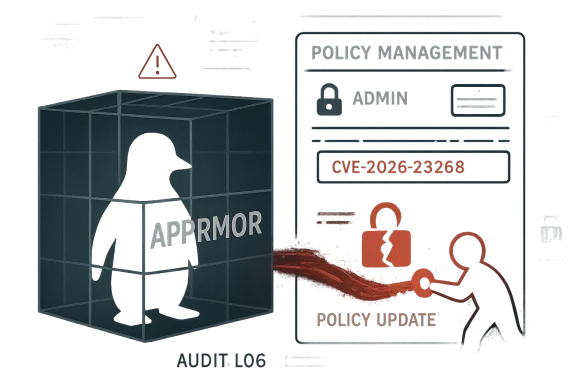
AppArmor is back in the spotlight, and this time the concern is not a subtle policy quirk but a path that reportedly lets an unprivileged local user reach privileged policy management. The issue behind CVE-2026-23268 matters because AppArmor sits at the heart of Linux containment for desktops, servers, and containers, meaning a weakness in its policy plumbing can ripple far beyond a single package. Microsoft’s update guide page for the CVE now returns “not found,” but the wording of the advisory title itself is enough to signal a potentially serious administrative boundary problem in one of Linux’s most widely deployed security modules.
AppArmor is one of the two major mainstream Linux mandatory access control systems, alongside SELinux. In practice, it is valued because it can be easier to deploy, easier to reason about, and easier to adopt in mixed enterprise environments where administrators want strong confinement without redesigning every workflow. It is also deeply embedded in distributions such as Ubuntu, and it has become part of the default security posture for many cloud images, developer workstations, and container hosts. That makes any flaw in its policy management layer especially important, because policy management is the mechanism that defines what is allowed in the first place.
The CVE title is telling: “fix unprivileged local user can do privileged policy management” implies the problem is not merely that a confinement rule is too permissive, but that a non-admin user may be able to interact with a privileged control path. That is a classic and dangerous pattern in security software. Once an attacker can influence policy state, they may be able to reduce confinement, create a new escape route, or shape the system into a condition that undermines future access control checks.
That distinction matters in a kernel-adjacent subsystem like AppArmor. AppArmor profiles are loaded from user space, but enforcement occurs in the kernel. When the interface between those two worlds is fragile, the result can be a policy layer that is conceptually strong but operationally brittle. In other words, the danger is not just “can the attacker run as root right now?” but “can the attacker manipulate the system so the root boundary no longer means what it should?”
There is also a broader industry context. Linux distributions have spent the last several years tightening user namespace behavior, container confinement, and AppArmor-related controls because attackers increasingly chain low-privilege local access with confinement gaps to reach higher-value targets. Microsoft, in particular, has been publishing Linux security guidance more often because Azure, AKS, and other hybrid environments routinely mix Windows management surfaces with Linux workloads. A flaw that looks like an AppArmor issue can therefore become a cloud workload issue, a desktop hardening issue, and a platform governance issue all at once.
The missing Microsoft page does not tell the whole story by itself, so the safest reading is cautious. The CVE title indicates a privilege boundary problem in AppArmor policy management, and the surrounding ecosystem tells us why that would be serious. Even without the now-missing page, the security implications are clear enough to warrant attention from administrators who rely on AppArmor for least-privilege enforcement.
The most important practical point is that AppArmor is not just for “hardening.” It is also for containment, which means it protects against both accidental misuse and adversarial behavior. If that containment is weakened, every service relying on AppArmor becomes more exposed to lateral movement and privilege escalation. That is why policy-management flaws are often more severe than a simple denial-of-service bug.
That is why the phrasing “privileged policy management” raises alarm bells. Policy changes are supposed to be controlled by administrators or trusted service processes, not by ordinary users. When that assumption fails, the attacker is no longer asking permission from the security layer—they may be changing the rules of the game.
This is especially relevant on Linux systems that host multiple tenants, containers, or interactive development workloads. A local user who can manipulate AppArmor policy may be able to widen access for other processes, reduce isolation between workloads, or enable persistence that survives ordinary account resets. In enterprise security terms, that changes an incident from a user-session problem into a host-integrity problem.
