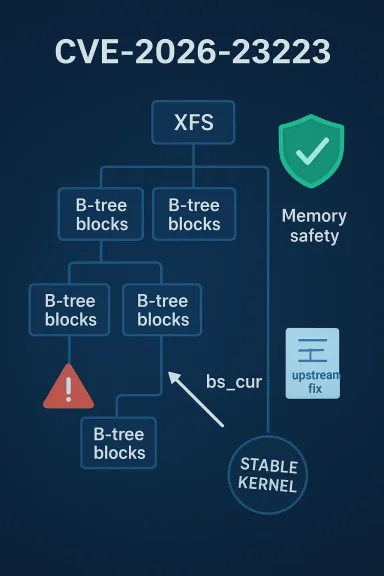
A one-line mistake in XFS scrub code has produced a classic memory-safety problem with outsized operational impact: a use-after-free (UAF) in the XFS filesystem’s B-tree checking path, tracked as CVE-2026-23223, has been fixed upstream and is now being rolled into stable kernels and Linux distribution updates. The bug is straightforward to describe at the source level — the code dereferences a cursor after a related cursor may already have been freed — but the implications for systems that run XFS, for administrators who depend on xfs_scrub and online fsck, and for vendors who ship kernel artifacts are anything but trivial.
XFS is a high-performance journaling filesystem widely deployed in enterprise Linux, cloud images, and storage appliances. Its scrub and online-fsck infrastructure perform integrity checks and repairs while filesystems stay mounted; those mechanisms walk B-trees and manage lightweight cursor objects that represent traversal state. The newly catalogued CVE-2026-23223 sits inside that scrub machinery: a function named xchk_btree_check_block_owner attempted to inspect a cursor (bs->cur) to determine whether it aliased another cursor (bs->sc->sa.{bno,rmap}_cur) after that other cursor may already have been freed. That ordering produces a use-after-free — reading memory the kernel may have already released — which can lead to kernel memory corruption, crashes (kernel oops/panic), and in worst cases provide a path to privilege escalation.
This vulnerability was reported, assigned CVE-2026-23223, and recorded in the public CVE/NVD ecosystem; multiple independent sources tracked the issue, the upstream patch, and the stable-kernel rollouts. NVD and distribution security trackers reference the upstream kernel commits that close the issue, and the patch author and reviewers left a clear explanation of the regression and its root cause: the temporal ordering guarantee that previously existed was broken when the developer removed a small enum type (xfs_btnum_t), which previously ensured the btree number was sampled before cursors were freed. The fix restores the sampling step before any freeing occurs.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
XFS is a high-performance journaling filesystem widely deployed in enterprise Linux, cloud images, and storage appliances. Its scrub and online-fsck infrastructure perform integrity checks and repairs while filesystems stay mounted; those mechanisms walk B-trees and manage lightweight cursor objects that represent traversal state. The newly catalogued CVE-2026-23223 sits inside that scrub machinery: a function named xchk_btree_check_block_owner attempted to inspect a cursor (bs->cur) to determine whether it aliased another cursor (bs->sc->sa.{bno,rmap}_cur) after that other cursor may already have been freed. That ordering produces a use-after-free — reading memory the kernel may have already released — which can lead to kernel memory corruption, crashes (kernel oops/panic), and in worst cases provide a path to privilege escalation.This vulnerability was reported, assigned CVE-2026-23223, and recorded in the public CVE/NVD ecosystem; multiple independent sources tracked the issue, the upstream patch, and the stable-kernel rollouts. NVD and distribution security trackers reference the upstream kernel commits that close the issue, and the patch author and reviewers left a clear explanation of the regression and its root cause: the temporal ordering guarantee that previously existed was broken when the developer removed a small enum type (xfs_btnum_t), which previously ensured the btree number was sampled before cursors were freed. The fix restores the sampling step before any freeing occurs.
What happened — technical recap
The bug in plain terms
- The vulnerable function is xchk_btree_check_block_owner inside the XFS scrub (online fsck / xfs_scrub) infrastructure.
- During checks, code maintains several cursors that point to B-tree positions. One cursor may be freed as part of cleanup or repair logic.
