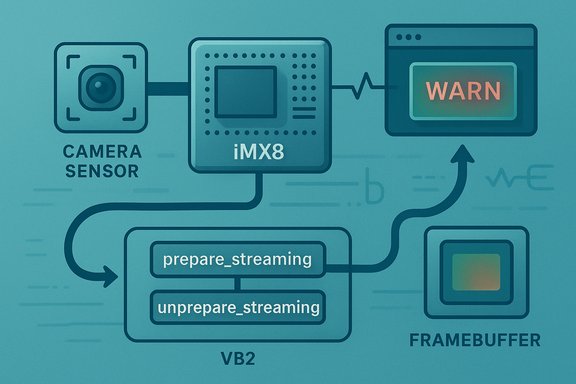
The Linux kernel has been assigned CVE-2025-68175 for a flaw in the NXP i.MX8 ISI (Image Sensor Interface) driver that can prematurely tear down an active video stream when userland issues a harmless query — a defect fixed upstream by moving streaming preparation and cleanup into the vb2 framework’s streaming lifecycle handlers. This is a correctness and availability issue in drivers/media/platform/nxp/imx8-isi that can be reproduced on i.MX8MP hardware with standard gstreamer / v4l2 tools and has been recorded in public vulnerability trackers and vendor advisories.
The i.MX8 family from NXP includes an on-chip Image Sensor Interface (ISI) used by many embedded camera and vision appliances. The Linux kernel driver for that hardware integrates with the media and V4L2 subsystems and uses the videobuf2 (vb2) helpers to manage buffer streaming. Proper lifecycle handling of streaming is essential: prepare_streaming and unprepare_streaming are the canonical vb2 hooks to set up and clean up streaming resources; other drivers follow that pattern so that streamon/streamoff and userland queries behave safely and predictably.
CVE-2025-68175 describes an implementation where the driver called mxc_isi_video_cleanup_streaming unconditionally from the device release path (mxc_isi_video_release. That unconditional cleanup meant an otherwise innocuous userland action (for example running a device enumeration or capability query via v4l2-ctl) could race with a running capture and force the streaming queue to be torn down, producing kernel warnings and IRQ-trace backtraces on affected boards. The NVD and other vulnerability databases have captured the problem description and the upstream remediation strategy.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
The i.MX8 family from NXP includes an on-chip Image Sensor Interface (ISI) used by many embedded camera and vision appliances. The Linux kernel driver for that hardware integrates with the media and V4L2 subsystems and uses the videobuf2 (vb2) helpers to manage buffer streaming. Proper lifecycle handling of streaming is essential: prepare_streaming and unprepare_streaming are the canonical vb2 hooks to set up and clean up streaming resources; other drivers follow that pattern so that streamon/streamoff and userland queries behave safely and predictably.CVE-2025-68175 describes an implementation where the driver called mxc_isi_video_cleanup_streaming unconditionally from the device release path (mxc_isi_video_release. That unconditional cleanup meant an otherwise innocuous userland action (for example running a device enumeration or capability query via v4l2-ctl) could race with a running capture and force the streaming queue to be torn down, producing kernel warnings and IRQ-trace backtraces on affected boards. The NVD and other vulnerability databases have captured the problem description and the upstream remediation strategy.
What went wrong — a technical postmortem
At a high level, the bug is a lifecycle ordering problem: the driver performed streaming cleanup from a release path that may be invoked while a queue is actively streaming. The incorrect behavior has two concrete consequences:- A userland query (for example,
v4l2-ctl -lto list capabilities) can call into the driver’s release flow in a corner case and trigger the cleanup. - The cleanup path was not safely synchronized with the active streaming path, leading to IRQ handler traces and WARN_ON messages observed in kernel logs.
- Start a capture from an ISI device with gstreamer:
gst-launch-1.0 -v v4l2src device=/dev/videoX ! video/x-raw,format=GRAY8,width=1280,height=800,framerate=1/120 ! fakesink - While streaming, invoke a userland caps query:
v4l2-ctl -l -d /dev/videoX
Key technical details
- The problematic code invoked mxc_isi_video_cleanup_streaming from mxc_isi_video_release without checking whether the queue was in a state that made cleanup safe.
