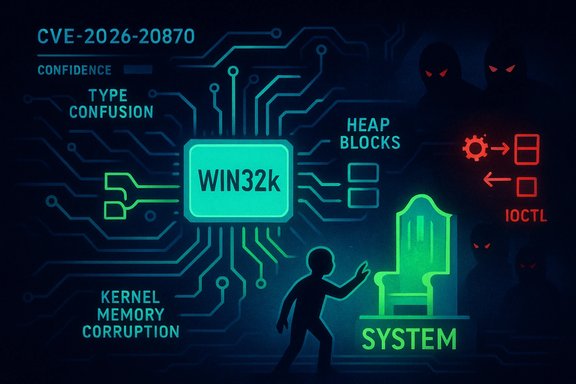
Microsoft’s public advisory for CVE-2026-20870 describes a high‑impact elevation‑of‑privilege defect in the Windows Win32k kernel subsystem that can be triggered by a local, authenticated actor and that Microsoft treats with a measured disclosure posture using its published confidence metric.
The vulnerability is recorded in Microsoft’s Security Update Guide as a Win32k‑level issue that permits local elevation of privilege (EoP) — in practical terms, an attacker with a low‑privilege process or an authenticated user account can, if exploitation succeeds, escalate to SYSTEM‑level privileges. The vendor’s entry is intentionally concise while mapping the CVE to the relevant updates; Microsoft also attaches a confidence indicator to the advisory that signals how certain the vendor is about the vulnerability and how much technical detail it will publish.
Community and vendor trackers categorize this family of Win32k defects as type‑confusion and related memory‑corruption classes (heap corruption, use‑after‑free), with public reporting pointing at the ICOMP surface in Win32k in cases analogous to this advisory. That class of kernel bug is historically powerful because Win32k handlers run at ring‑0 and service graphics, windowing and UI primitives that bridge user‑mode to kernel‑mode.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
The vulnerability is recorded in Microsoft’s Security Update Guide as a Win32k‑level issue that permits local elevation of privilege (EoP) — in practical terms, an attacker with a low‑privilege process or an authenticated user account can, if exploitation succeeds, escalate to SYSTEM‑level privileges. The vendor’s entry is intentionally concise while mapping the CVE to the relevant updates; Microsoft also attaches a confidence indicator to the advisory that signals how certain the vendor is about the vulnerability and how much technical detail it will publish.Community and vendor trackers categorize this family of Win32k defects as type‑confusion and related memory‑corruption classes (heap corruption, use‑after‑free), with public reporting pointing at the ICOMP surface in Win32k in cases analogous to this advisory. That class of kernel bug is historically powerful because Win32k handlers run at ring‑0 and service graphics, windowing and UI primitives that bridge user‑mode to kernel‑mode.
What Microsoft’s “confidence” metric means here
Microsoft’s Update Guide includes a compact confidence metric alongside each record. The metric measures two related things: (1) the vendor's degree of certainty that the vulnerability actually exists and (2) the credibility/amount of known technical detail that is safe to publish publicly. A higher confidence rating indicates vendor confirmation and typically accompanies clear KB→SKU mappings; a lower or terse rating means the vendor is acknowledging the issue but is withholding deeper exploit mechanics while patches are distributed. For defenders, the metric is a triage signal: a high‑confidence kernel EoP accelerates urgency, while lower‑confidence entries require cautious but prompt action.Technical summary and anatomy
The Win32k surface and why it matters
Win32k is a kernel‑mode subsystem responsible for the Windows graphical stack (windowing, composition, input, device contexts). Because it executes at kernel privilege, any memory‑safety or logic bug in Win32k is an immediate candidate for SYSTEM escalation when an attacker can convert the bug into a memory corruption or logic‑abuse primitive. Historically, Win32k bugs include type confusion, use‑after‑free, and heap overflows — each can be chained to produce arbitrary read/write or token‑stealing primitives.Type confusion and exploitation primitives
Type confusion occurs when kernel code interprets an object as the wrong type. In practice, an attacker supplies crafted inputs that cause privileged code to dereference or manipulate data under incorrect type assumptions. In kernel code this can:- Corrupt kernel heaps or adjacent structures,
- Produce arbitrary read/write primitives,
- Leak kernel addresses that defeat ASLR/KASLR,
- Be escalated to token manipulation or direct SYSTEM process creation.