That missing page also highlights a recurring challenge in vulnerability communication. A CVE identifier by itself is not enough for operations teams. They need affected versions, exploitability context, fix availability, and whether the issue is local-only or remotely reachable. If one of those details is missing, teams must make decisions under uncertainty, which is exactly what security advisories are supposed to reduce.
The container angle is particularly important because container security frequently relies on defense in depth. AppArmor is one layer, user namespaces are another, seccomp is another, and capabilities reduce what a process can do even if it escapes its intended workflow. If an attacker can tamper with one layer’s policy management, the effectiveness of the others can be reduced or nullified in practice.
What makes the current CVE noteworthy is that it appears to fit a pattern we have seen before: the policy layer is trusted too much, or in the wrong way, at the wrong boundary. That is a subtle but serious class of problem because the attack does not always look like a classic exploit. Sometimes it looks like a normal management operation performed by the wrong actor.
The worst-case outcome is not simply a mistaken policy update. It is a host where the security boundary is no longer enforced according to administrator intent. In practical terms, that can translate into unauthorized access to files, processes, namespaces, or management paths that were assumed to be locked down.
For enterprises, the issue is more urgent and more expensive. Managed Linux fleets often include workloads where local users, service accounts, or developer accounts have enough access to matter. A policy-management flaw can disrupt compliance assumptions, incident response workflows, and endpoint hardening baselines at the same time.
It is also worth validating monitoring and configuration management. If your environment tracks AppArmor profiles, policy reloads, and securityfs or related management events, confirm that those logs are being retained and alertable. The goal is to catch unexpected policy edits before they become a durable compromise.
The second question is whether this CVE becomes part of a larger pattern. AppArmor has already been the subject of renewed scrutiny across Linux distributions because of containerization, user namespaces, and local privilege boundaries. If more issues surface in the same area, organizations may need to revisit whether their current hardening strategy is sufficient or whether additional confinement layers are necessary.
AppArmor remains a valuable part of the Linux security stack, but its value depends on the integrity of the systems that administer it. If unprivileged users can reach privileged policy management, the entire confinement model becomes less trustworthy, and that is exactly the sort of flaw that deserves immediate attention from anyone responsible for hardened Linux environments.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Overview
Overview
AppArmor is one of the two major mainstream Linux mandatory access control systems, alongside SELinux. In practice, it is valued because it can be easier to deploy, easier to reason about, and easier to adopt in mixed enterprise environments where administrators want strong confinement without redesigning every workflow. It is also deeply embedded in distributions such as Ubuntu, and it has become part of the default security posture for many cloud images, developer workstations, and container hosts. That makes any flaw in its policy management layer especially important, because policy management is the mechanism that defines what is allowed in the first place.The CVE title is telling: “fix unprivileged local user can do privileged policy management” implies the problem is not merely that a confinement rule is too permissive, but that a non-admin user may be able to interact with a privileged control path. That is a classic and dangerous pattern in security software. Once an attacker can influence policy state, they may be able to reduce confinement, create a new escape route, or shape the system into a condition that undermines future access control checks.
That distinction matters in a kernel-adjacent subsystem like AppArmor. AppArmor profiles are loaded from user space, but enforcement occurs in the kernel. When the interface between those two worlds is fragile, the result can be a policy layer that is conceptually strong but operationally brittle. In other words, the danger is not just “can the attacker run as root right now?” but “can the attacker manipulate the system so the root boundary no longer means what it should?”
There is also a broader industry context. Linux distributions have spent the last several years tightening user namespace behavior, container confinement, and AppArmor-related controls because attackers increasingly chain low-privilege local access with confinement gaps to reach higher-value targets. Microsoft, in particular, has been publishing Linux security guidance more often because Azure, AKS, and other hybrid environments routinely mix Windows management surfaces with Linux workloads. A flaw that looks like an AppArmor issue can therefore become a cloud workload issue, a desktop hardening issue, and a platform governance issue all at once.