- That unconditional invocation created a race between device queries/release paths and active streaming threads/IRQ handlers.
- The fix reassigns preparation/cleanup responsibilities to vb2 callbacks so the driver’s teardown is executed at the correct point in the vb2-managed lifecycle.
Evidence, verification, and what the public trackers say
Multiple independent vulnerability and distribution trackers have recorded CVE-2025-68175 and list the same issue summary and remediation approach.- The NVD entry explicitly describes the bug, reproducer, and the upstream remediation to use vb2 .prepare_streaming / .unprepare_streaming, and it links back to stable-tree commits indicated by the kernel project.
- OSV (Open Source Vulnerabilities) published a corresponding entry for CVE-2025-68175 that imports the same upstream description and lists downstream mappings (for example Debian entries) where applicable.
- Vendor/distributor pages (example: SUSE security advisory) mirror the NVD/OSV summary and the reproducer commands, confirming the public disclosure aligns with vendor guidance.
Impact assessment — who should care and why
CVE-2025-68175 is principally an availability / robustness defect rather than a direct code-execution or privilege-escalation vulnerability. Still, it carries real operational risk in multiple contexts.- Affected hardware: NXP i.MX8 family (example: i.MX8MP) where the imx8-isi driver is present and used for camera capture. Experimental reproduction was shown on i.MX8MP boards in the public advisory.
- Attack vector: local. The issue is triggered by userland operations on device nodes exposed on the host (e.g., /dev/video*). It is not a remote network attack in the native sense.
- Privilege requirement: Low to moderate — an unprivileged user able to open the device node or run standard v4l2 tools can provoke the problematic state if device node permissions are permissive.
- Primary impact: Denial-of-service (kernel WARNs, IRQ tracebacks, potential instability of streaming pipeline) and operational disruption of camera/vision workloads.
- Exploitation potential: There is no public proof-of-concept that this defect enables arbitrary code execution or privilege escalation. However, availability faults are valuable to an adversary with local foothold — used alone for disruption or combined in chains with other kernel bugs.
The upstream fix and why it matters
The upstream remediation moves streaming preparation and cleanup logic into the vb2-managed lifecycle — specifically into the .prepare_streaming and .unprepare_streaming callbacks — and removes the manual cleanup from mxc_isi_video_release. This approach:- Aligns the driver with vb2 semantics and lifecycle guarantees.
- Enables direct use of standard vb2 ioctl helpers: vb2_ioctl_streamon and vb2_ioctl_streamoff, reducing bespoke, error-prone code paths.
- Eliminates the race surface where a release path could inadvertently tear down a streaming queue.
Detection and verification steps for operators
- Inventory: Identify hosts that run on NXP i.MX8 platforms or whose kernel packages include drivers/media/platform/nxp/imx8-isi.
- Check uname -r to get the kernel version.
- Inspect your kernel configuration (zcat /proc/config.gz or the packaged config) for the imx8_isi driver.
- Log search: Look for kernel messages similar to the public trace:
- Kernel warnings originating from drivers/media/platform/nxp/imx8-isi/imx8-isi-pipe.c and messages around mxc_isi_pipe_irq_handler.
- Example pattern from the advisory: a WARN at mxc_isi_pipe_irq_handler plus the IRQ call trace observed during the reproducer run.
- Confirm patch presence:
- For packaged distributions: check your distribution’s kernel changelog or security advisory for entries referencing CVE-2025-68175 or the upstream stable commit IDs. Distributors typically document backports in package changelogs.
- For custom kernels: search your kernel git tree for the commit message or the change that moves streaming prepare/cleanup to the vb2 callbacks. When present, the code will no longer call cleanup directly from mxc_isi_video_release and will implement vb2 .prepare_streaming/.unprepare_streaming handlers.
- Test in a lab: If you can reproduce the scenario safely, validate that the sequence described in the reproducer no longer provokes WARN traces after applying the candidate patch.
Mitigations and practical remediation guidance
Primary remediation (recommended)- Apply vendor or distribution kernel updates that include the upstream stable commits that fix CVE-2025-68175.
- Reboot into the patched kernel to ensure the corrected driver is loaded.
