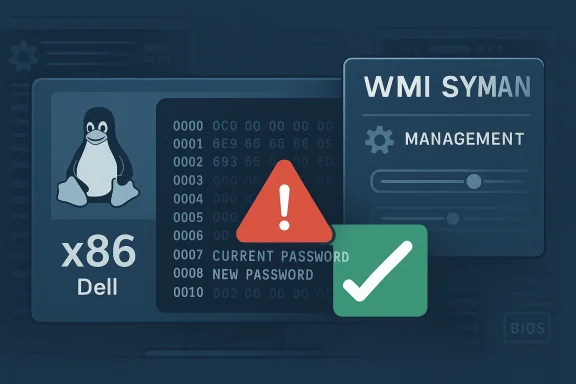
The disclosure of CVE-2026-23370 is a reminder that not every kernel security issue hinges on memory corruption or a dramatic exploit chain. Sometimes the vulnerability is a much simpler and more dangerous failure of operational hygiene: the Linux kernel’s Dell WMI Sysman path was hex-dumping an entire buffer that contained plaintext passwords, including both current and new credentials, and the fix is to remove that dump entirely. The issue sits in the platform/x86 Dell management code, which is maintained upstream in the Linux kernel tree, and the public record shows the CVE was received from kernel.org and linked to stable kernel commits on March 25, 2026.
The Dell WMI Sysman driver is part of the Linux kernel’s hardware-management layer for Dell systems, and it exists to expose system-management features through WMI interfaces. Kernel documentation lists the driver as maintained and names the Dell client kernel mailing list and the platform-driver-x86 list as its contact points, which is a useful clue about how specialized and vendor-adjacent this code is. This is not generic desktop plumbing; it is OEM-specific infrastructure for managing firmware attributes and system settings on Dell hardware.
That matters because firmware and system-management paths often sit close to sensitive configuration data. Password changes, BIOS settings, security policy toggles, and related controls are all the sort of operations that can pass through these interfaces. When a driver logs or dumps buffers during such operations, the consequences are not just noisy telemetry; they can become a direct credential exposure problem.
The vulnerability description says the bug was in
Linux kernel CVE handling also helps explain why this kind of issue gets a CVE even without a published exploit. Kernel.org documents that CVEs are commonly assigned to bugfixes in stable trees, and that the assignment process is intentionally cautious because even seemingly modest bugs can carry security implications. This CVE fits that pattern neatly: a targeted fix, a plausible security impact, and a stable-tree backport trail.
That durability is what transforms a narrow coding mistake into a larger incident response issue. Once plaintext credentials make it into logs, they may be replicated to SIEMs, centralized collectors, support bundles, or ticket attachments. Even if the original bug is fixed quickly, the historical log trail can remain a latent risk.
What makes the issue noteworthy is its simplicity. There is no need to speculate about speculative execution, race conditions, or privilege escalation primitives when the problem statement is already explicit: a debug-style hex dump exposed secrets. That kind of vulnerability is often dismissed as “just logging,” but in security operations, logs are frequently the easiest place for attackers and insiders alike to harvest useful secrets.
The broader ecosystem around the CVE also deserves attention. Microsoft’s Security Update Guide has increasingly become a cross-platform intake point for vulnerability intelligence, including Linux and OEM-linked issues, and the company has publicly described its advisory pages as a unified source for public security information. Even when Microsoft is not the vendor responsible for the fix, its inclusion of such CVEs signals that the issue is relevant to enterprise patch workflows that span Windows, Linux, and mixed-device estates.
For Dell-managed fleets, this is the kind of issue that can quietly sit below the radar if teams focus only on remote code execution or privilege escalation. Yet credential leakage often has a longer tail than a crash or a one-off denial of service. Password exposure can be reused across management tools, BIOS access, remote admin consoles, or helpdesk processes, turning a single bad log line into a broader identity problem.
That means the safe default for credential-handling code is not “log carefully,” but “do not log sensitive payloads at all.” When the payload includes both old and new passwords, even a sanitized partial dump would be risky. The fix in this case is the right kind of fix: eliminate the disclosure path rather than trying to redact it after the fact.
This sort of patch usually has a clean risk profile. Removing a debug dump generally does not alter the semantics of the password-setting operation itself, so the chance of functional regression is low compared with changes in parsing or state management. At the same time, the security gain is immediate and concrete: no more accidental plaintext exposure in logs.