The missing Microsoft page does not tell the whole story by itself, so the safest reading is cautious. The CVE title indicates a privilege boundary problem in AppArmor policy management, and the surrounding ecosystem tells us why that would be serious. Even without the now-missing page, the security implications are clear enough to warrant attention from administrators who rely on AppArmor for least-privilege enforcement.
What AppArmor Actually Protects
AppArmor is often described as a profile-based access control system, but that shorthand undersells its role. It does not simply block a few system calls; it defines a policy relationship between processes, file paths, capabilities, and in some cases other kernel-mediated resources. Because those rules are loaded from user space and enforced in kernel space, the policy lifecycle becomes a critical security boundary in its own right.The most important practical point is that AppArmor is not just for “hardening.” It is also for containment, which means it protects against both accidental misuse and adversarial behavior. If that containment is weakened, every service relying on AppArmor becomes more exposed to lateral movement and privilege escalation. That is why policy-management flaws are often more severe than a simple denial-of-service bug.
Policy Is the Product
A security module is only as strong as its policy pipeline. If an attacker can alter the pipeline, they may not need to bypass the enforcement engine at all. Instead, they can potentially change what the engine considers acceptable, which is often a more powerful position than overriding a single check.That is why the phrasing “privileged policy management” raises alarm bells. Policy changes are supposed to be controlled by administrators or trusted service processes, not by ordinary users. When that assumption fails, the attacker is no longer asking permission from the security layer—they may be changing the rules of the game.
- AppArmor depends on trusted policy loading and updates.
- Administrative interfaces are part of the attack surface.
- Containment failures can outlive the initial exploit.
- Policy abuse can be more dangerous than a single bypass.
- A local weakness can become a systemic weakness quickly.
Why Local Privilege Boundaries Still Matter
A common mistake in vulnerability triage is to discount local attacks because they appear to require prior access. That is a dangerous assumption. In real enterprise environments, the “unprivileged local user” may be a compromised developer account, a CI runner, a container breakout foothold, or a remote code execution foothold that has already been downgraded by sandboxing. Once that starting point exists, local privilege escalation becomes the most direct route to full compromise.This is especially relevant on Linux systems that host multiple tenants, containers, or interactive development workloads. A local user who can manipulate AppArmor policy may be able to widen access for other processes, reduce isolation between workloads, or enable persistence that survives ordinary account resets. In enterprise security terms, that changes an incident from a user-session problem into a host-integrity problem.
From User Shell to Control Plane
The most serious local escalation bugs are the ones that let an attacker pivot from a limited shell into a control plane that was supposed to be restricted. Policy management belongs in that category because it governs the behavior of security-critical services. If the attacker can touch that surface, the host may be compromised in ways that are hard to reverse cleanly.- Local access is often only the first step in a real attack chain.
- Container hosts are especially sensitive to policy drift.
- Persistent policy changes can survive process restarts.
- A small mistake in trust boundaries can have broad consequences.
- “Unprivileged” does not mean “low risk.”
The Significance of the Missing MSRC Page
Microsoft’s MSRC update guide is usually a useful signal when Linux CVEs appear there, even if Microsoft is not the maintainer of the affected software. In hybrid environments, MSRC often tracks cross-platform vulnerabilities because customers care about the security of Linux workloads on Microsoft-managed infrastructure and tooling. When the page becomes unavailable, that does not erase the issue; it merely deprives operators of the summary they expected to use for triage.That missing page also highlights a recurring challenge in vulnerability communication. A CVE identifier by itself is not enough for operations teams. They need affected versions, exploitability context, fix availability, and whether the issue is local-only or remotely reachable. If one of those details is missing, teams must make decisions under uncertainty, which is exactly what security advisories are supposed to reduce.
What the Title Suggests
The phrase “fix unprivileged local user can do privileged policy management” suggests the flaw may involve authorization boundaries rather than memory corruption. That matters because authorization bugs are often easier to exploit reliably than exploit-development-class bugs. They can also be harder for defenders to spot because the behavior may look like legitimate management traffic unless carefully audited.- The flaw appears to involve authorization, not just parsing.
