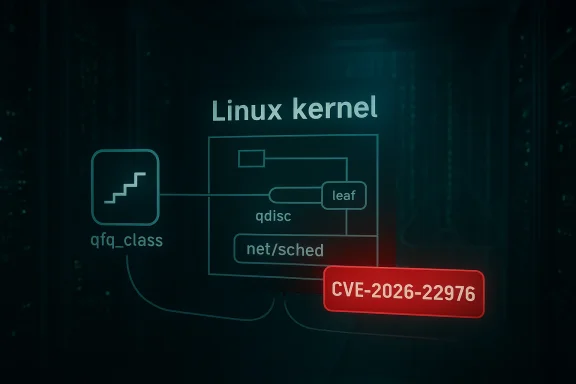
The Linux kernel's QFQ (Quick Fair Queueing) network scheduler was patched this month to fix a NULL pointer dereference that could crash a system when a qdisc reset deactivates an aggregate that is actually inactive — the flaw has been catalogued as CVE-2026-22976 and was published on January 21, 2026.
The vulnerability lives in the kernel's packet scheduling code, specifically in net/sched's sch_qfq module. QFQ is a scheduler for outbound packets that groups flows into aggregates and leaf queueing disciplines (leaf qdiscs). The bug occurs in the qfq_reset path when two separate qfq_class objects point to the same leaf_qdisc: under certain timing conditions one qfq instance may be destroyed while another still has packets enqueued through the shared leaf qdisc, causing a qfq_reset to attempt to deactivate an aggregate that was never active for that particular qfq instance. The resulting attempt reaches qfq_deactivate_agg with a NULL pointer and triggers a kernel NULL pointer dereference, producing a kernel oops and host-level crash (Denial of Service).
This is a local attack vector: the flaw requires privileged or at least local interaction with qdisc state (for example via traffic control operations), not a remote unauthenticated network packet from the outside. As published advisories and vulnerability records note, the practical impact is availability (kernel crash/DoS), rather than loss of confidentiality or integrity.
Conclusion: the vulnerability underscores the ongoing risk in kernel code paths that manage shared resources and lifetimes under concurrency. The kernel community and the major distributions have responded quickly; administrators should now close the window by patching vulnerable hosts, auditing qdisc usage, and validating that their kernels include the upstream fixes.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
The vulnerability lives in the kernel's packet scheduling code, specifically in net/sched's sch_qfq module. QFQ is a scheduler for outbound packets that groups flows into aggregates and leaf queueing disciplines (leaf qdiscs). The bug occurs in the qfq_reset path when two separate qfq_class objects point to the same leaf_qdisc: under certain timing conditions one qfq instance may be destroyed while another still has packets enqueued through the shared leaf qdisc, causing a qfq_reset to attempt to deactivate an aggregate that was never active for that particular qfq instance. The resulting attempt reaches qfq_deactivate_agg with a NULL pointer and triggers a kernel NULL pointer dereference, producing a kernel oops and host-level crash (Denial of Service).This is a local attack vector: the flaw requires privileged or at least local interaction with qdisc state (for example via traffic control operations), not a remote unauthenticated network packet from the outside. As published advisories and vulnerability records note, the practical impact is availability (kernel crash/DoS), rather than loss of confidentiality or integrity.
What exactly goes wrong: a concise technical breakdown
- QFQ classes reference leaf qdiscs that actually hold the packet queues. The code assumes that if the shared leaf qdisc's queue length is > 0 then the class owning that leaf qdisc is active. That assumption is incorrect when the same leaf qdisc is shared across two qfq_class objects.
- A sequence such as: (1) one QFQ instance attached as root enqueues packets into the shared leaf qdisc, and (2) a second QFQ instance is concurrently being destroyed (triggering qfq_reset) — can create a state where the destroying instance sees its own q->q.qlen == 0 but the shared leaf_qdisc->q.qlen > 0 from the other instance's enqueues.
- qfq_reset then attempts to deactivate an already inactive aggregate, calling qfq_deactivate_agg with a NULL aggregate pointer and leading to an immediate NULL pointer dereference in kernel context. The kernel call-trace produced in test repros and in the advisory reproduce this path through qfq_reset -> __qdisc_destroy -> tc_new_tfilter (or similar control-plane flows).
Confirmed facts and timeline
- CVE Assignment: CVE-2026-22976 was assigned and publicized on January 21, 2026. The NVD entry and multiple distribution trackers list that publication date.
- Fix merged into upstream kernel: The fix for the sch_qfq NULL deref was merged into the stable kernel trees and appeared in stable series updates such as the 6.6.121 stable release notes and related backports to maintained stable branches. Kernel changelogs show the sch_qfq fix landed as part of the stable maintenance window that produced 6.6.121 (and related stable backports to other series where maintainers accepted the patch).