Because the Linux kernel’s CVE process is tied to stable backports, the references linked to the CVE matter almost as much as the description itself. The public record shows several stable commit links associated with the fix, which suggests the patch is being propagated into supported branches rather than staying buried in mainline development. That is exactly the kind of downstream movement administrators need to track.
It is also worth noting that the driver is maintained within the Dell-specific platform x86 area of the kernel, which usually means downstream vendors and hardware integrators care more than generic desktop users do. A vulnerability in a vendor-management path can still affect a large installed base, but its exposure is often tied to specific hardware models and firmware workflows rather than every Linux system on earth.
That is why this CVE belongs in the same mental bucket as other “do not log secrets” mistakes. The patch is tiny, but the operational lesson is large. If a system-management interface can manipulate passwords, then every debug statement in that path should be treated as potential evidence of future exposure.
This is especially relevant in mixed environments where Linux systems are managed through the same operational tooling as Windows endpoints and Dell hardware inventory. Microsoft’s security guidance infrastructure is increasingly used to track cross-platform issues, and that reflects how real-world patch management works: one team, multiple operating systems, shared compliance obligations. A Linux kernel credential leak can therefore show up in the same queue as Windows and firmware vulnerabilities.
The likely enterprise exposure is also shaped by how Dell systems are used. BIOS passwords and management credentials are often tightly controlled, but they are also highly valuable. If they are leaked, attackers may gain a foothold into firmware settings, recovery workflows, or device-management consoles that are not protected by standard OS controls. That is a different kind of risk than ordinary application compromise, and it can be harder to detect.
There is also a compliance angle. Many organizations treat logs as evidence and store them for long periods. If plaintext credentials were captured, remediation may extend beyond patching the kernel into reviewing whether those logs need rotation, deletion, reprocessing, or restricted access. That is painful, but it is the correct response when secrets may already be compromised.
In many organizations, the most important next step is not just applying the fix but scoping historical exposure. If logs were exported to a SIEM, support portal, or backup system, the original plaintext may still exist there even after the patched kernel is deployed. That makes this CVE a good example of why credential leaks are often more difficult to close than memory-safety bugs.
The consumer risk becomes more serious if the machine is shared, serviced by a third party, or enrolled in remote support. In those cases, logs may be collected automatically and transmitted off-device, which broadens the audience for the secret far beyond the original user. The same goes for home lab enthusiasts who keep verbose system logs for troubleshooting.
In practical terms, individual users are less likely to know whether they were affected because the flaw leaves no obvious visual sign. There is no crash screen or warning banner here, only the absence of a harmful log entry after the fix. That makes the issue easy to miss and all the more important to patch quietly in the background.
If a user has ever sent a support bundle, posted a diagnostic archive, or shared a kernel log with a vendor or forum, they should treat that output with care. Passwords in logs are still passwords, no matter how many layers of tooling separated the user from the original dump.
That matters because many organizations do not sort vulnerabilities by vendor first; they sort by asset class, exposure, and patch status. A Linux kernel CVE surfaced in Microsoft’s ecosystem can therefore influence remediation even if the actual fix sits upstream in the kernel tree. The presence of the advisory route makes the issue easier to notice in heterogeneous environments.
The Linux kernel documentation also explains that CVEs are assigned after fixes are available in stable trees, which reinforces why these records are practical and actionable rather than hypothetical. In this case, the kernel.org trail and the NVD entry align with a standard Linux CVE lifecycle: fix first, CVE second, downstream propagation afterward.
For admins, this cross-publisher visibility is useful but imperfect. It helps surface the issue faster, yet it can also obscure who is actually responsible for remediation. Microsoft can help customers see the problem, but the patch ultimately comes from the Linux kernel and whatever downstream vendor or distribution packages it. That split is manageable, but only if teams understand it clearly.
This is especially valuable for security operations centers that rely on a single intake process. Unified advisory surfaces reduce the chance that a Linux kernel issue gets missed simply because the affected asset lives in a Windows-centric organization. In that sense, the Microsoft listing is a distribution channel for awareness, not a claim of product ownership.
