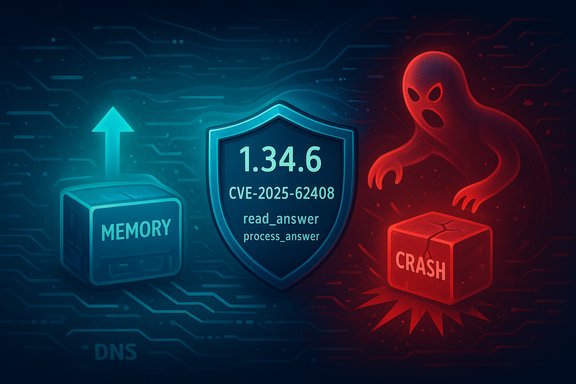
c-ares, the widely used asynchronous DNS resolver library, has a newly published Use‑After‑Free vulnerability tracked as CVE‑2025‑62408 that affects versions 1.32.3 through 1.34.5 and has been fixed in 1.34.6; the fault occurs when connection state is cleaned up after an error and can lead to process crashes and denial‑of‑service conditions.
Background
c-ares is a compact, cross‑platform C library that implements asynchronous DNS resolution and is embedded in many networked projects and language bindings. It is used as an optional dependency by libcurl and is directly consumed by some components of Node.js and other projects that need non‑blocking DNS lookup capabilities. The library supports a broad range of platforms including Linux, macOS, Windows, Android and iOS. The newly published advisory, recorded under CVE‑2025‑62408, originated from a maintainer disclosure and was summarized on the c‑ares project security advisory. The project classified the flaw as Moderate and produced a patch that is included in the 1.34.6 release. Public vulnerability trackers and open source mailing lists circulated the advisory and the upstream commit that resolves the issue. Note: the Microsoft Security Response Center (MSRC) link supplied by some users may return "page not found" or fail to render for some entries — vendor portals occasionally require a JavaScript‑enabled browser or have not mapped every upstream CVE to a Windows product page. Internal archival notes reflect similar behavior in vendor advisory pages.What the advisory says — quick facts
- Affected versions: c‑ares 1.32.3 through 1.34.5.
- Patched in: c‑ares 1.34.6.
- Vulnerability class: Use‑After‑Free (CWE‑416).
- Primary impact: Denial‑of‑Service / process crash; the advisory treats the bug as leading to a crash when extra answers are processed after the query has been terminated.
- Public exploit status at disclosure: No known in‑the‑wild exploit reported; observers caution that UAFs can sometimes be escalated to information leakage or code execution with substantial additional work.
Technical overview — how the bug works
Where the bug lives
The fault is in the DNS response handling code (the library functions commonly called read_answer and process_answer in c‑ares). The sequence goes broadly like this:- A c‑ares channel issues a DNS query and receives one or more DNS answers.
- Under certain error or termination conditions (for example, when the query hits the maximum allowed retry/attempt count), the library code will decide to terminate and clean up the query and its associated connection state.
- In the edge case described by the advisory, the cleanup path can free a connection or query object and then still allow subsequent answer‑processing logic to run against that freed object — a classic use‑after‑free condition. That dereference of freed memory can crash the process (segmentation fault) and produce undefined behavior.
Why this happened: an incomplete prior fix
The maintainers note this is effectively a missed case left over from an earlier fix (CVE‑2025‑31498). The earlier change addressed related lifetime handling but did not fully close the race/termination paths where process_answer might stop a query yet allow read_answer to continue processing additional buffered answers. This incomplete coverage enabled the new UAF scenario to persist. The maintainers fixed the logic in a focused commit that ensures the query/connection is not referenced after cleanup.What changed in the patch
The upstream commit is intentionally small and defensive: it adds the necessary checks and ordering that prevent answer‑processing from touching freed state once termination and cleanup have started. The patch was merged and included in the 1.34.6 release. The commit is available in the project repository for review and audit.Impact and exploitability — realistic assessment
Primary impact: Denial of Service
The most immediate and certain impact is crash leading to denial of service for any process that embeds the vulnerable c‑ares version and is exercising the affected code paths. Because c‑ares is typically linked into client‑side and service components, a crash can cause application downtime, application‑level errors, or process restarts in services. The advisory’s classification and independent trackers align on this being the principal, realistic consequence.Could this be escalated to code execution?
