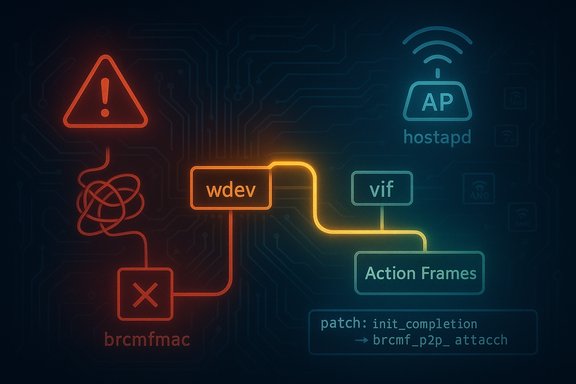
A small but dangerous bug in the Broadcom Linux wireless driver has been fixed upstream: CVE-2025-40321 addresses a NULL-pointer crash in brcmfmac that occurs when the driver attempts to send Wi‑Fi Action Frames while running in standalone AP mode (hostapd-only). The flaw can be triggered by an incoming ANQP/Action frame and results in an immediate kernel oops and driver crash on affected systems; an upstream patch changes how the driver selects the virtual interface (vif) for actframe IOVARs and moves the initialization of a completion object so the transmit path no longer dereferences an uninitialized pointer.
Conclusion: install the patched kernel as soon as vendor updates are available, prioritize high‑exposure AP and gateway devices in your estate, and treat kernel oops caused by wireless drivers as high‑impact incidents — a denial‑of‑service through a single, crafted management frame is small to implement and large in consequence for available infrastructure.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
What is brcmfmac and why this matters
brcmfmac is the in‑tree Linux kernel driver for Broadcom/Cypress FullMAC Wi‑Fi chipsets used in a huge range of consumer boards and embedded devices — notably many single‑board computers, laptops, and vendor routers. It implements firmware loading, station/AP modes, P2P (Wi‑Fi Direct) helpers and integrates with the cfg80211 / nl80211 stack. Because Wi‑Fi drivers run in kernel space, logic faults there commonly cause kernel oops/panic conditions that take down networking or the entire host. The vulnerability addressed by CVE‑2025‑40321 is a typical kernel‑space availability bug: a missing or incorrect pointer leads to a NULL dereference and crash when handling a specific management‑frame flow.Standalone AP mode vs wpa_supplicant
There are two common userspace managers for Linux wireless interfaces in practice: wpa_supplicant (typically for client and P2P workflows) and hostapd (for running access points and AP‑related services). The brcmfmac driver historically relied on P2P vifs being present when sending certain action frames — a condition true when wpa_supplicant manages the device — but not guaranteed when only hostapd manages the interface. This mismatch in assumptions is the operational context that allowed a NULL pointer to be dereferenced.Technical summary of CVE‑2025‑40321
Root cause in plain language
When userspace asks the kernel to transmit an Action Frame (for example, an ANQP presence/response), the brcmfmac driver must decide which virtual interface (vif) to use to build and forward the firmware IOVAR call that drives the hardware. The vulnerable code always selected the P2P vif for the actframe IOVAR. If the system is operating as an AP driven by hostapd alone, P2P vifs may never have been created; the driver then attempts to use an uninitialized P2P vif pointer. Dereferencing that NULL pointer causes a kernel NULL pointer dereference and crash. The upstream fix makes the driver use the vif corresponding to the wdev that initiated the transmit request and moves theinit_completion for the send_af_done completion into an attach path that always runs under hostapd scenarios. What changed in the patch
The patch set is intentionally small and surgical:- Select vif from the wdev that was used to request the Action Frame transmission rather than unconditionally using the P2P device vif. This eliminates the path where an uninitialized pointer can be used for the firmware call.
- Move initialization of the
send_af_donecompletion from a P2P device creation routine (which may not execute under hostapd-only scenarios) into the brcmf_p2p_attach path so the completion is always initialized prior to use. - Remove an unnecessary conditional around P2P Presence Response handling that depended on wpa_supplicant semantics and could be misleading when hostapd manages the interface.
Reproduction, symptoms and observable indicators
Typical crash signature
Operators who observed the crash reported an immediate kernel oops with traces pointing into the brcmfmac symbol space. Example call‑trace frames reported in public issue trackers and advisories includebrcmf_p2p_send_action_frame, brcmf_cfg80211_mgmt_tx, cfg80211_mlme_mgmt_tx, and nl80211_tx_mgmt followed by kernel message lines showing Unable to handle kernel NULL pointer dereference. On many platforms (for example Raspberry Pi 4), system logs contain the hardware identifier and the kernel backtrace captured by dmesg/journal. Real‑world triggers
The bug is triggered when the AP (hostapd) receives a certain Action Frame — notably ANQP Query REQ frames — even from an unassociated station. In publicly reported reproductions, a mobile handset sending a specific management frame to the AP was sufficient to provoke the crash. That pattern means the flaw can be triggered remotely from the perspective of a networked client (radio proximity required), unlike many kernel bugs that require local shell access.Who and what is affected
- Any Linux system that runs a kernel with the in‑tree brcmfmac driver (Broadcom/Cypress FullMAC Wi‑Fi) and that uses the driver to operate an AP using hostapd is in scope.
- Popular single‑board computers (notably Raspberry Pi models that use Broadcom wireless hardware and the brcmfmac driver) were reported in repros; embedded appliances and routers using the same driver may also be affected.
- Distributions that ship kernels with brcmfmac integrated will be affected until they include the upstream fix or a backport. Embedded vendor kernels and OEM images represent the long tail of exposure because they often lag upstream fixes and packaging.
Severity, exploitability and real‑world risk
Impact model
- Primary impact: Availability — immediate kernel oops/driver crash and lost Wi‑Fi connectivity or full system instability.
