out desktop‑grade drivers, but a custom WSL kernel or certain Azure VM images could include them. That means default behavior may be safe, but custom or alternative builds can introduce exposure.
- Third‑party and marketplace images that run on Microsoft infrastructure are often built by external publishers. Microsoft’s attestation covers Microsoft‑published Azure Linux images; it does not automatically attest partner or marketplace images, which remain the responsibility of their respective maintainers. Those images can include older or unpatched kernel modules.
Technical impact and exploitability — practical risk assessment
What the macb fix addresses
The patch reorders/unregisters the network device cleanup sequence in macb_remove, ensuring unregister_netdev or related teardown calls happen in the correct order to avoid stale pointers, racing unregister sequences, or incomplete cleanup. Fixes for this class of bug are typically surgical and low‑risk to backport but important to prevent instability.Typical symptom set and likely outcomes
- Kernel WARN_ON traces and refcount warnings during module unload or device removal.
- Sporadic device misbehavior, kernel oops, or instability in affected scenarios.
- Potential denial‑of‑service in multi‑tenant or automated environments where device hotplug/unplug operations are performed at scale.
Public trackers and vendor posts for similar kernel lifecycle defects emphasize availability and reliability impacts rather than immediate remote code execution or privilege escalation; exploiting an ordering bug to achieve RCE generally requires additional unrelated memory‑corruption bugs or allocator primitives.
Who should be most concerned
- Hosts and images that include the macb driver (embedded devices, custom VM images, appliance images).
- Environments that perform frequent device hotplug, module reloads, or dynamic network reconfiguration.
- Multi‑tenant or automated orchestration systems where an unstable kernel can cascade into service outages.
How to verify exposure (practical detection & hunting)
Operators should treat Microsoft’s Azure Linux attestation as authoritative for Azure Linux images and treat every other Microsoft image or artifact as unverified until proven otherwise. The only deterministic way to confirm exposure is to inspect the artifact(s) in your own estate.Priority checks (ordered steps):
- Inventory
- Enumerate all Azure images, VM SKUs, container images, and WSL kernels in use.
- Mark which are Microsoft‑published Azure Linux images (these are attested) versus third‑party / marketplace images (these must be validated separately).
- Kernel config and module inspection (host level)
- On a suspect system, check whether the macb driver is present:
- lsmod | grep macb
- modinfo macb
- zgrep CONFIG_MACB /proc/config.gz or check the kernel config in /boot for CONFIG_MACB=y or =m
- If macb is a module, inspect the module version and package providing it; compare against vendor kernel changelogs.
- Image and container inspection (artifact level)
- Pull container images into a staging registry and inspect installed kernel packages or check for bundled kernel modules.
- For VM images, mount the disk and inspect /lib/modules and the kernel config in /boot to determine whether macb is present.
- SBOMs and build provenance
- Use SBOMs (when available) for Microsoft images or your own images to validate whether the kernel sources or modules include macb.
- For statically packaged appliances, obtain build logs or request attestations from the vendor.
- Log hunting
- Search central syslog/journalctl for WARN traces mentioning macb, unregister_netdev, or stack traces during module remove or device teardown operations.
- Capture a vmcore or persistent dmesg if you see transient WARNs to preserve evidence for post‑mortem.
Remediation and mitigation guidance
- Prioritize Microsoft‑published Azure Linux images
- If you run Microsoft’s Azure Linux images, treat the VEX/CSAF attestation as an actionable signal and apply Microsoft’s published kernel updates as soon as they are released. Microsoft stated it will keep Azure Linux up to date and to monitor the published VEX attestation for remediation status.
- Patch and reboot
- Kernel fixes require a kernel package update and reboot to take effect. Plan for maintenance windows on production hosts where the kernel will be updated.
- For third‑party or partner images
- Contact the image vendor or rebuild images with updated kernels; do not assume Microsoft will patch those images unless the vendor is Microsoft. Marketplace and third‑party images are maintained by their publishers.
- For static, embedded or appliance binaries
- If a vendor ships a kernel or driver statically within an appliance, require an updated image from the vendor that contains the backport. Updating system packages is insufficient if the vulnerable module is embedded inside a fixed image.
