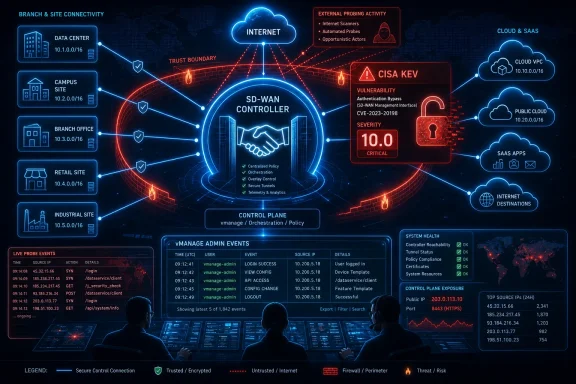
On May 14, 2026, CISA added CVE-2026-20182, a Cisco Catalyst SD-WAN Controller authentication bypass vulnerability, to its Known Exploited Vulnerabilities Catalog after evidence showed the flaw is being actively exploited in the wild. The move is not just another entry in a federal spreadsheet. It is a warning that attackers are still treating network control planes as the shortest path to enterprise-wide leverage. For Windows shops, cloud teams, and branch-heavy organizations, the lesson is blunt: the security perimeter is increasingly wherever your network controller accepts trust.
CISA’s latest KEV addition lands with the dry phrasing typical of federal vulnerability alerts, but the substance is anything but routine. CVE-2026-20182 affects Cisco Catalyst SD-WAN Controller and, according to Cisco’s advisory, carries the maximum CVSS severity score of 10.0. Cisco says the vulnerability sits in control connection handshaking and can affect Catalyst SD-WAN Controller and Catalyst SD-WAN Manager across deployment types, including on-premises, Cisco-managed cloud, Cloud-Pro, and government cloud environments.
That breadth matters. SD-WAN is not an edge feature bolted onto the network for convenience; in many enterprises it is the coordination layer that decides how branches, data centers, cloud workloads, and remote sites talk to one another. A bypass in that layer is more consequential than a bug in a single appliance because the attacker is aiming at policy distribution, not merely packet forwarding.
CISA’s decision to put the flaw into the Known Exploited Vulnerabilities Catalog means federal civilian agencies must treat it as an active operational risk, not a theoretical one. BOD 22-01 created the KEV catalog to force remediation of flaws that attackers are known to use, and it has become one of the clearest public signals for private-sector prioritization as well.
The timing also gives the alert extra weight. CISA did not publish this in isolation; it explicitly tied the warning to Emergency Directive 26-03 and supplemental hunting and hardening guidance for Cisco SD-WAN systems. That is federal-speak for “do not merely patch and move on.”
CVE-2026-20182 is described by Cisco as a new vulnerability discovered and fixed after the February 2026 disclosure. That phrasing matters because it tells defenders this is not merely an administrative update to the old advisory. It is a fresh defect in the same strategic neighborhood: authentication, control connections, and the trust relationships that allow SD-WAN components to coordinate.
The difference between endpoint compromise and controller compromise is the difference between breaking into an office and obtaining the building’s master access system. An attacker who can abuse controller authentication is not simply hoping to land on one host and move laterally the old-fashioned way. They may be able to influence the network’s own machinery for connectivity, reachability, and persistence.
That is why the KEV entry should not be read as “Cisco customers have a patching chore.” It should be read as “attackers are probing the management fabric that modern enterprises use to make distributed infrastructure manageable.” The convenience layer has become the blast-radius layer.
That is simple in a boardroom and messy in production. SD-WAN controllers are often woven into maintenance windows, carrier dependencies, branch uptime commitments, and change-control processes built to avoid outages. The result is a classic enterprise dilemma: the systems most painful to patch are often the ones attackers most want to own.
CISA’s language anticipates that tension. The agency urges adherence to Emergency Directive 26-03 and supplemental guidance, and it says organizations should follow BOD 22-01 guidance for cloud services or discontinue use of the product if mitigations are not available. That last clause is severe, but it reflects the reality of exploited authentication bypasses. If you cannot patch, isolate, or prove safety, continued exposure becomes an accepted risk rather than an unresolved ticket.
