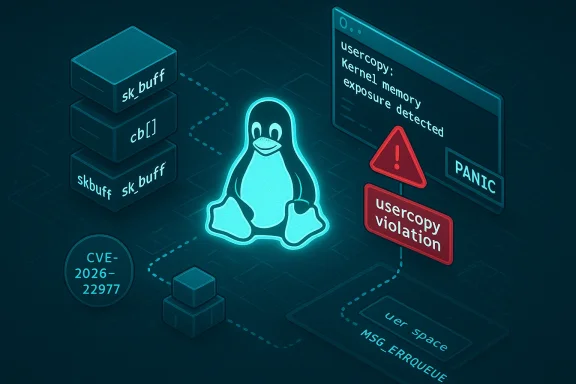
A subtle but consequential weakness in the Linux kernel’s socket handling has been assigned CVE‑2026‑22977: a hardened‑usercopy panic in sock_recv_errqueue that can crash systems compiled with usercopy hardening enabled. The defect is not a remote code‑execution hole, but it produces a deterministic kernel panic (availability impact) when a particular sequence of TCP skb allocation, cloning and error‑queue delivery intersects with userspace reads of the socket error queue (recvmsg(MSG_ERRQUEUE)). Upstream maintainers merged a targeted fix into the stable trees; major distributions are shipping or preparing backports. System administrators and kernel packagers should treat this as a pragmatic availability risk and prioritize updates for affected kernels, while understanding the limited attack surface and the correct operational mitigations.
The Linux kernel uses a variety of slab caches to allocate frequently used structures quickly. One such object is the network socket buffer (sk_buff, or “skb”), a central structure used by the networking stack to hold packet data, metadata and per‑packet control blocks.
This is not a typical memory corruption bug exploitable for privilege escalation; rather, it is a correctness/hardening mismatch that causes availability loss under a narrow set of conditions.
usercopy: Kernel memory exposure attempt detected from SLUB object 'skbuff_fclone_cache' (offset 296, size 16)!
That diagnostic is explicit: the kernel’s hardened usercopy mechanism detected a copy operation from a SLUB object that had not advertised the correct usercopy whitelist, and the kernel refuses to continue.
Distribution vendors have responded by preparing and releasing kernels that include the upstream patch or backports:
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
The Linux kernel uses a variety of slab caches to allocate frequently used structures quickly. One such object is the network socket buffer (sk_buff, or “skb”), a central structure used by the networking stack to hold packet data, metadata and per‑packet control blocks.- The kernel exposes some skb metadata to userspace through ancillary data on sockets; timestamping and error reporting use the socket error queue, read via recvmsg(MSG_ERRQUEUE).
- To improve performance, the kernel creates specialized caches such as
skbuff_head_cacheandskbuff_fclone_cache. The latter is used to pre‑allocate cloneable skbs (fclones) for lightweight cloning operations. - Hardened usercopy is a kernel hardening mechanism that restricts arbitrary kernel memory from being copied into userspace. When enabled, every kernel object that may be the source of a copy to userspace must declare a usercopy region so the runtime can verify and permit only those safe, whitelisted memcpy operations.
skbuff_fclone_cache was being created without a declared usercopy region for the cb[] control area within sk_buff, while code paths that copy socket error information to userspace expect skb->cb to be whitelisted. When hardened usercopy is enabled (CONFIG_HARDENED_USERCOPY=y), that mismatch leads to a runtime hardening check failing and the kernel aborting with a BUG() to prevent a potential kernel memory leak into userspace — i.e., a panic designed to avoid information exposure.This is not a typical memory corruption bug exploitable for privilege escalation; rather, it is a correctness/hardening mismatch that causes availability loss under a narrow set of conditions.