- The code path attempted to dereference bs->cur to check whether it aliases bs->sc->sa.bno_cur or bs->sc->sa.rmap_cur after those other cursors may have been freed.
- Dereferencing a pointer after its target has been released produces a use-after-free: the pointer may reference invalid or reallocated memory, leading to unpredictable behavior in kernel mode.
Root cause and regression vector
The regression that opened the window for UAF was subtle and human: a small cleanup — the removal of the xfs_btnum_t enumerated type — changed the order of operations in a way that no longer sampled the B-tree number before freeing related cursor objects. In other words, a prior safety step moved or disappeared during a refactor, and a rare timing path could then dereference a freed cursor. The upstream patch restores the necessary sampling (i.e., read the type into a local variable before any free can happen) so the code no longer relies on the cursor remaining valid. Upstream discussion and the patch notes make this explicit.Where the vulnerability lives in the stack
This is a kernel-space vulnerability in a widely used filesystem module. It is not a remote network-facing bug: an attacker must have local code-execution capability (or be able to induce specific filesystem operations locally) and must interact with XFS scrub or the specific online-fsck code paths that trigger the problematic logic. In deployed environments, that can still be serious: cloud guests, container hosts, and automated maintenance tasks frequently run scrub-like checks or accept actions that exercise filesystem metadata code.Sources, verification, and timeline
I cross-checked the upstream patch discussions, stable-kernel rollups, and multiple independent security trackers to ensure the description and remediation guidance are accurate.- The upstream patch and discussion were submitted by XFS maintainers and reviewed on the kernel mailing lists; reviewers called out the exact code paths and approved the change. The patch text is present in stable-kernel discussions and the XFS patchset threads.
- The vulnerability was indexed through the CNA/NVD pipeline and now appears in the NVD entry for CVE-2026-23223; the NVD record references the stable kernel commits that address the issue. That listing confirms the CVE assignment and links back to the kernel commits used by distributors.
- Vendor and third‑party vulnerability databases — including distribution trackers such as Ubuntu’s security notices — have cataloged the CVE and started the evaluation/patching process for specific kernels and releases. Ubuntu’s page lists the CVE and indicates distribution teams must evaluate and ship kernel updates.
- Coverage in security vendors and vulnerability feeds (SentinelOne, Snyk, cvefeed, etc.) independently described the same root cause and the same remediation: apply kernel patches or upgraded kernels that include the upstream fix.
Impact analysis — who should care and why
Systems at risk
- Any host that mounts XFS filesystems and runs the kernel code paths touched by xfs scrub / online fsck may be affected until patched.
- Threat scenarios range from straightforward denial‑of‑service (kernel oops or panic) to potential kernel memory corruption that could be leveraged into privilege escalation by a sophisticated local attacker.
- Systems that run automatic maintenance jobs (cron-triggered xfs_scrub), use automated recovery tools, or allow untrusted local code (shared hosting, multi‑tenant cloud VMs, CI runners) are higher-risk because those contexts increase opportunities to interact with the vulnerable logic.
Operational consequences
- Availability: A malformed or adversarially crafted interaction with the affected code could produce a kernel panic, causing downtime of services and requiring reboots.
- Integrity and confidentiality: While a simple crash is the most probable outcome, memory corruption in kernel space can sometimes be weaponized for privilege escalation or to read adjacent memory — although exploiting such conditions reliably is technically challenging. Security teams should therefore treat the UAF as a high‑impact memory-corruption bug until proven otherwise.
- Supply-chain and backport complications: Many vendors ship kernels with selective backports. A kernel package that claims to be “patched” may have had the original fix rebased or altered; administrators need to confirm that the correct commit or behavior is present, not just that a package number changed. Distribution advisories (Ubuntu, Debian, Red Hat, etc.) will indicate when a patched kernel is available for specific releases.
