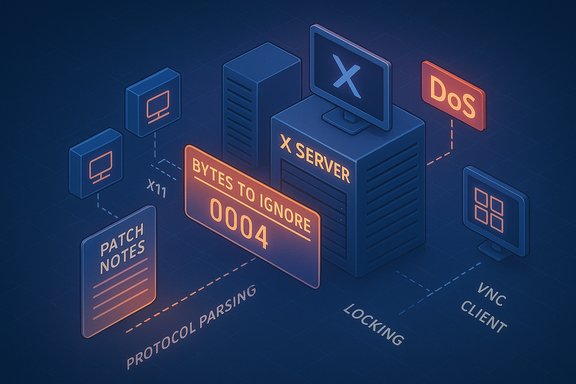
A newly disclosed vulnerability, tracked as CVE-2025-49178, allows malformed X11 protocol requests to disrupt X server request processing — a flaw that can be weaponized to produce a complete denial of service against affected X server implementations (notably xorg-x11-server, Xwayland and TigerVNC), and which has prompted rapid security advisories and vendor patches across major Linux distributions.
The X Window System (X11) remains widely used within Linux desktop stacks, remote desktop solutions, and compatibility layers such as Xwayland (the compatibility server that lets X11 clients run on Wayland compositors). Remote desktop implementations such as TigerVNC implement or interface with X server request handling to support remote graphical sessions. CVE-2025-49178 targets how the X server processes a specific part of the X11 request encoding — the “bytes to ignore” field — in a way that can lead the server to skip processing another client’s request, producing an availability failure. Vendor trackers classify the issue as an availability-focused defect; public advisories and distribution security pages have published fixes. This is not a memory-corruption exploit that directly enables code execution; the primary impact is denial of service — the attacker can crash or otherwise render the X server unusable for other clients, and in multi-tenant or remote-desktop contexts that equates to a complete loss of access for affected sessions or hosts. Multiple vendor trackers map the issue into X server and remote-VNC packages and have published fixes.
Additional telemetry — such as EPSS — indicates low but non-zero exploit prediction; public exploit activity was not widely reported at disclosure, but deterministic DoS primitives tend to be attractive in targeted disruption scenarios.
Actionable steps, prioritized:
A seemingly modest CVSS number should not lull operators into complacency; the practical outcomes — persistent denial of access to desktop sessions, mass user disruption, and potential cascading operational fallout (support tickets, halted automation, failed pipelines) — justify rapid patching in high‑availability contexts. Several vendor advisories emphasize this distinction between numeric severity and operational priority.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
The X Window System (X11) remains widely used within Linux desktop stacks, remote desktop solutions, and compatibility layers such as Xwayland (the compatibility server that lets X11 clients run on Wayland compositors). Remote desktop implementations such as TigerVNC implement or interface with X server request handling to support remote graphical sessions. CVE-2025-49178 targets how the X server processes a specific part of the X11 request encoding — the “bytes to ignore” field — in a way that can lead the server to skip processing another client’s request, producing an availability failure. Vendor trackers classify the issue as an availability-focused defect; public advisories and distribution security pages have published fixes. This is not a memory-corruption exploit that directly enables code execution; the primary impact is denial of service — the attacker can crash or otherwise render the X server unusable for other clients, and in multi-tenant or remote-desktop contexts that equates to a complete loss of access for affected sessions or hosts. Multiple vendor trackers map the issue into X server and remote-VNC packages and have published fixes. Technical anatomy — what goes wrong
X11 request structure and the “bytes to ignore” field
The X11 protocol frames client requests with a header and optional padding/extension fields. Historically, the server may accept requests containing an indicator of how many subsequent bytes should be skipped or ignored (for alignment or extension purposes). CVE-2025-49178 arises when the server’s handling of a non-zero bytes-to-ignore value results in the server advancing its internal request pointer incorrectly and thereby skipping over the next request in the queue (or losing synchronization between client streams). The skipped request can be left unprocessed or misinterpreted, causing the server to enter an inconsistent state that can be forced repeatedly to cause a denial of service.Root cause classification: improper locking / request bookkeeping
Multiple vulnerability reports characterize the underlying weakness as a logic/locking and request bookkeeping error (CWE-667 / improper locking). The server fails to correctly maintain or protect the request processing state when a client supplies a non‑zero bytes-to-ignore value; under certain sequences the server’s request dispatch loop misses processing a subsequent client request, which leads to session disruption or a crash-like failure mode for the X server process. This is not an out-of-bounds memory write or NULL-dereference exploit pattern, but a protocol parsing and synchronization failure with high availability consequences.Where the bug manifests
Affected components reported by distributors and security trackers include:- xorg-x11-server (the standard X.Org X server implementation),
- xorg-x11-server-Xwayland (Xwayland variant used when Wayland compositors host X clients),
- tigervnc (remote desktop server implementations that forward or translate X requests for VNC clients).
