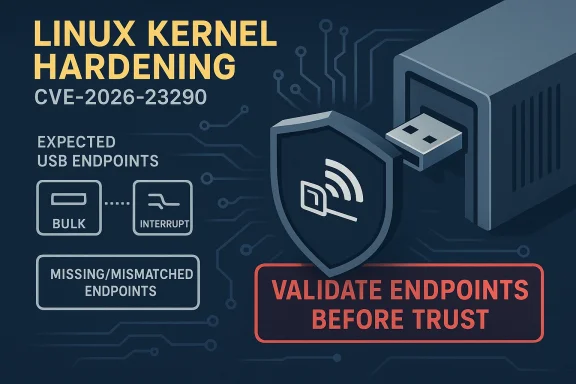
CVE-2026-23290 is a reminder that kernel security problems do not always arrive as dramatic memory-corruption headlines. In this case, the Linux pegasus USB network driver is being hardened so it checks that a connected device exposes the USB endpoints the driver expects before binding to it, because a malicious or malformed device could otherwise trigger a later crash when the driver blindly uses those endpoints. The vulnerability was received from kernel.org and published in NVD on March 25, 2026, but NVD had not yet assigned a severity score at the time of publication. re issue is straightforward but important: the pegasus driver assumed that a device it was probing would present a normal endpoint layout, and that assumption was not safe. According to the CVE description, the fix validates both the number and types of USB endpoints before the driver binds, closing a path where a hostile device could steer the driver into dereferencing endpoint structures that are not there. That is the kind of bug that often looks small in code review but can have outsized impact once the kernel is exposed to untrusted hardware.
USB is a protocol tescriptor parsing and punishes shortcuts. Linux documentation makes clear that endpoints are fundamental to USB device communication, and host-side drivers depend on them for transfers through URBs and endpoint-specific semantics. The kernel’s own USB documentation also shows why malformed or missing endpoint data is dangerous: drivers are expected to match their transfer logic to the hardware’s endpoint capabilities, not merely assume that any plugged-in device looks like the expected one.
The broader security pattern here is familiar to anyone who has watched USB bugs evolve over the years. Many device drivers are written with well-formed hardware in mind, but attackers and fuzzers routinely demonstrate that “well-formed” is a policy, not a guarantee. Linux’s own Raw Gadget documentation explicitly notes that malformed USB data is useful for fuzzing, and that sanity checks around descriptors exist for a reason. CVE-2026-23290 fits neatly into that class of “validate the device before trusting it” kernel fixes.
This is also not the first time the pegasus driver has needed security-sensitive attention. Historical kernel advisories have tied pegasus to crashes and memory corruption issues under specific conditions, showing that its code path has long been one of those older USB network implementations where assumptions and edge cases matter. The difference this time is that the reported flaw centers on endpoint validation, not scatter/gather mishandling or later-stage transfer logic. That distinction matters because it changes where the safe boundary belongs: at probe time, not after the device has already been trusted.
Probe-time checks are a first line of defense. Once a driver binds to a USB device, it often allocates resources, registers network interfaces, and prepares URBs based on a model of the hardware that may already be wrong.
If that model is wrong, the failure can appear much later and in a very different part of the code, which makes diagnosis harder and increases the chance of a crash.
The Linux USB subsystem itself is designed around endpoint-driven communication, where a device advertises a set of descriptors and the driver decides how to use them. In principle, that is elegant. In practice, it means drivers must be strict about what they accept, because the kernel is often the first and most trusted consumer of those descriptors. If the driver’s probe path is permissive, the USB device effectively dictates the driver’s later behavior.
That is why the specific wording in the CVE is so telling. The issue is not merely “the driver crashes” but that it crashes after binding to a device whose endpoint layout does s. The bug therefore sits at the intersection of discovery logic and runtime safety: the driver should reject the device early, before any later URB handling can reach undefined state.
Modern USB host-side code increasingly treats malformed descriptors as an expected threat model, not an anomaly. Kernel documentation for USB fuzzing and raw gadget support makes it clear that intentionally malformed data is part of the test universe, and that endpoint assumptions are exactly the sort of thing fuzzers try to break. This CVE strongly suggests that the pegasus path had not yet absorbed that lesson thoroughly enough.