Cloud, virtualization, and Windows intersections
- Cloud images: Public cloud providers and appliance images that include XFS and custom kernels (or vendor‑provided kernels) must inspect their kernel trees. Microsoft’s product security guidance for Linux components historically focuses on product-scoped attestations (for example, Azure Linux), but customers should not assume that a single product attestation means all vendor-supplied images are safe; independent artifact inventory is necessary. Our community threads and prior analysis note that vendor attestations are product-scoped and not an exhaustive inventory of every binary Microsoft ships. Administrators running Windows Subsystem for Linux (WSL) or other Windows-hosted Linux artifacts should verify the kernel in play — WSL2 uses a Microsoft-patched kernel — against the upstream fixes or vendor advisories.
Mitigation and remediation — practical guidance
If you manage Linux systems that use XFS, treat CVE-2026-23223 as actionable with the following prioritized steps.Immediate triage (minutes to hours)
- Inventory: Identify systems that mount XFS volumes and record their kernel versions. Use your configuration management system to locate hosts running kernels built from unpatched upstream commits or kernels older than the latest stable release that includes the fix. Ubuntu, Debian, and distribution trackers have CVE entries you can query for status.
- Reduce exposure: If a host runs untrusted code or allows guest code to trigger maintenance operations, consider restricting who can run xfs_scrub or similar repair utilities until you can patch. The immediate, low-cost mitigation is avoid running xfs_scrub on vulnerable kernels in production contexts where untrusted users have access. SentinelOne and vendor guidance explicitly recommend pausing scrub runs until patched.
- Monitoring: Add short-term alerts for kernel oops/panic signatures in your logging pipeline. Any new kernel oops with XFS tracebacks should be investigated as a potential hit. Enable kernel auditing and collect crash dumps for forensic analysis.
Patch and update (hours to days)
- Apply vendor-supplied kernel updates: Prefer distribution packages (stable kernels and CVE patches) or vendor-supplied fixes. Verify the distribution advisory before rollout. Distribution security pages and CVE trackers list CVE-2026-23223 and track patch availability.
- For custom kernels: Pull the upstream commits referenced by NVD and apply them to your kernel tree (or rebase onto a stable kernel that includes the commits). Confirm the exact commit references exist in your tree: NVD and other trackers point to the kernel commits that fix the bug. If you backport, include the sampling change described in the upstream patch (sample the btree type before freeing).
- Live-patching: If you use live kernel patching (kpatch, kgraft, ksplice), check vendor patches for a livepatch bundle. If none is available immediately, schedule a reboot window to install the patched kernel.
Validation and post-patch checks (days)
- Test restores and scrub runs in a staging environment that mirrors production: run xfs_scrub, exercise B-tree heavy operations, and monitor for warnings or oopses.
- If you must run scrubs during the patching window, do so only on isolated maintenance systems with full backups and under controlled conditions. The vendor guidance suggests treating scrub as potentially triggering the vulnerable path; only proceed if you accept the risk.
Code-level explanation for engineers
For kernel developers or engineers who need to audit or backport the change, the fix is local and conservative: determine the B-tree type (which previously was captured by the now-removed xfs_btnum_t enumeration) before freeing any cursor that could cause bs->cur to become invalid. The patch therefore:- Samples the necessary type or identification field into a local variable before any cursor free occurs.
- Uses that local sample to perform alias checks without dereferencing a possibly freed cursor.
- Leaves the broader scrub semantics unchanged but restores the temporal ordering guarantee required for safe access.
Risk assessment and exploitation likelihood
- Immediate exploitation from remote attackers: unlikely. This is a local kernel-space UAF that requires invoking specific XFS scrub code paths.
- Local exploitation: possible. A local, authenticated attacker (e.g., compromised container or VM tenant) that can trigger scrub or certain B-tree operations could attempt to exercise the bug. Whether an exploit can be reliably developed to gain code execution or privilege escalation depends on the surrounding heap layout and mitigations (KASLR, KPTI, kernel hardening flags) and therefore requires further research.
- Denial-of-service: the most immediate and realistic risk — a kernel panic or oops is the simplest and most likely consequence of hitting the UAF, and an attacker needing only local presence could attempt to cause service disruption. Security teams should treat the UAF as a stability and integrity risk until their kernels are patched. Several vulnerability trackers list EPSS and severity as low-to-medium for public exploitation likelihood, but operational impact remains important.