- Restrict access to video device nodes:
- Tighten permissions on /dev/video* and associated media nodes to trusted users and services.
- Remove device node exposure from untrusted containers; do not bind host device nodes to multi-tenant workloads unless necessary.
- Avoid querying device capabilities during an active capture in automated scripts/workflows until a patch is available. In other words, sequence userland tooling to not call v4l2 device queries against a device while a capture is in progress.
- For development/test hosts, consider running camera tests on isolated CI runners where patching can be prioritized, or perform capture/query sequences serially rather than concurrently.
- OEMs and embedded integrators should backport the upstream fix into their device kernels and ship updated firmware images. The fix is small and designed to be low-risk for stable-tree backports, which vendors can adopt without major rework.
Critical analysis — strengths of the fix and remaining risks
Strengths- The upstream remedy follows standard kernel engineering practice: use framework semantics rather than ad-hoc cleanup. That reduces the likelihood of regressions and aligns the driver with the expectations of the vb2 subsystem.
- The patch is small and localized, making it easy to review and backport. Small changes are more likely to pass distribution QA and appear quickly in vendor updates.
- Public trackers and distribution advisories have propagated the CVE and mapped upstream commits to package releases, which gives operators clear remediation pathways.
- Distribution and vendor lag: The long tail of embedded devices and OEM kernels remains the largest operational risk. Many embedded appliances run vendor-custom kernels that do not receive upstream fixes promptly. Devices that cannot be updated over-the-air for policy or certification reasons may remain exposed.
- Local-exposure scenarios: Any environment that exposes /dev/video* to untrusted processes (multi-tenant build hosts, CI runners, containerized testbeds) needs to treat this as a medium-priority patch even though the attack vector is local.
- Chaining potential: While the defect itself is availability-focused, availability primitives can be combined with other issues in an exploit chain. Local Denial-of-Service remains an attractive technique for attackers with an initial foothold.
- Exact commit diffs on kernel.org were referenced by NVD, but direct retrieval of the kernel.org commit pages may fail in some constrained environments (403 responses from git web viewers were observed during validation). When direct access is blocked, rely on distribution changelogs and OSV/NVD mappings — but operators should verify commit details from kernel.org or a trusted mirror when possible.
Practical checklist: patching to monitoring
- Inventory: Create a list of devices and kernels that include drivers/media/platform/nxp/imx8-isi. Prioritize embedded devices with camera capture, CI runners used for camera testing, and multi-tenant hosts that expose media device nodes.
- Patch: Apply vendor/distribution kernel updates that reference CVE-2025-68175 or the upstream stable commit. Reboot into updated kernels.
- Monitor: Add alerts for kernel WARNs and oopses that mention imx8-isi or mxc_isi_pipe_irq_handler. Capture and retain dmesg output for postmortem.
- Harden: Restrict access to /dev/video* and avoid exposing device nodes into untrusted containers.
- Validate: In a controlled test environment, run the reproducer sequence (gstreamer capture + v4l2-ctl query) before and after patching to confirm remediation.
- Verify kernel package changelog includes CVE-2025-68175 or the upstream commit ID.
- Reboot into the updated kernel and repeat the reproducer; kernel WARNs should no longer appear.
- If reproducible errors persist, collect full kernel logs and work with your vendor to ensure the correct backport was applied.
Conclusion
CVE-2025-68175 is an instructive example of how lifecycle and ordering bugs in kernel drivers — even when small — can produce reproducible availability problems on real hardware. The upstream fix is minimal and aligns the i.MX8 ISI driver with the videobuf2 lifecycle primitives, removing ad hoc cleanup from the device release path and preventing innocuous userland queries from tearing down an active stream. Operators should treat this as a medium-priority kernel patch for affected platforms: validate whether your deployed kernels contain the fix, apply vendor or distribution updates, restrict access to media device nodes in the interim, and monitor kernel logs for related WARN messages. Public advisories (NVD, OSV) and distributor pages document the issue and map upstream commits into packaged updates; where direct kernel.org access is unavailable, those mappings and vendor changelogs are the practical sources to confirm remediation status.Source: MSRC Security Update Guide - Microsoft Security Response Center