How the bug is triggered — a technical walkthrough
To understand the risk, it helps to step through the deterministic sequence that leads to the panic:- TCP allocates an skb using a specialized allocator that draws from the
skbuff_fclone_cache(alloc_skb_fclone()). This is the pre‑allocated fast clone pool. - The skb is cloned via skb_clone(), producing a lightweight clone that references the same data but carries per‑packet metadata in
skb->cb. - The cloned skb is queued to the socket error queue (sk_error_queue) for purposes like timestamp reporting.
- A userspace process calls recvmsg with the MSG_ERRQUEUE flag to read the socket’s error queue.
- The kernel code path
sock_recv_errqueue()callsput_cmsg()to populate a control message with the error/timestamp data. Internallyput_cmsg()copies fields fromskb->cbinto the userspace buffer. - Because
skbuff_fclone_cachewas created without registering thecb[]region as a legal usercopy source, the hardened usercopy runtime check (__check_heap_object()/ SLUB usercopy checks) flags the copy attempt as an illegal kernel memory exposure. The kernel then triggers a BUG() or panic to stop the copy.
usercopy: Kernel memory exposure attempt detected from SLUB object 'skbuff_fclone_cache' (offset 296, size 16)!
That diagnostic is explicit: the kernel’s hardened usercopy mechanism detected a copy operation from a SLUB object that had not advertised the correct usercopy whitelist, and the kernel refuses to continue.
Scope and impact: who is affected?
This vulnerability has a narrow but real scope:- Affected code: Linux kernel networking stack — the socket error queue handling and the skb clone cache initialization code. This is upstream kernel code, and fixes were merged into upstream stable branches.
- Configuration requirement: The kernel must be compiled with hardened usercopy enabled (CONFIG_HARDENED_USERCOPY). That is a compile‑time option; not every distribution or custom kernel enables it by default, but many modern kernels and security‑oriented builds do. Some mainstream distribution kernels include hardened usercopy as part of a broader hardening profile; others may not.
- Attack vector: Local (AV:L). The crash is triggered when userspace reads the error queue; that is, the attack requires either an unprivileged process that can open and read a socket’s MSG_ERRQUEUE, or an interaction that causes userspace to perform that read. In practice, the path is local rather than remote. Network traffic is part of the sequence (the skb creation/cloning), but the panic arises at the moment of copying to userspace.
- Severity: Availability impact. The kernel panic causes denial of service for the host. There is no reliable public evidence that this leads to arbitrary code execution or information disclosure; the kernel deliberately aborts to avoid memory leakage.
Upstream fixes and vendor responses
Kernel maintainers merged a surgical fix into the stable trees to ensure theskbuff_fclone_cache is created with the appropriate usercopy whitelist for the cb[] region. Stable release branches carrying the patch were published as part of normal stable updates; examples from the upstream stable review cycle include the 6.12.x and 6.1.y maintenance series that contained fixes around the January 2026 cycle.Distribution vendors have responded by preparing and releasing kernels that include the upstream patch or backports:
- Enterprise and major Linux distributions have published advisories or package updates that address the issue in their supported kernel lines.
- Some vendors classify the issue as medium severity because it is locally triggered and results in availability loss (no data‑exfiltration or privilege escalation is implied by the patch description), while others mark it for prompt backport to long‑term support kernels because of the real operational risk of a crash.
- Favor vendor kernels that include the upstream stable patch (the fix was merged into stable trees and backport candidates) and install vendor updates when available.
- If you manage custom kernel builds, ensure your tree includes the upstream patch or update to a patched stable point.
Detection and mitigation — practical steps for admins
If you manage Linux servers, here are concrete steps you can take now to assess exposure and mitigate risk.- Detect whether your kernel was built with hardened usercopy enabled
- Run:
1.) grep HARDENED_USERCOPY /boot/config-$(uname -r)
2.) Alternatively, inspect your kernel config under /proc/config.gz (if available) or the distro’s packaged kernel config. - If the result shows CONFIG_HARDENED_USERCOPY=y, your kernel is compiled with the hardening that makes this bug relevant.
- Search logs for signs of the panic
- Look for kernel messages such as:
- "usercopy: Kernel memory exposure attempt detected from SLUB object 'skbuff_fclone_cache' (offset ...)"
