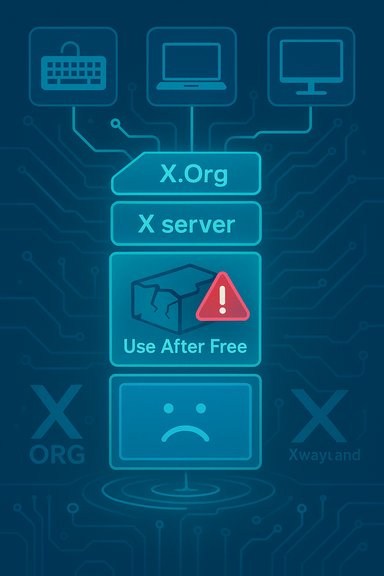
The discovery of CVE-2025-62230 exposes a long-standing but overlooked weakness in the X.Org display stack: a use‑after‑free in Xwayland’s handling of X Keyboard (Xkb) client resource cleanup that can crash or corrupt the display server and, in exposed deployments, produce durable denial‑of‑service for graphical sessions and remote desktops.
The flaw exists in the X.Org X server’s X Keyboard (Xkb) extension and specifically in the client resource removal logic used by Xwayland and other X server builds. When a client’s Xkb resources are removed, the code path in XkbRemoveResourceClient frees an XkbInterest structure while a corresponding resource reference remains attached; later, when the client fully terminates, the resource delete routine touches memory that has already been freed, creating a classic use‑after‑free (UAF) condition. The result is unpredictable memory corruption or a crash of the X server process (Xorg/Xwayland/Xvnc), with the most common, confirmed outcome being denial of graphical service for affected sessions. This vulnerability is tracked as CVE‑2025‑62230 and has been scored by multiple vendors in the high/important range (typical CVSS ~7.3) reflecting low complexity and low privilege required for a successful trigger when an attacker has the ability to send X protocol requests to the target server. The defect was disclosed during coordinated disclosure in late October 2025 and fixed upstream in the xserver tree; packaged vendor updates followed in major distributions.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
The flaw exists in the X.Org X server’s X Keyboard (Xkb) extension and specifically in the client resource removal logic used by Xwayland and other X server builds. When a client’s Xkb resources are removed, the code path in XkbRemoveResourceClient frees an XkbInterest structure while a corresponding resource reference remains attached; later, when the client fully terminates, the resource delete routine touches memory that has already been freed, creating a classic use‑after‑free (UAF) condition. The result is unpredictable memory corruption or a crash of the X server process (Xorg/Xwayland/Xvnc), with the most common, confirmed outcome being denial of graphical service for affected sessions. This vulnerability is tracked as CVE‑2025‑62230 and has been scored by multiple vendors in the high/important range (typical CVSS ~7.3) reflecting low complexity and low privilege required for a successful trigger when an attacker has the ability to send X protocol requests to the target server. The defect was disclosed during coordinated disclosure in late October 2025 and fixed upstream in the xserver tree; packaged vendor updates followed in major distributions. Why this matters: operational impact and threat model
Primary impact: availability, not (primarily) remote code execution
The immediate, verifiable consequence is availability loss — crashing the display server or its compatibility layer (Xwayland) terminates GUI sessions, forces compositors to restart, and drops remote desktop sessions served by TigerVNC, Xvnc or similar gateways. Many production environments rely on continuous graphical access (VDI, remote desktops, CI runners that spawn GUI tests, shared developer workstations), so an attacker who can reliably trigger crashes can create widespread disruption. Vendor and distribution advisories consistently treat the defect as an availability‑first vulnerability. That said, UAFs are memory‑corruption primitives that in some memory layouts and exploitation setups can be escalated into integrity or code‑execution outcomes. No authoritative vendor advisory published a confirmed remote code execution (RCE) proof‑of‑concept at disclosure; claims that this bug directly yields RCE are therefore unverified and should be treated as speculative until a demonstrable exploit appears. This distinction matters for triage: patch fast because of operational risk, but do not assume immediate privilege escalation is guaranteed.Attack vectors: local vs. network‑reachable
- Local: In default desktop installations, unprivileged local processes (including sandboxed or container guest workloads that can access /tmp/.X11‑unix or connect to a user session X socket) can create X clients and trigger the faulty cleanup sequence. Multi‑tenant desktops, shared CI runners and containerized GUI workloads are especially exposed.