The practical challenge for IT teams is that SD-WAN often sits between networking, security, and infrastructure operations. The group that owns the controller may not own the vulnerability management platform. The group that can see suspicious identity events may not understand SD-WAN peering. The group that can approve emergency changes may not understand why a controller flaw deserves faster treatment than a domain workstation vulnerability.
This is where governance either works or collapses. A KEV listing gives security teams the leverage to force prioritization, but it does not magically create asset inventories, change windows, tested rollback plans, or executive appetite for emergency upgrades.
But mature defenders should not stop at the public-facing inventory. SD-WAN management planes are often reachable from administrative networks, cloud segments, jump hosts, VPN pools, monitoring systems, and automation platforms. Those paths may not show up in a naive external scan, but they can become reachable after a smaller intrusion elsewhere.
This is where Windows-heavy enterprises have a particular stake. Many environments still center identity, administration, logging, and incident response around Active Directory, Entra ID, Windows Server jump boxes, PowerShell automation, and endpoint management tooling. If the network control plane is reachable from those administrative zones, a compromise in one domain can become the staging ground for an attack on the SD-WAN fabric.
The reverse is equally troubling. If an attacker reaches the SD-WAN controller first, they may gain insight into site topology, management addresses, routing behavior, and trust relationships that help them target Windows infrastructure more precisely. Even without a direct exploit chain into Windows hosts, the network’s control layer can become a reconnaissance and persistence asset.
That is why “is it internet-facing?” is necessary but insufficient. The better question is: who and what can talk to the control plane, through which paths, under which identities, and with which monitoring? Anything less is inventory theater.
This is one reason SD-WAN incidents are difficult to investigate. The artifacts can look boring. A control connection appears. A peer relationship exists. A privileged internal account authenticates. In a healthy environment, all of those things happen constantly.
The defender’s job is to separate expected fabric behavior from hostile imitation. That requires more than searching for a single string in a log file. It requires a baseline of which controllers, validators, managers, system IPs, certificate identities, management accounts, and source networks are supposed to exist.
Many organizations will discover during this exercise that they never had that baseline in a usable form. Their SD-WAN topology may be documented in design diagrams, ticket histories, or the heads of two network engineers, but not in a form that the SOC can query at 2 a.m. That gap is precisely what attackers exploit after the initial bypass.
Cisco also advises customers who suspect compromise to open a TAC case and gather admin-tech data from control components. That is sensible, but it underscores the operational seriousness of the issue. Once a controller’s trust model is in doubt, the problem may not be solved by applying a patch alone. The organization may need to validate peers, credentials, certificates, configuration changes, and persistence mechanisms.
That does not make KEV perfect. Not every exploited bug is immediately visible to CISA, and absence from the catalog is not proof of safety. But inclusion is a strong signal. It means defenders should stop treating the issue as part of the normal monthly backlog and start treating it as part of the active threat landscape.
CVE-2026-20182 fits the catalog’s purpose almost too neatly. It is remotely relevant, high-impact, and connected to a widely deployed enterprise networking platform. It affects the sort of infrastructure that may not be patched as quickly as endpoints because outages can be politically and operationally painful. It also sits in an area where defenders cannot rely on user behavior controls, email filtering, or endpoint detection alone.
For federal civilian agencies, BOD 22-01 gives this urgency a deadline. For everyone else, it gives cover. Security leaders in private companies can point to KEV and say this is not a theoretical red team scenario or a vendor scare tactic; it is an exploited vulnerability in a control-plane product used to run distributed networks.
That distinction matters when the business asks why a change window must move, why a branch outage risk is being accepted, or why a managed cloud SD-WAN deployment needs immediate vendor confirmation. KEV is not merely a list. It is a prioritization weapon.
Cloud-managed networking often creates a psychological shortcut. If the controller is not in the customer’s rack, teams may assume the problem belongs elsewhere. But SD-WAN trust still reaches into the customer’s branches, routers, tunnels, policies, and administrative workflows. A flaw in the controller plane can still affect customer traffic and network integrity.