- The likely blast radius is policy integrity.
- Operational teams need version and package guidance.
- Hybrid environments depend on clear advisory language.
- Missing advisory content increases response friction.
AppArmor, Containers, and the Modern Attack Surface
AppArmor is no longer just a desktop hardening feature. It has become part of the modern Linux platform story, especially in containers and cloud workloads where administrators need layered isolation. That means flaws in AppArmor do not stay neatly on a single machine; they can affect developer laptops, build systems, CI/CD runners, and Kubernetes nodes.The container angle is particularly important because container security frequently relies on defense in depth. AppArmor is one layer, user namespaces are another, seccomp is another, and capabilities reduce what a process can do even if it escapes its intended workflow. If an attacker can tamper with one layer’s policy management, the effectiveness of the others can be reduced or nullified in practice.
Why This Becomes an Enterprise Issue
Enterprises often assume that container isolation plus standard Linux permissions is enough. That assumption is only valid when the surrounding kernel enforcement tools are trustworthy and correctly configured. If policy management can be manipulated, a hostile local user may be able to undermine a carefully designed controls stack without touching the underlying application code.- Containers amplify the importance of host-level policy integrity.
- CI systems often run with broad filesystem and policy access.
- Security drift in one node can spread operationally.
- AppArmor is frequently treated as a default trust anchor.
- A policy flaw can weaken multiple workloads at once.
How This Fits the History of AppArmor Bugs
AppArmor has a long track record of both value and vulnerability. Its utility as an approachable security module has made it attractive to distributions that want strong defaults, but that same complexity has produced recurring issues over the years. Historically, AppArmor bugs have ranged from profile miscompilation to confinement loss to unexpected behavior around restarts and policy transitions.What makes the current CVE noteworthy is that it appears to fit a pattern we have seen before: the policy layer is trusted too much, or in the wrong way, at the wrong boundary. That is a subtle but serious class of problem because the attack does not always look like a classic exploit. Sometimes it looks like a normal management operation performed by the wrong actor.
Recurring Themes in MAC Failures
Mandatory access control systems are powerful precisely because they are centralized. But centralization also means that if the management plane falters, the security model can fail broadly. That is why AppArmor bugs are often treated with more weight than ordinary application bugs, even when the immediate symptom seems narrow.- Policy loading is an attractive target.
- Administrative interfaces need strong authentication and authorization.
- Restart and upgrade paths can introduce regressions.
- Kernel-user-space boundaries are easy to mishandle.
- Security modules must be tested under real-world management flows.
The Likely Security Impact
Even without the full bulletin text, the security consequences are not hard to infer. If an unprivileged local user can perform privileged policy management, they may be able to add, modify, or trigger policy changes that should have required elevated authority. Depending on the exact code path, that could allow them to weaken confinement for specific applications, influence the behavior of security services, or set up a later privilege escalation.The worst-case outcome is not simply a mistaken policy update. It is a host where the security boundary is no longer enforced according to administrator intent. In practical terms, that can translate into unauthorized access to files, processes, namespaces, or management paths that were assumed to be locked down.
What Defenders Should Assume
Until vendors publish full remediation details, defenders should assume that the issue is more serious than a benign misconfiguration. Local privilege escalation bugs in security subsystems usually deserve urgent treatment because they can combine with other footholds. The attacker does not need to own the network if they can own the node.- Treat policy-management flaws as privilege escalation candidates.
- Review systems where untrusted users have shell access.
- Prioritize hosts that run containers or multi-tenant workloads.
- Watch for unexpected AppArmor policy changes.
- Assume chained exploitation is possible.
Enterprise vs Consumer Exposure
For consumers, AppArmor is mostly invisible. It quietly protects browsers, desktop applications, and system services, often without much user awareness. That means a flaw in policy management is unlikely to be noticed by the average home user until there is a real incident, because there may be no obvious sign that the system’s confinement model has been altered.For enterprises, the issue is more urgent and more expensive. Managed Linux fleets often include workloads where local users, service accounts, or developer accounts have enough access to matter. A policy-management flaw can disrupt compliance assumptions, incident response workflows, and endpoint hardening baselines at the same time.