- Network‑reachable: When the X protocol is exposed through remote desktop gateways (notably TigerVNC/Xvnc) or when Xwayland instances accept network connections from untrusted clients, the vulnerability becomes remotely exploitable in practice. Vendors such as Amazon (ALAS), Debian and Red Hat note this expanded risk surface and publish network‑facing mitigations for VNC services.
Technical anatomy: what went wrong
At a code level, the underlying problem is a resource lifetime mismatch in the Xkb extension implementation. The function that removes Xkb client resources frees the interest structure associated with a device but leaves the resource object (the thing that the server later uses to notify or clean up) still attached or referenced. When client teardown continues, the resource deletion path dereferences the stale pointer and acts on memory that has already been returned to the allocator — a textbook use‑after‑free (CWE‑416). The issue was present across long stretches of the X server code base and traced back into widely used branches. Upstream maintainers fixed the issue with targeted changes that ensure the resource is detached before freeing associated structures and that the cleanup path checks the pointer state defensively. The upstream fixes were merged into the X.Org xserver tree and shipped in releases such as xorg‑server‑21.1.19 and xwayland‑24.1.9 (packaging names vary by distro). Multiple independent advisories reference the same upstream commits.Who’s affected: packages and platforms
Affected components commonly identified in vendor and distribution advisories include:- xorg‑x11‑server (the upstream X.Org Server)
- xorg‑x11‑server‑Xwayland (the Xwayland builds used on Wayland compositors)
- TigerVNC/Xvnc — remote desktop servers that embed or forward X server code paths and therefore inherit the same defect in many distributions
Detection, hunting and forensic indicators
Because the practical outcome is a crash or memory corruption, detection relies on system and application telemetry:- Sudden X server or Xwayland crashes and compositor restarts correlated with client activity. Look for restart loops or repeated session drops.
- System logs: journalctl, /var/log/Xorg.*, dmesg entries showing SIGSEGV/SIGABRT originating in X server binaries. Core dumps and application backtraces are high-value artifacts for incident response.
- Remote desktop indicators: abrupt VNC disconnects immediately after client registration attempts or when specific client actions occur. If VNC services are logging client request payloads or sequence numbers, correlate timestamps to identify suspicious client behavior.
- Reproducible crash traces: if a crash reproduces deterministically with a specific client request sequence, treat that as a high‑confidence sign of an attempt to weaponize the vulnerability. Preserve logs and core dumps for vendor triage.
- Correlate X server crash times with network connection logs and process audits to identify the source client.
- Search SIEM for patterns: repeated process restarts for Xorg/Xwayland, spikes in session disconnects from VNC endpoints, or repeated unusual client request payloads.
Immediate remediation and mitigations (practical playbook)
Apply vendor patches as the first and highest‑priority action. The upstream fixes are small, surgical changes, and vendors already shipped packaged updates; installing those updates and restarting the display services or rebooting hosts will remove the vulnerability from the runtime. Confirm the package changelogs reference the upstream commit or CVE entry when possible. If you cannot patch immediately, prioritize the following mitigations:- Block or restrict network exposure to VNC/TigerVNC services. Use firewall rules to limit access to management subnets and trusted hosts; bind VNC to localhost and require SSH tunneling for remote access.
- Restrict local client access to the X server socket:
- Tighten permissions on /tmp/.X11‑unix/* so only the owning session user and trusted processes can connect.
- Use per‑session authentication (xauth) and ensure untrusted users cannot open client connections to the compositor/Xwayland socket.
- Isolate containers: do not mount host X sockets into untrusted containers; use virtual framebuffer solutions where possible.
- If Xwayland is not needed, consider disabling or removing it from images that don’t require X compatibility.
- For VNC deployments, require strong authentication and encryption; place VNC gateways behind VPNs or management proxies.
Step‑by‑step remediation checklist (recommended)
- Inventory: identify hosts running xorg, xwayland or tigervnc.
- RPM-based: rpm -qa | egrep 'xorg|xwayland|tigervnc'
- Debian-based: dpkg -l | egrep 'xserver|xwayland|tigervnc'
- For containers: inspect the image manifest or run a container and check installed packages.
- Map to vendor advisories: consult your distro security tracker (Debian DSA/DLA, Ubuntu USNs, Red Hat RHSA, ALAS, Oracle ELSA) and identify the fixed package version that applies to your release.