This is why CISA’s language about cloud services is important. Agencies and organizations cannot simply say the provider owns it and close the ticket. They need to confirm whether their deployment is affected, whether fixed software or service-side mitigation has been applied, whether any customer-side action is required, and whether logs or telemetry show suspicious activity before the fix.
The shared-responsibility model is often discussed in cloud compute terms: the provider secures the cloud, the customer secures what they put in it. For SD-WAN, the split is murkier. The provider may host or manage components, but the customer’s routing architecture, administrative access, certificates, identity integrations, and monitoring pipelines still shape risk.
That ambiguity is where incidents breed. If neither the vendor nor the customer has a crisp answer to who validates compromise, who reviews system IPs, who checks control connections, and who confirms fixed versions, the attacker inherits the silence.
A compromised SD-WAN control plane can change the terrain underneath Windows infrastructure. It can affect which sites can reach domain controllers, how administrative traffic flows, which cloud services are preferred, and what telemetry paths are reliable. In an incident, that can mean the difference between a contained compromise and a confusing, multi-site investigation where routing and trust are no longer assumed to be honest.
Windows administrators also tend to inherit the operational fallout. If branch users lose access after emergency remediation, the help desk lights up. If domain controller replication behaves strangely because network policy changed, Windows teams are pulled in. If incident responders need to isolate sites, disable admin paths, rotate credentials, or validate jump-host access, Windows infrastructure becomes part of the response even if it was never the initial vulnerability.
The deeper lesson is that platform security is no longer bounded by platform ownership. A Windows domain can be well-patched and still exposed by the network fabric around it. An SD-WAN controller can be a Cisco asset and still become a Windows incident because identity, administration, and business applications cross the fabric every day.
That is why sysadmins should resist the temptation to mentally file this under “networking team problem.” Attackers do not respect org charts. They follow control.
In ordinary applications, an authentication bypass may expose data or user-level functionality. In a network controller, the same class of flaw can threaten the legitimacy of peers, control connections, management sessions, and policy distribution. The attacker does not need to brute-force a password if the system can be convinced to treat them as already trusted.
CVE-2026-20182 is classified under improper authentication, and Cisco’s advisory describes the issue in control connection handshaking. That is exactly the sort of phrase that should make network defenders slow down. Handshakes are where distributed systems decide whether the entity on the other end belongs in the conversation.
The history of enterprise breaches shows that trust systems often fail catastrophically because they are designed for efficiency under normal conditions. Once the wrong entity is inside the trust boundary, logging may record activity as legitimate, peer relationships may look plausible, and administrative workflows may continue without dramatic alarms.
This is why the fix cannot be reduced to “install the update.” Patching closes the known door, but defenders still need to determine whether anyone walked through it while it was open.
A trust audit starts with the inventory of SD-WAN control components and the paths allowed to reach them. It then moves to peer validation, certificate review, administrator account review, and log analysis for unexpected control connections or authentication events. The goal is not just to prove that the current version is fixed, but to prove that the fabric has not been quietly altered.
For organizations using managed or cloud-hosted SD-WAN, the trust audit includes vendor confirmation. Customers should know when the environment was patched, what components were affected, whether logs show exploitation attempts, and whether any customer action remains. Vague assurances that “the service is managed” are not enough for an exploited CVSS 10.0 authentication bypass.
For Windows and identity teams, the audit should include administrative paths into the SD-WAN environment. Which jump hosts can reach the controller? Which administrator groups can manage it? Are those identities protected with phishing-resistant MFA? Are service accounts overprivileged? Are logs from the SD-WAN platform landing somewhere the SOC actually watches?
This is the practical convergence point between network engineering and security operations. The network team understands the fabric. The SOC understands attacker behavior. The identity team understands administrative trust. CVE-2026-20182 is the sort of bug that punishes organizations where those groups meet only during incident calls.
The federal government has learned, sometimes painfully, that exploited infrastructure bugs do not wait for ordinary change management. Appliances, controllers, VPNs, firewalls, and management platforms have become preferred targets because they sit at privileged junctions and often lack the monitoring depth of endpoints. Attackers know that a domain workstation may be heavily instrumented while the network control plane is treated as trusted plumbing.