- Distro tracking: Debian, Ubuntu and other distributions have published tracking entries and security notices mapping the vulnerability to fixed package versions. Debian's tracker shows the vulnerability and the fixed package versions pushed to security suites; Ubuntu lists the issue with medium priority and references the kernel fix commit. These distribution entries confirm that the fix has been packaged for mainstream distributions.
- Severity: Several vulnerability feeds score the issue as medium with a CVSSv3 base score around 5.5 (attack vector Local, privileges required Low, impact: Availability high). The principal impact is Denial-of-Service via kernel crash.
Who is affected?
- Any Linux systems that have the QFQ scheduler enabled and in use can be affected. QFQ is not the default on all distributions, but it is present in the kernel and may be used in specialized networking setups or distributions that enable it.
- Systems running kernels that do not include the upstream fix or a vendor backport remain vulnerable. Distribution trackers and advisories indicate fixes were backported to multiple stable kernel branches; administrators should consult their distro's security advisory for specific package versions.
- The vulnerability requires local interaction with qdisc state (for example, via tc, traffic-control configuration, or kernel interfaces that create/destroy qdiscs). Remote unauthenticated exploitation is not indicated in published advisories. Attackers with local access or the ability to run traffic-control commands could trigger the kernel crash.
Exploitation, reproducibility and indicators of compromise
Exploitation is straightforward in the sense that a crafted sequence manipulating qdisc attachments, deletions, and traffic can reliably produce the crash in testing environments. Publicly available logs and advisory reproductions show the kernel oops call trace that points to qfq_deactivate_agg and qfq_reset as the faulting frames. Administrators should look for kernel oops messages in system logs resembling:- a kernel NULL pointer dereference (page fault at address 0)
- call traces that include qfq_deactivate_agg, qfq_reset_qdisc/qfq_reset, and qdisc destruction paths (qdisc_reset / __qdisc_destroy)
- netlink/rtnetlink or tc-related context in the trace (since control-plane actions like tc_new_tfilter can trigger the qdisc put/destroy path)
Mitigation and remediation guidance
Immediate, practical actions for system administrators:- Patch: The recommended and definitive mitigation is to install a kernel that includes the upstream fix or your vendor's backport. Consult your distribution's security advisory and install the updated kernel package(s) — then reboot to activate the patched kernel. Debian and Ubuntu security trackers list fixed package versions; stable kernel releases such as 6.6.121 include the upstream patch. Prioritize rolling this update into production systems where QFQ is used.
- Verify whether QFQ is in use: If you are uncertain whether your host uses QFQ, check qdisc configuration on interfaces:
- Use tc qdisc show to list qdiscs. If any interfaces show qfq qdiscs installed as root or attached to classes, those interfaces are potential exposure points.
- If QFQ is not required in your environment, remove or replace it with a more commonly used and maintained qdisc such as fq_codel or pfifo_fast, until you can apply the kernel update safely.
- Workarounds when patching isn't immediately possible:
- Remove or avoid configuring QFQ on interfaces (delete the qfq root qdisc); this prevents the vulnerable code path from being exercised. Note that deleting qdiscs can impact traffic shaping and QoS behavior; plan changes accordingly.
- Avoid operations that temporarily reference alternate QFQ instances on the same device that could cause overlapping leaf qdisc lifetimes — for example, minimize concurrent tc filter/tc qdisc manipulation in production until patched.
- Where feasible, restrict local access (via sudo/policy) to users who can run traffic-control commands, and audit recent tc/rtnetlink operations.
- If your environment uses automated orchestration that manipulates qdiscs, pause or gate those automation jobs until systems are patched.
- Detection and monitoring:
- Add kernel oops and dmesg monitoring to existing observability/alerting pipelines. Pattern-match for qfq_deactivate_agg, qfq_reset, qdisc_destroy, and netlink/tc related call traces.
- Monitor package feeds and vendor advisories for pending updates if your distribution has not yet published a fixed package.
A distribution maintainer perspective
Distribution maintainers and kernel package teams have already mapped CVE-2026-22976 into their release management pipelines. Debian's tracker lists fixed versions for several release series, and Ubuntu published its security advisory marking the issue medium priority, with the kernel fix tied to a specific kernel commit. LWN and upstream changelogs confirm the upstream patch; maintainers are packaging and backporting the fix into their respective kernel package streams. System owners should consult their distro-specific advisories and package indices for the precise package version numbers to install.Risk assessment and operational impact
- Severity profile: The vulnerability is an availability issue — attacker-controlled kernel crash and host-level Denial of Service. CVSS scoring in multiple feeds places it in the mid-range (around 5.5) because it requires local access (not remotely exploitable) but can reliably take down a host if triggered.