- Patch: apply the vendor security updates from your package manager and restart the X server components; in many cases a full host reboot ensures the patched binary is loaded. Verify the package version after update.
- Verify: validate by exercising representative GUI and remote desktop workflows in test environments and monitoring logs for unexpected crash patterns.
- Monitor: add SIEM rules to flag rapid X server restarts and repeated remote session disconnects.
- Long‑tail: identify appliances, Marketplace images, and vendor images that ship their own X server and require separate remediation or isolation.
Threat and risk analysis — strengths, limitations, and residual risk
Strengths of the remedial situation:- The upstream fix is small and targeted, making backports and packaging straightforward; major distributors issued updates quickly. This reduces the window of exposure for well‑maintained systems.
- Detection for this class of vulnerability is practical: crashes and service restarts are high‑signal events that can be tripped by relatively simple telemetry rules.
- The vulnerability’s practical severity depends on deployment topology: network‑exposed X/VNC services or incorrectly isolated containers transform a local DoS into a remotely reachable operational hazard. Numeric CVSS scores vary across vendors depending on packaging context, but the operational impact is consistent: sustained denial of service for GUI and remote desktop users.
- Long‑tail systems (embedded devices, vendor images, appliances) are often out of normal patch windows and may remain vulnerable. These devices are frequent sources of post‑patch incidents and lateral threat vectors.
- While there is no confirmed in‑the‑wild RCE at disclosure, UAFs can be valuable primitives for exploit developers — treat the integrity risk as plausible, and accelerate patching for exposed systems accordingly. Flag any claims of large‑scale exploitation as unverified absent vendor telemetry.
Developer and engineering guidance
For developers working on X clients, compositor integrations or system images:- Validate resource lifetimes rigorously: ensure that a resource’s detach/removal is atomic and that no dangling pointers remain after cleanup.
- Use safe programming idioms: check pointers after teardown, use defensive nulling of references before freeing related structures, and prefer ownership semantics that make it harder to free shared objects prematurely.
- In protocol parsing code, adopt safe arithmetic, bounds checks, and explicit maximums. While this CVE is a UAF, many related X server defects in 2024–25 were due to arithmetic/order or bounds‑checking mistakes that are easily avoided with consistent defensive coding practices.
Cross‑verification and evidence
Independent trackers and vendor advisories corroborate the technical summary and remediation timeline:- The upstream fix and commit history are documented in the X.Org xserver GitLab and were integrated into xorg‑server‑21.1.19 / xwayland‑24.1.9 releases. Public announcements and commit references were included in multiple vendor advisories.
- Distribution security trackers (Debian, Ubuntu) list fixed package versions mapped to the upstream fix and provide upgrade paths for affected releases.
- Commercial vulnerability databases and security vendors (Snyk, Rapid7, Wiz) independently summarize the defect, the CVE mapping and the recommended patch actions; these sources concur on the primary availability impact and the recommended fixes.
- The internal operational guidance and mitigation checklist included in vendor and community advisories closely matches the practical playbook operators should follow: patch, restart, restrict network exposure, and harden local socket access.
Practical timelines and operational advice
- Immediate (hours): block untrusted network access to VNC/TigerVNC endpoints and restrict remote desktop access to trusted management subnets. Harden socket permissions and restrict container access to host X sockets.
- Short term (days): apply vendor packages that include the upstream fix, restart the affected X server / Xwayland processes, and validate remediation in a controlled test window. Confirm patched package versions via rpm/dpkg queries.
- Medium term (weeks): inventory long‑tail devices, third‑party Marketplace images and embedded appliances; prioritize remediation or isolation for these artifacts. Update runbooks and SIEM detection rules to keep watch for regressions or new exploit techniques.
Conclusion: priorities for administrators and WindowsForum readers
CVE‑2025‑62230 is an availability‑first vulnerability in a mature, widely deployed graphics stack. The technical fix is straightforward and already available in upstream releases and in distributor packages. The operational imperative is clear:- Prioritize patching hosts that expose X services to untrusted clients (VDI, VNC/TigerVNC servers, multi‑tenant CI, containerized GUIs).
- If you cannot patch immediately, apply compensating controls: restrict network access, tighten socket permissions, and avoid exposing host X sockets to untrusted workloads.
- Treat any unexplained X server crashes or repeated VNC disconnects as high‑signal telemetry that requires investigation and potential isolation until systems are patched.
Source: MSRC Security Update Guide - Microsoft Security Response Center