Severity, scoring, and vendor variance
The vulnerability has been categorized variably across vendors:- The National Vulnerability Database (NVD) and several Linux distributors report a CVSS v3.x vector emphasizing a local attack vector, low complexity, low privileges, and availability-only impact (typical vector: AV:L/AC:L/PR:L/UI:N; CVSS ≈ 5.5 in many trackers).
- Amazon Linux advisory (ALAS) lists a CVSS variant with a higher base score (6.5) and a network attack vector (AV:N) in some of its mappings — a reflection of practical exposure when TigerVNC or other remote‑access surfaces are exposed to untrusted networks. In short, when the vulnerable code persists behind a network-exposed service (for example a publicly reachable VNC server), the attack surface expands and the practical risk rises.
Additional telemetry — such as EPSS — indicates low but non-zero exploit prediction; public exploit activity was not widely reported at disclosure, but deterministic DoS primitives tend to be attractive in targeted disruption scenarios.
Attack model and exploitability
Preconditions an attacker needs
- Ability to submit X11 protocol requests to the target X server process. This can be:
- Local: unprivileged process on a shared desktop host, or
- Remote: a remote VNC/TigerVNC client if the VNC server forwards or replays raw X requests and is reachable over the network.
- Low privileges are sufficient in common desktop setups because unprivileged processes can talk to X server sockets or influence compositors; containerized workloads with /tmp/.X11-unix or /dev/dri access also increase exposure.
- No special hardware or kernel privileges are required; the flaw is in user-space X server request handling.
Typical exploitation outcomes
- Immediate session disruption: the victim’s X session freezes or the display server drops client connections.
- Persistent denial of service: attacker can repeatedly cause the server to skip requests and force further failures, often requiring a server restart or a host reboot to restore availability for all users.
- In remote scenarios where TigerVNC or similar services are exposed, the attacker may not need local access; simply connecting and sending crafted requests can trigger the condition. This is why some vendor scores model a network vector when the VNC service is exposed.
Real-world practicality
At disclosure time, public advisories did not document in‑the‑wild campaigns weaponizing this exact flaw, but the exploitation barrier is low in exposed contexts: once the request parsing behavior is known, remote or local actors can craft payloads to force the server into the skipping condition. Targets of particular concern are multi-user servers, developer CI runners that expose GUI components to untrusted jobs, virtual desktop infrastructure (VDI) and any system that offers remote graphical access to untrusted tenants.Detection and forensic indicators
Administrators and incident responders should look for the following signs that the vulnerable X server path has been triggered or abused:- Sudden termination or restart of the X server process (xorg) or Xwayland; session manager crash logs.
- Repeated X server errors in system logs (journalctl -u display-manager or dmesg/journalctl correlated with X server timestamps).
- Unexpected disconnects from VNC/TigerVNC sessions or session hangs directly following remote client activity.
- Evidence that client requests were dropped or that request processing order mismatches occurred when auditing request logs or debug traces (if X server debug logging is enabled).
Remediation and mitigation (practical playbook)
The definitive remediation is to install vendor-supplied updates that include the upstream fix and then restart the affected server components (often requiring a full session manager restart or host reboot in some configurations). Follow your distribution’s security advisory for the exact package names and fixed versions.Actionable steps, prioritized:
- Inventory and exposure mapping (Immediate)
- Identify hosts running X server, Xwayland or TigerVNC: query package managers (dpkg -l | grep xorg; rpm -qa | grep xorg; rpm -qa | grep tigervnc).
- Identify which machines expose VNC/TigerVNC ports (common ports 5900+), and which X sockets are accessible to unprivileged users (/tmp/.X11-unix/*).
- Identify containers or VMs that mount or expose X sockets or device nodes.
- Patch and verify (Highest priority)
- Update packages to the vendor fixed versions (Ubuntu, Red Hat, Amazon Linux and other vendors published fixes; install the package updates from official repos).
- Restart X server, Xwayland and TigerVNC processes; in some cases a system reboot may be recommended or required to fully clear transient state.
- Validate by exercising representative workflows (local GUI, remote VNC session), and monitor logs for errors within a validation window.
- Short-term mitigations if you cannot immediately patch
- Restrict network exposure: block VNC/TigerVNC ports at the firewall or bind VNC services to localhost and use SSH tunnels for remote access.
- Disable or stop TigerVNC / VNC services on hosts where remote graphical access is not needed: systemctl stop vncserver@: && systemctl disable vncserver@.
- Limit access to X sockets: tighten filesystem ACLs on /tmp/.X11-unix and ensure untrusted users/containers cannot connect to the display.
- Harden container runtime: drop privileges and avoid mapping X sockets or /dev/dri into untrusted containers.
- Enable stricter authentication and network isolation for remote desktop sessions (VPN-only, bastion hosts, or ephemeral session brokers).
