The Linux kernel record for CVE-2025-68236 documents a narrow but important UFS (Universal Flash Storage) driver fix that prevents an over‑current protection (OCP) trip during UFS power‑down sequences by inserting a short, defensive delay after asserting hardware reset — a change that reduces the risk of regulator faults and unintended device behaviour on Qualcomm UFS host controllers used in mobile and embedded platforms.
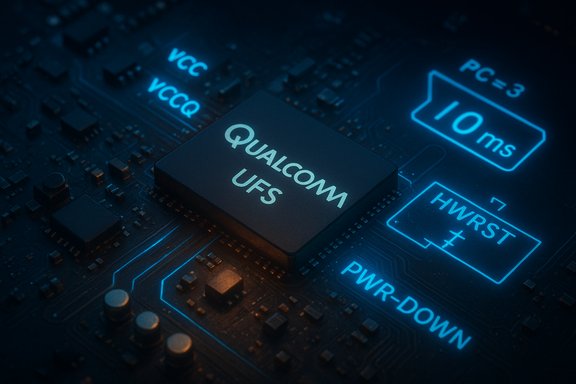
Universal Flash Storage (UFS) is a widely used storage interface on modern ARM‑based phones, tablets and many embedded systems. The UFS specification defines a strict sequence for powering a device off: send an SSU (Set Power Save) or SSU-like command with Power_Condition=3, assert hardware reset (RST_N/HWRST), stop clocks, then disable VCC and the I/O rail(s). In practice, the firmware inside a UFS device often wakes briefly when a hardware reset is asserted and performs initialization tasks that can draw a significant ICCQ (I/O rail) current for a few milliseconds. If the host driver and the regulator framework move the power rails into a low‑power mode (LPM) too quickly during that wake window, the regulator may detect a short‑duration current spike as an over‑current condition and trip OCP, causing the UFS rail to drop unexpectedly and creating hard failures during shutdown. Upstream maintainers addressed this class of problem in a small, surgical change that inserts a short delay (10 ms) after asserting HWRST (hardware reset) during the PC=3 power‑down path for Qualcomm UFS controllers. The delay allows the device firmware to complete its wake/reset routine while power rails remain active and the regulator remains in normal (higher‑current) operating mode, avoiding transient OCP trips in regulators that implement LPM transitions immediately after disable requests. The patch was merged into the stable kernel stream and cataloged by major vulnerability trackers.
Conclusion
CVE-2025-68236 is not a dramatic exploit chain, but it is an operationally meaningful fix for devices that pair Qualcomm UFS controllers with sensitive regulators. Patch affected kernels, verify vendor images, and treat this as part of routine device hardening: inventory, test, and roll out updates for embedded/mobile fleets where UFS is present.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
Universal Flash Storage (UFS) is a widely used storage interface on modern ARM‑based phones, tablets and many embedded systems. The UFS specification defines a strict sequence for powering a device off: send an SSU (Set Power Save) or SSU-like command with Power_Condition=3, assert hardware reset (RST_N/HWRST), stop clocks, then disable VCC and the I/O rail(s). In practice, the firmware inside a UFS device often wakes briefly when a hardware reset is asserted and performs initialization tasks that can draw a significant ICCQ (I/O rail) current for a few milliseconds. If the host driver and the regulator framework move the power rails into a low‑power mode (LPM) too quickly during that wake window, the regulator may detect a short‑duration current spike as an over‑current condition and trip OCP, causing the UFS rail to drop unexpectedly and creating hard failures during shutdown. Upstream maintainers addressed this class of problem in a small, surgical change that inserts a short delay (10 ms) after asserting HWRST (hardware reset) during the PC=3 power‑down path for Qualcomm UFS controllers. The delay allows the device firmware to complete its wake/reset routine while power rails remain active and the regulator remains in normal (higher‑current) operating mode, avoiding transient OCP trips in regulators that implement LPM transitions immediately after disable requests. The patch was merged into the stable kernel stream and cataloged by major vulnerability trackers. What exactly went wrong (technical summary)
- The UFS driver’s power‑down sequence follows the UFS specification: SSU (PC=3) → assert RST_N (HWRST) → stop clocks → disable VCC → disable VCCQ/VCCQ2.
- Asserting HWRST causes the device firmware to wake, initialize hardware blocks, and in doing so briefly draw elevated ICCQ current — observed as a multi‑millisecond transient on some UFS devices.
- The kernel’s regulator framework, upon receiving a disable request from its only client (the UFS driver), may transition rails into LPM quickly; if the rail’s LPM current threshold is lower than the firmware’s transient ICCQ, the regulator can interpret the transient as an overcurrent condition and engage OCP.
