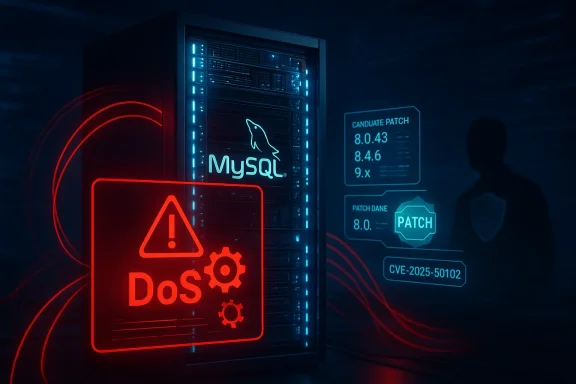
A denial-of-service weakness in Oracle’s MySQL Server optimizer — tracked as CVE-2025-50102 — affects a broad set of 8.0, 8.4 and 9.x releases and can be trivially triggered by a high‑privileged user with network access to cause repeated crashes or sustained hangs of the mysqld process, producing complete loss of availability until the server is patched or the attack is stopped.
MySQL’s July 2025 Critical Patch Update (CPU) grouped several optimizer/InnoDB issues together; among them is CVE-2025-50102, which Oracle lists as affecting MySQL Server releases in the ranges 8.0.0–8.0.42, 8.4.0–8.4.5, and 9.0.0–9.3.0. The vendor marks the issue as an availability-only impact with a CVSS v3.1 base score commonly reported as 4.9 and a vector indicating network attack vector, low attack complexity, and uired.
At a high level, public advisories and independent trackers describe the bug as an optimizer / stored-procedure handling logic flaw that can be reached over MySQL protocols and that, once invoked by an account with elevated privileges, causes uncontrolled resource consumption or internal error states that crash or hang the server. The predominant operational risk is therefore denial of service ratre or wide-ranging integrity compromise.
Independent vulnerability databases and distribution vendors corroborated Oracle’s advisory quickly and mapped vendor fixes into downstream packages, so a reliable remediation path exists — but operational realities (staged rollouts, containerized binaries, and managed services) c organizations can actually reach a fixed state.
Two practical attacker profiles should concern defenders:
If you run MySQL in production: treat this as a high‑priority operational emergency rather than a low‑priority numeric CVSS. Patch swiftly, isolate what you cannot patch, and harden privilege controls so that the “keys to the kingdom” cannot be used to weaponize availability against your services.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
MySQL’s July 2025 Critical Patch Update (CPU) grouped several optimizer/InnoDB issues together; among them is CVE-2025-50102, which Oracle lists as affecting MySQL Server releases in the ranges 8.0.0–8.0.42, 8.4.0–8.4.5, and 9.0.0–9.3.0. The vendor marks the issue as an availability-only impact with a CVSS v3.1 base score commonly reported as 4.9 and a vector indicating network attack vector, low attack complexity, and uired.At a high level, public advisories and independent trackers describe the bug as an optimizer / stored-procedure handling logic flaw that can be reached over MySQL protocols and that, once invoked by an account with elevated privileges, causes uncontrolled resource consumption or internal error states that crash or hang the server. The predominant operational risk is therefore denial of service ratre or wide-ranging integrity compromise.
Why this matters now
MySQL remains a foundational component of countless web applications, SaaS platforms, control panels, and internal tooling. Availability failures in the database layer translate rapidly into application failures, failed transactions, and costly incident responses. Even though CVE-2025-50102 requires high database privileges to exploit, that prerequisite does not make the issue safe: privileged credentials travel widely in modern estates — stored in CI/CD pipelines, embedded in container images, or accessible to automated maintenance tooling — and can be leaked, that means the practical attack surface is often significantly larger than a raw CVSS vector suggests.Independent vulnerability databases and distribution vendors corroborated Oracle’s advisory quickly and mapped vendor fixes into downstream packages, so a reliable remediation path exists — but operational realities (staged rollouts, containerized binaries, and managed services) c organizations can actually reach a fixed state.
Technical analysis: what the vulnerability does and how it can be triggered
Component, root cause, and effect
- Component: Server: Optimizer (affects optimizer and stored-procedure handling paths in MySQL Server).