From an enterprise perspective, the issue also illustrates a subtle but important operational truth: hardware bugs are security bugs when they can be triggered by a malicious peripheral. That includes lab equipment, dropped-in adapters, counterfeit devices, and anything with USB access in an environment where users or attackers can physically connect hardware. In other words, the attack surface is not abstract; it lives at the desk, in the rack, and on the bench.
A driver that handles “normal” devices correctly can still be fragile when the hardware lies, omits descriptors, or advertises an impossible combination of endpoints.
The CVE text suggests the failure mode is a crash rather than a more elaborate exploit chain. That does not make it harmless. In kernel enial of service, and if the bug can be triggered by a deliberately malformed device, the attacker does not need kernel privileges to create the condition. They need hardware access, a malicious peripheral, or a controlled testing environment.
The kernel’s USB API documentation makes this clear by emphasizing endpoint capabilities and the role they play in matching driver behavior to device hardware. That is why endpoint validation belongs at the beginning of the binding process. It is the point where the driver still has a chance to say “no” before any operational state has been built on bad assumptions.
That matters because many Windows-focused organizationdows estates anymore. They manage Linux guests, appliances, containers, lab machines, and mixed infrastructure where a kernel bug in one ecosystem still affects the same security team, the same asset inventory, and the same remediation calendar. The practical result is that a Linux USB driver bug can show up in the same triage queue as a Windows patch item.
That means a CVE does not need to be “Windows” to matter to a Windows-first organization, and it does not need a flashy exploit chain to create work.
The pegasus driver itself has seen prior security-adjacent fixes over the years, which reinforces the idea that older USB networking code is not automatically bad, but it often needs defensive maintenance. The presence of a historical pegasus CVE tied to crashes and memory corruption underlines how this driver family has long required careful handling. That history does not prove a broader systemic failure, but it does show a pattern that maintainers clearly take seriously.
That mismatch between original design and modern threat model is where many kernel bugs live.
The goal is to reduce trust, not introduce a new compatibility headache.
What makes this class of bug persist is that USB device enumeration is highly contextual. A driver may work perfectly with intended hardware yet fail badly with a counterfeit, damaged, or maliciously constructed device. Linux’s USB infrastructure is intentionally flexible, which is great for compatibility but bad for assumptions. Security hardening therefore becomes an ongoing process of narrowing trust boundaries one driver at a time.
If a local device or malicious peripheral can reliably crash the kernel, the issue still matters for availability, resilience, and physical attack paths.
This is where defenders should resist the temptation to rank only by headline severity. Many of the most disruptive incidents begin as simple-looking validation failures that let the system trust something it should have rejected. That is what makes endpoint validation such a valuable defensive practice in the kernel.
It is also worth watching whether this issue triggers follow-on audits in related USB networking drivers. Historically, once one driver is found to have relied too heavily on descriptor assumptions, maintainers often review neighboring code for the same pattern. That kind of preventative work is not glamorous, but it is how the kernel slowly becomes harder to trick with malformed hardware.
CVE-2026-23290 is ultimately about strengthening the kernel’s habit of distrust. That is a healthy direction for USB code, and one that should make life better for both maintainers and defenders. The fix does not just patch one driver; it reinforces an important security principle: if the hardware can lie, the kernel must verify before it believes.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
USB is a protocol tescriptor parsing and punishes shortcuts. Linux documentation makes clear that endpoints are fundamental to USB device communication, and host-side drivers depend on them for transfers through URBs and endpoint-specific semantics. The kernel’s own USB documentation also shows why malformed or missing endpoint data is dangerous: drivers are expected to match their transfer logic to the hardware’s endpoint capabilities, not merely assume that any plugged-in device looks like the expected one.
The broader security pattern here is familiar to anyone who has watched USB bugs evolve over the years. Many device drivers are written with well-formed hardware in mind, but attackers and fuzzers routinely demonstrate that “well-formed” is a policy, not a guarantee. Linux’s own Raw Gadget documentation explicitly notes that malformed USB data is useful for fuzzing, and that sanity checks around descriptors exist for a reason. CVE-2026-23290 fits neatly into that class of “validate the device before trusting it” kernel fixes.