- The result is a cascading hardware/regulator reaction: the OCP trip can remove power or otherwise distort the expected shutdown flow, possibly leaving the controller or device in an inconsistent state or causing a hard failure during power‑down transitions.
The upstream fix — what changed in code and why it works
The patch series added an explicit sleep of approximately 10 milliseconds immediately after asserting HWRST in the affected power‑down path for ufs‑qcom. The rationale is pragmatic: there is no reliable host‑side mechanism (the UFS spec provides no way for the host to query “reset complete”) to know precisely when the device’s internal reset routine has finished. The 10 ms delay is conservative and based on empirical testing across several Qualcomm UFS controllers and UFS device vendors; it gives the device time to finish reset‑related initialization while keeping the power rails in normal mode, thereby avoiding LPM-induced OCP activation. Why a short delay is preferable to a more complex handshake:- The UFS standard does not define a query for reset completion, so any handshake would be vendor‑specific.
- A 10 ms delay is tiny in terms of user‑visible latency during shutdown or suspend, but large enough to cover observed device reset wakeup profiles.
- The change is localized, low‑risk, and easy to backport to stable kernels and vendor trees, which accelerates remediation for embedded device vendors and distributions.
Platforms and products likely affected
This fix targets the ufs‑qcom glue/host driver used with Qualcomm controllers. Consequently, the highest‑risk systems are those that:- Ship with Qualcomm UFS host controller drivers compiled in or as modules. These typically include Android phones, SoC‑based tablets, and a range of embedded devices.
- Use regulators whose low‑power mode transitions may be triggered immediately upon the last client disable and where LPM current thresholds are relatively low.
- Run vendor kernels or OEM images that are on bespoke maintenance schedules (long tail exposure). Cloud images that include Linux kernels built for ARM boards or embedded appliances could also be affected if they include the ufs‑qcom code path.
Severity, exploitability, and operational risk
- Classification: Hardware‑timing / availability issue (DoS/hard failure) rather than a software privilege escalation or data disclosure vulnerability.
- Remote exploitability: None — the condition stems from power‑down timing and hardware behaviour, not from a remotely reachable software interface.
- Likelihood: Platform‑dependent. Devices whose regulators and UFS firmware combine to create the ICCQ spike window are at greatest risk. The bug requires specific hardware + timing conditions; it is most likely to appear on embedded/mobile devices using Qualcomm UFS hosts.
- CVSS / scoring: At the time of upstream cataloging, the public trackers show the entry without a pervasive CVSS score; operational triage should prioritize based on device criticality and exposure rather than raw numeric scores. Treat it as a medium‑operational‑impact problem for affected UFS platforms.
Detection, verification, and triage steps for administrators
System owners should treat this as an inventory, verify, and patch mission. Concrete steps:- Inventory UFS presence
- Check running kernel and config: uname -r; zgrep CONFIG_UFS /proc/config.gz (or check /boot/config-$(uname -r).
- Check modules: lsmod | grep ufs; modinfo ufs-qcom (or ufshcd).
- If UFS is built into a vendor kernel, review the vendor package changelog or kernel config in the image.
- Map your kernel package to the upstream fix
- Look for the stable commit IDs mentioned in public trackers and vendor advisories. The upstream patch is referenced in stable kernel updates (see stable commit metadata). Confirm whether your distribution’s kernel package changelog contains the fix or the relevant commit ID.
- Reproduce (lab) and monitor
- If you have representative hardware, reproduce power‑down sequences and monitor regulator logs, dmesg, and watchdog traces during suspend/shutdown transitions.
- Instrument regulator debug (if available) and kernel debug prints around the UFS power‑down path to capture LPM/OCP transitions.
- If you cannot reproduce, assume potential exposure until the kernel package is confirmed fixed.
- Short‑term mitigations (if you cannot patch immediately)
- Avoid workflows that cycle the UFS controller’s power rails in-situ on production devices; schedule maintenance windows to apply updates.
- If the platform permits it, coordinate with the power‑management/regulator vendor to adjust LPM thresholds or introduce a firmware/regulator workaround — this is vendor‑dependent and often impractical for fleet‑wide rollouts.
- Consider isolating affected hardware from critical workloads until the kernel or vendor firmware is updated.
Remediation guidance and rollout plan
- Identify the fixed kernel packages
- Use distribution security trackers and package changelogs to find kernels that include the upstream fix (stable patch). Where stable commit IDs are listed, map them to your kernel package. Upstream lists and VEX/CSAF attestations help confirm which vendor artifacts include the fix.