Technically, use‑after‑free vulnerabilities can sometimes be exploited for information disclosure or remote code execution if an attacker can precisely control heap layout and memory contents. However, that escalation path requires a favorable memory layout, deterministic control over the freed object’s memory, and often additional platform‑specific primitives — conditions that make such an escalation considerably harder than triggering a crash. Public reports and maintainers did not record proofs‑of‑concept for code execution at the time of disclosure, and most downstream trackers describe the realistic threat as DoS. That said, the UAF class remains attractive to advanced attackers and should be fixed promptly.Attack vector and complexity
- Attack vector: Network. The advisory metrics categorize the vector as network‑reachable because c‑ares processes responses that could arrive over a network.
- Attack complexity: Non‑trivial / High in many public CVSS mappings; the attacker typically needs to trigger very specific response/termination timing or be in a position to influence DNS answers (for example, by controlling a DNS server for a name or by a man‑in‑the‑middle). Public trackers assigned a medium overall severity in part because those environmental conditions constrain mass exploitation.
Public detection / exploitation status
At disclosure there were no public reports of active exploitation, and maintainers and public trackers stated no PoC was available. Parties analyzing the advisory flagged the absence of active exploitation but advised prompt remediation because UAF flaws are valuable building blocks for skilled adversaries.Who should care — real‑world exposure
Libraries and software that may include c‑ares
c‑ares appears as an optional or bundled dependency in several high‑profile projects and language ecosystems. Notable examples include:- libcurl: curl can be built to use c‑ares for asynchronous name resolution; many distributions and builds include c‑ares support.
- Node.js: Node’s DNS resolution architecture can interface with c‑ares (via node‑cares bindings in some builds or modules). Many Node applications and platform packages reference c‑ares in their dependency graphs.
- Other applications and embedded clients that require asynchronous DNS lookups may also bundle or link c‑ares directly; the c‑ares homepage invites users to report usage and explicitly documents broad platform support.
Distribution packages and containers
Many Linux distributions and container images provide c‑ares as a package (or as part of libcurl builds). Users running packaged distributions, containers, or bundled binaries should consult their vendor and upstream package feeds for patched versions. Container images, language runtime images and vendor SDKs that include c‑ares are possible carriers of the vulnerable library.Windows consumers
c‑ares runs on Windows and can be embedded in Windows applications (including some ports of libcurl or other networking libraries). Windows users who rely on third‑party applications that include c‑ares (for example, custom network tools, agents, or dev tools) should treat those apps as potentially affected and confirm with the vendor whether their build includes the vulnerable library. Projects that ship their own third‑party binaries — installers or self‑contained apps — may need to push updated builds.Remediation — what to do now
- Upgrade c‑ares where you directly control it: update to c‑ares 1.34.6 or later. The upstream patch is included in that release.
- For packages and OS distributions: monitor your OS or distro security feed (apt/yum/zypper/pacman) and apply the vendor’s updated c‑ares package or libcurl rebuilds that include the fixed c‑ares. Many distributions will publish updated packages rapidly when a CVE is assigned.
- For container images and runtimes: rebuild images that include the library, or pull vendor images that have been rebuilt with the fixed c‑ares. Treat base layers and runtime images as first‑class patch items.
- For third‑party software (closed‑source apps): contact vendors and request a build that includes c‑ares >= 1.34.6, or confirm that the vendor’s product is not linked against vulnerable c‑ares versions.
- Where immediate patching is difficult: consider isolating or restarting affected services proactively to clear crashed or unstable processes, and use network segmentation or firewall rules to reduce exposure until a fixed binary is deployed.