- Operational mitigations (temporary)
- If immediate patching is impossible, reduce exposure by limiting device hotplug operations, restricting access to management interfaces that trigger the driver teardown path, and monitoring for suspect WARN_ON traces. These are temporary controls; they do not fix the root cause.
Cross‑checks and verification best practices
- Use independent sources to confirm the technical nature of the fix (upstream kernel commit, distro security trackers, NVD/OSV entries). Cross‑validation reduces reliance on a single vendor statement and helps operators judge backport coverage and timelines. Microsoft’s VEX attestation is authoritative for Azure Linux, but independent upstream/distro data helps you confirm patch availability and mapping across other images.
- Incorporate SBOMs and build provenance into CI/CD and image‑creation workflows. Knowing which kernel config and which commit a kernel image was built from removes ambiguity in future incidents. Microsoft’s move to publish CSAF/VEX attestations for Azure Linux makes this kind of automation feasible; adopt similar automation for your internal images.
Strengths and potential risks in Microsoft’s disclosure approach
Strengths
- Microsoft’s CSAF/VEX rollout and the explicit attestation for Azure Linux provide machine‑readable, actionable signals for customers who run those specific images. That reduces triage time for those customers and allows automated remediation workflows to operate deterministically.
- The vendor’s commitment to update CVE/VEX entries if additional products are identified is a strong procedural promise that improves transparency compared to earlier ad‑hoc advisories.
Risks and gaps
- The phased approach inevitably leaves a time window where other Microsoft artifacts might include the vulnerable component but lack an attestation. Customers running other Microsoft images or third‑party Marketplace images must perform independent verification; absence of a VEX mapping is not proof of absence. Treat un‑attested artifacts as “not yet verified” rather than “safe.”
- Complex cloud estates that use a mix of Microsoft‑published images, marketplace images, curated containers, and customer‑built images can face fragmentation in patch cadences and responsibilities. Operational owners must confirm which vendor (Microsoft or third‑party) is responsible for each artifact’s patching.
Practical checklist for WindowsForum readers and enterprise operators
- If you run Azure Linux images:
- Treat Microsoft’s attestation as authoritative for those images and apply the vendor‑published kernel updates as soon as they are released.
- If you run other Microsoft images or services:
- Inspect kernel configs and modules on hosts; do not assume Microsoft’s Azure Linux attestation covers them. Use the commands and image inspection steps above to confirm presence of macb.
- If you run marketplace or partner images:
- Contact the image publisher and request their CVE status or updated images. Treat Marketplace images as independently maintained artifacts.
- For development and CI pipelines:
- Add SBOM and build toolchain metadata checks to detect if an image or binary was built from a kernel commit range containing the macb issue. Rebuild affected images with patched kernels.
- Monitor telemetry and logs:
- Centralize kernel logs and alert on WARN_ON traces mentioning macb, unregister_netdev, or related stack frames to detect attempted or occurring failures.
Conclusion
Microsoft’s public attestation that Azure Linux includes the open‑source component implicated by CVE‑2025‑39805 is an authoritative, machine‑readable signal for customers who run those images — and Microsoft has committed to update the CVE/VEX record if other Microsoft products are later identified as carriers. That statement is deliberately product‑scoped and procedural: it reports what Microsoft has validated so far, not a blanket guarantee about every Microsoft product.Operationally, the right posture is pragmatic and artifact‑centric: treat Microsoft’s Azure Linux attestation as a high‑priority signal and apply the vendor’s patches for those images immediately, while also inventorying and verifying any other Microsoft or third‑party images you run. The presence of the macb driver — and thus potential exposure to CVE‑2025‑39805 — is a per‑artifact property determined by kernel build choices and image provenance; the only way to be certain for non‑attested artifacts is to inspect the image, kernel config, or module set directly.
Key takeaways:
- Azure Linux: attested by Microsoft as potentially affected — act now if you use these images.
- Other Microsoft products: may include the same driver depending on build choices; verify per artifact rather than assuming safety.
- Third‑party / Marketplace images: remain the publisher’s responsibility; do not rely on Microsoft’s Azure Linux attestation to cover them.
Source: MSRC Security Update Guide - Microsoft Security Response Center