- Class: Described in trackers as eiization / logic weakness (CWE‑863) or uncontrolled resource consumption (CWE‑400)* in stored-procedure/optimizer code paths that are reachable via network protocols.
- Primary impact: Availability — the attacker can cause mysqld to hang or crash repeatedly, producing a denial-of-service condition until the service is restarted or the exploit stops.
Exploit prerequisites and attacker profile
- Privileges required: High (e.g., DBA, administrative account, or similar elevated rights within MySQL).
- Attack vector: Network — exploitable over whatever protocol the affected MySQL instance exposes (classic TCP 3306, proxied connections, etc.).
- Complexity: Low once privileges are obtained — triggers orward and repeatable per vendor descriptions.
Evidence, exploitation status and threat likelihood
As of vendor disclosure and near-term follow-ups, there were no widely published proof‑of‑concept exploits demonstrating unauthenticated remote weaponization beyond crash triggers; public exploit activity and EPSS scores remained low compared with actively exploited CVEs. That said, DoS-style faults are among the easiest to weaponize when credentials are available, and automated scripts can quickly escalate nuisance impact against internet-facing instances. (feedly.com)Two practical attacker profiles should concern defenders:
- An attacker who has already obtained administrative credentials (through phishing, credential reuse, or lateral movement) and uses them to crash primary nodes or create repeatous insider or over‑privileged service account that intentionally or accidentally executes the sequence that triggers the bug.
Operational impact — where this hurts most
- Public-facing single-tenant servers with hardened admin controls: r access is tightly constrained, but still non‑zero if misconfiguration or leaked credentials exist.
- Multi-tenant and hosted-control-panel environments: high risk, because one compromised tenant or mi tool can expose administrative capability to the attacker.
- CI/CD pipelines, automation tools, and backup scripts that run with elevated accounts (mysqldump, replicat): vulnerable if those workflows carry admin credentials into places where untrusted users or CI runners might access them.
- Container images and immutable artifacts: if an image embeds a vulnerable mysqld binary, host-level package upgrades will not fix the container. Images must be rebuilt from patched bases and redeployed.
- Managed DBaaS: your provider may patch for you, but patch schedules vary — customers must confirm whether their managed instance has been upgraded to a fixed build.
Patching and mitigation: immediate, short-term and long-term steps
Oracle’s July 2025this class of optimizer/InnoDB issues; upstream releases that include the patches were rolled shortly after the CPU (typical remediation targets for operators are MySQL 8.0.43 for 8.0 line, 8.4.6 for 8.4 liater for 9.x). Downstream Linux distributors published equivalent security errata mapped to those upstream builds. Prioritize vendor packages when available rather thades where possible.Immediate actions (first 24–72 hours)every MySQL instance (including containers, images, VMs, and backups) and record the exact version string. Use package tools and container scanners.
- Reduce exposure: restrict MySQL ports (default 3306) to management subnets only, appl isolate instances that cannot be patched immediately.
- Rotate credentials: rotate any administrative credentials used by automation, backup jobs, or third‑party tools; remove unnecessary admin grants.
- Enable or increase logging: if not already enabled, enable general query and audit on) to capture any suspicious stored-procedure calls or admin actions. Preserve binary logs and error logs for forensic analysis.
al steps (next maintenance window) - Apply vendor-supplied security updates (or upgrade to patched upstream builds) on a staging replica first, then follow a controlled rollout
 te a patched replica, then patch the former primary to minimize downtime.
te a patched replica, then patch the former primary to minimize downtime. - Rebuild container images and redeploy — do not rely ackages when your service runs from immutable images.
- Harden admin access: force admin connections through bastions or VPNs with MFA, and remove any admin accounts that accept remote ghtly controlled hosts.
Long-term hardening
- Enforce least privilege for database accounts; avoid shared admin accounts and ado Improve supply-chain hygiene: require SBOMs and rebuild images on any base-image security update. Automate image scanning in CI to fail builds containing vulnerable package versions.
- Implement strong secrets management als for automation (avoid long-lived admin credentials in CI/pipelines).
Detection and forensic guidance
Signs that CVE-2025-50102 mayenvironment:- Repeated mysqld crashes or hangs, frequent restarts, or a spike in core dumps and systemd/journald error entries.