Exploitability model
- Attack vector: Local. An attacker must run code on the target host (malicious binary, compromised process, or crafted user‑action).
- Complexity: Varies — type‑confusion and heap corruption can be straightforward to trigger, but converting them reliably to SYSTEM often requires advanced heap grooming and timing. Still, skilled exploit teams and automation can make these reliable.
- Impact: SYSTEM or equivalent kernel privileges — enabling persistence, credential theft, disabling protections, and lateral movement.
- Evidence of exploitation: Public reporting often withholds low‑level PoCs immediately after patching; absence of a public PoC does not equal absence of weaponization. Treat vendor acknowledgement and CVE registration as sufficient operational urgency.
What we can verify now (concise, verifiable facts)
- Microsoft has an Update Guide entry for this Win32k CVE and classifies the impact as Elevation of Privilege; the entry includes a confidence metric.
- Public vulnerability aggregators and community trackers have grouped Win32k ICOMP/ICOMP‑adjacent defects into type‑confusion categories, often assigning high severity (commonly reported CVSS base scores in the high‑sevens range). These external summaries align with vendor statements about the nature and severity of the class.
- Microsoft’s Update Guide is the canonical source to map the CVE to the exact KB package(s) and OS build(s) that contain the remediation; administrators must consult that mapping before deploying fixes.
Operational impact and urgency
Why this vulnerability is a high‑priority operational concern
- Post‑compromise multiplier: Local EoP primitives are the core building block for post‑compromise escalation. Once attackers obtain a foothold (phishing, malicious installer, browser exploit, or compromised neutral process), converting that foothold into SYSTEM is often the key step to domain compromise. Win32k class bugs are classic, reliable primitives for this purpose.
- High‑value targets: Admin workstations, jump hosts, RDP/VDI servers, build servers, and domain controllers are especially sensitive. An exploited Win32k on any such host can have outsized network consequences.
- Exploitability despite mitigations: Kernel mitigations raise difficulty but not impossibility; skilled exploit developers have repeatedly bypassed or leveraged partial mitigations to make practical exploits.
Typical enterprise prioritization model
Organizations typically triage kernel EoP fixes ahead of routine updates because:- They enable privilege elevation to the highest local privilege.
- They are frequently chained with other initial access vectors.
- Vendor confidence and KB mappings provide a straightforward remediation path.
Recommended remediation and playbook
The canonical remediation is vendor patching. Use Microsoft’s Update Guide to identify the exact KB for each build, then deploy via existing orchestration tooling.Immediate 0–72 hour checklist
- Inventory and prioritize:
- Identify all hosts that include the Win32k surface (Windows desktop SKUs, VDI images, servers with GUI components).
- Prioritize admin workstations, jump boxes, RDP/VDI hosts, domain controllers, build servers and any host that processes untrusted content.
- Map KBs:
- For each OS build, use the Microsoft Update Guide to confirm the precise KB package(s) that fix CVE‑2026‑20870. Do not rely on generic rollup names; confirm the KB→SKU mapping for each build.
- Pilot and deploy:
- Stage updates in a small test ring (24–72 hours).
- Roll to high‑value and exposed hosts first.
- Reboot and validate the post‑install build and update history.
- If immediate patching is impossible:
- Harden against local code execution (application allow‑listing via WDAC/AppLocker).
- Remove unnecessary local administrative rights.
- Isolate high‑value hosts behind bastions and stricter network segmentation.
- Post‑deploy validation:
- Confirm KB installation via Windows Update history or PowerShell listing of installed updates.
- Monitor for abnormal behavior and collect WER/kernel crash dumps for triage.
Detection, hunting and mitigation guidance
Even when patches are available, defenders must hunt for evidence of exploitation and harden telemetry.Detection signals and telemetry to enable
- Suspicious process ancestry where unprivileged processes spawn SYSTEM interpreters (cmd.exe, PowerShell) or services.
- Token duplication and manipulation API usage patterns (DuplicateTokenEx, OpenProcessToken) from unexpected parents.
