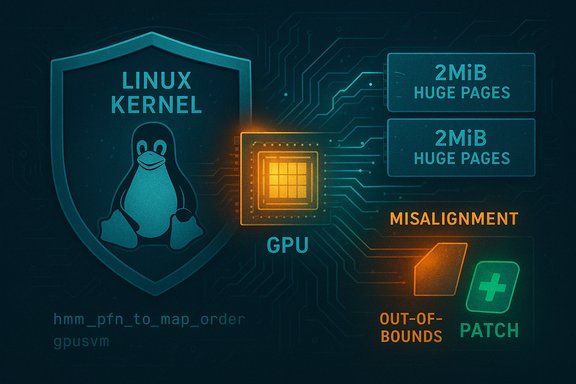
The Linux kernel security community disclosed CVE-2025-40336, a vulnerability in the DRM gpusvm code that mishandles hmm_pfn_to_map_order when an HMM range partially covers a huge page; the bug could allow the kernel to map memory outside the intended range (and potentially outside the process’s mm), risking kernel-level memory corruption and denial-of-service until systems are patched.
Background
The Linux kernel’s GPU SVM (Shared Virtual Memory) integration relies on the HMM (Heterogeneous Memory Management) helpers to safely translate and map user/guest memory into GPU address spaces. A subtle arithmetic/ordering assumption in the DRM gpusvm code meant that when an HMM range only covered part of a huge page (for example, a 2 MiB huge page), the conversion performed by hmm_pfn_to_map_order could produce an incorrect mapping order. That incorrect order permitted mapping granules that extended beyond the HMM-specified range, which in turn may cause the kernel to reference or map pages that are not present in the task’s mm — a correctness defect with immediate availability and integrity implications. The upstream remediation was small and surgical: align the order computation to handle partial huge-page coverage and make the mapping decision consistent with the xe userptr approach. Why this matters in practical terms: a kernel mapping that reaches outside the declared HMM range can produce invalid PTEs, induce page-table races or stale mappings, and trigger kernel oopses, corrupt kernel memory structures, or crash the host. For multi-tenant infrastructure (cloud hosts, CI runners, GPU-enabled containers) or shared developer workstations with GPU access enabled for unprivileged processes, this class of bug presents an operationally serious denial-of-service vector even if it is not trivially exploitable for remote code execution. Public vulnerability trackers and distribution advisories classify the issue as a correctness / memory-corruption bug and have mapped the fix into the upstream stable tree.Technical analysis
The vulnerable pattern: partial huge-page ranges and order calculation
At the heart of the bug is a mismatch between HMM range boundaries and the granularity used when deciding how to map pages for GPU access. HMM operates on page-frame numbers (PFNs) and returns ranges that describe which PFNs belong to the range. The helper function hmm_pfn_to_map_order is responsible for computing the order (power-of-two grouping) used when mapping PFNs to the GPU’s page table. When the HMM range aligns perfectly with huge pages, simple page-aligned arithmetic suffices. But when the HMM range begins or ends inside a huge page, naïve computations can produce an order that crosses the declared boundaries — i.e., a mapping unit larger than the portion that HMM guarantees is safe to map. That produces a situation where the driver may attempt to map PFNs that are outside the range, or even unmapped in the mm. The upstream patch corrected the order calculation to explicitly handle partial huge-page coverage and follow the semantics used by the xe userptr code path, preventing out-of-range mapping.Why the upstream fix is intentionally small
Kernel maintainers prefer local, low-risk edits when the issue is a correctness invariant rather than a design flaw. The fix aligned the gpusvm mapping order logic with the approach already used in the xe userptr implementation, added kernel-doc comments, and replaced a few helper calls (for example, moving from fls to ilog2 in v2 of the submission) to be explicit about the bit-width and ordering semantics. Because the change affects only the mapping-order calculation and the guard around partial huge page handling, it is straightforward to review and backport into stable series without widespread behavioral change in the rest of the driver. This surgical edit reduces regression risk while removing the out-of-range mapping primitive.Potential consequences if unpatched
- Kernel oopses and hardening-triggered panics when the kernel attempts to walk or modify page tables that were never created or owned by the mm.
- Data corruption in kernel data structures or GPU mapping tables when invalid PFNs are inserted, creating unstable system state and possible cascading failures of the graphics subsystem.
- Deterministic denial-of-service from local code that can trigger the affected path repeatedly (for instance, unprivileged applications or sandboxed workloads that use GPU SVM or userptr techniques).
- In theory, a skilled attacker with local access and the right memory-shaping primitives might attempt to escalate this into a stronger exploit (for example by leveraging memory-corruption primitives). There is no public proof of such escalation for this CVE at disclosure, but kernel memory-corruption primitives are historically attractive to attackers aiming for privilege escalation — so treat claims about immediate remote RCE as unverified and prioritize remediation.
Scope and affected releases
Multiple vulnerability trackers and distribution security pages indexed CVE-2025-40336 after the upstream stable commits landed. The Open Source Vulnerabilities (OSV) entry and the NVD record the short technical summary and link to the kernel commits that implement the fix. Debian’s security tracker maps this CVE to specific package versions across releases and shows which Debian branches remained vulnerable versus which ones were marked fixed; upstream stable commit references indicate that earlier stable kernels prior to the fixed commit are affected. SUSE and other trackers published similar upstream summaries, reflecting a broad vendor consensus about the defect and remediation path. Practical takeaways for operators:- Inventory kernels: identify the running kernel version (uname -r) and the distribution kernel package version. Distribution advisories — Debian, SUSE, Ubuntu, etc. — are the authoritative place to find mapped, fixed package versions for each release. Debian’s tracker, for example, lists ranged statuses and fixed package references for certain branches.
- Vendor kernels and OEM forks: remember that downstream and vendor-supplied kernels (Android OEM kernels, embedded vendor images, appliance kernels) often lag upstream and may not have the stable commit backported. Those images are the long tail of exposure and warrant special attention in device fleets and embedded appliances.
Exploitability and real-world evidence
At disclosure, public-tracking entries treat the attack vector as local and focus on availability and correctness rather than confidentiality or integrity compromise. Tools that score exploitability (for example, EPSS) report low probability for mass exploitation because the bug requires local access and particular mapping patterns to reach the partial-huge-page case. Some enrichment sources classify the attack complexity as medium–high due to the need for specific conditions and kernel configurations. There is no authoritative public evidence that this CVE was weaponized in the wild at the time of disclosure; however, the mere presence of a reliable kernel crash primitive is sufficient reason to prioritize patching on shared infrastructure and any host that exposes GPU device nodes to untrusted processes. Be conservative in threat modeling: treat the bug as a near-term availability risk and a medium-term escalation primitive only if additional local conditions and memory-shaping techniques can be controlled by an attacker. That pragmatic stance aligns with how maintainers and distribution trackers framed the vulnerability.Detection and triage steps
Quick triage checklist to determine exposure and detect likely exploitation attempts:- 1. Confirm kernel and modules:
- Run uname -r to capture the kernel release string.
- Check for loaded DRM modules and gpusvm/xe components: lsmod | grep -i drm; lsmod | grep -i xe. These identify systems that may load the affected code path.
- 2. Inspect package changelogs:
- Consult your distribution’s security tracker (Ubuntu USNs, Debian tracker, SUSE bulletins) and kernel package changelogs for CVE-2025-40336 mappings or the stable commit IDs referenced by the CVE entries.
- 3. Search logs for relevant OOPS signatures:
- Examine dmesg and journalctl -k for call traces that reference gpusvm, hmm_pfn_to_map_order, or mapping helper frames in the amdgpu/xe DRM stacks. Kernel oops traces typically include symbol names that directly point to the affected code path.
- 4. Reproduce in staging (safely):
- If you manage a test farm with representative GPUs and kernels, attempt workload patterns that use GPU SVM/userptr flows to see whether the patched behavior resolves previously observed oopses.
- 5. Harden access if patching will be delayed:
- Restrict access to /dev/dri devices via udev rules or group membership to remove untrusted processes’ ability to trigger the mapping path. Remove GPU passthrough from untrusted containers and VMs where feasible.
Remediation and mitigation
The definitive remediation is to install the vendor- or distribution-provided kernel update that includes the upstream stable commit(s) for CVE-2025-40336 and reboot into the patched kernel. The fix is kernel-level; it becomes effective only after a kernel update + reboot. Operators should:- Prioritize patching on:
- Multi-tenant hosts, cloud hypervisors, CI runners, and GPU-accelerated VM hosts.
- Developer machines and workstations that run untrusted code with access to GPU devices or that expose /dev/dri to non-privileged users.
- Embedded or appliance devices with vendor kernels — require direct vendor confirmation for backports.
- Validate patch presence:
- Use distribution package metadata or changelog entries to confirm the specific stable commit ID has been included in the installed kernel package. Distribution trackers show fixed-version mappings (e.g., Debian security tracker lists candidate fixed versions for specific branches).
- Apply compensating controls when immediate patching is infeasible:
- Limit access to GPU device nodes with udev or group policies.
- Remove direct device passthrough from untrusted guests/containers.
- Monitor for recurring kernel oopses and escalate hosts that repeatedly hit DRM mapping traces.
- For custom kernels:
- Backport the upstream stable commit into your custom tree and rebuild the kernel. The upstream patch is deliberately small and designed to be easy to backport; keep changes minimal to avoid regressions.
