Microsoft’s security trackers show a new entry for CVE-2026-21520 — an information‑disclosure vulnerability affecting Cotheilot Studio — but public technical details are intentionally sparse and the vendor record currently provides more affirmation of existence than a full exploit recipe.
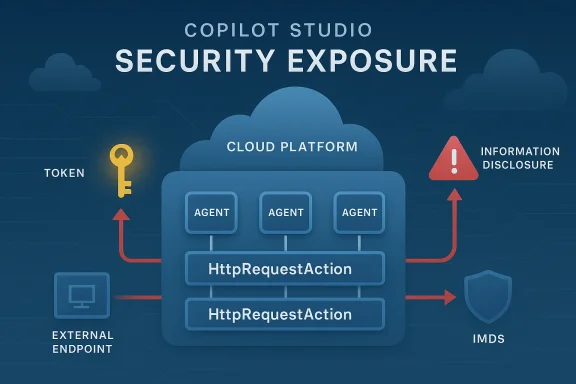
Copilot Studio — Microsoft’s platform for building and hosting agentic copilots — has had a visible, evolving security history over the past two years. Multiple research reports and vendor advisories have shown the product surface is attractive to researchers because features that let agents fetch URLs, perform HTTP actions, and run user‑configured request templates can be combined with redirect handling and header shaping to produce server‑side request forgery (SSRF), token theft and cross‑tenant exposure scenarios. Independent research published in 2024 and vendor follow‑ups in 2025 demonstrate how these classes of flaws translate into real risk. Microsoft’s public response posture has been to publish Update‑Guide / MSRC entries for affected CVEs, deploy platform hardenings (removing wildcard validDomains, tightening manifest flags and making fetch confirmations stricter), and to urge customers to apply updates and to harden agent manifests and tenant governance. That programmatic response and the pattern of disclosures baseline: Copilot Studio can expose sensitive cloud metadata or tokens when HTTP‑action primitives are combined with inadequate redirect/header handling; Microsoft has patched prior instances and updated the product’s manifest and default-security posture.
s, limitations and operational risk
Strengths
Microsoft’s Update Guide (MSRC) remains the authoritative source for remediation mapping; confirm KB identifiers and deployment guidance there before automating any large‑scale patch rollouts.
This article synthesizes the public CVE listing for CVE‑2026‑21520 and the broader Copilot Studio security history to give operators an actionable, defensible triage and mitigation path while vendor‑level technical details remain restricted.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
Copilot Studio — Microsoft’s platform for building and hosting agentic copilots — has had a visible, evolving security history over the past two years. Multiple research reports and vendor advisories have shown the product surface is attractive to researchers because features that let agents fetch URLs, perform HTTP actions, and run user‑configured request templates can be combined with redirect handling and header shaping to produce server‑side request forgery (SSRF), token theft and cross‑tenant exposure scenarios. Independent research published in 2024 and vendor follow‑ups in 2025 demonstrate how these classes of flaws translate into real risk. Microsoft’s public response posture has been to publish Update‑Guide / MSRC entries for affected CVEs, deploy platform hardenings (removing wildcard validDomains, tightening manifest flags and making fetch confirmations stricter), and to urge customers to apply updates and to harden agent manifests and tenant governance. That programmatic response and the pattern of disclosures baseline: Copilot Studio can expose sensitive cloud metadata or tokens when HTTP‑action primitives are combined with inadequate redirect/header handling; Microsoft has patched prior instances and updated the product’s manifest and default-security posture. What we know about CVE‑2026‑21520
- The vulnerability is recorded as CVE‑2026‑21520 and is classified as an information disclosure issue attributed to Copilot Studio in vendor‑level feeds. The public CVE listing available from aggregated feeds shows a high base score (CVSS 3.1 ≈ 7.5) but the entry itself contains minimal descriptive text at time of publication.
- Official vendor pages (Microsoft’s Update authoritative mapping for CVE → KB → product SKUs; in this case the MSRC record confirms the CVE identifier and vendor listing but — in keeping with normal responsible‑disclosure practice — avoids releasing low‑level exploit mechanics in the public advisory. That leaves defenders with a confirmed vulnerability identifier, requirement to consult MSRC/patch notes for precise remediation.
