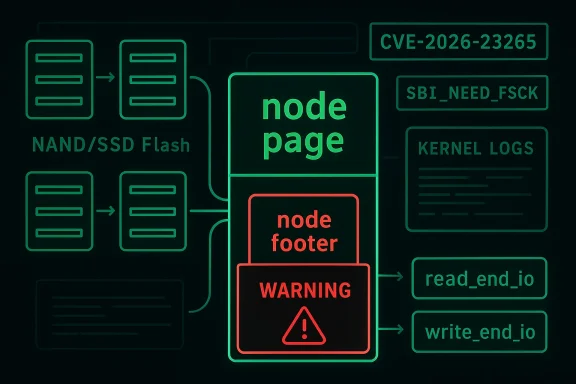
The Linux kernel’s F2FS filesystem is getting a security-relevant hardening fix that closes a gap in how node-page metadata is validated during asynchronous I/O completion. The issue, tracked as CVE-2026-23265, centers on a corrupted node footer slipping through read and write end-io paths, where it could later trigger a kernel bug when the page is written back. The patch adds an explicit sanity check on the node footer in both
F2FS, the Flash-Friendly File System, was designed to better match the behavior of NAND flash, SSDs, eMMC, and SD cards than legacy filesystems optimized around spinning disks. Its log-structured layout, node-based metadata model, and cleaning behavior are intended to reduce write amplification and improve performance on flash media. Over the years, F2FS has also become a feature-rich Linux filesystem with support for fscrypt, fs-verity, compression, and other modern data-path features.
At the core of F2FS is the idea of a node: a structure that represents inodes and pointer blocks, not just plain data pages. That model gives F2FS flexibility, but it also creates a security and integrity burden, because a malformed or corrupted node footer can carry contradictory metadata about where a node belongs and how it should be interpreted. The kernel documentation describes F2FS as relying on node blocks mapped through NAT, which is exactly why footer consistency matters when the filesystem loads or reuses metadata pages.
The patch associated with this CVE was reported through syzbot and discussed on the Linux kernel mailing lists in January 2026, with later stable backport activity continuing into February and March 2026. The bug is not a theoretical paper cut; the report includes an actual kernel BUG trace in
What makes this issue notable is the path by which corrupted metadata reaches the dangerous state. The upstream discussion says that if a node footer is corrupted in a fuzzed image, F2FS may load it via asynchronous read paths such as
The patch description makes the failure mode concrete: a corrupted node page can be loaded asynchronously, bypass the expected sanity check, and only later cause a kernel BUG after writeback. That sequence matters because a filesystem bug is often not dangerous at the moment of read; the danger emerges when internal invariants are violated and later code assumes they still hold. In security terms, the kernel is being forced to trust metadata that has not been validated at every relevant boundary. (spinics.net)
The practical result is that F2FS now checks the footer earlier and in more places. That is a classic kernel-hardening pattern: move validation closer to ingress, so the kernel never has to speculate that “this page should still be valid” later on. It is much better to reject a corrupted node while it is being completed than to let it become part of a dirty writeback path. (spinics.net)
On the write side,
The helper also rate-limits warnings and sets
That is a familiar kernel design tension. Filesystems want to be fast, and validation costs CPU cycles, but metadata paths are also the place where cheap checks save expensive failures. In this case, the bug shows the downside of assuming that “a page already in cache must be fine.” The patch rejects that assumption and makes every completion path participate in integrity checking. (spinics.net)
The broader lesson is that every async completion boundary in a filesystem deserves suspicion. When metadata pages arrive from disk, the kernel should not wait until a later writeback phase to discover that a footer is inconsistent. The new fix effectively says that the read completion path is already late enough to validate the page, and write completion is too late to defer the check any further. (spinics.net)
The new code also introduces a small type enum for node classification. That suggests maintainers wanted a way to express whether the code was dealing with a regular node, inode, xattr node, or non-inode node, which makes the sanity-check logic more precise and future-proof. Precision matters in filesystem code because “close enough” metadata validation is often indistinguishable from no validation at all. (spinics.net)
On the read side, the change is even more important because it closes the gap between asynchronous load and later dirtying of the page. If the footer is already corrupted when the page is brought in, the page should be rejected there and then, rather than being allowed to become a ticking time bomb in memory. This is the practical security value of the patch: it cuts off the bad state at the first realistic opportunity. (spinics.net)
The most important operational consequence is availability. A kernel BUG in a filesystem end-io path can crash a host, panic a VM, or at least force a recovery cycle that disrupts services. For enterprise operators, that makes this defect especially uncomfortable because it sits in the intersection of storage, reliability, and security—three areas where downtime costs money fast. (spinics.net)
The good news is that the fix is relatively straightforward to deploy once it lands in vendor kernels. The less good news is that stable backports can take time to propagate through the ecosystem, and older long-term support trees may need separate attention if they do not apply cleanly. The stable mailing-list failure notice shows exactly that kind of friction: the patch did not apply cleanly to 6.12-stable and needed backport handling.