- Any BUG or OOPS traceback that references mm/usercopy.c, sock_recv_errqueue, put_cmsg, or skbuff_fclone_cache.
- These messages indicate a hardened usercopy check triggered the abort.
- Patch promptly
- The most reliable mitigation is to update to a kernel that includes the upstream fix. Use your distribution’s security advisory and update channels.
- For long‑term kernel lines, look for the vendor’s backport package; distributors typically release security updates for their supported kernels quickly when an upstream fix is available.
- If update is not immediately possible
- Consider temporary containment:
- Reduce exposure by restricting which processes can open or read sockets under your trust boundary. In practice, there is no simple sysctl to disable the specific path.
- Avoid running untrusted or network‑facing processes that may exercise MSG_ERRQUEUE reads on sockets you host.
- Avoid reconfiguring your kernel to disable hardened usercopy as a mitigation — that takes away a valuable hardening protection and is not recommended except in carefully controlled test environments where you accept the security trade‑off.
- Enterprise deployment guidance
- Test the patched kernel in a staging environment against your workload and performance baseline before widespread rollout.
- Use staged rollouts, canaries, and monitoring to detect regressions. Although this was a correctness fix, any kernel update can expose subtle driver or platform interactions.
- If you subscribe to livepatch services, check with the livepatch vendor whether a hotpatch is available; if not available, plan for a scheduled maintenance reboot with the updated kernel.
Why this bug matters: analysis and risk assessment
Several aspects make this issue noteworthy for enterprise and cloud operators:- Deterministic availability risk: The bug produces a hard failure (BUG/panic) when the runtime check is exercised. Even if the scope is limited to systems with hardened usercopy enabled, those systems are typically chosen precisely because they run high‑security or auditing profiles. An availability bug in a hardened kernel undermines the operational benefits of that very hardening: systems made safer against subtle kernel memory exposure can be pushed into panic by a correctness mismatch.
- Hardening vs. correctness tradeoff: Hardened usercopy is explicitly designed to detect and halt suspicious kernel‑to‑user copies — its assertion‑style behavior is to crash rather than risk data leakage. This case highlights a recurring theme in kernel hardening: hardening layers can expose latent initialization mistakes (missing usercopy whitelists), turning correctness bugs into availability incidents. The ultimate fix is always to reconcile the initialization and the copy sites — which is what upstream did.
- Exploitability profile: The CVE is not a remote remote RCE. The attack vector is local (or a local read triggered after network activity). That reduces the immediacy of exploitation across public networks, but not its importance: in multi‑tenant hosts, containers, or environments where untrusted code can execute, a local availability trigger can be weaponized to cause denial‑of‑service.
- Distribution response and patch cadence: The patch was merged to upstream stable trees, and distribution vendors have been moving to backport the fix into their long‑term kernels. Organizations that rely heavily on vendor‑supplied kernels should prioritize installing the vendor security updates; those building custom kernels must pick up the upstream patch or rebuild from a patched stable branch.
Code-level takeaway for kernel engineers
For kernel maintainers and contributors the root cause is instructive:- Always ensure caches and slab objects that can be sources of usercopy to userspace declare the correct usercopy regions. The kernel’s
kmem_cache_create_usercopy()and related SLUB interfaces exist for this reason; omitting the usercopy whitelist leaves a window where a legitimate copy site expects the object to be listed, but the allocator’s metadata does not reflect that. - Hardened usercopy is an effective guard, but it is only as useful as the accuracy of the annotations. When adding new caches or refactoring allocators, a checklist should include declaring usercopy regions for any object that might be copied or partially copied to userspace.
- Instrumentation and regression tests: Automated kernel test suites and regression checks should include test cases that exercise usercopy‑sensitive paths under hardened configurations — specifically tests that exercise ancillary data (control messages), MSG_ERRQUEUE handling, and skb clone paths. Such tests can catch missing usercopy metadata before commit or release.