- Exploitability: Because the bug requires local interactions with qdisc lifecycle, it is less attractive to remote threat actors who lack local access. However, in multi-tenant environments, containers, or shared hosting systems where multiple users have delegated control or where orchestration components manipulate qdiscs, this becomes a meaningful local-privilege risk. Attackers that already have low-level access, or untrusted users with the ability to issue tc/netlink commands, can weaponize the bug for DoS.
- Business impact: Kernel crashes are disruptive. On routers, edge devices, NAT gateways, appliances, and performance-sensitive hosts, an unexpected kernel panic can disrupt services, cause failovers, or complicate incident response. Even a single scheduled update that introduces a regression can manifest as repeated crashes across fleet nodes if qdisc state differs — so careful rollout and monitoring are essential.
Developer and code-level notes (for kernel engineers)
- Root cause: The code conflates leaf qdisc queue length with class active state and fails to handle the case of a shared leaf qdisc referenced by multiple qfq_class owners. The patch addresses the logic in qfq_reset and qfq_deactivate_agg to avoid deactivating aggregates that are not owned/active for that particular qfq instance. Upstream maintainers applied the fix in the stable branch and marked or recommended backports to affected stable series.
- Patch hygiene: The kernel community followed standard practice: a focused change in net/sched that adjusts the deactivation check and ensures the aggregate pointer is validated before use. When evaluating any backport or distro patch, check for these properties:
- Conservative change-set that only alters the deactivation path and pointer checks
- Tests for qdisc lifecycles where multiple qfq instances can reference the same leaf qdisc
- Clear regression test coverage, where feasible, that simulates the tc_new_tfilter qdisc_put/destroy sequence in concurrent workloads
- For downstream maintainers: Do not cherry-pick unrelated commits. Apply the upstream patch series that maintainers have reviewed and ensure backports also include any required locking or concurrency fixes that touch the same codepaths.
Practical checklist for administrators (quick, actionable)
- Identify: Run tc qdisc show on all network interfaces to detect qfq usage.
- Prioritize: For hosts running qfq, prioritize kernel updates and schedule reboots during maintenance windows.
- Patch: Install vendor-provided kernel security updates that include the sch_qfq fix; verify the package version against your distro advisory.
- Workaround: If immediate patching is impossible, remove qfq qdiscs or restrict who can change qdisc state.
- Monitor: Watch dmesg/syslog for kernel oops traces referencing qfq_reset/qfq_deactivate_agg and add alerts.
- Test: In staging, validate that kernel upgrades do not regress network behavior under your workload.
Strengths and limitations of the fix
Strengths:- The upstream fix is narrow and targeted to the qfq lifecycle logic; it avoids large-scale refactors and therefore reduces regression risk.
- Vendors and distributions have began packaging and backporting the fix, which reduces the window of exposure for production systems that follow vendor updates.
- Because QFQ is not universally used, organizations might miss the issue if they do not routinely audit qdisc configuration.
- In multi-tenant or automated orchestration environments where qdisc manipulation is frequent, the root cause is a concurrency/lifetime issue — such environments will require careful testing of backports to ensure the fix interacts correctly with existing vendor-specific changes.
- Workarounds such as removing QFQ can negatively affect QoS and network performance; teams must understand the operational trade-offs before making changes.
- While many distribution trackers and the upstream changelog show the fix and backports, the exact list of all affected kernel versions across every vendor build is maintained by each vendor. Administrators should rely on their distribution's published package advisories for the authoritative fixed-version list. If you manage custom kernels, verify your kernel tree includes the upstream commit(s) labeled for this fix.
Bottom line
CVE-2026-22976 is a legitimate kernel-level Denial-of-Service vulnerability that targets the QFQ scheduler's deactivation logic. It is locally exploitable and results in a kernel NULL pointer dereference and crash. The correct remediation path is to apply vendor patches or an upstream kernel that contains the sch_qfq fix (stable releases and backports are already being packaged by distributions). Where patching is delayed, remove or avoid deploying QFQ, lock down local access to qdisc control, and monitor kernel logs for telltale oops traces. Prioritize remediation on network-edge devices and multi-tenant hosts where local qdisc manipulation is more likely or where system availability is critical.Conclusion: the vulnerability underscores the ongoing risk in kernel code paths that manage shared resources and lifetimes under concurrency. The kernel community and the major distributions have responded quickly; administrators should now close the window by patching vulnerable hosts, auditing qdisc usage, and validating that their kernels include the upstream fixes.
Source: MSRC Security Update Guide - Microsoft Security Response Center