This is also not the first time the pegasus driver has needed security-sensitive attention. Historical kernel advisories have tied pegasus to crashes and memory corruption issues under specific conditions, showing that its code path has long been one of those older USB network implementations where assumptions and edge cases matter. The difference this time is that the reported flaw centers on endpoint validation, not scatter/gather mishandling or later-stage transfer logic. That distinction matters because it changes where the safe boundary belongs: at probe time, not after the device has already been trusted.
 Why probe-time validation matters
Why probe-time validation matters
Probe-time checks are a first line of defense. Once a driver binds to a USB device, it often allocates resources, registers network interfaces, and prepares URBs based on a model of the hardware that may already be wrong.If that model is wrong, the failure can appear much later and in a very different part of the code, which makes diagnosis harder and increases the chance of a crash.
- The driver may dereference an endpoint pointer that was never valid.
- Transfer setup may succeed on paper but fail when traffic starts.
- The bug may appear only with malicious or defective hardware.
- Faults can propagate into unrelated networking or USB core paths.
Background
The Pegasus family of USB-to-Ethernet chips has been around for a long time, which is part of the reason this story matters. Long-lived drivers tend to accumulate assumptions about what hardware will look like, especially when their original target devices were simple, predictable, and manufactured under tighter compatibility expectations than modern adversarial environments. That historical baggage is not unique to pegasus, but it is a classic source of kernel fragility.The Linux USB subsystem itself is designed around endpoint-driven communication, where a device advertises a set of descriptors and the driver decides how to use them. In principle, that is elegant. In practice, it means drivers must be strict about what they accept, because the kernel is often the first and most trusted consumer of those descriptors. If the driver’s probe path is permissive, the USB device effectively dictates the driver’s later behavior.
That is why the specific wording in the CVE is so telling. The issue is not merely “the driver crashes” but that it crashes after binding to a device whose endpoint layout does s. The bug therefore sits at the intersection of discovery logic and runtime safety: the driver should reject the device early, before any later URB handling can reach undefined state.
Modern USB host-side code increasingly treats malformed descriptors as an expected threat model, not an anomaly. Kernel documentation for USB fuzzing and raw gadget support makes it clear that intentionally malformed data is part of the test universe, and that endpoint assumptions are exactly the sort of thing fuzzers try to break. This CVE strongly suggests that the pegasus path had not yet absorbed that lesson thoroughly enough.
From an enterprise perspective, the issue also illustrates a subtle but important operational truth: hardware bugs are security bugs when they can be triggered by a malicious peripheral. That includes lab equipment, dropped-in adapters, counterfeit devices, and anything with USB access in an environment where users or attackers can physically connect hardware. In other words, the attack surface is not abstract; it lives at the desk, in the rack, and on the bench.
Why USB drivers are a perennial risk
USB is flexible enough to support almost any device class, which is exactly why it is so frequently abused.A driver that handles “normal” devices correctly can still be fragile when the hardware lies, omits descriptors, or advertises an impossible combination of endpoints.
The role of stable kernel backports
The references attached to the CVE point to multiple stable-tree commits, which usually means maintainers considered the fix suitable for broad ba a niche cleanup. That is consistent with the kind of bug that can affect older supported kernel lines and not just the newest mainline release. In practice, that often makes remediation simpler for vendors but more important for downstream users who rely on long-term support kernels.What the Vulnerability Looks Like
At a technical level, the flaw is best understood as a missing validation step during USB probe. The driver sh expected endpoint count and endpoint types are present before it begins using them, but instead it could proceed and only fail later when the code path reaches an endpoint access that no longer makes sense. That is a classic trust first, validate later mistake.The CVE text suggests the failure mode is a crash rather than a more elaborate exploit chain. That does not make it harmless. In kernel enial of service, and if the bug can be triggered by a deliberately malformed device, the attacker does not need kernel privileges to create the condition. They need hardware access, a malicious peripheral, or a controlled testing environment.
