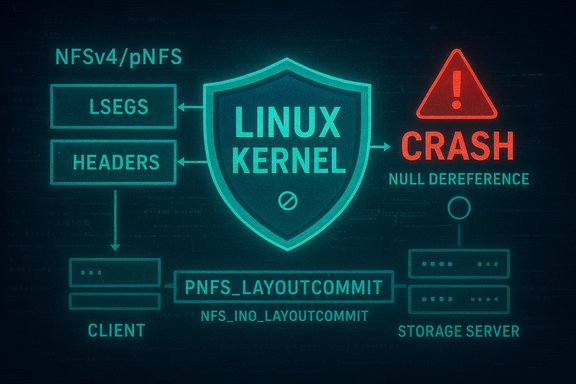
A recently assigned CVE, CVE-2025-68349, identifies a stability flaw in the Linux kernel’s NFSv4/pNFS client code where a missing flag clear can let the kernel attempt to reference a null layout during layoutcommit handling — a condition that causes a kernel crash and creates a local denial-of-service (DoS) risk for systems using pNFS.
Background
Parallel NFS (pNFS) is an extension to NFSv4 that lets clients obtain layouts and perform IO directly against storage devices (data servers) while the metadata server coordinates state. The pNFS architecture relies heavily on reference counting and internal flags so that layout segments (lsegs) and layout headers remain valid across asynchronous operations such as layoutget, layoutreturn and layoutcommit. When internal flags and reference counts get out of sync, the client code can attempt to dereference objects that have been freed — yielding NULL-pointer accesses and kernel oops/panics. The kernel’s pnfs core and layout drivers therefore must carefully manage flags and counts to maintain integrity. In mid‑December 2025 the Linux project assigned CVE‑2025‑68349 to a bug described as “NFSv4/pNFS: Clear NFS_INO_LAYOUTCOMMIT in pnfs_mark_layout_stateid_invalid.” The publicly-available writeup explains that when a layout becomes null during a particular call chain, the code can still have an inode-level flag set (NFS_INO_LAYOUTCOMMIT) that signals a pending layoutcommit; later logic relies on the layout pointer being non-null and tries to access layout fields, causing a crash.What happened (technical summary)
- The faulty sequence is triggered when an inode that previously had a layout loses that layout (the nfsi->layout pointer becomes NULL), but the inode flag NFS_INO_LAYOUTCOMMIT is still set. That flag indicates a pending layoutcommit work item for the inode.
- If a write (or other operation) ends up invoking pnfs_layoutcommit_inode while NFS_INO_LAYOUTCOMMIT remains set but the layout pointer is NULL, the layoutcommit logic tries to access nfsi->layout without guarding for NULL and dereferences it — causing a kernel oops or panic.
- The upstream fix is to ensure that, in the path that marks a layout/stateid invalid (pnfs_mark_layout_stateid_invalid), the inode-level NFS_INO_LAYOUTCOMMIT flag is cleared when the layout is being invalidated so that subsequent attempts to perform layoutcommit will not proceed against a NULL layout. This avoids referencing freed data structures and prevents the crash.
Why this matters
- Impact: This is primarily an availability issue. A kernel crash in the NFS client yields a denial-of-service condition for the host or virtual machine running the affected kernel, which can be disruptive on storage‑heavy systems such as HPC clusters, virtualization hosts, or networked file servers consuming pNFS. Vendor assessments have given the issue a moderate severity rating and a CVSS base score consistent with a local DoS vector (SUSE lists CVSS 5.5 with AV:L/AC:L/PR:L/UI:N and Availability impact High).
- Attack surface: The vulnerability is local — an attacker must be able to execute operations that trigger the affected NFS client code path on the vulnerable host. This means untrusted local accounts or processes that can perform IO to the affected NFS mount have the most realistic chance to trigger the condition. The report does not indicate remote code execution or confidentiality/integrity compromise; it focuses on a crash condition.
- Exploitability: The code path and fix descriptions show the problem is a logic/flag-management flaw rather than a complex memory corruption or privilege escalation primitive. That makes triggering a crash plausibly easy for a local actor with write access to the right NFS mount or by causing a layout state transition at an unfortunate time. Public risk-scoring sources and vulnerability aggregators show low EPSS/exploit probabilities so far, but the local DoS risk is real for affected deployments.