- Test in a controlled ring
- Deploy the patched kernel to a test ring of devices with the same UFS controller and regulator combination as production to validate that the fix removes the OCP symptoms without introducing regressions.
- Roll out staged updates
- Patch critical production fleets first (devices running on battery‑sensitive or regulator‑sensitive hardware), then broader fleets. Ensure you track rollback plans in case of regression.
- Vendor coordination for embedded devices
- For OEMs and embedded vendors that ship long‑tail kernels, request backports and provide test cases demonstrating the OCP behaviour if necessary. The upstream change is small and low‑risk to backport, so vendors should be able to provide updates quickly.
- Validate after update
- After installing fixed kernels, repeat shutdown/power‑down tests and monitor for any recurrence of regulator OCP events. Confirm that devices complete shutdown smoothly and that kernel logs no longer show power‑management anomalies tied to UFS power‑down.
Why the upstream approach is sound — strengths and tradeoffs
Strengths- The change is minimal and conservative: a timed delay is simple to reason about, easy to test, and straightforward to backport into stable vendor kernels and long‑term maintenance branches.
- It avoids introducing fragile, vendor‑specific handshakes or speculative polling code that could complicate the UFS host driver or violate the portability principles across UFS device vendors.
- The fix is low‑risk for regressions because it does not change normal operational paths — it only delays the rail shutdown slightly during reset, a safety margin that avoids trips without observable functional impact for users.
- The guard is empirical: the 10 ms value is conservative and based on observed behaviour across tested controllers, but it is not a formal standard‑backed handshake. Very unusual devices with longer reset wake times could, in theory, still misbehave; conversely, devices with tight power windows may see a slight extra latency during shutdown.
- The fix relies on a delay rather than a deterministic signal from the device; it is therefore a mitigation that trades a small timing overhead for much greater robustness.
- Vendor and OEM lag remains the primary operational risk: many embedded devices, OEM Android kernels and appliance images follow bespoke patching schedules. Even though the upstream patch is small and easy to backport, real‑world fleets may remain exposed until vendors publish updates and images.
Operational checklist (concise runbook)
- Inventory devices:
- uname -r
- zgrep CONFIG_UFS /proc/config.gz || cat /boot/config-$(uname -r) | grep -i UFS
- lsmod | grep -E 'ufs|ufshcd|ufs_qcom|ufs-qcom'
- Verify package changelogs for the stable commit ID or explicit CVE reference.
- For test devices: perform repeated shutdowns and power cycles while collecting dmesg and regulator debug logs; compare results before and after the kernel update.
- If needed, apply temporary mitigations (isolate device, avoid power cycling during critical windows).
- Contact OEM/vendor support for firmware/regulator adjustments if the kernel update cannot be applied promptly.
Cross‑validation and sources of record
The technical description of the issue and the fix is recorded in public vulnerability registries and mirrored in the stable kernel update announcements. The NVD entry explains the power‑sequence context and the rationale for the 10 ms delay; the stable kernel patch list and auto‑sel patch mailings reference the upstream commits that implement the change; OSV and other vulnerability aggregators reflect the same mapping. These independent points of record allow operators to map package changelogs and vendor advisories back to the upstream commits for verification. Note: some vendor advisory pages (for example cloud‑vendor CVE pages or MSRC records) may render dynamic content or require artifact‑level attestation; administrators should verify per‑image and per‑artifact rather than assuming a global vendor “not affected” statement. Practical verification must be done at the image/kernel package level.Final analysis — practical takeaways for WindowsForum readers
- The root cause is power‑management timing in the UFS shutdown sequence, not a conventional software security exploit. The fix is a small, practical mitigation (10 ms delay after HWRST) that improves hardware compatibility and prevents regulator overcurrent trips on Qualcomm UFS hosts.
- Real danger is to embedded and mobile fleets where shutdown timing and regulator LPM behaviour vary across vendors. Desktop/server fleets without UFS hardware are not impacted.
- Remediation is straightforward in principle — install kernels that include the upstream stable commit — but the real challenge is the operational rollout across vendor‑maintained images and long‑tail embedded devices.
- Administrators should prioritize inventory, verify kernel package changelogs for the specific commit or CVE mapping, test on representative hardware, and coordinate with OEMs where kernel updates are not under direct control.
Conclusion
CVE-2025-68236 is not a dramatic exploit chain, but it is an operationally meaningful fix for devices that pair Qualcomm UFS controllers with sensitive regulators. Patch affected kernels, verify vendor images, and treat this as part of routine device hardening: inventory, test, and roll out updates for embedded/mobile fleets where UFS is present.
Source: MSRC Security Update Guide - Microsoft Security Response Center