Detection and hunting guidance
- Crash logs and core dumps: look for segmentation faults or abnormal process termination in services that perform DNS queries. The easiest indicator of exploitation attempts or accidental triggers will be repeated crashes with stack traces pointing into c‑ares functions (read_answer/process_answer).
- Application logs: monitor application telemetry for unexplained DNS‑related errors or sudden denial‑of‑service symptoms at the application layer after DNS events.
- Network telemetry: unusual or repeated DNS replies that trigger client retries or retry exhaustion may be present when an attacker tries to force the maximum attempts condition; correlate client crashes with DNS traffic patterns.
- Fuzz and test: organisations that perform internal fuzzing or have test harnesses should add tests that exercise aggressive retry/termination conditions to ensure patched behavior.
Risk management — prioritization advice
- High priority: Internet‑facing services or critical infrastructure that embed c‑ares and handle untrusted DNS responses should be patched immediately.
- Medium priority: Developer machines, build agents, CI runners and developer tools that include c‑ares but are not exposed directly to untrusted networks. Patching is recommended, but operational urgency is lower than for production services.
- Low priority: Offline or isolated appliances that never perform DNS queries against untrusted servers; confirm via inventory and vendor attestations before deferring.
Practical checklist for WindowsForum readers (developers, admins, and power users)
- Inventory: grep your codebase, build scripts and binaries for c‑ares symbols or package references. On Linux, check installed packages (e.g., dpkg -l | grep c-ares) and binary dependencies (ldd on the executable). On Windows, inspect bundled DLLs and installer manifests for c‑ares or libcurl builds that include c‑ares.
- Containers and CI: ensure your CI builds pull fresh base images and that the images used for production are rebuilt after package updates. If your CI pipelines bake c‑ares into application images, trigger new builds that use the updated library.
- Node and language ecosystems: check if Node or language modules you consume depend on c‑ares (directly or via bindings). For Node apps, inspect native modules and your runtime build configuration.
- Test: after upgrading, exercise your DNS failover and retry paths in staging. Specifically test conditions that might trigger query termination on max‑attempts so you can verify the patched behavior and confirm no regressions were introduced.
Strengths of the upstream response — and remaining risks
The c‑ares project produced a focused advisory, open commit and a release that contains the fix; the change is small and easily auditable. That pattern is exactly what operators prefer for supply‑chain security: a minimal, targeted fix that can be backported or incorporated into downstream packages without large API or ABI churn. Public discussion on oss‑security and related mailing lists also provided rapid community visibility. Remaining risks to monitor:- Vendor packaging lag: downstream Linux distributions, third‑party software vendors and container image maintainers may take varying amounts of time to ship patched binaries. Until those are published and pulled, vulnerable binaries can remain in circulation.
- Embedded / statically linked consumers: applications statically linking c‑ares require vendor rebuilds — a slow remediation vector in some ecosystems.
- Unknown dependency chains: projects that vendor or copy c‑ares sources into larger repos may not be immediately obvious to maintainers, increasing the inventory effort required to fully remediate. Operators should use SBOMs and binary scanning to find all occurrences.
Final recommendations
- Upgrade immediately where you directly control the c‑ares library: move to 1.34.6 or later.
- For packaged software and distributions: apply vendor updates as soon as they are available. Track distro security feeds and container image rebuilds.
- For third‑party binaries: demand vendor attestations that shipped builds do not include vulnerable c‑ares versions, or obtain patched builds.
- Monitor application crashes, core dumps and DNS traffic for anomalous patterns; instrument staging pipelines to test the specific termination and retry paths described in the advisory.
Conclusion
CVE‑2025‑62408 is a focused use‑after‑free bug in the c‑ares DNS resolution code that can cause crashes and denial‑of‑service in processes that embed the vulnerable versions. Upstream provided a small, auditable fix in 1.34.6; the most effective mitigation is to update affected packages and rebuild any images or binaries that include c‑ares. Given c‑ares’ pervasiveness in network tooling and runtimes, the best defense is rapid inventory, prompt updating and verification of third‑party vendor builds.
Source: MSRC Security Update Guide - Microsoft Security Response Center