- Error-log traces with InnoDB assertions, internal aborts, or patterns of” immediately following administrative queries.
- Correlation between specific high‑privilege queries or stored-procedure invocations and crash times in binary logs. Use mysqlbinlog to i unauthorized INSERT/UPDATE/DELETE events.
- Unexplained changes to user grants, creation of new admin users, or unusual admin logins from unexpected IP addresses. Preserve lor lateral-movement correlation.
- Preservinary logs, general/audit logs, and any core dumps before performing destructive recoveries.
- Use mysqlbinlog to reconstruct statements and tie them to user accoun
- Capture a forensic image of the host if there are indications of broader host compromise; do not overwrite logs by restarting services without copying artifacts.
Step-by-step remediation playbook (prioritized)
- Run aand produce a list of all MySQL hosts and container images. Verify version strings with SELECT VERSION(); and host package querImmediately restrict access to MySQL listeners to admin subnets; block untrusted IPs at netwoalls.
- Rotate and revoke exposed or stale admin credentials and secrets stored in automation.
- If possible, stage and validate patched builds (8.0.43+, 8.4.6+, 9.4.0+) in a replica environment; run stress and replication tests.
- Patch replicas first, promote a patched replica to primary, then patch tlidate replication and post-upgrade health.
- Rebuild and redeploy any container images or clustered appliancesnerable MySQL binary.
- Monitor logs and metrics for recurrent crashes after patching; if crashes persist, capture core dumps and co
Critical appraisal: strengths, ambiguities, and residual risks
Strengths in the public response:- Oracle published the issue as part of a scheduled CPU and downstream distributors quickly mapped in patched packages; that coordination makes remediation practical for most operators.
- The vulnerability is availability-only in most authoritative descriptions, meaning confidentiality and integrity cosed on current public information.
- Different trackers occasionally present slight numeric differences in CVSS scores or nuance in integrity impact (some report a base score of 5.5 with low integrity impact, others the 4.9 score). These numeric discrepancies stem from interpretation of whether limited DML is possible and how integrity is weighted; operators should therefore prioritise the qualitative descriptions (PR:H, AV:N,meric value.
- Public advisories do not publish full exploit details (nor should they, before fixes are broadly available); the absence of public PoCs reduces immediate wormability risk but is not a substitute for patching. Exploit availability can change rapidly afterl operational risk:
- Containerized workloads and embedded binaries are the largest operational trap: system-level package updates are insufficient if the vulnerable mysqld binary is included in images that are redeployed frequently. CI/CD and image-building pipelines must be part of remediation.
- Managen varying timelines; customers should validate the provider’s remediation status and request explicit confirmation where SLAs or compliance are at stake.
Checklist: concrete am readers and sysadmins
- Inventory all MySQL servers and images; mark those in the affected ranges (<= 8.0.42, <= 8.4.5, <= 9.3.0).
- If you cannot patch immediately: restrict networ credentials, and force admin logins through hardened bastions with MFA.
- Schedule staged patching: replicas → promotion → primaries; test replication and application behavior after each step.
- Rebuild container images from patched base images; do not rely on host updates alone.
- Increase logg logs and error logs for at least the period during which remediation and forensic investigd.
- Review and reduce which accounts can create or execute stored procedures; apply least privilege.
Conclusion
CVE-2025-50102 is not a remouthenticated takeover — but it is a practical and repeatable availability weapon in the hands of atrols a high‑privilege MySQL account. That combination (widely deployed database, privileged credentials that can be exposed, and a reliable crash path) makes the issue operationally urgent for administrators who care about uptime and resilience. The good news is that vendor fixes were released as part of Oracle’s July 2025 CPU and downstream packages exist; the hard work is organizational: inventorying instances, rebuilding images, rotating credentials, and completing staged rollouts without breaking production.If you run MySQL in production: treat this as a high‑priority operational emergency rather than a low‑priority numeric CVSS. Patch swiftly, isolate what you cannot patch, and harden privilege controls so that the “keys to the kingdom” cannot be used to weaponize availability against your services.
Source: MSRC Security Update Guide - Microsoft Security Response Center