The ED 26-03 language around Cisco SD-WAN reflects that lesson. It pushes agencies toward exposure assessment and risk mitigation, not just software remediation. It also acknowledges cloud-service realities, where the affected system may not be something the agency can patch directly.
Private-sector organizations should watch this playbook carefully. CISA’s emergency directives are mandatory for federal civilian agencies, but they often preview what reasonable care will look like elsewhere. When regulators, insurers, boards, or customers ask why an exploited KEV vulnerability remained unaddressed, “we were waiting for the next maintenance window” will sound increasingly weak.
The direction of travel is clear. Exploited infrastructure vulnerabilities are becoming executive-risk events faster than many IT operating models can absorb.
That does not mean every environment faces equal exposure. A tightly restricted, fully patched deployment with no internet-reachable management paths and strong monitoring is in a different position from a globally exposed, underdocumented SD-WAN environment running vulnerable software. But the burden is on the organization to know which category it occupies.
The lack of workarounds raises the stakes. If the only real fix is a software upgrade, delay becomes a choice. If the product cannot be mitigated and remains exposed, discontinuation or isolation becomes part of the conversation, however uncomfortable that may be.
For some teams, the hardest part will be sequencing remediation across control components without destabilizing the network. For others, it will be proving that Cisco-managed or cloud-managed instances have been addressed. For many, the painful discovery will be that SD-WAN visibility was designed for uptime and performance, not adversarial forensics.
That discovery should not lead to paralysis. It should lead to a more honest operating model: critical network controllers deserve the same vulnerability urgency, telemetry investment, and incident response planning as identity providers and endpoint fleets.
The concrete lessons are not complicated, but they require discipline:
CVE-2026-20182 will eventually become another line item in the long history of critical infrastructure bugs, but the pattern behind it is still accelerating. Enterprises are centralizing control to manage complexity, and attackers are following that control upstream. The next defensible network will not be the one with the fewest controllers; it will be the one that treats every controller as a high-value target before CISA has to remind everyone that attackers already do.
Source: CISA CISA Adds One Known Exploited Vulnerability to Catalog | CISA
 CISA’s New Cisco Warning Is Really About Control
CISA’s New Cisco Warning Is Really About Control
CISA’s latest KEV addition lands with the dry phrasing typical of federal vulnerability alerts, but the substance is anything but routine. CVE-2026-20182 affects Cisco Catalyst SD-WAN Controller and, according to Cisco’s advisory, carries the maximum CVSS severity score of 10.0. Cisco says the vulnerability sits in control connection handshaking and can affect Catalyst SD-WAN Controller and Catalyst SD-WAN Manager across deployment types, including on-premises, Cisco-managed cloud, Cloud-Pro, and government cloud environments.That breadth matters. SD-WAN is not an edge feature bolted onto the network for convenience; in many enterprises it is the coordination layer that decides how branches, data centers, cloud workloads, and remote sites talk to one another. A bypass in that layer is more consequential than a bug in a single appliance because the attacker is aiming at policy distribution, not merely packet forwarding.
CISA’s decision to put the flaw into the Known Exploited Vulnerabilities Catalog means federal civilian agencies must treat it as an active operational risk, not a theoretical one. BOD 22-01 created the KEV catalog to force remediation of flaws that attackers are known to use, and it has become one of the clearest public signals for private-sector prioritization as well.
The timing also gives the alert extra weight. CISA did not publish this in isolation; it explicitly tied the warning to Emergency Directive 26-03 and supplemental hunting and hardening guidance for Cisco SD-WAN systems. That is federal-speak for “do not merely patch and move on.”
The Same SD-WAN Story Keeps Repeating
The uncomfortable part of CVE-2026-20182 is that it follows a familiar script. Earlier in 2026, Cisco and government agencies were already dealing with critical Catalyst SD-WAN authentication and control-plane issues, including CVE-2026-20127, another maximum-severity authentication bypass that drew emergency federal action. That earlier wave was not a garden-variety patch Tuesday footnote; it involved warnings about active exploitation and possible compromise of the SD-WAN fabric itself.CVE-2026-20182 is described by Cisco as a new vulnerability discovered and fixed after the February 2026 disclosure. That phrasing matters because it tells defenders this is not merely an administrative update to the old advisory. It is a fresh defect in the same strategic neighborhood: authentication, control connections, and the trust relationships that allow SD-WAN components to coordinate.