Deeper technical analysis
How pNFS layoutcommit works (concise)
pNFS tracks which layout segments need a layoutcommit using a combination of per-inode flags (e.g., NFS_INO_LAYOUTCOMMIT, NFS_INO_LAYOUTCOMMITTING) and per-lseg flags. When writes occur that require a layoutcommit, pnfs_set_layoutcommit is invoked and relies on lsegs maintaining a refcount so that the layout header remains valid until the commit finishes. The layoutcommit code assembles a layoutcommit RPC payload by iterating the in‑flight lsegs and reading state from the layout header. If the layout header pointer (nfsi->layout) is NULL at that time, the logic must never assume it exists.Root cause: flag vs. reference-count mismatch
The immediate bug is a mismatch between flag state and object lifetime. pnfs_set_layoutcommit expects the presence of lsegs and their reference counts to keep the layout header alive across the asynchronous layoutcommit path. However, in a race or error path where pnfs_mark_layout_stateid_invalid removes or nulls the layout, the inode’s NFS_INO_LAYOUTCOMMIT flag was left set. Later a caller checks the inode flag and proceeds into pnfs_layoutcommit_inode, which then dereferences nfsi->layout unguarded. The right fix, adopted upstream, is to clear NFS_INO_LAYOUTCOMMIT in pnfs_mark_layout_stateid_invalid so the post‑invalidated inode no longer indicates that a layoutcommit is pending. That prevents pnfs_layoutcommit_inode from running against a null layout.Why the fix is correct and conservative
- Clearing the inode-level flag at the point where the layout is invalidated is conservative: it avoids starting a layoutcommit when the layout is gone.
- The change reduces the chance of dereferencing freed layout header state while still preserving the reference-counting discipline of lsegs when they are valid.
- This approach addresses the immediate crash without a heavy redesign of layout commit semantics; it is a minimal, targeted change to restore consistent state in the presence of layout invalidation.
Confirmations and sources
The vulnerability record and fix summary are visible in multiple vulnerability trackers and distribution trackers. OSV and other vulnerability aggregators list CVE‑2025‑68349 and describe the same call stack (write_inode -> nfs4_write_inode -> pnfs_layoutcommit_inode) and the core cause (not clearing NFS_INO_LAYOUTCOMMIT when layout gets null). Distribution trackers (SUSE, Debian) have added entries or action items reflecting the issue and are treating it as a kernel fix to be applied. The upstream kernel stable tree contains commits addressing pNFS layoutcommit handling consistent with this description.Practical impact for WindowsForum readers and mixed environments
Even though this is a Linux kernel issue, Windows shops and mixed OS environments often rely on NFS storage appliances (NetApp, ONTAP, vendor storage clusters) that serve NFS clients running Linux. If you manage Linux guests, hypervisors, NAS appliances, or shared storage nodes that use pNFS, this CVE matters:- Hosts acting as NFS clients and using pNFS could crash under normal workload conditions if they hit the layoutcommit path at the wrong time.
- Storage vendors that implement pNFS on appliances (ONTAP, NetApp, dCache and others) may provide controls to disable pNFS or to force proxy mode so clients always go through the metadata server rather than direct pNFS IO. Temporary configuration changes on appliances may reduce exposure until kernels are patched.
Detection and triage steps
- Identify potentially affected systems:
- Run uname -r to see kernel versions on Linux clients, hypervisors, and storage nodes.
- Check whether NFS mounts are using NFSv4.1/4.2 and pNFS (client mounts may include a pnfs option or the server can present layouts). Example: examine /proc/mounts and system mount options or nfsstat output.
- Inspect logs for kernel oopses containing NFS/pnfs strings:
- Check dmesg or the system journal for recent NFS/pnfs-related oopses or stack traces. Grep keywords such as pnfs_layoutcommit, pnfs_layoutcommit_inode, pnfs_mark_layout_stateid_invalid or NFS_INO_LAYOUTCOMMIT.
- Example commands: dmesg | grep -i pnfs ; journalctl -k | grep -i pnfs.
- Reproduce carefully in a test environment:
- If you can reproduce the layout state transitions in a controlled test cluster, capture kernel logs and backtraces. Do not attempt aggressive faulting on production systems.
- Consult your distro and vendor advisories:
- Because kernel updates and backported fixes vary by vendor, always check your Linux distribution’s security tracker and vendor bulletins to determine which kernel package contains the backport for your platform. Distribution packages may carry the patch in different kernel tree versions.
Short-term mitigations
- Patch and update: The recommended action is to apply updated kernel packages from your Linux distribution once they are available and validated for your environment. This is the safest and most reliable mitigation.
- Disable or limit pNFS where feasible:
- On clients, you can avoid negotiating pNFS by mounting without pNFS support (for example, force NFSv4.0 or ensure the client does not request layouts); the exact mount options vary by client and distribution. The mount(8)/mount.nfs manual documents the pnfs-related mount option; explicitly disabling pNFS or forcing proxy-mode on the server can prevent clients from receiving layouts that trigger the problematic code path. Test performance and behavior before applying in production.
