 CVE-2026-31549: Linux Kernel cp2615 NULL Pointer Dereference in I2C Probe Path
CVE-2026-31549: Linux Kernel cp2615 NULL Pointer Dereference in I2C Probe Path
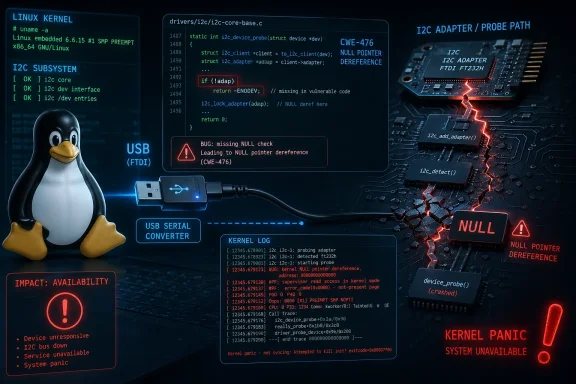
CVE-2026-31549 is a Linux kernel vulnerability affecting the Silicon Labs CP2615 I2C driver. The issue occurs in the i2c-cp2615 driver during device probing, where the driver uses the USB device’s serial string as the I2C adapter name without first confirming that the serial string exists. If a CP2615-compatible USB device does not provide a serial number, the driver may dereference a NULL pointer and crash the kernel.In practical terms, this is a local denial-of-service vulnerability. A malicious or malformed USB device could trigger the bug when connected to a vulnerable Linux system, potentially causing a kernel panic or system instability. The vulnerability is categorized as CWE-476: NULL Pointer Dereference.
The affected component is tied to support for the Silicon Labs CP2615 USB sound card and I2C adapter, exposed through the Linux kernel option
CONFIG_I2C_CP2615. LKDDb identifies this driver as i2c-cp2615, with support appearing across Linux kernel series beginning with 5.13 and continuing through later 6.x and release-candidate versions. The CP2615 itself is a Silicon Labs USB-to-I²S digital audio bridge with I2C-related functionality, commonly relevant to embedded, audio, and development-board environments.Severity and Exploitability
NVD scoring in the data you provided lists the vulnerability as:- CVSS v3.1 Base Score: 5.5
- Severity: Medium
- Vector:
AV:L/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H
This is especially relevant for:
- Linux workstations where users can connect USB devices
- Embedded Linux systems using CP2615-based audio hardware
- Kiosks, appliances, or lab systems with exposed USB ports
- Development environments using USB audio or I2C bridge devices
- Systems that automatically load the
i2c-cp2615module
Affected Kernel Versions
Based on the CPE information you provided, affected versions include Linux kernel lines starting from 5.13 and spanning multiple long-term and mainline branches, with fixes appearing in later stable releases. The affected ranges include, among others:- 5.13 and 5.13.1 through before 5.15.203
- 5.16 through before 6.1.167
- 6.2 through before 6.6.130
- 6.7 through before 6.12.78
- 6.13 through before 6.18.20
- 6.19 through before 6.19.10
- 7.0 release candidates rc1 through rc7
i2c: cp2615 patch.Remediation
The primary fix is to update to a kernel version or distribution kernel package that includes the cp2615 patch. The upstream fix changes the driver behavior so that it verifies the presence of a USB serial number before using it as the I2C adapter name. NVD lists multiple upstream stable kernel patch references for this issue.Recommended actions:
- Apply vendor kernel updates from your Linux distribution.
- Reboot into the patched kernel after installation.
- Verify the running kernel, not just the installed package.
- If immediate patching is not possible, consider disabling or blacklisting the
i2c-cp2615module where CP2615 support is not needed. - Restrict physical or local USB access on systems where untrusted users may connect devices.
Risk Assessment
For most servers, this CVE is likely a low-to-moderate operational risk, especially if USB access is restricted or the affected driver is not loaded. For endpoints, embedded devices, audio appliances, lab systems, or hardware-development setups, the risk is higher because attacker-controlled USB devices are a realistic threat model.This vulnerability is not described as remote code execution or privilege escalation. Its main impact is availability loss through a kernel crash. However, kernel NULL pointer dereferences are still important because they can take down production systems, disrupt appliances, and create reliability problems in environments where untrusted hardware may be connected.
Bottom Line
CVE-2026-31549 is a medium-severity Linux kernel denial-of-service issue in the CP2615 I2C driver. It is caused by unsafe handling of a missing USB serial string during device probing. Organizations should patch affected kernels, verify whetheri2c-cp2615 is present or loaded, and restrict untrusted USB device access where patching is delayed.Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center