The difference between endpoint compromise and controller compromise is the difference between breaking into an office and obtaining the building’s master access system. An attacker who can abuse controller authentication is not simply hoping to land on one host and move laterally the old-fashioned way. They may be able to influence the network’s own machinery for connectivity, reachability, and persistence.
That is why the KEV entry should not be read as “Cisco customers have a patching chore.” It should be read as “attackers are probing the management fabric that modern enterprises use to make distributed infrastructure manageable.” The convenience layer has become the blast-radius layer.
“No Workaround” Turns Patching Into a Governance Test
Cisco’s advisory says there are no workarounds for CVE-2026-20182. In security operations, that phrase turns a technical vulnerability into a management decision. If an organization cannot mitigate the issue through configuration, access controls, or a temporary compensating control that actually removes the vulnerable path, it must either upgrade to fixed software or remove exposure.That is simple in a boardroom and messy in production. SD-WAN controllers are often woven into maintenance windows, carrier dependencies, branch uptime commitments, and change-control processes built to avoid outages. The result is a classic enterprise dilemma: the systems most painful to patch are often the ones attackers most want to own.
CISA’s language anticipates that tension. The agency urges adherence to Emergency Directive 26-03 and supplemental guidance, and it says organizations should follow BOD 22-01 guidance for cloud services or discontinue use of the product if mitigations are not available. That last clause is severe, but it reflects the reality of exploited authentication bypasses. If you cannot patch, isolate, or prove safety, continued exposure becomes an accepted risk rather than an unresolved ticket.
The practical challenge for IT teams is that SD-WAN often sits between networking, security, and infrastructure operations. The group that owns the controller may not own the vulnerability management platform. The group that can see suspicious identity events may not understand SD-WAN peering. The group that can approve emergency changes may not understand why a controller flaw deserves faster treatment than a domain workstation vulnerability.
This is where governance either works or collapses. A KEV listing gives security teams the leverage to force prioritization, but it does not magically create asset inventories, change windows, tested rollback plans, or executive appetite for emergency upgrades.
The Exposure Question Starts With the Internet, But It Does Not End There
Cisco’s indicators of compromise guidance emphasizes risk for systems exposed to the internet and ports exposed to the internet. That is the obvious starting point. If a controller or manager component accepts traffic from broad or untrusted sources, an authentication bypass moves from dangerous to urgent.But mature defenders should not stop at the public-facing inventory. SD-WAN management planes are often reachable from administrative networks, cloud segments, jump hosts, VPN pools, monitoring systems, and automation platforms. Those paths may not show up in a naive external scan, but they can become reachable after a smaller intrusion elsewhere.
This is where Windows-heavy enterprises have a particular stake. Many environments still center identity, administration, logging, and incident response around Active Directory, Entra ID, Windows Server jump boxes, PowerShell automation, and endpoint management tooling. If the network control plane is reachable from those administrative zones, a compromise in one domain can become the staging ground for an attack on the SD-WAN fabric.
The reverse is equally troubling. If an attacker reaches the SD-WAN controller first, they may gain insight into site topology, management addresses, routing behavior, and trust relationships that help them target Windows infrastructure more precisely. Even without a direct exploit chain into Windows hosts, the network’s control layer can become a reconnaissance and persistence asset.
That is why “is it internet-facing?” is necessary but insufficient. The better question is: who and what can talk to the control plane, through which paths, under which identities, and with which monitoring? Anything less is inventory theater.
Hunting Must Assume the Attacker Knows the Fabric
Cisco’s advisory points customers toward checking authentication logs for accepted public key events involving the vmanage-admin account from unknown or unauthorized IP addresses. It also recommends comparing the source IPs in logs against configured system IPs visible in the SD-WAN Manager interface. That is not a generic log review suggestion; it is a sign that compromise may masquerade as normal-looking control-plane activity.This is one reason SD-WAN incidents are difficult to investigate. The artifacts can look boring. A control connection appears. A peer relationship exists. A privileged internal account authenticates. In a healthy environment, all of those things happen constantly.