- Monitoring and detection (Ongoing)
- Add SIEM rules for X server crashes and VNC disconnects; monitor for repeated client disconnect patterns or request-order anomalies.
- Record and retain X server logs to support triage.
- Backport or rebuild (for long-tail systems)
- For embedded or vendor kernels that cannot be upgraded via distro repos, consider building or backporting the minimal upstream patch into the local package and redeploying.
- Test any backport in a staging environment before production rollout.
Risk assessment and operational impact
Why a “medium” CVSS score can still be a critical operational problem
CVE-2025-49178 is commonly scored in the medium numeric range (CVSS ≈ 5.5) because the canonical attack vector is local and the flaw does not directly affect confidentiality or integrity. However, the real-world operational severity is driven by the availability impact: a full session or host-level disruption in a VDI, multi-tenant, or CI environment is effectively catastrophic for users and services relying on graphical session continuity.A seemingly modest CVSS number should not lull operators into complacency; the practical outcomes — persistent denial of access to desktop sessions, mass user disruption, and potential cascading operational fallout (support tickets, halted automation, failed pipelines) — justify rapid patching in high‑availability contexts. Several vendor advisories emphasize this distinction between numeric severity and operational priority.
Likelihood of exploitation
- Remote exploitation likelihood depends heavily on whether an X server‑handling component (e.g., TigerVNC) is exposed to untrusted networks.
- Local exploitation is comparatively easy in desktop contexts where unprivileged users or container processes may communicate with the X server or Xwayland.
- Public exploitation records at disclosure were sparse or non-existent, but predictable DoS primitives are attractive for adversaries targeting shared compute or interactive desktop infrastructures.
Long-tail and embedded device risk
Many embedded devices, vendor forks, and old distribution branches lag in security updates; such devices commonly run older X server packages and VNC stacks that may remain vulnerable for extended periods. These long-tail systems deserve special attention from asset inventories and remediation programs.Defensive recommendations (beyond patching)
- Apply the principle of least exposure: avoid making VNC or X server sockets network-accessible unless strictly necessary; prefer SSH tunneling or VPN access for remote graphical sessions.
- Use modern remote-desktop gateways and brokers that mediate and authenticate sessions rather than exposing raw X/TCP-based services.
- Harden multi-user desktops: isolate user sessions, restrict who can launch or control display-attached processes, and enforce strict container capability profiles.
- Maintain an accurate inventory of GUI-capable hosts, containers with display access, and remote-desktop endpoints — asset visibility is the first line of defense.
- Automate verification: include package-version checks in configuration management and vulnerability scanning pipelines so any host running an affected package is flagged and remediated quickly.
Cross-checks, verification and caveats
Independent vendor pages (Ubuntu, Red Hat/Red Hat-derived trackers, Amazon Linux Advisories) and vulnerability databases converged on the technical characterization: malformed bytes to ignore handling in X server implementations can cause skipped or misprocessed requests leading to denial of service. However, there are implementation differences and scoring disagreements across vendors — for example, Amazon’s mapping and advisories emphasize network exposure via TigerVNC, which drives a higher CVSS mapping in their advisory; many distribution trackers preserve a local-vector assessment. Operators must map the CVE to their own packaging and network topology to determine real exposure. Where vendor guidance is ambiguous or where a distribution’s security tracker lists different fixed package versions, always confirm the mapping between the CVE, the upstream commit(s) and the distribution package changelog before rolling patches widely. If in doubt, assume exposure until proven not vulnerable by package verification.What remains uncertain (flagged claims)
- Public exploit evidence: at the time of coordinated disclosure and subsequent advisories, authoritative public reports of in‑the‑wild exploitation were limited or absent. That absence should be treated cautiously: DoS primitives are often weaponized quickly once details are public. Current detection and incident telemetry should treat “no reported exploit” as provisional, not definitive.
- Exact package mappings across every Linux vendor and release: distribution-specific backports and naming differences mean the exact upgrade steps differ by distro and release. Operators must consult their vendor advisory pages or package changelogs for the authoritative fixed-package identifiers before patching production systems.
Conclusion — prioritized checklist for administrators
- Inventory immediately: identify machines running xorg-x11-server, xorg-x11-server-Xwayland, or tigervnc and determine network exposure.
- Patch and restart: apply vendor-provided updates from official repos, restart X server/Xwayland/TigerVNC, and validate session stability.
- If patching is delayed: block VNC/TigerVNC network access, bind services to localhost, restrict X socket access, and harden containers.
- Monitor for indicators: X server crashes, sudden VNC disconnects, or repeated request-order anomalies.
- Treat availability as critical: prioritize multi-tenant, CI, VDI and remote‑desktop hosts for immediate remediation.
Source: MSRC Security Update Guide - Microsoft Security Response Center