This CVE also reinforces a broader kernel trend: more validation is being pushed into helper functions and shared paths, rather than left to scattered callers. That pattern reduces the odds of one path drifting out of sync with another, which is especially important in codebases as performance-sensitive and concurrency-heavy as filesystem I/O. The change is small, but it is the kind of change that keeps mature subsystems from accumulating silent assumptions. (spinics.net)
That distinction matters for buyers and architects. Security teams often focus on encryption or authenticity features because they are visible and policy-driven, but low-level metadata integrity bugs can still take down a system long before cryptography gets a chance to help. The lesson is not that F2FS is uniquely risky; it is that feature richness and core safety need to evolve together.
The appearance of the patch in later kernel changelogs and stable-update discussions reinforces that this was treated as a genuine regression or defect worth backporting. The stable pipeline is often the best window into what kernel developers consider urgently worth fixing, and here the answer is obvious: a crash in filesystem metadata handling is not something anyone wants to leave to chance.
The practical takeaway is reassuring: the kernel ecosystem still has a strong pipeline for finding, reproducing, and fixing these problems before they become widely exploitable. But it is also a warning that seemingly small integrity checks can have outsized importance once storage code meets corrupted input. That is where the real risk lives. (spinics.net)
The deeper question is whether this prompts additional cleanup in F2FS’s metadata validation paths. Given the introduction of a shared helper and a more explicit node-type enum, it would not be surprising to see more callers adopt the same function or for related sanity checks to get similar treatment. In mature filesystem code, the best fixes often become templates for the next round of hardening. (spinics.net)
Source: MSRC Security Update Guide - Microsoft Security Response Center
{read,write}_end_io, preventing bad metadata from silently surviving into later stages of the I/O lifecycle. (spinics.net)
 Background
Background
F2FS, the Flash-Friendly File System, was designed to better match the behavior of NAND flash, SSDs, eMMC, and SD cards than legacy filesystems optimized around spinning disks. Its log-structured layout, node-based metadata model, and cleaning behavior are intended to reduce write amplification and improve performance on flash media. Over the years, F2FS has also become a feature-rich Linux filesystem with support for fscrypt, fs-verity, compression, and other modern data-path features.At the core of F2FS is the idea of a node: a structure that represents inodes and pointer blocks, not just plain data pages. That model gives F2FS flexibility, but it also creates a security and integrity burden, because a malformed or corrupted node footer can carry contradictory metadata about where a node belongs and how it should be interpreted. The kernel documentation describes F2FS as relying on node blocks mapped through NAT, which is exactly why footer consistency matters when the filesystem loads or reuses metadata pages.
The patch associated with this CVE was reported through syzbot and discussed on the Linux kernel mailing lists in January 2026, with later stable backport activity continuing into February and March 2026. The bug is not a theoretical paper cut; the report includes an actual kernel BUG trace in
fs/f2fs/data.c, which is the kind of failure that drives maintainers to convert “should never happen” assumptions into explicit runtime checks. (spinics.net)What makes this issue notable is the path by which corrupted metadata reaches the dangerous state. The upstream discussion says that if a node footer is corrupted in a fuzzed image, F2FS may load it via asynchronous read paths such as
f2fs_ra_node_pages() or f2fs_ra_node_page() without immediately checking the footer. If that page later becomes dirty, the corruption is rediscovered only at writeback time, at which point the system can hit a BUG rather than failing more gracefully. (spinics.net)What the Vulnerability Actually Is
The essence of CVE-2026-23265 is a mismatch between where F2FS thinks a node page belongs and what the node footer says inside the page itself. In the reported failure, the node page index (nid) did not match footer.nid, and the old behavior allowed the corrupted object to travel further into the lifecycle than it should have. That mismatch is especially dangerous in a filesystem that treats node pages as structural metadata rather than ordinary cached data. (spinics.net)The patch description makes the failure mode concrete: a corrupted node page can be loaded asynchronously, bypass the expected sanity check, and only later cause a kernel BUG after writeback. That sequence matters because a filesystem bug is often not dangerous at the moment of read; the danger emerges when internal invariants are violated and later code assumes they still hold. In security terms, the kernel is being forced to trust metadata that has not been validated at every relevant boundary. (spinics.net)
Why the Footer Matters
A node footer is not decorative metadata. It is the filesystem’s way of binding the logical identity of a node page to the inode or node hierarchy that owns it, and inconsistencies can indicate corruption, fuzzing artifacts, or maliciously crafted images. The patch’s new helper,f2fs_sanity_check_node_footer(), formalizes that validation and makes it callable from paths that previously relied on weaker assumptions. (spinics.net)The practical result is that F2FS now checks the footer earlier and in more places. That is a classic kernel-hardening pattern: move validation closer to ingress, so the kernel never has to speculate that “this page should still be valid” later on. It is much better to reject a corrupted node while it is being completed than to let it become part of a dirty writeback path. (spinics.net)
- The bug is rooted in metadata inconsistency, not an ordinary data read error.