The defender’s job is to separate expected fabric behavior from hostile imitation. That requires more than searching for a single string in a log file. It requires a baseline of which controllers, validators, managers, system IPs, certificate identities, management accounts, and source networks are supposed to exist.
Many organizations will discover during this exercise that they never had that baseline in a usable form. Their SD-WAN topology may be documented in design diagrams, ticket histories, or the heads of two network engineers, but not in a form that the SOC can query at 2 a.m. That gap is precisely what attackers exploit after the initial bypass.
Cisco also advises customers who suspect compromise to open a TAC case and gather admin-tech data from control components. That is sensible, but it underscores the operational seriousness of the issue. Once a controller’s trust model is in doubt, the problem may not be solved by applying a patch alone. The organization may need to validate peers, credentials, certificates, configuration changes, and persistence mechanisms.
KEV Is Becoming the Patch Queue That Actually Matters
For years, vulnerability management programs have been buried under CVSS scores, scanner output, asset criticality debates, and vendor advisories that describe everything as urgent. CISA’s KEV catalog has changed that conversation by focusing on a narrower and more useful question: is this vulnerability known to be exploited?That does not make KEV perfect. Not every exploited bug is immediately visible to CISA, and absence from the catalog is not proof of safety. But inclusion is a strong signal. It means defenders should stop treating the issue as part of the normal monthly backlog and start treating it as part of the active threat landscape.
CVE-2026-20182 fits the catalog’s purpose almost too neatly. It is remotely relevant, high-impact, and connected to a widely deployed enterprise networking platform. It affects the sort of infrastructure that may not be patched as quickly as endpoints because outages can be politically and operationally painful. It also sits in an area where defenders cannot rely on user behavior controls, email filtering, or endpoint detection alone.
For federal civilian agencies, BOD 22-01 gives this urgency a deadline. For everyone else, it gives cover. Security leaders in private companies can point to KEV and say this is not a theoretical red team scenario or a vendor scare tactic; it is an exploited vulnerability in a control-plane product used to run distributed networks.
That distinction matters when the business asks why a change window must move, why a branch outage risk is being accepted, or why a managed cloud SD-WAN deployment needs immediate vendor confirmation. KEV is not merely a list. It is a prioritization weapon.
Cloud-Managed Does Not Mean Cloud-Absolved
One of the more important details in Cisco’s advisory is that the vulnerability affects all deployment types, including Cisco-managed cloud offerings and government cloud environments. That should puncture a common misconception in infrastructure security: moving management to a vendor-operated or cloud-hosted model may change who applies the fix, but it does not eliminate customer responsibility for exposure, validation, and incident response.Cloud-managed networking often creates a psychological shortcut. If the controller is not in the customer’s rack, teams may assume the problem belongs elsewhere. But SD-WAN trust still reaches into the customer’s branches, routers, tunnels, policies, and administrative workflows. A flaw in the controller plane can still affect customer traffic and network integrity.
This is why CISA’s language about cloud services is important. Agencies and organizations cannot simply say the provider owns it and close the ticket. They need to confirm whether their deployment is affected, whether fixed software or service-side mitigation has been applied, whether any customer-side action is required, and whether logs or telemetry show suspicious activity before the fix.
The shared-responsibility model is often discussed in cloud compute terms: the provider secures the cloud, the customer secures what they put in it. For SD-WAN, the split is murkier. The provider may host or manage components, but the customer’s routing architecture, administrative access, certificates, identity integrations, and monitoring pipelines still shape risk.
That ambiguity is where incidents breed. If neither the vendor nor the customer has a crisp answer to who validates compromise, who reviews system IPs, who checks control connections, and who confirms fixed versions, the attacker inherits the silence.