Different Risk Profiles
The consumer threat is usually a single-device compromise, while the enterprise threat is systemic trust erosion. On a business fleet, one compromised node can become a staging point for lateral movement, credential theft, or persistence in tooling that administrators believe is protected. That is why the same CVE can look modest on paper and severe in operations.- Consumers face stealthier, less visible risk.
- Enterprises face fleet-wide governance problems.
- Shared infrastructure increases the value of escalation.
- Developer workstations are often the weakest link.
- Compliance controls can be undermined by policy drift.
What Administrators Should Do Now
Until the final vendor guidance is published or rediscovered through alternate channels, administrators should treat this as a high-priority review item. The first step is to identify which systems rely on AppArmor, which distributions are in use, and whether there are any local users or service accounts that interact with policy tooling. The second step is to check vendor advisories and package repositories for patched builds as soon as they become available.It is also worth validating monitoring and configuration management. If your environment tracks AppArmor profiles, policy reloads, and securityfs or related management events, confirm that those logs are being retained and alertable. The goal is to catch unexpected policy edits before they become a durable compromise.
Practical Response Checklist
A disciplined response is better than a frantic one. Security teams should focus first on exposure, then on containment, then on remediation. That sequence helps avoid the common mistake of patching one node while leaving the underlying trust issue unexamined.- Inventory systems using AppArmor.
- Identify users and services with policy-management access.
- Review recent changes to profiles and enforcement settings.
- Check for vendor patches and distribution advisories.
- Harden logging around policy reloads and admin actions.
- Reassess local-user privileges on shared systems.
Strengths and Opportunities
The upside of a flaw like this, if there is one, is that it forces organizations to re-examine how much trust they place in local management paths. That can lead to better logging, tighter privilege assignment, and more careful separation of duties. It also provides a reminder that security modules need the same operational scrutiny as the applications they protect.- Better auditing of AppArmor policy changes.
- Stronger separation between users and policy admins.
- Improved hardening for container hosts.
- More disciplined patch management across Linux fleets.
- Greater awareness of local escalation paths.
- A chance to review hybrid Windows/Linux governance.
Risks and Concerns
The main risk is that this issue may be underestimated because it sounds local and administrative. That would be a mistake. Security control bugs often hide in plain sight, and attackers love mechanisms that defenders assume are “just management plumbing.”- The flaw may be chainable with other local exploits.
- Policy manipulation could persist after reboot.
- Logging may be insufficient to detect abuse.
- Hybrid environments may miss Linux-specific guidance.
- Container hosts may suffer disproportionate impact.
- Confusion from missing advisory content can delay response.
- Organizations may assume default settings are still safe.
Looking Ahead
The immediate question is whether distributions and upstream maintainers issue a clear, coordinated fix path. That will determine whether the bug is primarily a patch-management problem or a broader hardening issue. If the flaw is easily reachable by ordinary users, administrators should expect a rapid round of updates and possibly accompanying mitigation advice.The second question is whether this CVE becomes part of a larger pattern. AppArmor has already been the subject of renewed scrutiny across Linux distributions because of containerization, user namespaces, and local privilege boundaries. If more issues surface in the same area, organizations may need to revisit whether their current hardening strategy is sufficient or whether additional confinement layers are necessary.
What to Watch
- Vendor patches and backported fixes.
- Distribution advisories for Ubuntu, Debian, SUSE, and related platforms.
- Any clarification on exact affected AppArmor versions.
- Evidence of active exploitation in the wild.
- Guidance for container hosts and developer workstations.
AppArmor remains a valuable part of the Linux security stack, but its value depends on the integrity of the systems that administer it. If unprivileged users can reach privileged policy management, the entire confinement model becomes less trustworthy, and that is exactly the sort of flaw that deserves immediate attention from anyone responsible for hardened Linux environments.
Source: MSRC Security Update Guide - Microsoft Security Response Center