- The dangerous condition appears when corrupted node pages are loaded asynchronously.
- The defect can remain latent until writeback, where it becomes a BUG.
- The fix shifts validation into both read completion and write completion paths. (spinics.net)
How the Fix Works
The patch touches bothdata.c and node.c, and the design is simple but effective: validate node footers at end-io time and make the check reusable. In f2fs_finish_read_bio(), the code now checks whether the folio is a node folio and whether the footer is sane; if not, it marks the bio status as BLK_STS_IOERR. That converts a hidden metadata problem into a visible I/O failure instead of allowing the corruption to continue. (spinics.net)On the write side,
f2fs_write_end_io() now calls the shared sanity-check helper before continuing with the existing node-index assertion. The important nuance is that the patch does not merely add a second BUG trigger; it adds the metadata validation step before the existing consistency assertion, so the filesystem has a chance to classify and report the failure more accurately. That is a more disciplined failure mode than relying only on a later invariant check. (spinics.net)The New Helper Function
The patch exportsf2fs_sanity_check_node_footer() from node.c and declares it in f2fs.h, making the check available to the I/O completion logic. It also introduces a small enum describing node types for use in __get_node_folio(), which suggests the maintainers wanted a cleaner and more expressive validation interface rather than ad hoc checks sprinkled through the code. In other words, the patch is both a fix and a small refactor toward a more coherent validation model. (spinics.net)The helper also rate-limits warnings and sets
SBI_NEED_FSCK when it detects an inconsistency. That combination is telling: the kernel is not pretending it can self-heal the corruption, but it is trying to fail in a controlled way while signaling that the filesystem likely needs offline repair. This is exactly the kind of behavior administrators want from metadata-integrity code. (spinics.net)read_end_ionow treats a bad footer as an I/O error.write_end_ionow performs explicit footer validation.- The helper centralizes the consistency logic in one reusable function.
- The filesystem marks itself as needing fsck when corruption is found. (spinics.net)
Why Async Paths Are the Problem
The key challenge here is that asynchronous read paths often optimize for performance, not deep validation. F2FS uses readahead-style behavior for node pages, and that means a node can enter memory through a path that is not the same as the one used for a strict inode lookup or a direct metadata fetch. If the validation policy is inconsistent across those paths, corrupted metadata can survive long enough to be acted on later. (spinics.net)That is a familiar kernel design tension. Filesystems want to be fast, and validation costs CPU cycles, but metadata paths are also the place where cheap checks save expensive failures. In this case, the bug shows the downside of assuming that “a page already in cache must be fine.” The patch rejects that assumption and makes every completion path participate in integrity checking. (spinics.net)
The Security Angle
From a security perspective, the vulnerability is a reminder that filesystem parsers are attack surfaces, especially when they process disk images or filesystems exposed to fuzzing, removable media, or guest-controlled storage. A malformed footer that escapes validation is not just an internal bug; it can be the first step toward denial of service or an exploitable state if the kernel later dereferences or asserts against the bad metadata. In this case the public report points to a crash, which is still serious because kernel BUG is an availability failure even when it does not become code execution. (spinics.net)The broader lesson is that every async completion boundary in a filesystem deserves suspicion. When metadata pages arrive from disk, the kernel should not wait until a later writeback phase to discover that a footer is inconsistent. The new fix effectively says that the read completion path is already late enough to validate the page, and write completion is too late to defer the check any further. (spinics.net)
- Async readahead can bypass stricter lookup-time checks.
- Metadata corruption can remain dormant until writeback.
- Failing early reduces the chance of latent kernel BUGs.