The Windows Angle Is Not the Brand on the Box
At first glance, a Cisco SD-WAN vulnerability may seem peripheral to WindowsForum readers. It is not a Windows kernel bug, not an Exchange zero-day, not a Defender bypass, and not a new Active Directory escalation technique. But modern Windows estates live inside networks whose behavior is increasingly defined by SD-WAN overlays, cloud security brokers, identity-aware proxies, and controller-driven policy.A compromised SD-WAN control plane can change the terrain underneath Windows infrastructure. It can affect which sites can reach domain controllers, how administrative traffic flows, which cloud services are preferred, and what telemetry paths are reliable. In an incident, that can mean the difference between a contained compromise and a confusing, multi-site investigation where routing and trust are no longer assumed to be honest.
Windows administrators also tend to inherit the operational fallout. If branch users lose access after emergency remediation, the help desk lights up. If domain controller replication behaves strangely because network policy changed, Windows teams are pulled in. If incident responders need to isolate sites, disable admin paths, rotate credentials, or validate jump-host access, Windows infrastructure becomes part of the response even if it was never the initial vulnerability.
The deeper lesson is that platform security is no longer bounded by platform ownership. A Windows domain can be well-patched and still exposed by the network fabric around it. An SD-WAN controller can be a Cisco asset and still become a Windows incident because identity, administration, and business applications cross the fabric every day.
That is why sysadmins should resist the temptation to mentally file this under “networking team problem.” Attackers do not respect org charts. They follow control.
Authentication Bypass Remains the Most Dangerous Phrase in Infrastructure
Not all critical vulnerabilities are equal. Remote code execution gets the headlines, and privilege escalation drives many post-exploitation chains, but authentication bypass in infrastructure controllers has a special menace. It attacks the boundary that decides whether the rest of the system should listen.In ordinary applications, an authentication bypass may expose data or user-level functionality. In a network controller, the same class of flaw can threaten the legitimacy of peers, control connections, management sessions, and policy distribution. The attacker does not need to brute-force a password if the system can be convinced to treat them as already trusted.
CVE-2026-20182 is classified under improper authentication, and Cisco’s advisory describes the issue in control connection handshaking. That is exactly the sort of phrase that should make network defenders slow down. Handshakes are where distributed systems decide whether the entity on the other end belongs in the conversation.
The history of enterprise breaches shows that trust systems often fail catastrophically because they are designed for efficiency under normal conditions. Once the wrong entity is inside the trust boundary, logging may record activity as legitimate, peer relationships may look plausible, and administrative workflows may continue without dramatic alarms.
This is why the fix cannot be reduced to “install the update.” Patching closes the known door, but defenders still need to determine whether anyone walked through it while it was open.
The Real Remediation Is a Trust Audit
The immediate action is obvious: identify affected Cisco Catalyst SD-WAN Controller and Manager deployments, determine exposure, and move to fixed software. Cisco’s advisory provides fixed release guidance, and organizations should prioritize internet-exposed and externally reachable control-plane systems first. But a serious response should go beyond version checking.A trust audit starts with the inventory of SD-WAN control components and the paths allowed to reach them. It then moves to peer validation, certificate review, administrator account review, and log analysis for unexpected control connections or authentication events. The goal is not just to prove that the current version is fixed, but to prove that the fabric has not been quietly altered.
For organizations using managed or cloud-hosted SD-WAN, the trust audit includes vendor confirmation. Customers should know when the environment was patched, what components were affected, whether logs show exploitation attempts, and whether any customer action remains. Vague assurances that “the service is managed” are not enough for an exploited CVSS 10.0 authentication bypass.
For Windows and identity teams, the audit should include administrative paths into the SD-WAN environment. Which jump hosts can reach the controller? Which administrator groups can manage it? Are those identities protected with phishing-resistant MFA? Are service accounts overprivileged? Are logs from the SD-WAN platform landing somewhere the SOC actually watches?
This is the practical convergence point between network engineering and security operations. The network team understands the fabric. The SOC understands attacker behavior. The identity team understands administrative trust. CVE-2026-20182 is the sort of bug that punishes organizations where those groups meet only during incident calls.