Frequently asked operational questions
- Is this a remote code execution (RCE) vulnerability?
- No. The behavior described is a hardened usercopy violation that leads to kernel BUG/panic when a copy to userspace is attempted from an object that lacks a usercopy whitelist. There is no evidence upstream provided or public reporting that this can be converted into arbitrary code execution or information disclosure.
- Do all Linux systems need patching immediately?
- Systems whose kernels were built without CONFIG_HARDENED_USERCOPY are unlikely to experience the panic from this issue. However, many distribution kernels do enable hardened usercopy as a security hardening. Operators must check kernel configurations and patch accordingly. Given the availability impact, environments that run hardened kernels should prioritize updates.
- Can I mitigate by toggling a sysctl or runtime parameter?
- No simple, safe runtime sysctl exists to disable this exact path. Disabling hardened usercopy would remove a broad security protection and is not a recommended operational workaround. The recommended mitigation is to install a vendor/patched kernel.
- Will cloud providers (public clouds) be affected?
- Public cloud providers that run customized host kernels or allow customer VMs to run kernels may be affected if the host or guest kernel includes hardened usercopy. Cloud customers should follow the provider’s advisory. In multi‑tenant or container hosts the local attack surface increases risk, so providers typically patch host kernels promptly.
Strengths of the upstream response and residual risks
Strengths:- The upstream fix is surgical and limited in scope: it corrects the cache initialization to include the proper usercopy whitelist, eliminating the mismatch that triggers the hardened usercopy check.
- The problem was assigned a CVE and tracked across stable branches, allowing distribution vendors to backport and ship fixes to supported kernels.
- The hardening mechanism worked exactly as intended — it detected an unexpected kernel memory copy and prevented a potential data exposure by aborting. That behavior, while causing a crash, preserved confidentiality.
- Operational availability: For systems that must remain continuously available, even a low‑frequency, local crash vector is significant. Operators must account for the maintenance window and testing required to roll out patched kernels.
- Detection challenges: Unless you have explicit monitoring for the exact kernel log lines or perform kernel config audits, you may miss exposure until a crash occurs. Proactive auditing of kernel builds and configurations is necessary.
- Livepatch gap: For some enterprise customers, a livepatch (hotfix) would be preferable to a full reboot. Not all livepatch services will have an immediate fix for this precise change; consult your vendor. If livepatch is not available, schedule an update/reboot.
Recommended checklist for administrators
- Immediately:
- Verify whether your kernels are built with CONFIG_HARDENED_USERCOPY enabled.
- Inspect recent kernel logs for hardened usercopy violations referencing skbuff_fclone_cache, sock_recv_errqueue, put_cmsg, or mm/usercopy.c.
- Within 24–72 hours:
- Apply vendor security updates that include the upstream fix, test them in staging.
- For custom kernels, pull the upstream stable fixes and rebuild on a tested branch, then deploy with a controlled reboot.
- For longer term hardening:
- Add the usercopy‑related kernel config checks into your build/test pipeline so missing whitelists are detected during CI.
- Add monitoring rules that alert on the specific hardened usercopy kernel log line and general OOPS/BUG patterns.
- Maintain a policy for livepatch evaluation and vendor support to minimize downtime for future kernel hardening regressions.
Conclusion
CVE‑2026‑22977 is a clear example of the tradeoffs inherent in aggressive kernel hardening: mechanisms like hardened usercopy raise the bar against kernel memory exposure, but they also force correctness problems to surface — sometimes as abrupt availability failures. The bug itself is a correctness/initialization oversight; the fix is straightforward and has been merged upstream and distributed to vendors. For operators, the two practical lessons are to (1) verify whether your kernels enable hardened usercopy, and (2) prioritize deployment of vendor‑supplied or upstream‑patched kernels for any hosts that do. Patch, test, and monitor — and treat hardened kernels as both a security asset and an operational responsibility.Source: MSRC Security Update Guide - Microsoft Security Response Center