- The patch hardens the exact boundary where corruption enters memory. (spinics.net)
What Changed in the Patch
The mailing-list diff shows a fairly compact but meaningful set of changes. The read path now validates node footers inf2fs_finish_read_bio(), the write path validates in f2fs_write_end_io(), and the validation function itself is moved into a form that can be called externally. This is one of those patches where the line count is modest but the semantic value is high, because it adjusts the filesystem’s trust model rather than just patching a symptom. (spinics.net)The new code also introduces a small type enum for node classification. That suggests maintainers wanted a way to express whether the code was dealing with a regular node, inode, xattr node, or non-inode node, which makes the sanity-check logic more precise and future-proof. Precision matters in filesystem code because “close enough” metadata validation is often indistinguishable from no validation at all. (spinics.net)
Before and After
Before the patch,write_end_io() mainly relied on f2fs_bug_on() to catch a mismatch between the folio index and the node identity. After the patch, the filesystem first performs an explicit sanity check on the node footer, then continues with the existing assertion. That order gives the code a chance to record a meaningful footer inconsistency instead of only reacting to the downstream symptom. (spinics.net)On the read side, the change is even more important because it closes the gap between asynchronous load and later dirtying of the page. If the footer is already corrupted when the page is brought in, the page should be rejected there and then, rather than being allowed to become a ticking time bomb in memory. This is the practical security value of the patch: it cuts off the bad state at the first realistic opportunity. (spinics.net)
- A corrupted node page is loaded asynchronously.
- The new read-side check detects the footer mismatch.
- The page is marked with an I/O error instead of being trusted.
- The write-side path now revalidates before proceeding. (spinics.net)
Impact on Enterprise Systems
For enterprises, the immediate concern is not that every F2FS system is in danger today, but that storage integrity bugs often sit unnoticed until an unusual image, malformed device, or test workload triggers them. Linux distributions, container hosts, Android-derived platforms, embedded devices, and storage appliances using F2FS all inherit the same code path once they ship a vulnerable kernel. That means the blast radius depends less on “who uses F2FS” and more on who consumes kernels before the fix lands.The most important operational consequence is availability. A kernel BUG in a filesystem end-io path can crash a host, panic a VM, or at least force a recovery cycle that disrupts services. For enterprise operators, that makes this defect especially uncomfortable because it sits in the intersection of storage, reliability, and security—three areas where downtime costs money fast. (spinics.net)
Consumer and Embedded Considerations
On consumer devices and embedded systems, the issue may show up differently. Phones, IoT appliances, kiosks, and flash-based edge devices are often more likely to use F2FS precisely because it suits flash storage well. If those devices ingest untrusted images, perform OTA updates, or rely on unusual mount and recovery workflows, the risk of triggering a latent metadata bug becomes more than academic.The good news is that the fix is relatively straightforward to deploy once it lands in vendor kernels. The less good news is that stable backports can take time to propagate through the ecosystem, and older long-term support trees may need separate attention if they do not apply cleanly. The stable mailing-list failure notice shows exactly that kind of friction: the patch did not apply cleanly to 6.12-stable and needed backport handling.
- Enterprise impact is primarily availability and crash risk.
- Consumer and embedded impact depends on flash-heavy deployments.
- Backporting can be uneven across stable and long-term trees.
- The fix is low-complexity but may still require vendor integration work.
Competitive and Ecosystem Implications
Filesystem bugs like this do not exist in isolation; they affect how vendors and downstream distributions view F2FS relative to ext4, btrfs, and other storage options. F2FS has a reputation for flash-specific efficiency, but every security or reliability bug reminds operators that niche filesystem advantages must be balanced against operational maturity. In competitive terms, the stronger the safety story, the easier it is for F2FS to remain attractive in shipping products.This CVE also reinforces a broader kernel trend: more validation is being pushed into helper functions and shared paths, rather than left to scattered callers. That pattern reduces the odds of one path drifting out of sync with another, which is especially important in codebases as performance-sensitive and concurrency-heavy as filesystem I/O. The change is small, but it is the kind of change that keeps mature subsystems from accumulating silent assumptions. (spinics.net)
Relationship to fs-verity and fscrypt
F2FS already supports modern security and integrity features such as fs-verity and fscrypt, which makes this CVE feel particularly important. Those features help protect file contents and confidentiality, but they do not eliminate the need for robust metadata validation in the filesystem’s core code. A filesystem can be excellent at cryptography and still be vulnerable if its node-management layer trusts malformed on-disk structures too much.That distinction matters for buyers and architects. Security teams often focus on encryption or authenticity features because they are visible and policy-driven, but low-level metadata integrity bugs can still take down a system long before cryptography gets a chance to help. The lesson is not that F2FS is uniquely risky; it is that feature richness and core safety need to evolve together.