CISA’s Emergency Directive Shows the Federal Playbook Hardening
Emergency Directive 26-03 is part of a broader pattern in CISA’s posture: when exploitation affects foundational systems, the agency is increasingly willing to prescribe not just patching but hunting, hardening, reporting, and discontinuation if mitigation is unavailable. That is a notable shift from the older model of advisory publishing, where agencies warned and vendors patched while customers decided how urgently to care.The federal government has learned, sometimes painfully, that exploited infrastructure bugs do not wait for ordinary change management. Appliances, controllers, VPNs, firewalls, and management platforms have become preferred targets because they sit at privileged junctions and often lack the monitoring depth of endpoints. Attackers know that a domain workstation may be heavily instrumented while the network control plane is treated as trusted plumbing.
The ED 26-03 language around Cisco SD-WAN reflects that lesson. It pushes agencies toward exposure assessment and risk mitigation, not just software remediation. It also acknowledges cloud-service realities, where the affected system may not be something the agency can patch directly.
Private-sector organizations should watch this playbook carefully. CISA’s emergency directives are mandatory for federal civilian agencies, but they often preview what reasonable care will look like elsewhere. When regulators, insurers, boards, or customers ask why an exploited KEV vulnerability remained unaddressed, “we were waiting for the next maintenance window” will sound increasingly weak.
The direction of travel is clear. Exploited infrastructure vulnerabilities are becoming executive-risk events faster than many IT operating models can absorb.
The Patch Window Is Now a Business Decision
One persistent problem in enterprise security is that technical teams often describe urgency in technical terms while business leaders hear only disruption. CVE-2026-20182 is a case where the translation should be direct. The risk is not merely that a device could be compromised; it is that the system coordinating connectivity across the organization could be undermined.That does not mean every environment faces equal exposure. A tightly restricted, fully patched deployment with no internet-reachable management paths and strong monitoring is in a different position from a globally exposed, underdocumented SD-WAN environment running vulnerable software. But the burden is on the organization to know which category it occupies.
The lack of workarounds raises the stakes. If the only real fix is a software upgrade, delay becomes a choice. If the product cannot be mitigated and remains exposed, discontinuation or isolation becomes part of the conversation, however uncomfortable that may be.
For some teams, the hardest part will be sequencing remediation across control components without destabilizing the network. For others, it will be proving that Cisco-managed or cloud-managed instances have been addressed. For many, the painful discovery will be that SD-WAN visibility was designed for uptime and performance, not adversarial forensics.
That discovery should not lead to paralysis. It should lead to a more honest operating model: critical network controllers deserve the same vulnerability urgency, telemetry investment, and incident response planning as identity providers and endpoint fleets.
The Cisco Alert Leaves Little Room for Comfortable Assumptions
CISA’s May 14 action is narrow in form and broad in implication. One vulnerability entered the KEV catalog, but the surrounding message is about the way adversaries now target the administrative and control systems that make modern IT manageable. The safer the enterprise feels because everything is centrally orchestrated, the more valuable that orchestration layer becomes to an attacker.The concrete lessons are not complicated, but they require discipline:
- Organizations using Cisco Catalyst SD-WAN Controller or Manager should immediately determine whether their deployment is affected by CVE-2026-20182 and whether fixed software has been applied.
- Teams should treat internet-facing or broadly reachable SD-WAN control-plane components as the highest priority for remediation and exposure reduction.
- Administrators should review Cisco’s recommended indicators of compromise, including authentication log entries and control-plane relationships that do not match the expected SD-WAN topology.
- Cloud-managed SD-WAN customers should obtain clear confirmation of patch status, exposure, and any evidence of exploitation rather than assuming the provider has silently resolved every customer-side risk.
- Windows, identity, and SOC teams should be included in the response because SD-WAN compromise can affect administrative paths, branch connectivity, logging, and incident containment across the Microsoft estate.
- Patching should be followed by validation of peers, accounts, certificates, management access, and configuration integrity because an exploited authentication bypass may leave behind changes that survive the update.
CVE-2026-20182 will eventually become another line item in the long history of critical infrastructure bugs, but the pattern behind it is still accelerating. Enterprises are centralizing control to manage complexity, and attackers are following that control upstream. The next defensible network will not be the one with the fewest controllers; it will be the one that treats every controller as a high-value target before CISA has to remind everyone that attackers already do.
Source: CISA CISA Adds One Known Exploited Vulnerability to Catalog | CISA