Technical context: plausible mechanics and precedent
Because the public CVE description is minimal, the safest approach for risk modeling is to rely on documented precedents and confirmed behaviors in Copilot Studio and adjacent Copilot components.- Prior Copilot Studio research (notably Tenable’s August 2024 disclosure) demonstrated a practical SSRF chain: a user‑configurable HttpRequestAction combined with redirect responses and header manipulation allowed researchers to induce Copilot Studio to request internal resources (for example the Instance Metadata Service, IMDS), obtain managed identity tokens and then use those tokens to access otherwise restricted internal storage endpoints. That chain is a concrete illustration of how an information‑disclosure bug in an agent runner can quickly become an authorization and infrastructure‑access problem.
- The common technical primitives observed across multiple Copilot/Copilot‑Studio disclosures action that can initiate HTTP requests on behalf of a conversation or agent workflow.
- Insufficient redirect handling or permissive trust/validDomains semantics that allow a crafted redirect to point from an externally controlled endpoint into internal infrastructure.
- Header manipulation or request normalization quirks that permit the required metadata header semantics (for example the IMDS required header) to be preserved across proxying/forwarding mechanics.
- Shared cloud infrastructure where a compromise or read access to internal services can have cross‑tenant impact.
Confidence, corroboration and what remains unverified
The degree of confidence in the vulnerability’s existence is high — Microsoft’s Update Guide lists the CVE — but the publicly available technical details are limited by design. This is a common vendor choice to delay detailed exploit publication until patches are widely deployed. Two practical consequences follow:- The CVE’s existence and scope (Copilot Studio) are vendor‑confirmed; that elevates remediation priority for affected tenants.
- The precise exploit steps, function names, and code paths are not published in the advisory. Any public claim that provides an exploit recipe should be treated as either speculative or as a later community proof‑of‑concept that must be validated. Where independent researchers have published PoCs for earlier Copilot Studio SSRF (e.g., CVE‑2024‑38206), those PoCs are useful for modeling risk but are not necessarily identical to CVE‑2026‑21520.
Impact and threat model
Given the classification as information disclosure and the prior Copilot Studio SSRF precedent, the practical consequences to prioritize are:- Exposure of cloud metadata and managed identity tokens — a read of the IMDS can reveal credentials that permit further access. This is both an information disclosure and a lateral‑movement enabler.
- Access to internal data stores — once a token is available, the ability to query internal Cosmos DB instances or other internal APIs can permit read/write operations against infrastructure artifacts that are otherwise firewall‑restricted. Past researcher demonstrations recovered Cosmos DB master keys after escalating via IMDS access.
- Cross‑tenant effects — because Copilot Studio services often run on shared infrastructure, a local information disclosure may have a broader blast radius than a single tenant, especially where the service uses shared internal APIs or multi‑tenant bit week.
- Attack vector: prior Copilot Studio incidents required an authenticated user/agent or an agent payload that would be processed by the platform. If the CVE follows that pattern, remote anonymous exploitation will be less likely, but social‑engineering or supply‑chain nts/topics) can reach many users.
- Complexity: SSRF and redirect/header manipulations are technically straightforward for a skilled researcher attacker, but reliably chaining them into a token theft and internal‑API access path requires environment‑specific knowledge. Prior public demonstrations show the complexity is practical not theoretical.
- Detectability: because the exfiltration goes over vendor‑hosted processing and internal service calls, local EDR/standard network edge monitoring can miss the event unless the organization monitors the Copilot‑Studio tenant activity and Microsoft‑hosted telemetry. That reduces on‑host visibility for defenders.
Immediate actions for administrators and developers
Until the vendor maps the CVE to explicit KBs and release notes for your tenant variant, apply a conservative, defense‑in‑depth approach that follows prior Copilot Studio:- Confirm patch status
- Check Microsoft’s Security Update Guide / MSRC entry for CVE‑2026‑21520 and the KB mapping for your tenant and region. Treat MSRC as the primary authoritative source.
- If vendor KBs are published, prioritize installation in a stagigh‑value hosts → full rollout.
- Apply short‑term mitigations if patching is not yet possible
- Restrict who can create and publish Copilot Studio agents in your organization.
- Disable or limit public agent hosting and remove wildcard validDomains or overly broad manifest entries in internal agent inventories.