The kernel community has long recognized that not all security bugs are memory corruption bugs. Information disclosure, improper logging, stale data handling, and secret leakage can all be serious vulnerabilities in their own right. What changes is the path to exploitation: instead of forcing code execution, the bug may simply hand an attacker the exact credentials they need to move laterally.
That is why the patch’s modest scope should not mislead readers. In the kernel world, a one-line removal can matter just as much as a deep refactor. The key question is whether the bug touched something that should never have been exposed. Here, the answer is plainly yes.
The Dell WMI Sysman bug fits that mold perfectly. It is not about algorithmic novelty; it is about discipline. Sensitive data should stay off the console, off the log, and out of any diagnostic path that is not explicitly designed to handle it.
The second question is whether other management paths in the Linux kernel or OEM tooling contain similar debug output mistakes. If one password-setting function dumped its buffer, there is a reasonable chance other device-management code has comparable logging habits. That is why a single CVE like this often leads to broader code review, especially in firmware and platform-management subsystems.
The third question is whether enterprises treat this as a logging hygiene issue or a full incident-response event. If any plaintext credentials were captured, they may need to be rotated and the logs may need to be treated as sensitive data themselves. That is a messy operational reality, but it is the correct one.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 Background
Background
The Dell WMI Sysman driver is part of the Linux kernel’s hardware-management layer for Dell systems, and it exists to expose system-management features through WMI interfaces. Kernel documentation lists the driver as maintained and names the Dell client kernel mailing list and the platform-driver-x86 list as its contact points, which is a useful clue about how specialized and vendor-adjacent this code is. This is not generic desktop plumbing; it is OEM-specific infrastructure for managing firmware attributes and system settings on Dell hardware.That matters because firmware and system-management paths often sit close to sensitive configuration data. Password changes, BIOS settings, security policy toggles, and related controls are all the sort of operations that can pass through these interfaces. When a driver logs or dumps buffers during such operations, the consequences are not just noisy telemetry; they can become a direct credential exposure problem.
The vulnerability description says the bug was in
set_new_password(), where the function hex-dumped the entire buffer and therefore printed both the current and new passwords in plaintext form. That is a classic example of a security bug that does not require an attacker to bypass protections in the usual sense; the dangerous data is already in memory, and the log output becomes the leak path. In other words, the problem is not that the kernel failed to protect the password at rest, but that it helped disclose it during normal handling.Linux kernel CVE handling also helps explain why this kind of issue gets a CVE even without a published exploit. Kernel.org documents that CVEs are commonly assigned to bugfixes in stable trees, and that the assignment process is intentionally cautious because even seemingly modest bugs can carry security implications. This CVE fits that pattern neatly: a targeted fix, a plausible security impact, and a stable-tree backport trail.
Why this kind of bug matters
A password leak in kernel logging is especially troubling because logs tend to be widely accessible inside organizations. Administrators, support tooling, crash collection systems, and remote diagnostic pipelines may all touch the data, which makes the exposure surface much broader than the original code path. A secret that should have remained transient instead becomes durable and replayable.That durability is what transforms a narrow coding mistake into a larger incident response issue. Once plaintext credentials make it into logs, they may be replicated to SIEMs, centralized collectors, support bundles, or ticket attachments. Even if the original bug is fixed quickly, the historical log trail can remain a latent risk.
- The kernel path handled plaintext credentials.
- The leaked data included current and new passwords.
- The output path was hex dumping, not encrypted storage.
- The blast radius includes logs, crash reports, and support artifacts.
Overview
The timeline is straightforward. On March 25, 2026, the CVE record was created and associated with the Linux kernel fix for the Dell WMI Sysman driver, with NVD noting that it was still awaiting enrichment analysis at publication time. The record also includes kernel.org references to stable commits, which is typical for Linux kernel CVEs that originate from upstream fixes and are then tracked downstream.What makes the issue noteworthy is its simplicity. There is no need to speculate about speculative execution, race conditions, or privilege escalation primitives when the problem statement is already explicit: a debug-style hex dump exposed secrets. That kind of vulnerability is often dismissed as “just logging,” but in security operations, logs are frequently the easiest place for attackers and insiders alike to harvest useful secrets.
The broader ecosystem around the CVE also deserves attention. Microsoft’s Security Update Guide has increasingly become a cross-platform intake point for vulnerability intelligence, including Linux and OEM-linked issues, and the company has publicly described its advisory pages as a unified source for public security information. Even when Microsoft is not the vendor responsible for the fix, its inclusion of such CVEs signals that the issue is relevant to enterprise patch workflows that span Windows, Linux, and mixed-device estates.
For Dell-managed fleets, this is the kind of issue that can quietly sit below the radar if teams focus only on remote code execution or privilege escalation. Yet credential leakage often has a longer tail than a crash or a one-off denial of service. Password exposure can be reused across management tools, BIOS access, remote admin consoles, or helpdesk processes, turning a single bad log line into a broader identity problem.
The practical security lesson
The real lesson here is that debug output is part of the attack surface. Engineers often treat dumps and traces as harmless because they are intended for internal troubleshooting, but the kernel does not live in an internal-only world. Anything written to logs can be captured, forwarded, indexed, and retained far longer than intended.That means the safe default for credential-handling code is not “log carefully,” but “do not log sensitive payloads at all.” When the payload includes both old and new passwords, even a sanitized partial dump would be risky. The fix in this case is the right kind of fix: eliminate the disclosure path rather than trying to redact it after the fact.
- Logging is a security boundary.
- Passwords should never be hex-dumped.
- Redaction is harder than omission.
- Credential leakage often outlives the original bug.
What changed in the kernel
The fix is narrowly scoped but important: theset_new_password() path no longer hex-dumps the buffer containing password data. That means the kernel still performs the password-setting logic, but it stops printing the contents of the request while doing so. In security terms, this is a reduction of exposure rather than a redesign of the feature.This sort of patch usually has a clean risk profile. Removing a debug dump generally does not alter the semantics of the password-setting operation itself, so the chance of functional regression is low compared with changes in parsing or state management. At the same time, the security gain is immediate and concrete: no more accidental plaintext exposure in logs.
Because the Linux kernel’s CVE process is tied to stable backports, the references linked to the CVE matter almost as much as the description itself. The public record shows several stable commit links associated with the fix, which suggests the patch is being propagated into supported branches rather than staying buried in mainline development. That is exactly the kind of downstream movement administrators need to track.
It is also worth noting that the driver is maintained within the Dell-specific platform x86 area of the kernel, which usually means downstream vendors and hardware integrators care more than generic desktop users do. A vulnerability in a vendor-management path can still affect a large installed base, but its exposure is often tied to specific hardware models and firmware workflows rather than every Linux system on earth.
Why the fix is low drama but high value
Small code changes can have outsized security impact when they remove a leak rather than patch an exploit chain. The absence of a dramatic architectural change should not be confused with a lack of importance. In practice, many enterprises suffer more from accidental disclosure than from sophisticated remote exploitation, especially when secrets show up in diagnostics that are widely shared during support incidents.That is why this CVE belongs in the same mental bucket as other “do not log secrets” mistakes. The patch is tiny, but the operational lesson is large. If a system-management interface can manipulate passwords, then every debug statement in that path should be treated as potential evidence of future exposure.
- The patch is surgical.
- The security benefit is immediate.
- The regression risk is comparatively low.
- The logging path was the real vulnerability.
Enterprise impact
For enterprise administrators, the key question is not whether the bug allows arbitrary code execution. The real issue is whether the system may have emitted secrets into logs, crash bundles, or support artifacts. If a Dell client system was affected and those logs were centralized, the organization may need to consider log hygiene, retention, and access controls as part of the response.This is especially relevant in mixed environments where Linux systems are managed through the same operational tooling as Windows endpoints and Dell hardware inventory. Microsoft’s security guidance infrastructure is increasingly used to track cross-platform issues, and that reflects how real-world patch management works: one team, multiple operating systems, shared compliance obligations. A Linux kernel credential leak can therefore show up in the same queue as Windows and firmware vulnerabilities.
The likely enterprise exposure is also shaped by how Dell systems are used. BIOS passwords and management credentials are often tightly controlled, but they are also highly valuable. If they are leaked, attackers may gain a foothold into firmware settings, recovery workflows, or device-management consoles that are not protected by standard OS controls. That is a different kind of risk than ordinary application compromise, and it can be harder to detect.
There is also a compliance angle. Many organizations treat logs as evidence and store them for long periods. If plaintext credentials were captured, remediation may extend beyond patching the kernel into reviewing whether those logs need rotation, deletion, reprocessing, or restricted access. That is painful, but it is the correct response when secrets may already be compromised.
Operational implications
The operational burden will fall on teams that own Dell Linux fleets, not on general-purpose desktop users. They should inventory affected kernel builds, confirm whether the relevant Dell WMI Sysman code path is present, and determine whether password-setting operations were logged anywhere. In enterprise settings, this is the sort of issue that can trigger both a patching task and an incident-response task.In many organizations, the most important next step is not just applying the fix but scoping historical exposure. If logs were exported to a SIEM, support portal, or backup system, the original plaintext may still exist there even after the patched kernel is deployed. That makes this CVE a good example of why credential leaks are often more difficult to close than memory-safety bugs.
- Check whether Dell-managed Linux hosts use the affected code path.
- Review centralized logs for password-setting traces.
- Audit who can read support artifacts and diagnostics.
- Rotate any credentials that may have been exposed.
- Preserve evidence before deleting logs, if incident handling requires it.
Consumer impact
For most consumers, the practical exposure window is narrower than it is for enterprises. Many users never interact with Dell BIOS management through Linux utilities, and even those who do may not generate the sort of logs that get widely aggregated. Still, consumer systems are not immune; a leaked password in a local log is still a leaked password.The consumer risk becomes more serious if the machine is shared, serviced by a third party, or enrolled in remote support. In those cases, logs may be collected automatically and transmitted off-device, which broadens the audience for the secret far beyond the original user. The same goes for home lab enthusiasts who keep verbose system logs for troubleshooting.
In practical terms, individual users are less likely to know whether they were affected because the flaw leaves no obvious visual sign. There is no crash screen or warning banner here, only the absence of a harmful log entry after the fix. That makes the issue easy to miss and all the more important to patch quietly in the background.
What a home user should care about
Even if the average consumer never sees the bug directly, the message is simple: firmware-management tools should be updated as part of normal system maintenance, especially on branded hardware. Password-related code paths are not the place for experimentation, and users who troubleshoot with logs should remember that diagnostics can outlive the session that created them.If a user has ever sent a support bundle, posted a diagnostic archive, or shared a kernel log with a vendor or forum, they should treat that output with care. Passwords in logs are still passwords, no matter how many layers of tooling separated the user from the original dump.
- Home systems may still generate sensitive local logs.
- Third-party support can widen the exposure.
- Shared machines increase the odds of misuse.
- Firmware-management tools deserve the same update discipline as the OS.
Microsoft’s role in tracking the issue
Microsoft’s appearance in the story may look odd at first, but it is part of a broader trend. The Microsoft Security Update Guide has become a centralized disclosure surface for vulnerabilities across Microsoft and non-Microsoft ecosystems, including issues that matter to enterprise patch coordination. Microsoft has also described its advisory and CVE workflows as a way to provide machine-readable security intelligence to customers.That matters because many organizations do not sort vulnerabilities by vendor first; they sort by asset class, exposure, and patch status. A Linux kernel CVE surfaced in Microsoft’s ecosystem can therefore influence remediation even if the actual fix sits upstream in the kernel tree. The presence of the advisory route makes the issue easier to notice in heterogeneous environments.
The Linux kernel documentation also explains that CVEs are assigned after fixes are available in stable trees, which reinforces why these records are practical and actionable rather than hypothetical. In this case, the kernel.org trail and the NVD entry align with a standard Linux CVE lifecycle: fix first, CVE second, downstream propagation afterward.
For admins, this cross-publisher visibility is useful but imperfect. It helps surface the issue faster, yet it can also obscure who is actually responsible for remediation. Microsoft can help customers see the problem, but the patch ultimately comes from the Linux kernel and whatever downstream vendor or distribution packages it. That split is manageable, but only if teams understand it clearly.
Why cross-platform visibility matters
Modern patch management is no longer neatly divided by operating system. The same enterprise may run Windows endpoints, Linux servers, Dell hardware, and cloud images all under one security program. That means a CVE like this is relevant not because it belongs to Microsoft, but because Microsoft’s ecosystem is one of the places defenders look for authoritative vulnerability intelligence.This is especially valuable for security operations centers that rely on a single intake process. Unified advisory surfaces reduce the chance that a Linux kernel issue gets missed simply because the affected asset lives in a Windows-centric organization. In that sense, the Microsoft listing is a distribution channel for awareness, not a claim of product ownership.
- Microsoft’s guide is a triage surface, not the source of the bug.
- The upstream fix remains in Linux kernel code.
- Enterprises benefit from one more place to spot the CVE.
- Responsibility for remediation still sits with Linux and OEM owners.
How this fits the Linux kernel security model
This CVE also says something important about Linux kernel security culture. Kernel.org’s own CVE documentation emphasizes that the project assigns identifiers to bugfixes because even bugs that look minor can be security relevant once they interact with privileged code paths or sensitive data. The Dell WMI Sysman issue is a textbook example of that policy in action.The kernel community has long recognized that not all security bugs are memory corruption bugs. Information disclosure, improper logging, stale data handling, and secret leakage can all be serious vulnerabilities in their own right. What changes is the path to exploitation: instead of forcing code execution, the bug may simply hand an attacker the exact credentials they need to move laterally.
That is why the patch’s modest scope should not mislead readers. In the kernel world, a one-line removal can matter just as much as a deep refactor. The key question is whether the bug touched something that should never have been exposed. Here, the answer is plainly yes.
The broader pattern
There is also a broader pattern visible across kernel CVEs: many fixes are not glamorous, but they are operationally necessary. A log leak, a missing bounds check, a bad state reset, or a refcount mistake may not generate headlines outside the security community, yet each one removes a foothold for attackers or reduces the chance of accidental harm.The Dell WMI Sysman bug fits that mold perfectly. It is not about algorithmic novelty; it is about discipline. Sensitive data should stay off the console, off the log, and out of any diagnostic path that is not explicitly designed to handle it.
- Kernel CVEs are often about cleanup, discipline, and invariants.
- Information disclosure is a first-class security issue.
- The most dangerous logs are the ones people assume are harmless.
- Small patches can eliminate large exposure windows.
Strengths and Opportunities
The good news is that this is a fixable class of problem, and the kernel patch is already doing the most important thing: removing the disclosure path. The issue is also easy to understand, which makes it easier for downstream vendors, distributions, and administrators to validate quickly. In a world of highly technical vulnerabilities, clarity is a strength.- Simple remediation path: remove the dump, stop the leak.
- Low functional risk compared with deep logic changes.
- Easy to audit in code review and downstream backports.
- Strong enterprise relevance because the exposed data is credentials.
- Useful wake-up call for logging policies in management code.
- Good example of why debug output must be treated as sensitive.
Risks and Concerns
The main concern is that the leaked information may already exist in logs, support bundles, or centralized telemetry before the fix is applied. That means patching the kernel is necessary but not sufficient; organizations may also need to search, rotate, or delete exposed material. Credential leaks are especially troublesome because their impact often extends beyond the machine that generated them.- Historical exposure may remain after patching.
- Log aggregation can multiply the blast radius.
- Credential reuse can turn one leak into many compromises.
- Access control gaps in support systems make recovery harder.
- Silent exploitation is possible because the bug leaves no obvious alert.
- Hardware-specific scope can make inventorying affected systems harder.
Looking Ahead
The immediate question is how quickly downstream distributions and OEMs fold the fix into their supported kernels. Because this issue lives in a vendor-management path, the real-world exposure will depend on whether Dell Linux systems in the field actually exercise the password-setting code and whether logs are retained long enough to matter. The patch itself is straightforward, but the cleanup around it may take longer.The second question is whether other management paths in the Linux kernel or OEM tooling contain similar debug output mistakes. If one password-setting function dumped its buffer, there is a reasonable chance other device-management code has comparable logging habits. That is why a single CVE like this often leads to broader code review, especially in firmware and platform-management subsystems.
The third question is whether enterprises treat this as a logging hygiene issue or a full incident-response event. If any plaintext credentials were captured, they may need to be rotated and the logs may need to be treated as sensitive data themselves. That is a messy operational reality, but it is the correct one.
- Confirm which kernel builds include the fix.
- Review retained logs for credential traces.
- Rotate any passwords that might have been exposed.
- Audit other OEM management paths for unsafe dumps.
- Watch downstream distro advisories for backport status.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center