- New service installations, scheduled tasks, or persistence artifacts created by low‑privileged accounts shortly before unusual behavior.
- Kernel crash signatures and memory dumps referencing Win32k call stacks or ICOMP handling routines.
- Unusual DeviceIoControl / IOCTL usage against Win32k‑exposed surfaces (where observable).
Hunting playbook (short)
- Query EDR logs for user‑level processes spawning SYSTEM‑context processes in the preceding 30 days.
- Inspect for newly created services, scheduled tasks, or driver loads by non‑admin accounts.
- Collect and analyze any kernel memory dumps that reference Win32k or related kernel symbols.
- Cross‑check with patch deployment timelines to rule out false positives from post‑patch restarts or legitimate admin actions.
Mitigations and compensating controls
- Removal of local admin rights: Reducing the number of privileged local accounts reduces the blast radius of a successful EoP.
- Application allow‑listing: WDAC or AppLocker dramatically reduces the chance that untrusted code can run to exercise the vulnerability.
- Network and host segmentation: Isolate admin workstations and management hosts so local compromises cannot easily be used for lateral movement.
- EDR behavioral policies: Enforce policies that flag token changes, unexpected parent/child process relationships, and suspicious driver install attempts.
Risk analysis and critical assessment
Notable strengths in the vendor response
- Microsoft’s use of a confidence metric improves triage: it enables defenders to calibrate urgency based on vendor validation and the amount of disclosed technical detail. This is a useful, standardized signal for operational teams.
- The Update Guide remains the canonical remediation reference, mapping CVE→KB→SKUs; this reduces ambiguity when deploying fixes at scale.
Potential risks and gaps
- Information asymmetry at disclosure: Microsoft and other vendors commonly withhold low‑level exploit mechanics at the time of public patching to reduce short‑term weaponization. While this is defensible policy, it creates operational friction: defenders must act quickly on limited technical artefacts and may lack precise detection signatures until independent researchers publish patch‑diff analyses.
- Patch mapping complexity: The Update Guide’s interactive SKU→KB rendering sometimes requires an interactive browser to extract precise mappings, complicating automated inventory mapping in managed environments. Administrators should validate KB numbers via the Microsoft Update Catalog or their management tooling.
- Local only does not mean low risk: Because the vulnerability requires local access, some teams deprioritize it. That is a mistake: local EoP primitives are exactly what attackers chain after initial access and are frequently used in real‑world campaigns.
Where claims are not fully verifiable (flagged)
- Any statement of a precise CVSS vector, exact KB identifiers for specific builds, or the existence of a public, working proof‑of‑concept exploit should be treated as provisional unless confirmed in Microsoft’s Update Guide or by reputable independent technical write‑ups. Those specifics were not present in the public snippets reviewed here and must be confirmed interactively against vendor records.
Practical recommendations for security teams
- Treat CVE‑2026‑20870 as a high‑priority kernel EoP: prioritize patching for admin hosts, jump boxes, VDI, RDP servers, and build servers.
- Use the Update Guide as the authoritative KB mapping source and confirm per‑build KB identifiers before deployment.
- If you cannot patch immediately:
- Enforce strict application allow‑listing,
- Remove unnecessary local admin privileges,
- Harden and segment high‑value hosts,
- Increase EDR and SIEM monitoring for token operations and unusual process ancestry.
- Post‑patch: monitor for unusual behavior for at least two weeks and collect kernel dumps for any anomalous crashes tied to Win32k code paths.
Conclusion
CVE‑2026‑20870 sits squarely in the high‑impact family of Win32k kernel vulnerabilities: a class that has repeatedly enabled attackers to convert modest local footholds into full SYSTEM compromises. Microsoft’s Update Guide entry and its accompanying confidence metric give defenders a pragmatic starting point for rapid triage and KB mapping, but the vendor’s cautious disclosure posture means that defenders must act on high‑level facts and robust operational playbooks rather than detailed exploit signatures alone. Prioritize patching, harden local controls, and tune telemetry for token abuse and suspicious process ancestry — those three actions together materially lower the risk that an initial compromise becomes a full‑blown host or domain compromise.Source: MSRC Security Update Guide - Microsoft Security Response Center