Endpoint expectations in context
USB devices do not just “exist”; they present a structured set of endpoints, each with a direction and a transfer type. Network adapters, storage devices, serial converters, and similar peripherals all depend on these descriptors being correct and complete. If a driver expects specific bulk or interrupt endpoints and they are absent, the driver’s later assumptions become unsafe.The kernel’s USB API documentation makes this clear by emphasizing endpoint capabilities and the role they play in matching driver behavior to device hardware. That is why endpoint validation belongs at the beginning of the binding process. It is the point where the driver still has a chance to say “no” before any operational state has been built on bad assumptions.
Failure mode and impact
The likely outcome of the bug is a kernel fault or crash when the driver attemt data that was never safe to use. The severity depends on where the code runs and what the system is doing, but the core concern is reliability under attacker-controlled conditions. Even a “mere crash” can be serious in embedded deployments, kiosks, router-style devices, and other systems where uptime matters more than feature richness.- Malicious device presents anet.
- The driver binds without sufficient endpoint checks.
- Later code assumes the endpoints exist and are usable.
- A crash or denial of service follows.
Why This Matters for Windows-Centric Shops
Even though this is a Linux kernel CVE, the Microsoft Security Response Center has published it in the Update Guide, which is a signal many enterprise defenders will see first. Microsoft’s own guidance says the Security Update Guide is the authoritative source for its security updates, and the presence of a Linux kernel CVE there is a reminder that vulnerability management is now ecosystem-wide rather than platform-isolated.That matters because many Windows-focused organizationdows estates anymore. They manage Linux guests, appliances, containers, lab machines, and mixed infrastructure where a kernel bug in one ecosystem still affects the same security team, the same asset inventory, and the same remediation calendar. The practical result is that a Linux USB driver bug can show up in the same triage queue as a Windows patch item.
Mixed-fleet operational reality
Modern defenders increasingly work from a single prioritization model across heterogeneous platforms.That means a CVE does not need to be “Windows” to matter to a Windows-first organization, and it does not need a flashy exploit chain to create work.
- Asset owners still need to know which systems load the affected module.
- Patch teams still need vendor backports and package versions.
- Security teams still need a reliable severity estimate.
- Operations still need to test regression risk.
Enterprise and consumer distinction
For consumers, the risk is likely concentrated in niche hardware scenarios: old USB Ethernet adapters, embedded devices, or systems that regularly accept untrusted peripher the exposure widens because the same device class may appear in labs, manufacturing, support desks, or field kits where physical access is broader than administrators would like. The enterprise concern is less “does this affect my laptop?” and more “where in the fleet can a bad USB device be introduced?”Historical Pattern: USB Endpoint Bugs Are Not New
This CVE lands in a well-established category of USB problems. Linux has a long history of fixes that improve endpoint validation, descriptor checking, and transfer setup because malformed or unexpected USB hardware keeps finding ways to stress assumptions in host-side drivers. The broader kernel documentation for raw gadget and endpoint handling exists precisely because endpoint semantics are easy to get wrong and hard to test exhaustively.The pegasus driver itself has seen prior security-adjacent fixes over the years, which reinforces the idea that older USB networking code is not automatically bad, but it often needs defensive maintenance. The presence of a historical pegasus CVE tied to crashes and memory corruption underlines how this driver family has long required careful handling. That history does not prove a broader systemic failure, but it does show a pattern that maintainers clearly take seriously.
Why older drivers are harder to harden
Older code often predates today’s threat assumptions. It may assume trusted hardware, stable descriptors, and benign plug-and-play behavior.That mismatch between original design and modern threat model is where many kernel bugs live.
- Legacy code paths often lack strict descriptor checks.
- Assumptions are buried in older probe logic.
- Regressionrs cautious about large rewrites.
- Small defensive patches become the preferred fix.
Patch Mechanics and Likely Remediation
The fix appearsimple: verify the number and type of endpoints during probe, and refuse to bind if the device does not match the driver’s expected layout. In driver terms, that usually means adding defensive checks before the driver stores endpoint pointers or submits any URBs. Simplicity is a strength here, because it reduces the chance of collateral damage in a stable keratch is also easier for distributors to backport. Endpoint validation tends to be self-contained, and when done correctly it changes the acceptance criteria for the device without altering the driver’s normal runtime behavior. In the best case, valid devices keep working exactly as before, while malicious or malformed ones are rejected early.What a good fix should preserve
A good kernel fix should avoid changing the behavior of correctly enumerated devices while tightening the gate for invalid ones.The goal is to reduce trust, not introduce a new compatibility headache.