- On storage appliances that support server-side pNFS toggles, administrators can disable pNFS or enforce proxy mode until clients are patched. Appliance-specific commands (e.g., ONTAP vserver nfs modify -v4.1-pnfs disabled) control this behavior on vendor platforms. This may impact performance.
- Reduce local-risk exposure:
- Restrict untrusted local accounts’ ability to touch NFS mounts.
- Revoke unnecessary write access from service accounts that do not need write privileges on pNFS mounts.
Recovery steps if you hit this crash
- Capture the system console and kernel logs immediately (kmsg, journalctl, dmesg).
- If the host panicked, collect the vmcore (kexec/kdump) if configured — these artifacts help developers confirm the crash frame and validate the fix.
- Reboot into a patched kernel as soon as a validated update is available.
- For critical storage nodes, consider switching workloads to failover nodes while you remediate to reduce service disruption.
Vendor and distribution handling
At time of writing multiple vulnerability aggregators and distribution trackers show CVE-2025-68349 in their lists and refer to patches in the upstream stable kernel tree. However, package availability and exact fixed kernel package versions vary by distribution. Vendors maintain different backport policies: some apply the upstream fix to current stable kernels, others backport to long-term support kernels and enterprise kernels with different version numbers. Always verify with the vendor advisory for your distribution before applying updates to production systems. Because the upstream commits are in the stable kernel trees, many vendors will provide a patch quickly, but the timeframe and package names will differ. If you manage mixed Linux fleets, coordinate update windows carefully and use staged rollouts with testing.Risks and limitations of the fix
- The upstream fix is narrowly scoped and prevents the kernel from attempting a layoutcommit when the layout pointer is NULL by clearing the inode flag at layout invalidation time. The change is conservative and removes the immediate crash trigger.
- However, this is a fix for a state‑consistency bug, not a design change to the pNFS reference-counting model. That means other races or logic lapses elsewhere in pNFS could manifest in future; ongoing testing and fuzzing of pNFS layout state transitions remain necessary.
- The fix eliminates the crash scenario described in the CVE, but administrators should still plan for broader pNFS testing: layout state transitions are complex, especially across multiple storage devices and when combining NFSv4.1/4.2 or vendor-specific extensions. Rigorous QA is recommended before re‑enabling pNFS after patching.
Recommendations (action checklist)
- Inventory: Identify all Linux systems and appliances that use NFSv4.1/4.2 and pNFS (clients, hypervisors, NAS appliances). Use uname -r, /proc/mounts, and nfsstat to locate mounts.
- Monitor: Watch kernel logs for pnfs_layoutcommit or NFS-INTERNAL oops messages; set alerts on repeated NFS kernel oops signatures.
- Patch: Apply vendor-supplied kernel updates that include the upstream fix as soon as they are available and validated.
- Mitigate: If immediate patching is not possible, consider disabling pNFS on storage appliances or mounting without pNFS on clients (proxy mode), after testing the performance impact.
- Harden local access: Limit who can run code or services that perform IO against NFS mounts; untrusted local accounts are the primary threat vector.
- Post-patch validation: After patching, run workload tests that exercise layoutgets/layoutcommits/layoutreturns and monitor for stability.
Final analysis and takeaways
CVE‑2025‑68349 is not a remote privilege-escalation or data-exfiltration vulnerability; it is a logic bug that can cause the Linux kernel to crash when pNFS layoutcommit code is invoked with an inconsistent internal state. The fix — clearing an inode-level layoutcommit flag when the layout state is invalidated — is straightforward and reduces the immediate DoS risk. Administrators running pNFS in production should treat this issue as actionable: prioritize kernel updates on NFS clients and evaluate temporary server- or client-side configuration changes to guard against layout-driven crashes. Mixed Windows/Linux environments that rely on Linux clients for shared storage must coordinate vendor advisories and test the impact of disabling pNFS on performance before applying workarounds. Until patched kernels are in place, reducing the attack surface by limiting local untrusted access and avoiding pNFS where it is not strictly required are reasonable interim steps. Caveat: the upstream commit references and vendor backport details have been published in kernel and distribution trackers, but exact fixed package version numbers vary by distribution and vendor. Confirm the presence of the fix in your kernel package by checking your vendor advisory and the distribution kernel changelog before assuming systems are remediated.The core lesson: complex distributed filesystem features like pNFS improve throughput but increase state-management complexity. Even small mismatches between flags and object lifetimes can produce system-wide availability problems. Keep systems patched, monitor kernel logs, and apply functional fallbacks (proxy mode / pNFS disable) when life‑cycle critical stability is more important than raw performance.
Source: MSRC Security Update Guide - Microsoft Security Response Center