Vendor and product-space considerations
- Distribution packages: distributions will evaluate the upstream commit and decide whether to backport it or require a kernel update. Ubuntu’s security team and Debian’s tracker already list the CVE; administrators should watch the distribution security advisories for an actionable kernel package.
- Cloud providers: images and custom kernels used by cloud providers may carry the vulnerable code unless the provider has explicitly rolled the upstream patches into their images. Microsoft’s historical approach with Azure Linux (product-scoped attestations) underscores that product attestation is not an exhaustive guarantee for every Microsoft-provided artifact; customers should ensure the kernel image they run contains the fix rather than relying on a single product statement. Our earlier analysis of vendor attestations shows that product-level attestations are helpful but not a substitute for artifact-level inventory.
- Windows-related Linux artifacts (WSL): WSL2 uses a Microsoft-supplied Linux kernel; organizations running WSL at scale — or using Linux images inside Windows-hosted virtualization — should confirm whether the Microsoft-supplied kernel has the upstream fix or if an update has been issued.
Recommended timeline for remediation (practical playbook)
- Day 0 (discovery): Inventory XFS hosts, identify kernels, and block or restrict xfs_scrub access where feasible.
- Day 1: Apply vendor-supplied kernel updates in a staging environment; run smoke tests that include xfs_scrub and high‑metadata activity.
- Day 2–3: Schedule production rollouts with reboots; apply patched kernels and validate via test scrubs and filesystem stress tests.
- Week 1: Audit cloud images, container base images, and images used by automation pipelines (CI, backup/restore images) and update them with patched kernels.
- Ongoing: Subscribe to distribution CVE advisories and upstream kernel stable announcements to catch any related regressions or follow-up fixes.
What defenders should watch for
- Kernel oops messages containing XFS frames — collect and triage them immediately.
- Unexpected reboots or instability on hosts that mount XFS.
- New or unusual uses of xfs_scrub or maintenance pipes in automated jobs — review who can trigger scrubs and why.
- Vendor advisories for this CVE and confirmation that the specific kernel packages in use contain the correct upstream commits. Use the NVD references and distribution trackers to check commit IDs and backport status.
Strengths and weaknesses of the upstream handling
Notable strengths
- The upstream XFS maintainers produced a focused, minimal patch that restores temporal safety without changing semantics, reducing risk of regressions.
- The kernel stable and distribution processes caught the issue, assigned a CVE, and propagated the fix into stable trees and vendor trackers quickly — illustrating a responsive OSS security pipeline. NVD and multiple distribution trackers now reference the fix and the relevant commits.
- Reviewers on the kernel lists validated the patch and documented the root cause clearly, which helps downstream vendors apply correct backports.
Potential risks and weaknesses
- Tests and refactors can easily change ordering guarantees; even small types (like an enum) being removed triggered a safety regression. This underscores the fragility of temporal-order assumptions in kernel code.
- Backport and supply‑chain ambiguity: vendors that backport fixes may alter code during packaging. Administrators cannot assume a package labeled “patched” contains the same fix unless they verify the commit or test behavior.
- Exploitability assessment remains uncertain: while DoS is likely, whether the UAF can be converted into a reliable privilege escalation remains an open, high‑value research question. Treat the issue conservatively until proof limits the risk.
Conclusion
CVE-2026-23223 is a textbook example of how a small refactor or type removal can quietly break a subtle ordering guarantee and open a memory-safety hole in kernel code. The bug lives in XFS’s scrub code and manifested as a use-after-free when the code dereferenced a cursor after related cursors could have been freed. Upstream maintainers produced a small, safe patch that restores the required sampling-before-free behavior; stable kernels have incorporated that change and vendors are rolling updates into their distribution packages. Administrators running XFS should prioritize inventorying affected systems, avoid running xfs_scrub on unpatched kernels where possible, and apply vendor or upstream-backed kernel updates as soon as practical. Because the vulnerability is kernel-space and local in scope, the most immediate operational risk is availability loss through crashes, but memory corruption always warrants a conservative security posture until systems are upgraded and tested.Source: MSRC Security Update Guide - Microsoft Security Response Center