- Preserve normal operation for compliant devices.
- Fail early on missing or mismatched endpoints.
- Avoid late crashes in the transmit or receive path.
- enough for stable trees.
What this means for downstream vendors
Downstream vendors and distro maintainers should treat this as a routine but importm. Systems that carry older USB networking support, especially those exposed to physical peripherals, should be verified against the fixed tree rather than assumed safe because the issue sounds narrow. The same caution applies to appliance vendors who may ship Linux kernels with backported USB stacks.Comparing This CVE to Other USB and Kernel Issues
CVE-2026-23290 is not a spectacular exploit int is a robustness issue with security consequences, and that puts it in the same broad family as many kernel bugs that are dismissed too quickly because they are “just” crashes. In reality, attack surface is attack surface, especially when the adversary can control the peripheral.What makes this class of bug persist is that USB device enumeration is highly contextual. A driver may work perfectly with intended hardware yet fail badly with a counterfeit, damaged, or maliciously constructed device. Linux’s USB infrastructure is intentionally flexible, which is great for compatibility but bad for assumptions. Security hardening therefore becomes an ongoing process of narrowing trust boundaries one driver at a time.
Security relevance without exploit glamour
A vulnerability does not need code execution to be operationally serious.If a local device or malicious peripheral can reliably crash the kernel, the issue still matters for availability, resilience, and physical attack paths.
This is where defenders should resist the temptation to rank only by headline severity. Many of the most disruptive incidents begin as simple-looking validation failures that let the system trust something it should have rejected. That is what makes endpoint validation such a valuable defensive practice in the kernel.
Strengths and Opportunities
This fix has several positive qualities that make it easy to defend operationally. It is narrow, conceptually clear, and aligned with the kernel’s own USB design principles. More importantly, it targets the right place in the lifecycle: before the driver commits to the device.- Small patch surface reduces regression risk.
- Probe-time validation closes the bug early.
- Stable-tree friendliness should make backporting straightforward.
- Better fault containment prevents later crashes.
- Clear security boundary improves maintainability.
- Useful precedent for auditing other USB drivers.
- mpact** for correctly enumerated devices.
Risks and Concerns
The main concern is not that the fix is weak; it is that the underlying class of bug is easy to miss across the rest of the USB stack. Legacy drivers often share similar assumptions, and endpoint validation bugs can exist in many more places than the current CVE names. There is also the evergreen problem of downstream lag: a fix can be merged upstream long before every supported vendor tree has absorbed it.- Undisclosed exposure window may vary by distro and kernel branch.
- Legacy deployments may lag on patch adoption.
- Malicious peripherals remain a real physical attack path.
- Similar assumptions may exist in sibling drivers.
- NVD enrichment delay can slow severity triage.
- Embedded systems may not receive uField environments** often have less controlled USB access.
Looking Ahead
The most important thing to watch next is how quickly downstream vendors pick up the stablnces point to multiple kernel.org stable commits, which usually means the patch is already in circulation in maintainers’ pipelines, but publication timing across distributions can still differ. Organizations should verify actual fixed build numbers rather than assuming that a kernel version label alone tells the whole story.It is also worth watching whether this issue triggers follow-on audits in related USB networking drivers. Historically, once one driver is found to have relied too heavily on descriptor assumptions, maintainers often review neighboring code for the same pattern. That kind of preventative work is not glamorous, but it is how the kernel slowly becomes harder to trick with malformed hardware.
What administrators should do next
- Inventory systems that load the pegasus USB network driver.
- Confirm whether your vendor kernel includes the endpoint-validation fix.
- Treat malicious or unknown USB hardware as a real risk, not a lab curiosity.
- Prioritize systems that operate in exposed physical environments.
5.security tooling reflects the backported fixed build.
CVE-2026-23290 is ultimately about strengthening the kernel’s habit of distrust. That is a healthy direction for USB code, and one that should make life better for both maintainers and defenders. The fix does not just patch one driver; it reinforces an important security principle: if the hardware can lie, the kernel must verify before it believes.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
Last edited: