The short answer is: No — Azure Linux is the only Microsoft product Microsoft has publicly attested today to include the upstream systemd-coredump component implicated by CVE‑2025‑4598, but that attestation is product‑scoped, not an exclusivity guarantee. Any Microsoft artifact that ships or runs a Linux kernel or the systemd userspace could plausibly carry the same vulnerable code until it is verified; customers should treat un‑attested Microsoft images and kernels as unverified rather than safe.
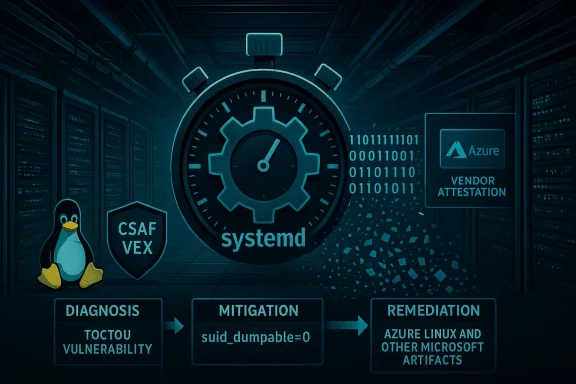
CVE‑2025‑4598 is a race‑condition information‑disclosure bug in systemd’s coredump helper. Discovered and published in late May 2025, the defect allows a local, unprivileged attacker to provoke a SUID process crash, race to reuse the crashed PID, and trick systemd‑coredump into using metadata from a non‑privileged replacement process when it decides access rights for the stored core file. If the attacker wins that millisecond‑scale race, they can read the contents of a core file written for the original privileged process — potentially exposing password hashes, in‑memory secrets, and other sensitive data. The vulnerability has been analyzed and reproduced by multiple vendor researchers and aggregator services.
This article explains the vulnerability itself, why Microsoft’s wording matters, how to interpret the Azure Linux attestation, which Microsoft products should be inspected, and pragmatic steps security teams should take now.
WindowsForum community analysis and independent commentary have repeatedly emphasized the same reading: Microsoft has authoritatively declared Azure Linux as a known carrier (so Azure Linux customers should act), but the statement is not an exclusionary technical proof for other Microsoft artifacts. Treat the attestation as a positive identification for one product, not as a negative clearance for all others.
CVE‑2025‑4598 is a reminder that modern vendor‑level transparency programs are valuable — but they do not replace per‑artifact verification. Microsoft’s attestation that Azure Linux includes the affected component is an important and actionable signal; it is also exactly that — a signal scoped to a product. Security teams should treat that attestation as a call to action for Azure Linux and as a prompt to inventory and verify any other Microsoft kernels or images in their environment. The technical fixes are straightforward (patch packages; use pidfd/%F where available), and pragmatic mitigations (disable SUID core dumps) can be deployed immediately to reduce risk while you complete updates.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CVE‑2025‑4598 is a race‑condition information‑disclosure bug in systemd’s coredump helper. Discovered and published in late May 2025, the defect allows a local, unprivileged attacker to provoke a SUID process crash, race to reuse the crashed PID, and trick systemd‑coredump into using metadata from a non‑privileged replacement process when it decides access rights for the stored core file. If the attacker wins that millisecond‑scale race, they can read the contents of a core file written for the original privileged process — potentially exposing password hashes, in‑memory secrets, and other sensitive data. The vulnerability has been analyzed and reproduced by multiple vendor researchers and aggregator services.This article explains the vulnerability itself, why Microsoft’s wording matters, how to interpret the Azure Linux attestation, which Microsoft products should be inspected, and pragmatic steps security teams should take now.
What CVE‑2025‑4598 is — a technical recap
How the attack works (short, non‑academic description)
When the kernel signals that a process has crashed, it invokes the configured userspace core‑dump handler (commonly systemd‑coredump on many modern distributions). systemd‑coredump inspects /proc/<pid> metadata (for example, the auxiliary vector in /proc/<pid>/auxv) to decide who is allowed to read the generated core file. The bug is a classic time‑of‑check / time‑of‑use (TOCTOU) window: an attacker can cause the privileged process to crash, cause the kernel to reuse the freed PID for a user‑controlled process, and — if the timing is precise — allow systemd‑coredump to read the replacement process' metadata. Because the replacement’s UID/GID and AT_SECURE flags will show a non‑privileged process, systemd‑coredump may grant read access to the core file that actually contains the crashed, privileged process memory. The result: local read access to privileged memory contents.Realistic difficulty and impact
Researchers stress that winning the race is non‑trivial — the attack window is short and requires high timing precision — but it is feasible in practice under realistic conditions, especially on busy systems or when attackers can tune PID reuse and process creation timing. The practical impact is confidentiality exposure: password hashes, keys, and other in‑memory secrets present in the crashed process can be exfiltrated. Industry trackers give the issue a moderate severity rating but flag the confidentiality impact as high if the exploit succeeds. Recommended short‑term mitigations (disabling SUID core dumps at the kernel level) are well known.Microsoft’s public statement — what it actually says
Microsoft’s Security Response Center entries for a number of Linux CVEs use a short, repeated FAQ answer when they map upstream components into Microsoft products. The wording reads, in effect: “Azure Linux includes this open‑source library and is therefore potentially affected. We began publishing CSAF/VEX in October 2025 and, if impact to additional products is identified, we will update the CVE to reflect this.” That is a clear product‑level attestation for Azure Linux and a commitment to expand machine‑readable attestations as Microsoft completes inventory work. It is not a statement that Azure Linux is the only Microsoft product that could ever include the affected code.WindowsForum community analysis and independent commentary have repeatedly emphasized the same reading: Microsoft has authoritatively declared Azure Linux as a known carrier (so Azure Linux customers should act), but the statement is not an exclusionary technical proof for other Microsoft artifacts. Treat the attestation as a positive identification for one product, not as a negative clearance for all others.
Is Azure Linux the only Microsoft product that contains systemd‑coredump?
Short answer: No — not necessarily.- Microsoft has publicly attested that Azure Linux includes the affected upstream component and is therefore potentially affected. That attestation is authoritative for Azure Linux and should be acted on by customers running that distribution.
- However, Microsoft also ships or operates other artifacts that may include Linux kernels or Linux userspace components — notably the WSL2 kernel builds, multiple Azure VM images, and Kubernetes node images used by AKS. Any of those artifacts could include a systemd userspace or a kernel configuration thatump to run. Microsoft’s attestation for Azure Linux is a first‑phase inventory result; it does not prove the absence of the component in other Microsoft products. Customers should therefore treat non‑attested Microsoft artifacts as unverified and check them directly.
Which Microsoft SKUs should you check now
Below are the Microsoft artifacts and service families that are plausible carriers — listed in descending order of likelihood and practical impact.- Azure Linux images and nodes (confirmed attestation). If you run Azure Linux, you must treat those images as in‑scope and apply the vendor patches/updates Microsoft or the Azure Linux maintainers publish.
- Azure Marketplace VM images that run distribution userland (RHEL, Fedora, CentOS derivatives, Ubuntu, Oracle Linux, etc.). These images may include systemd‑coredump as part of the distribution; Microsoft does not automatically sanitize every third‑party image. Validate the specific marketplace image/version you run.
- WSL2 kernels and WSL2 user instances. Microsoft publishes the WSL2 Linux kernel source (the microsoft/WSL2‑Linux‑Kernel repo) and ships kernels in multiple places; WSL2 distributions may run systemd in user space depending on configuration. These artifacts are plausible carriers and should be checked if you rely on WSL2 on Windows build fleets.
- AKS node images and managed node pools. AKS often uses a minimal node OS (Azure Linux is increasingly the default for AKS Automatic), and container host images may include components that handle crashes in containerized processes. If your cluster runs Azure Linux‑based nodes, it is in scope by Microsoft attestation; if you run other node images (RHEL‑based nodepools, custom images), verify those images as well.
- Any Microsoft‑maintained Linux artifacts shipped as part of appliances, hypervisor guests, or managed services (for example, the Linux kernels used inside some Azure services, partner images Microsoft curates, or any Microsoft‑distributed kernel binaries). These require case‑by‑case inventory. Microsoft has said it will update CVE attestations when it discovers additional carriers.
How to verify whether a given image or host is vulnerable
Perform the following checks on any Linux host or artifact you control:- Check if systemd‑coredump is installed or active:
- Look for the binary or package: e.g. query your package manager for a systemd‑coredump package or check for /usr/lib/systemd/systemd‑coredump, /lib/systemd/systemd‑coredump or equivalent.
- Confirm the distribution and package version and correlate with upstream advisories:
- Use vendor advisories (Red Hat, Fedora, Debian, Oracle) and the NVD to map affected versions to your installed package versions.
- Check kernel core pattern and suid_dumpable settings:
- If /proc/sys/fs/suid_dumpable is non‑zero, SUID core dumps are allowed — raising the risk surface. The known immediate remediation is to set echo 0 > /proc/sys/fs/suid_dumpable until patches are applied.
- For Microsoft images, check MSRC/CSAF/VEX attestations and the image’s SBOM if provided:
- Microsoft now publishes machine‑readable VEX/CSAF output for products it inventories; consult the attestation if one exists for the SKU you run. Absent an attestation, follow the steps above directly on the host.
Short‑term mitigations and long‑term fixes
Immediate mitigations you can deploy now
- Disable SUID core dumps until a patched package is available and deployed:
- As root: echo 0 > /proc/sys/fs/suid_dumpable
- This prevents SUID processes from generating core dumps, which blocks the attack vector even if systemd‑coredump is present. It is a blunt instrument (it prevents helpful debugging of legitimate SUID crashes) but it is effective as a stopgap.
- Remove or disable systemd‑coredump if your environment does not need it for crash analysis:
- Uninstall the package or mask the systemd‑coredump service on systems where crash collection is not required. This is operationally feasner hosts and hardened images but may impair debugging workflows.
- Limit local untrusted user ability to trigger crashes on privileged processes:
- Tighten file and execution permissions around SUID binaries and monitor for unusual local process creation patterns.
Long‑term remediation
- Apply vendor patches as soon as the distribution you run publishes them. Red Hat, Fedora, Oracle and other distro teams published fixes and backports; map those back to your image versions and deploy updates.
- Where possible, move to kernel+userspace configurations that use the pidfd/%F core_pattern protections introduced upstream; these make pid reuse attacks far less practical by passing a unique pidfd to the coredump helper rather than relying on a recycled numeric PID. Upstream kernel and systemd maintainers have documented the new parameter and systemd support for it.
Risk analysis: why Microsoft’s attestation approach is helpful — and why it can be confusing
Microsoft’s recent public commitment to publish CSAF/VEX attestations (started October 2025, per their advisory language) is a real improvement in vendor transparency for customers who run Microsoft‑curated Linux artifacts. Having a machine‑readable product mapping reduces the time security teams spend chasing down whether a given CVE affects a specific Microsoft SKU. But there are practical limitations:- Inventory‑by‑inventory rollout: Microsoft will publish attestations product‑by‑product. That means early attestations are useful but incomplete. Absence of an attestation is not proof that the code isn’t present.
- Build‑time variance: kernel subsystems and userspace packages are included or excluded based on build choices. Two images with the same vendor name may carry different vulnerable code depending on the kernel version, configuration, and installed packages. This is why per‑artifact verification is essential.
- Customer assumptions: some teams will read Microsoft’s concise MSRC sentence and assume “Microsoft scanned everything and only Azure Linux is affected.” That is a dangerous misinterpretation; the correct posture is to treat the attestation as actionable for Azure Linux and indicative for other Microsoft artifacts but not dispositive. Community analysis has repeatedly emphasized this point.
What to tell your board / procurement / operations team right now
- If you run Azure Linux: consider the Microsoft attestation a direct instruction to treat those images as in‑scope. Apply available systemd/system updates and/or implement the kernel‑level suid_dumpable mitigation immediately. Log and track the applied mitigation as part of your patch program.
- If you run other Microsoft Linux images (WSL2 kernels, Azure Marketplace OS images, AKS node images): do not assume safety. Verify whether systemd‑coredump is present and whether your image versions match any affected upstream releases; if in doubt, apply the suid_dumpable mitigation while you verify and patch.
- Document and prioritize basethat run SUID binaries you trust to contain secrets (password hashes, key material, credential managers) should be prioritized for checks and mitigations. The operational impact of losing confidentiality in those processes is higher than for many other crash scenarios.
- Request SBOMs / attestations from vendors and from your Microsoft account team for any Microsoft images you run. Microsoft has committed to expanding CSAF/VEX coverage; request early visibility for SKUs you depend on.
Caveats, open questions and monitoring
- Microsoft’s attestation language promises to update CVE pages if additional Microsoft products are identified as carriers. That process relies on internal inventories and build provenance checks; timeline and completeness depend on Microsoft’s prioritization and the complexity of artifact lineage. Customers should not use the absence of an entry as comfort.
- Some claims about exploitability and exploitation speed in public posts differ in emphasis. Multiple vendor writeups (Qualys, Oracle, distribution trackers) show exploitability is feasible but timing‑sensitive; independent proof‑of‑concepts exist but require skill. Treat practical risk as real for high‑value targets but lower for generic laptop populations — still, the remedy is simple and inexpensive relative to the potential impact, so remediation should be applied where possible.
- If you rely on WSL2 in enterprise fleets, speak to your Windows platform team: Microsoft publishes WSL2 kernel sources and ships kernels via Windows Update; whether a given WSL2 kernel build includes the vulnerable systemd userspace depends on distribution configuration inside each WSL instance and whether systemd‑coredump is active. Audit WSL instances the same way you audit full Linux hosts.
Final verdict and recommended actions (practical checklist)
- Treat Microsoft’s MSRC line — “Azure Linux includes this open‑source library and is therefore potentially affected” — as authoritative for Azure Linux, and act on that attestation immediately.
- Do NOT assume that statement means no other Microsoft product is affected. Absence of an MSRC attestation for another Microsoft SKU is not evidence of absence of exposure. Verify directly.
- For any Linux image you run (Microsoft‑supplied or otherwise):
- Check if systemd‑coredump is present.
- Check package versions against upstream advisories (Red Hat, Fedora, Debian, Oracle).
- If you cannot immediately patch, set echo 0 > /proc/sys/fs/suid_dumpable and consider removing or disabling systemd‑coredump where feasible.
- Ask Microsoft for CSAF/VEX attestations and SBOMs for Microsoft‑provided images you depend on (WSL2 kernels, AKS node images, Azure Marketplace images). Microsoft has committed to publish attestations as inventory checks complete; use these to reduce your verification workload.
- Document the remediation effort, monitor vendor advisories for updated packages and kernel features (e.g., pidfd/%F core_pattern), and plan to move to those safer configurations when they are available.
CVE‑2025‑4598 is a reminder that modern vendor‑level transparency programs are valuable — but they do not replace per‑artifact verification. Microsoft’s attestation that Azure Linux includes the affected component is an important and actionable signal; it is also exactly that — a signal scoped to a product. Security teams should treat that attestation as a call to action for Azure Linux and as a prompt to inventory and verify any other Microsoft kernels or images in their environment. The technical fixes are straightforward (patch packages; use pidfd/%F where available), and pragmatic mitigations (disable SUID core dumps) can be deployed immediately to reduce risk while you complete updates.
Source: MSRC Security Update Guide - Microsoft Security Response Center