- F2FS remains attractive for flash-oriented workloads.
- Integrity features like fs-verity do not replace metadata validation.
- The patch improves F2FS’s trust model at a core boundary.
- Downstream vendors will likely treat this as a routine but important backport.
Signs That the Kernel Maintainers Took It Seriously
The patch was not just posted as a speculative cleanup; it carried aCc: stable@ tag, a syzbot report, and a clear crash trace. That combination usually means maintainers saw a real reproducible failure path, not merely a theoretical possibility. It also explains why the issue moved quickly from mailing-list discussion into stable follow-up. (spinics.net)The appearance of the patch in later kernel changelogs and stable-update discussions reinforces that this was treated as a genuine regression or defect worth backporting. The stable pipeline is often the best window into what kernel developers consider urgently worth fixing, and here the answer is obvious: a crash in filesystem metadata handling is not something anyone wants to leave to chance.
Why Syzbot Matters
Syzbot has become one of the most valuable sources of kernel hardening issues because it finds edge cases humans rarely hit in normal testing. In this case, a fuzzed image exposed a code path where the filesystem trusted a node footer for too long. That is a textbook example of why coverage from synthetic workloads is critical in kernel development, especially for filesystems that have to parse persistent state from potentially adversarial storage. (spinics.net)The practical takeaway is reassuring: the kernel ecosystem still has a strong pipeline for finding, reproducing, and fixing these problems before they become widely exploitable. But it is also a warning that seemingly small integrity checks can have outsized importance once storage code meets corrupted input. That is where the real risk lives. (spinics.net)
- The issue was reproducible, not merely theoretical.
- It was reported through syzbot, which specializes in edge-case kernel bugs.
- Stable maintainers treated it as a backportable fix.
- The patch aligns with standard Linux kernel security handling. (spinics.net)
Strengths and Opportunities
The fix improves F2FS in a way that is unusually efficient: it adds validation where the system already has the data in hand, instead of introducing a whole new machinery layer. That keeps the performance impact constrained while meaningfully improving resilience. It also gives downstream distributors a clear, well-scoped patch to carry into supported kernels. (spinics.net)- Earlier corruption detection in both read and write completion paths.
- Better failure semantics by turning latent corruption into an I/O error.
- Reusable helper logic that reduces duplication.
- Stronger fsck signaling via
SBI_NEED_FSCK. - Cleaner maintenance for future node-type handling.
- Low implementation complexity, which helps stable backports.
- Improved confidence in F2FS metadata integrity for vendors. (spinics.net)
Risks and Concerns
Even a solid fix does not erase the fact that corrupted node pages can still be introduced by bad media, malformed disk images, or fuzzing-driven inputs. That means administrators should treat this as part of a broader reliability conversation, not as a one-off bug. The presence of a fix lowers risk, but it does not remove the need for careful patch management and filesystem health monitoring. (spinics.net)- Crash risk remains on unpatched kernels.
- Backport delays can leave long-term systems exposed.
- Dirty-page propagation means corruption can survive briefly in memory.
- Malformed images remain an attack and test vector.
- Operational downtime is a real consequence if the kernel BUG is triggered.
- Vendor kernel divergence can slow consistent remediation.
- Overconfidence in async paths may lead to similar bugs elsewhere. (spinics.net)
Looking Ahead
The most likely next step is routine: vendors will fold the patch into their kernel streams, stable trees will absorb backports where needed, and F2FS users will get a small but meaningful hardening improvement in standard updates. If the disclosure and CVE mapping continue to track the mailing-list fix, the issue should become another example of the Linux community’s fast-moving security response rather than a lingering emergency. (spinics.net)The deeper question is whether this prompts additional cleanup in F2FS’s metadata validation paths. Given the introduction of a shared helper and a more explicit node-type enum, it would not be surprising to see more callers adopt the same function or for related sanity checks to get similar treatment. In mature filesystem code, the best fixes often become templates for the next round of hardening. (spinics.net)
What to Watch
- Whether the patch lands in all supported stable branches without further churn.
- Whether downstream vendors ship fast security advisories for F2FS users.
- Whether related node-footer checks are extended to more call sites.
- Whether additional syzbot reports surface nearby edge cases.
- Whether filesystem maintainers use this pattern for other metadata invariants.
Source: MSRC Security Update Guide - Microsoft Security Response Center