Operational recommendations for enterprise fleets
- Inventory and risk-rank assets by GPU exposure: hosts that provide GPU acceleration to containers, CI jobs, or guest VMs should be the highest remediation priority.
- Add GPU driver monitoring to SIEM rules: new oopses that mention gpusvm or hmm_pfn_to_map_order should alert a security response workflow.
- Maintain a vendor-kernel inventory: OEMs and appliance vendors often lag upstream; document which devices rely on vendor kernels and request explicit CVE backport windows where necessary.
- Automate patch verification: use configuration management to verify kernel package versions and, when possible, match upstream commit hashes embedded in vendor changelogs to confirm the presence of the fix.
- Test patched kernels in canary pools before fleet rollout: GPU-related fixes can interact with hardware-specific topologies; validate patched kernels with representative workloads and monitor for regressions.
Broader context: DRM, HMM, and the long tail of kernels
This CVE is another example of how subtle arithmetic and alignment mistakes at the intersection of HMM, huge-page semantics, and driver mapping logic can produce reliability and security problems. The kernel community has seen multiple, similar classes of issues where mixed-width arithmetic, incorrect bounds, missing guards, or improper ordering of cleanup operations produced out-of-bounds writes, null-dereferences, or inconsistent page-table state. Those historical patterns explain why maintainers choose small, targeted fixes and why distributors treat the remediation as an urgent but low-risk backport candidate.A second, operationally important point is the “long tail” of vendor kernels: many embedded devices, OEM platforms, and appliance images ship customized kernel trees that do not receive immediate backports. Those artifacts can remain vulnerable long after mainstream distributions have applied upstream fixes. Operators must actively inventory devices and engage vendors for CVE backport timelines rather than assuming a platform is secure because upstream released a patch.
Practical example: a conservative remediation playbook
- Inventory — Within 24 hours:
- List all hosts with GPU device nodes: find /dev/dri -type c -ls and check for group membership and container mounts.
- Record kernel versions for each host: uname -r.
- Triage — Within 48 hours:
- Consult your distribution’s security tracker for CVE-2025-40336 mapping; note the fixed package version for each release. Debian’s tracker and OSV list mapping and commit references.
- Apply temporary udev rules to restrict /dev/dri to a trusted group for unpatched hosts.
- Patch and verify — Within 7 days (or as your change window permits):
- Schedule patching of high-priority hosts: cloud hypervisors, multi-tenant CI runners, developer build servers with GPU passthrough.
- Install the vendor kernel package containing the stable commit and reboot.
- Validate by checking dmesg for the absence of previously observed gpusvm oops traces under representative workloads.
- Confirm long-tail coverage:
- Contact vendors for appliance kernels, embedded devices, and marketplace images to confirm backport status or a compensating mitigation plan.
- Monitor:
- Add SIEM rules for gpusvm/hmm stack frames and for kernel oopses referencing mapping helpers to detect potential exploitation attempts on unpatched hosts.
What we verified and what remains unverified
Verified facts:- The CVE title, affected component (drm/gpusvm), and high-level description (fix to hmm_pfn_to_map_order usage to handle partial huge pages) appear in the NVD summary and the OSV entry.
- Distribution trackers (Debian, SUSE) have mapped the CVE to upstream commits and listed package-status data that shows vulnerable versus fixed branches.
- Public aggregated CVE mirrors (CVE Details, OpenCVE, cvefeed) reproduce the technical summary and reference the kernel commit IDs that implement the fix.
- There is no publicly confirmed report of in-the-wild exploitation or weaponization of this specific CVE at the time of the last aggregated advisories; absence of evidence is not evidence of absence. Operators should treat that as a provisional finding and prioritize remediation on exposed hosts.
- Direct review of the raw kernel diffs on git.kernel.org may be blocked by access policy in some crawlers; authoritative commit objects are referenced by trackers and should be used to validate exact code changes where necessary. Where commit hashes are needed for secure backports, use your distribution’s changelog or the kernel stable git tree to fetch commit diffs directly.
Conclusion
CVE-2025-40336 is a narrowly scoped but consequential kernel vulnerability in the DRM gpusvm mapping logic that fails to account for HMM ranges partially covering huge pages. The resulting potential for out-of-range mappings creates an availability-first risk (kernel oops, denial-of-service) and a memory-corruption primitive that should not be ignored on multi-tenant or GPU-exposed infrastructure. The upstream fix is small and deliberate, and distributors and trackers have mapped the remedy into stable kernels; operators should prioritize patching affected hosts, verify vendor backports on long-tail devices, and apply interim access controls where immediate patching is not possible. Evidence in public trackers indicates no wide-scale exploitation at disclosure, but the practical operational risk for shared systems remains high enough to warrant rapid remediation.Source: MSRC Security Update Guide - Microsoft Security Response Center