- Attack surface: A remote management frame transmitted over the air (radio proximity required). This is network‑facing in the sense that an unauthenticated wireless client can send the triggering management frames, but the attacker must be able to reach the AP radio.
Exploitability nuance
The flaw is triggered by a wireless management frame; thus, an unprivileged external client can cause the AP host to crash. That elevates exploitability in contexts where untrusted Wi‑Fi clients are permitted to associate or otherwise interact with the AP management plane (public hotspots, guest networks, or unconstrained IoT deployments). There is no authoritative public evidence (at disclosure) that this was used to gain privilege escalation or remote code execution in the wild, but the ability to cause consistent crashes is itself a potent denial‑of‑service vector.Remediation and mitigation — practical guidance
Definitive remediation (recommended)
- Install a kernel that includes the upstream brcmfmac fix — upgrade to the distribution kernel package that contains the patch or apply the upstream commit and rebuild your kernel. Many distributions and stable kernel trees have received backports; apply vendor updates when they are available.
- Reboot into the patched kernel to remove the vulnerable code path from live memory.
Short‑term mitigations (if patching is delayed)
- Isolate the affected APs from untrusted wireless clients: restrict guest networks, enforce mutual authentication or WPA2/3, and limit management‑frame exposure. This reduces the window where an untrusted client can send the triggering frame.
- Harden local access: reduce the set of users/processes that can manage hostapd or manipulate wireless interfaces on the host.
- Monitor for signature logs: watch kernel logs for
brcmf_p2p_send_action_framebacktraces,NULL pointer dereference, or other brcmfmac oops symptoms usingjournalctl -kordmesg. Capture crash dumps (kdump) if you need forensics.
uname -r— confirm running kernellsmod | grep brcmfmac— check if the module is loadedjournalctl -k | egrep -i 'brcmf|brcmf_p2p_send_action_frame|NULL pointer'— hunt for oopsmodinfo brcmfmac— inspect module metadata
For vendors and embedded devices
- Push a patched firmware/kernel image to customers as a priority. The upstream fix is small and low risk to backport; appliance vendors should test and publish updates for their device images.
- If kernel updates are infeasible in the short term, consider network‑level isolation of vulnerable devices until updates are available.
Detection and incident response checklist
- Inventory hosts with Broadcom wireless:
grep -i brcmfmac /boot/config-* || lsmod | grep brcmfmac. - Cross‑reference your kernel package version with your distro security tracker and the upstream commit list to confirm whether your kernel contains the fix.
- If you observe crashes: capture
dmesgoutput, preservevmcoreif available, and collect timestamps of wireless client activity for correlation. - Apply vendor patches and reboot in a controlled maintenance window; validate AP behavior after patching by stressing management‑frame handling and run client interoperability checks.
Why the fix is reasonable — strengths and remaining risks
Strengths
- The upstream resolution is small and surgical: selecting the correct vif and ensuring the completion object is initialized are minimal changes that close the crash path with low regression risk. This surgical approach favors rapid backporting to stable kernel branches and distribution kernels.
- The root cause is a clear logic/initialization mismatch which is easily explainable and verifiable in the driver source. The upstream patch was accepted and flagged for stable backports, which accelerates distribution updates.
Potential risks and caveats
- Long‑tail devices: many embedded appliances and vendor images use forked or outdated kernels; these devices may remain vulnerable for an extended period unless vendors issue firmware/kernel updates. This is the common operational gap for small kernel fixes.
- Detection noise: kernel oops traces can be noisy and intermittent. Hosts without centralized kernel logging may miss early hits, so invest in log collection and retention.
- Misinterpretation of severity: public discourse can incorrectly conflate a crash‑only bug with immediate RCE risk. There is no public proof that CVE‑2025‑40321 enables remote code execution; treat claims of RCE as unverified unless accompanied by a reproducible PoC. Availability impact is the clear, observed effect.
Recommended timeline and checklist for administrators
- Short term (days)
- Inventory affected hosts and prioritize high‑impact APs (public hotspots, multi‑tenant APs, IoT gateways).
- Implement temporary network restrictions for untrusted clients where practical.
- Enable kernel log aggregation and search for brcmfmac oops signatures.
- Near term (1–2 weeks)
- Apply distribution kernel updates that include the brcmfmac fix as they arrive.
- Reboot patched hosts during planned maintenance windows and validate AP operation.
- Long term (weeks–months)
- For vendor appliances, track vendor advisories and coordinate firmware updates.
- Harden Wi‑Fi management plane exposure and limit untrusted client access on critical APs.
- Update patching and incident playbooks to include kernel driver CVEs in mixed OS estates.
Final analysis
CVE‑2025‑40321 is a classic example of how small assumptions in kernel drivers — a reliance on a particular vif being present and a misplaced initialization — translate to real operational risk. The bug is not exotic: the fix is straightforward, low risk and already integrated upstream. The practical problem for operators is not the technical difficulty of the patch but the operational reality of getting patched kernels into the right machines: vendor appliances, embedded devices, and long‑lived SBC images are the primary long‑tail exposure. Administrators should prioritize patching AP hosts and Raspberry Pi‑class devices that run hostapd and brcmfmac, monitor for brcmfmac oopses, and apply network hardening where timely patching is not immediately possible. The change itself is well‑scoped and conservative, and once deployed should restore predictable, stable behavior when handling action frames.Conclusion: install the patched kernel as soon as vendor updates are available, prioritize high‑exposure AP and gateway devices in your estate, and treat kernel oops caused by wireless drivers as high‑impact incidents — a denial‑of‑service through a single, crafted management frame is small to implement and large in consequence for available infrastructure.
Source: MSRC Security Update Guide - Microsoft Security Response Center