- Require tenant administrators to vet and approve any agents that include HttpRequestAction or similar network‑request actions.
- Rotate and limit credentials
- Rotate managed identities and long‑lived keys that could be exposed if you have reason to suspect prior token harvesting.
- Enforce least privilege for any identity used by Copilot Studio agents and log all token issuance events.
- Increase detection and logging
- Enable tenant‑level auditing for Copilot Studio and Microsoft 365 admin logs; hunt for anomalous agent creations, HttpRequestAction usage, nd unusual internal API calls.
- Correlate Microsoft telemetry with internal SIEM signals for spikes in out‑of‑pattern Cosmos DB or IMDS access patterns.
- Harden developer guidance and CI
- Require code review and manifest review for agents pushed from developer workstations.
- Use approval gates for any agent that contains network fetch calls or that can be configured with arbitrary request headers/redirects.
Detection guidance: concrete expected IMDS or internal API activity that originates from known Copilot Studio service IP blocks (use Microsoft published IP lists and tenant telemetry). Past research used IMDS reads as the critical signal of compromise.
- New or modified Copilot agent artifacts that include HttpRequestAction, redirect handlingields.
- Sudden issuance or use of managed identity tokens tied to Copilot agents followed by Cosmos DB or internal storage access.
- Unusual agent creation timestamps that correlate to customer service hours or to a change in deployment pattern (where an attacker would intentionally trigger actions). Maintain audit trails and correlate with Microsoft tenant logs.
s, limitations and operational risk
Strengths
- Vendor confirmation of the CVE (MSRC/Update Guide) provides a clear remediation path and legal/compliance justification to escalate patching.
- Historical vendor responsiveness to Copilot Studio disclosures (manifest hygiene, fetch confirmations, validDomains cleanup) demonstrates Microsoft can and will push targeted mitigations quickly when research demonstrates systemic weaknesses.
- Public advisory sparseness: the lack of exploit‑level detail makes precise detection tuning difficult. Defenders must assume worst‑case SSRF semantics until proven otherwise.
- Shared infrastructure consequences: Copilot Studio’s multi‑tenant design increases the potential blast radius of information disclosure, meaning tenant‑level detection alone may not capture cross‑tenant risk.
- Vendor‑hosted processing invisibility: exfiltration that occurs in cloud‑hosted model processing can bypass typical network egress monitoring on customer hosts, requiring tenant admin telemetry and cooperation with Microsoft to triage.
How to verify your environment is safe (checklist)
- Verify MSRC/KBA mapping for CVE‑2026‑21520 and apply vendor patches.
- Inventory all Copilot Studio agents and topics that include HttpRequestAction or any outbound network action.
- Remove wildcard or overly permissive va manifests; replace with explicit allowlists.
- Require design reviews and threant that accepts external parameters or can be triggered by untrusted input.
- Hunt for IMDS reads, unexpected Cosmos DB access, or new managed identity use tokens; rotate any identities suspected to have exposure.
Closing assessment and advisory
CVE‑2026‑21520 is vendor‑listed and deserves prompt operational attention. The public CVE record confirms a legitimate issue but intentionally withholds exploit‑level detail; practitioners must therefore rely on credible precedents — especially earlier Copilot Studio SSRF research — to prioritize mitigations. Tenable’s prior SSRF demonstration showed how HTTP‑action primitives combined with redirect/header quirks can lead to IMDS reads and token theft, and Microsoft’s subsequent hardenings reflect both the seriousness of that pattern and its real‑world feasibility. Recommended posture for immediate action:- Treat the CVE as high priority for tenant admins and for teams that create or publish Copilot agents.
- Apply vendor KB/patches as soon as they’re available and mapped to your SKUs.
- Harden agent manifests, restrict who can publish agents, and implement auditing and telemetry to detect IMDS/internal API access originating from Copilot service activity.
Microsoft’s Update Guide (MSRC) remains the authoritative source for remediation mapping; confirm KB identifiers and deployment guidance there before automating any large‑scale patch rollouts.
This article synthesizes the public CVE listing for CVE‑2026‑21520 and the broader Copilot Studio security history to give operators an actionable, defensible triage and mitigation path while vendor‑level technical details remain restricted.
Source: MSRC Security Update Guide - Microsoft Security Response Center